Now let’s cover two things people often forget until it’s too late: security and cost. You’ve already seen how cloud services are structured and where responsibility splits between you and the provider. Security and cost are cross-cutting concerns — they run through everything you build in the cloud. One misplaced permission, one misconfigured storage bucket, or one oversized database can turn a small issue into a production incident or a large monthly bill. In this lesson we’ll zoom in on cloud security fundamentals you must get right (shared responsibility, network controls, IAM, and the CIA triad) and set up the right mindset before switching to cost-management techniques.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.

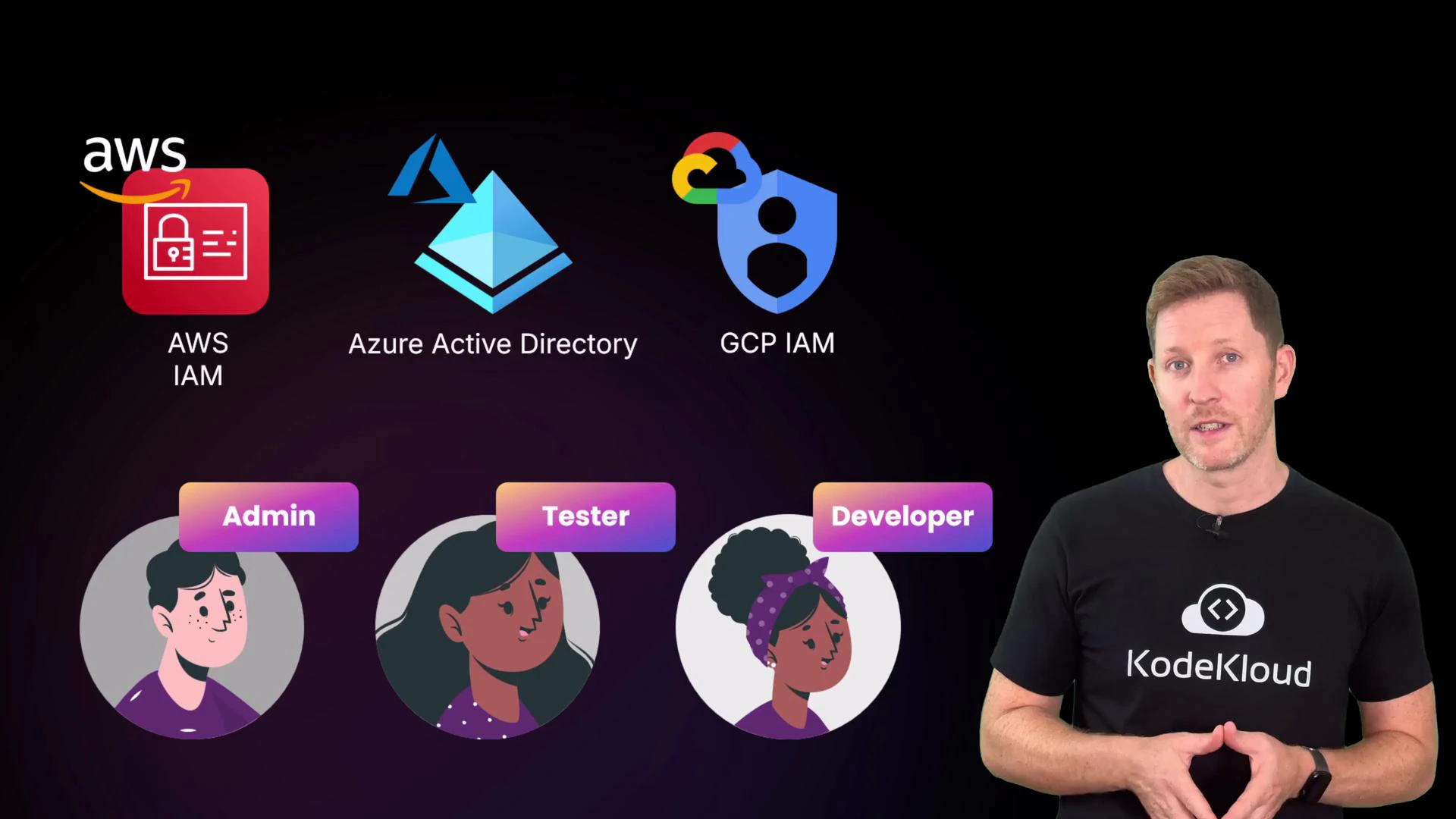
Cloud providers (AWS, Azure, GCP) secure the infrastructure — the physical data centers, hypervisors, and managed platform services. You are responsible for securing your workloads, data, and access policies running on top of that infrastructure. This is the shared responsibility model. For reference, see AWS Shared Responsibility, Azure shared responsibility and GCP shared responsibility.
