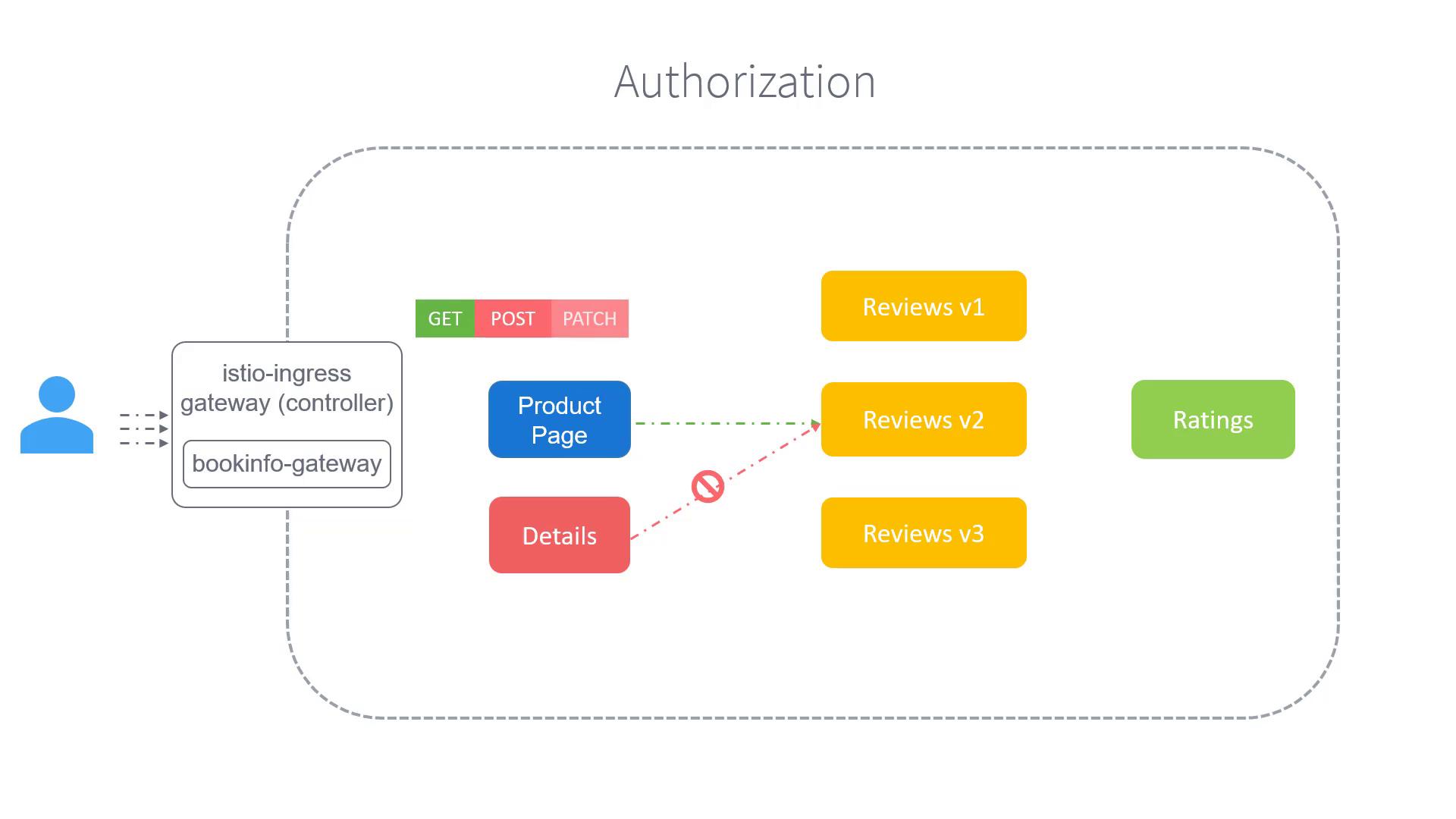
Istio authorization provides a flexible, robust mechanism to manage inbound traffic and secure communication between services. By leveraging authorization policies, you can control which services are permitted to interact with one another—this is commonly referred to as east-west traffic control. When coupled with authentication policies, the system not only secures end-user and service-to-service communications but also enforces fine-grained access control. For instance, you may want a paid product service to access a reviews service exclusively via GET requests while denying POST or UPDATE operations. Likewise, you might need to prevent unauthorized services, such as a product page service, from attempting to modify reviews using POST calls.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
