A service mesh in Kubernetes offers a dedicated communication layer that abstracts networking and infrastructure concerns away from application code. By injecting a lightweight proxy—called a sidecar—next to each service instance, it intercepts all inbound and outbound traffic. This approach provides consistent traffic management, mTLS security, and observability without changing your application. Services (e.g., frontend, middle-tier, backend) run alongside their respective sidecar proxies. Although deployed together, proxies are managed independently, allowing you to update or scale them separately. The result is a clean codebase while the mesh transparently handles retries, circuit breaking, encryption, and more. Open Service Mesh (OSM) for AKS consists of two main layers: the data plane and the control plane.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
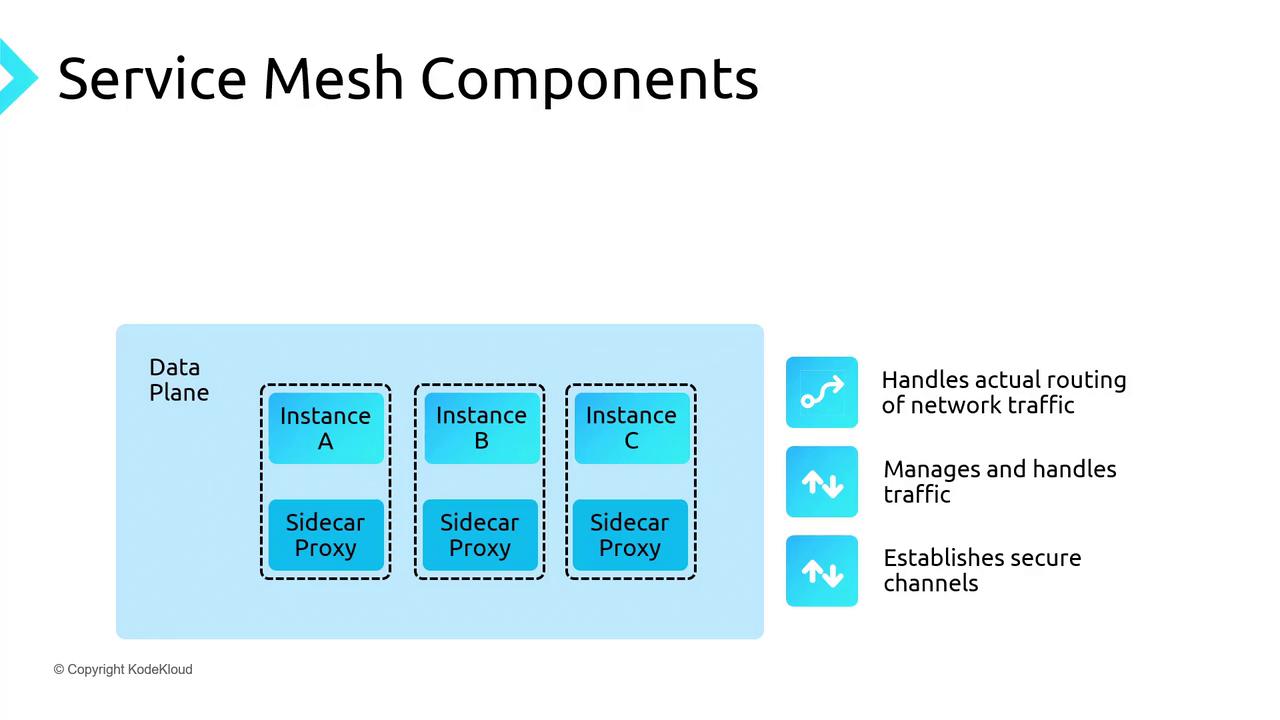
Data Plane
The data plane is responsible for the actual routing of network traffic between services. Its key functions include:- Service discovery: Automatically finding and routing to healthy instances.
- Traffic management: Implementing retries, circuit breakers, and load balancing.
- Security: Establishing mutual TLS (mTLS) channels for encrypted, authenticated communication.