- Security groups (network controls): Virtual firewalls that let you define which ports and IP ranges or services can connect to a given resource.
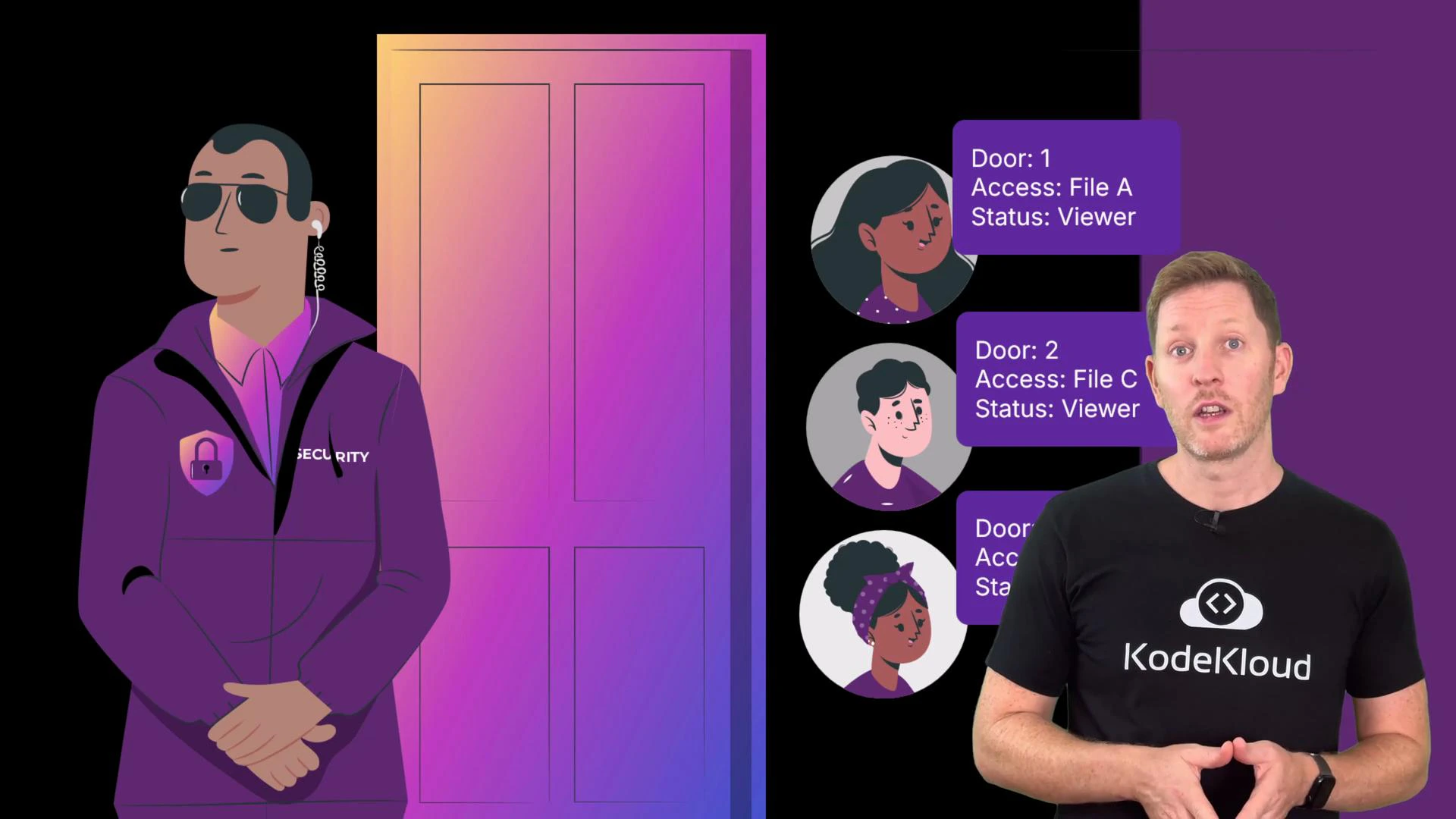
