Kubernetes pods communicate freely by default, which simplifies development but poses risks in production. Network Policies close this gap by defining fine-grained rules for pod-to-pod, namespace, and external traffic. Think of them as traffic signs in your cluster that explicitly allow or deny connections.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
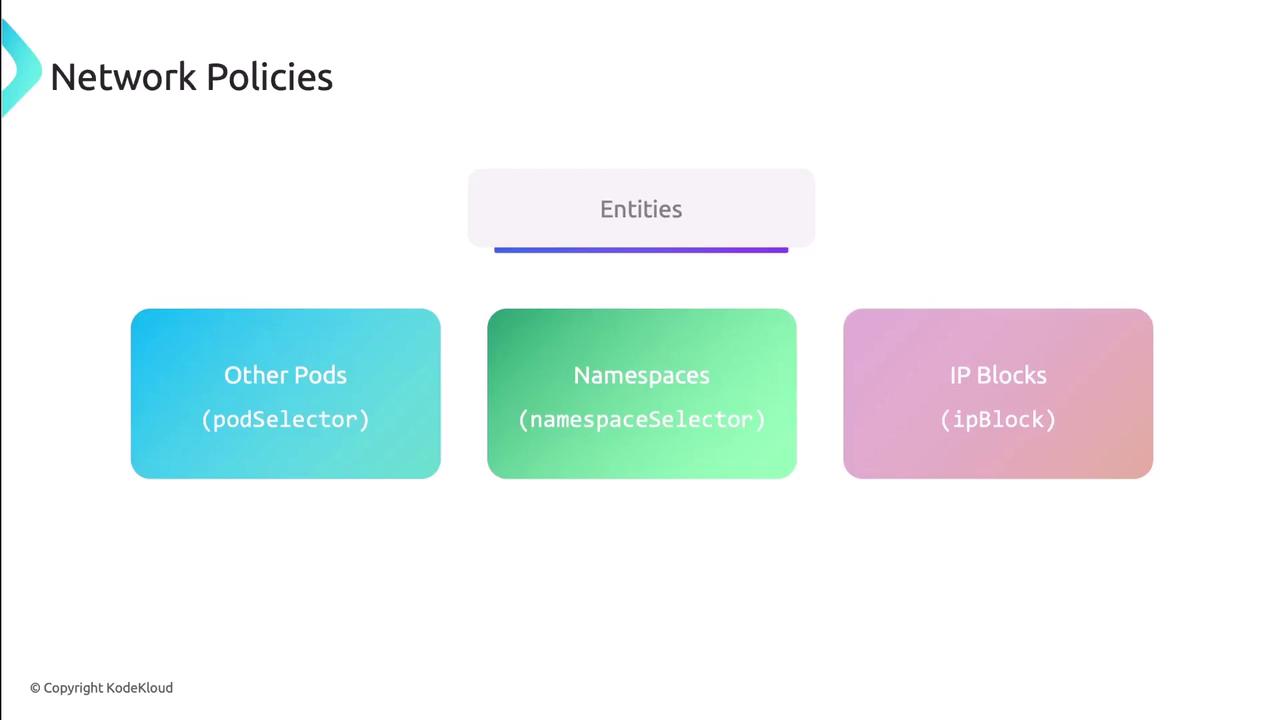
Key Entity Types
Network Policies match traffic based on three entities:| Entity Type | Selector Key | Description |
|---|---|---|
| Other Pods | podSelector | Select pods by labels |
| Namespaces | namespaceSelector | Select namespaces by labels |
| IP Blocks | ipBlock | Specify CIDR ranges and exclusions |
Defining a NetworkPolicy
ANetworkPolicy is a namespaced resource that applies to pods matching podSelector. You must also declare policyTypes (Ingress, Egress, or both) and the corresponding rules:
Entity Selectors and IP Blocks
Use label selectors for pods and namespaces:Layer 4 Ports and Protocols
Control ports and protocols (requires Kubernetes v1.25+ for port ranges):port: Single port or starting port of a rangeprotocol: TCP or UDP (defaults to TCP)endPort: End of port range (optional)
Default Policies
By default, all ingress and egress traffic is allowed. You can enforce a “deny all” or “allow all” baseline by using an emptypodSelector: {}.