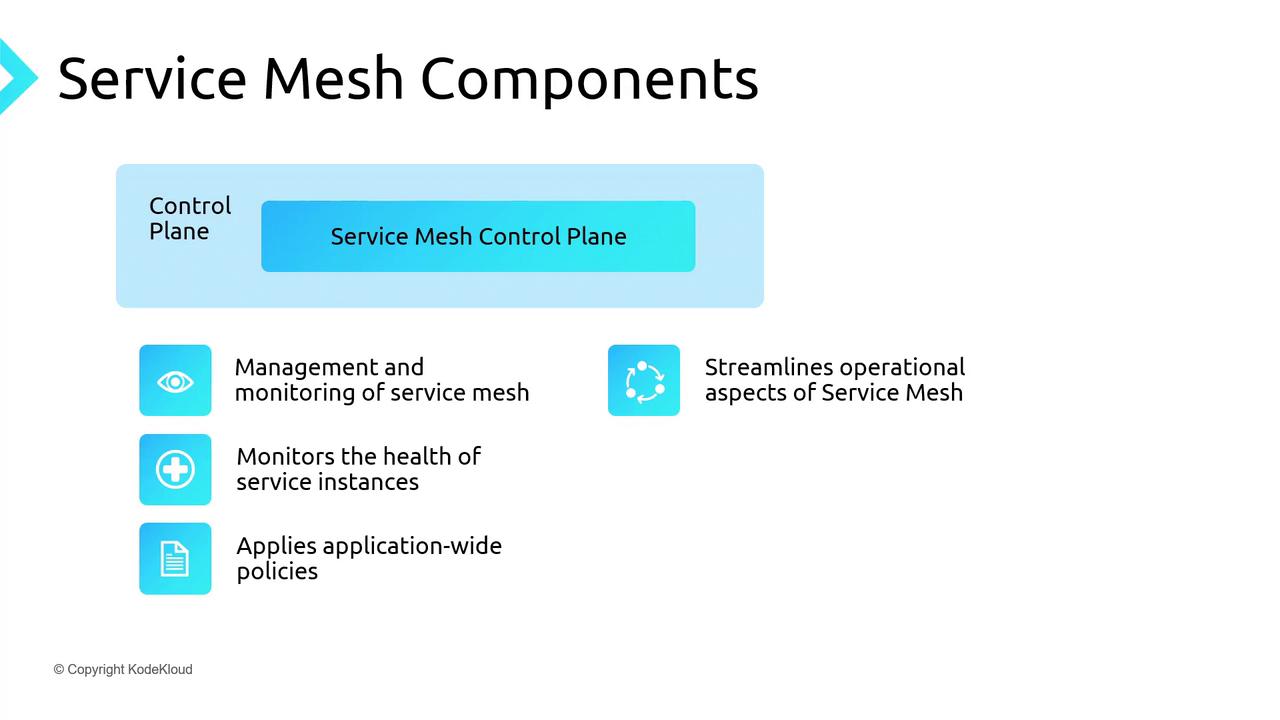
Control Plane
The control plane provides centralized orchestration and visibility. It:- Provisions and scales service instances.
- Monitors pod health and replaces unhealthy instances.
- Enforces policies such as rate limits, access control, and routing rules.
Popular Service Mesh Implementations
| Implementation | Language/Platform | Key Characteristics |
|---|---|---|
| Istio | Go | Extensible, full-featured, advanced policy engine |
| Linkerd | Scala (JVM) | Lightweight, simplicity-first, low overhead |
| Open Service Mesh (OSM) | Go | CNCF-compliant, Envoy-based, lightweight control plane |
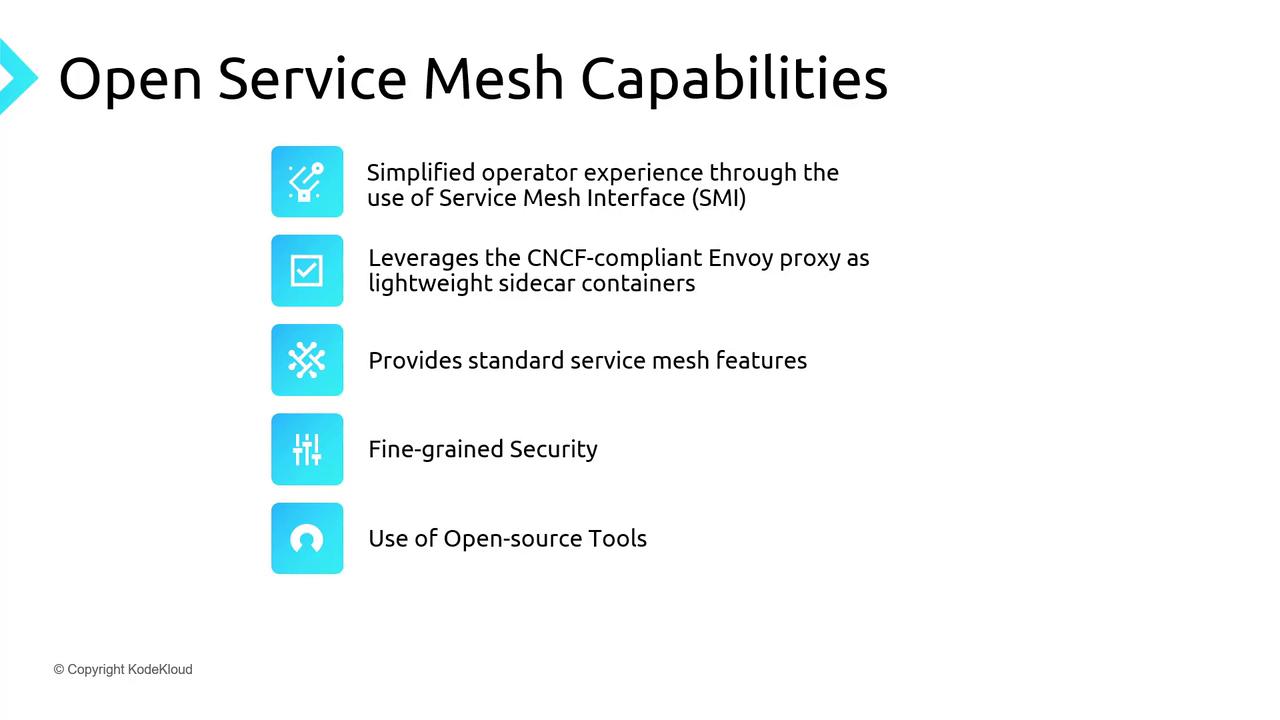
Features of Open Service Mesh
- Simplified control plane for easy operations