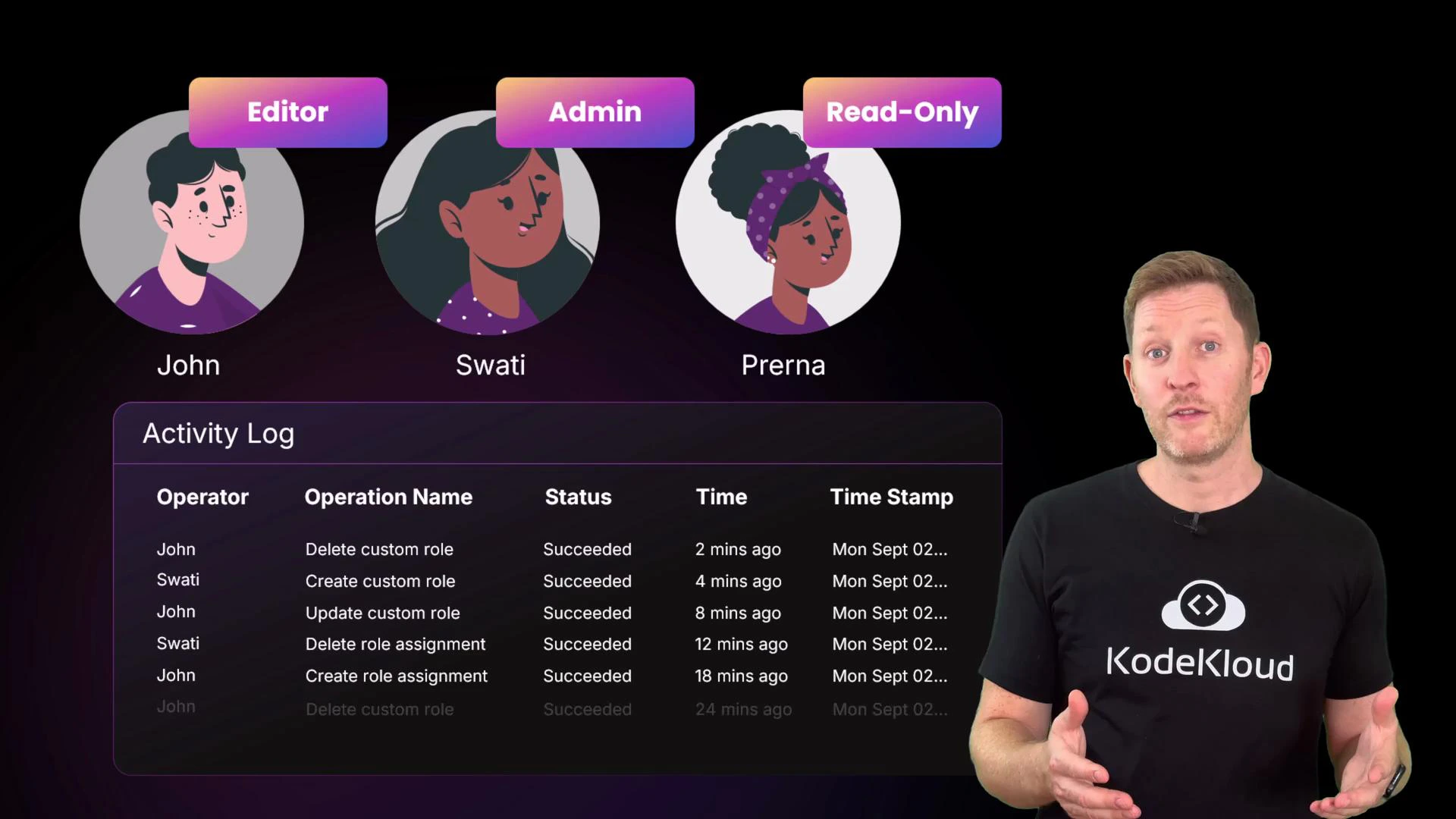
- IAM (identity and access management): Policies and roles that define who can read, write, create, or delete cloud resources.