An empty
podSelector: {} matches every pod in the namespace.Ingress Defaults
Egress Defaults
Benefits of Network Policies
- Granular security controls by workload
- Isolation in multi-tenant clusters
- Compliance with GDPR, HIPAA, PCI DSS
- Reduced attack surface by blocking unused paths
- Consistent enforcement across applications
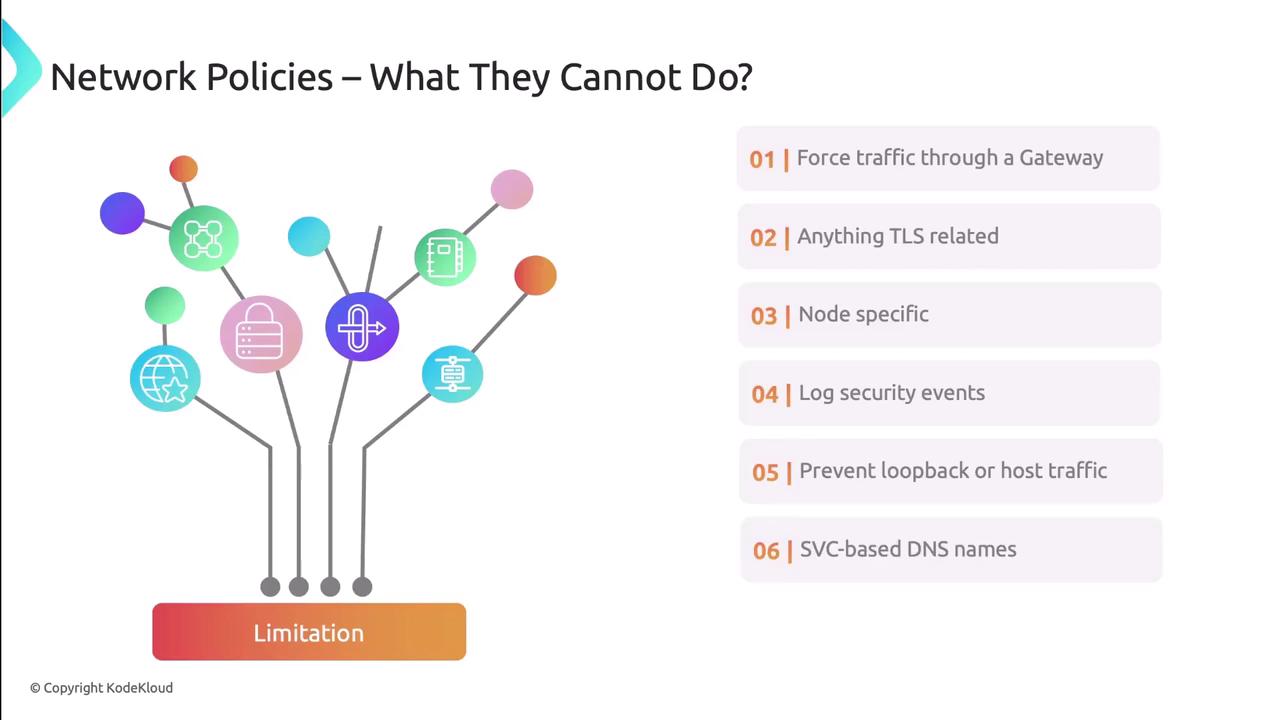
Limitations
Network Policies operate at layers 3 & 4 and have some constraints:- Cannot enforce a common gateway (service mesh can)
- No built-in TLS termination or deep packet inspection
- Cannot restrict host-level traffic or localhost loops
- No native allow/deny event logging
- Label-based only—cannot target Service objects
- No Layer 7 (HTTP/gRPC) filtering
CNI-Specific Enhancements
Several CNI providers extend Kubernetes Network Policies with advanced capabilities:| CNI Plugin | Advanced Features |
|---|---|
| Project Calico | Global policies, BGP routing, NetworkSets |
| Cilium | Layer 7 HTTP/gRPC filtering, eBPF datapath, Hubble insights |
| Istio | Service mesh policies, mTLS, ingress/egress gateways |