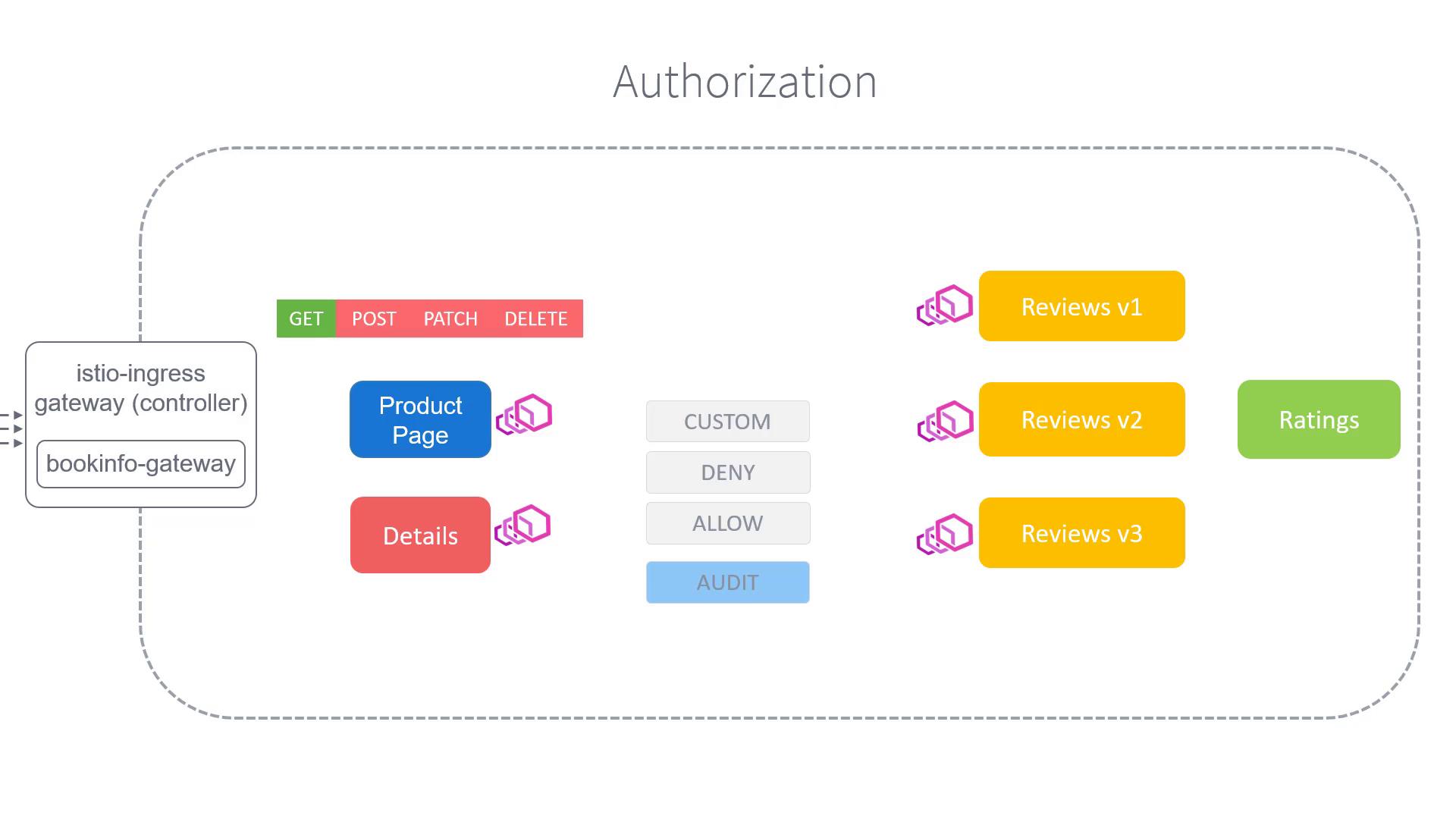
- Allow: Permits the request.
- Deny: Blocks the request.
- Custom: Enables extension of request handling with user-defined logic.
Authorization policies can also be configured to audit requests. When a request matches a specific rule, it is logged for auditing, offering valuable insights for security monitoring.
Example: Implementing an Authorization Policy
Consider the following example of an Authorization Policy. In this scenario, the policy is defined with thekind set to AuthorizationPolicy and configured to block all POST requests originating from the “bar” namespace to the “bookinfo” namespace.
Ensure that your authorization policies are carefully tested in a staging environment before deploying them to production. Incorrect configurations may inadvertently block legitimate traffic.