| CIA Pillar | Typical Risks | Practical Mitigations |
|---|---|---|
| Confidentiality | Misconfigured storage, secrets leaked in code, phishing | Default storage to private, apply least privilege with IAM, enable automated scans/audit logs, use a secrets manager, enforce MFA, run phishing awareness training. |
| Integrity | Unauthorized edits, accidental deletes, rogue scripts | Separate read/write roles, enable detailed audit logging, use versioning/immutable backups, restrict admin actions with just-in-time or approval workflows. |
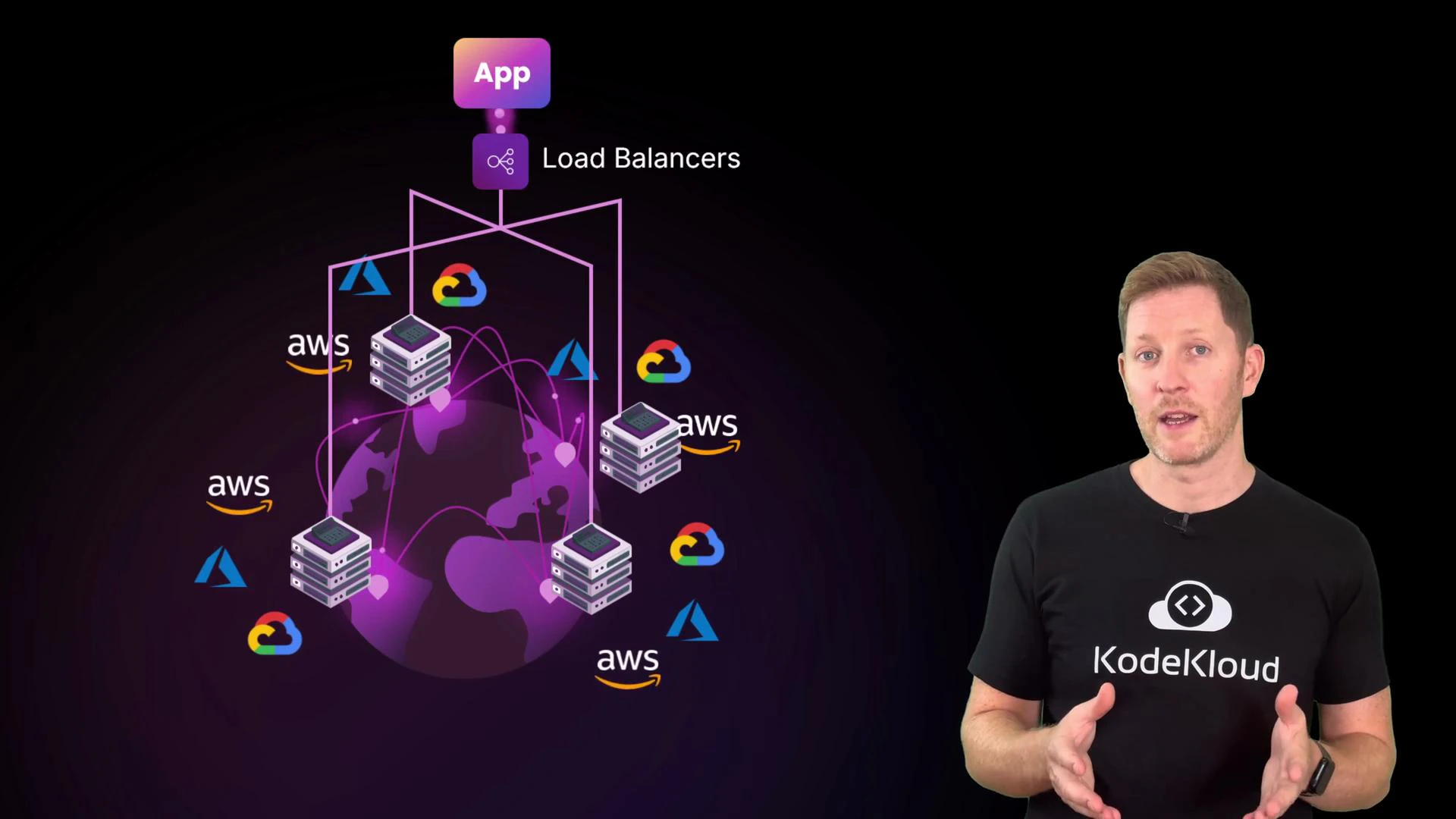
| Availability | Single-server failure, AZ/region outage, traffic spikes | Architect across availability zones/regions, use load balancers, configure auto scaling with clear thresholds (e.g., scale if CPU > 70% for N minutes), run health checks, and automate instance recovery. |
- Misconfigured storage: Example — a team uploads customer invoices to a cloud folder but leaves sharing public. Mitigation: default to private, restrict access with IAM, and enable automated public-exposure scanners and audit logs.
- Secrets in code: Example — an API key committed to a public repo. Mitigation: never store credentials in code; use a secrets manager (inject secrets at runtime or via secure CI/CD).
- Phishing: Example — stolen credentials via a fake login. Mitigation: user training and phishing-resistant authentication like multi-factor authentication (MFA).


Never commit secrets (API keys, credentials) to source control. Use a managed secrets store and integrate secrets into CI/CD pipelines securely. If a secret is exposed, rotate it immediately and audit any usage.

- Tampering or accidental edits: A rogue script or an unauthorized user could modify or delete records, making data inaccurate. Mitigations: least-privilege IAM roles (separate read-only from write/admin), detailed audit logging, and versioning or immutable backups so you can trace and roll back changes.
- Downtime and capacity issues: Even if data is confidential and intact, users still need the service to be available. Outages can result from a single-server failure, an availability zone or regional outage, or sudden traffic spikes. Cloud providers design infrastructure across regions and availability zones, but you must architect your applications to leverage that redundancy.

- Spread resources across multiple availability zones and, when appropriate, across regions.
- Use load balancers to distribute traffic to healthy instances.
- Configure auto scaling with clear rules (for example, scale out when average CPU > 70% for N minutes).
- Implement health checks and automated recovery policies so unhealthy instances are replaced without manual intervention.