- Envoy sidecars for CNCF-approved, high-performance proxying
- Traffic policies: access control, traffic splitting, telemetry
- Fine-grained mTLS for service-to-service encryption
- Integration with Prometheus, Grafana, Jaeger for monitoring and tracing
- Support for external certificate authorities in production
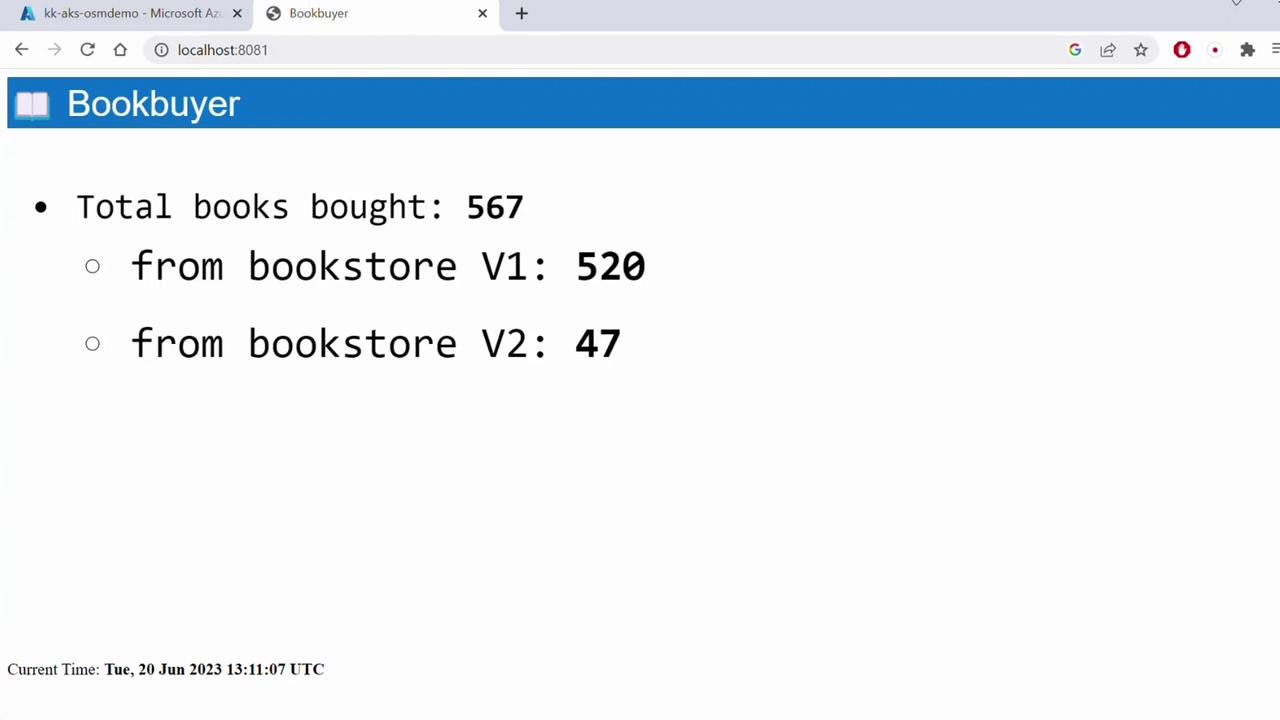
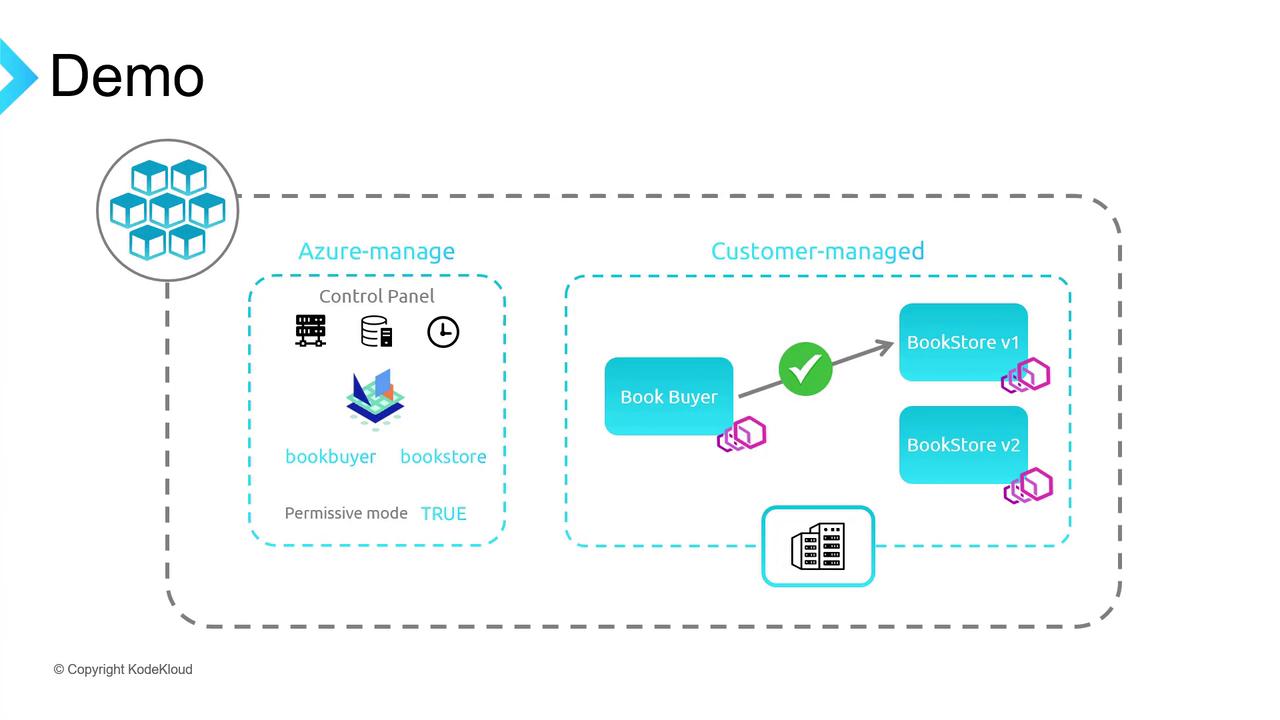
Demo Architecture
We’ll deploy a sample bookstore application on AKS with OSM in permissive mode. The demo includes:- Book Buyer (client)
- Bookstore V1 (primary backend)
- Bookstore V2 (for traffic splitting)
- Book Warehouse (additional service)
Prerequisites
- Azure CLI installed
kubectlconfigured locallyosmCLI for namespace onboarding
1. Create Resource Group and AKS Cluster
2. Configure kubectl Context
3. Create Namespaces and Onboard to OSM
4. Deploy Sample Applications
5. Port-Forward and Verify Default Traffic
http://localhost:8081 to see Book Buyer successfully fetching from Bookstore V1 under OSM’s permissive policy.
Permissive mode allows all services in the mesh to communicate without explicit SMI traffic policies.
6. Disable Permissive Traffic Policy
In the Azure Portal under AKS → Open Service Mesh → Configuration, update:Disabling permissive mode without defining traffic policies will block all inter-service communication.
7. Apply Explicit Allow Traffic Policy
http://localhost:8081 to confirm connectivity.
8. Demonstrate Traffic Splitting
Createtraffic-split.yaml:
weight values to shift more traffic to a particular version.