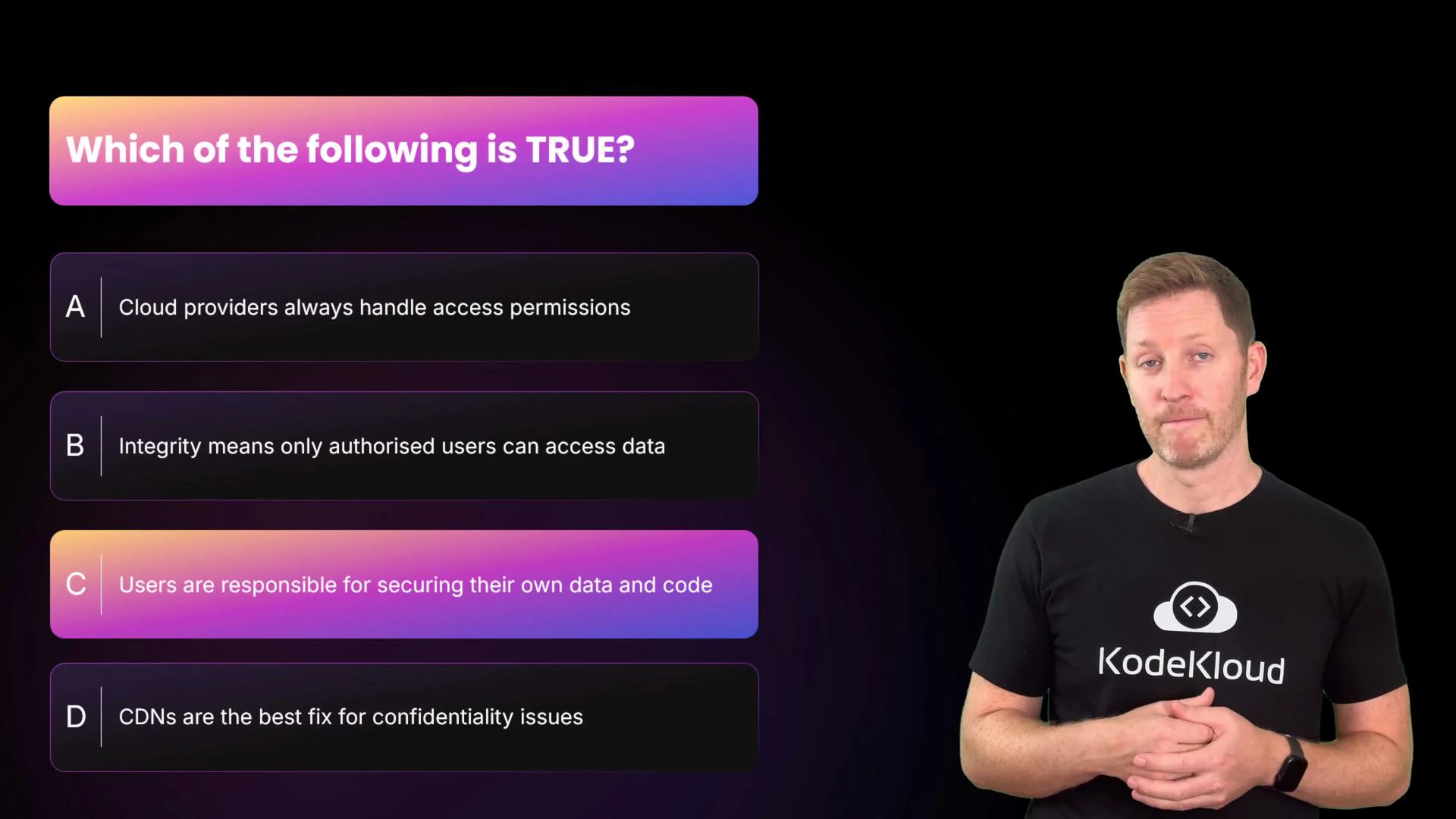
B. Integrity means only authorized users can access data.
C. Users are responsible for securing their own data and code.
D. CDNs are the best fix for confidentiality issues. Pause to think, then continue. The correct answer is C.
- Why: A is false — providers provide the tools, but you configure access.
- Why: B is false — integrity is about preventing unauthorized modification (accuracy), while confidentiality is about preventing unauthorized reading.
- Why: D is false — CDNs help performance and availability (and can provide DDoS protection), but they’re not the primary solution for confidentiality.
- Shared responsibility model: cloud providers secure the platform; you secure workloads, data, and access policies.
- Map threats to the CIA triad: Confidentiality (data leaks), Integrity (tampering or accidental edits), Availability (outages and capacity failures).
- Mitigate threats with correct configuration (security groups, IAM), cloud-native features (secrets managers, logging, versioning, multi-zone architectures), and operational practices (least privilege, MFA, training, automation).