Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
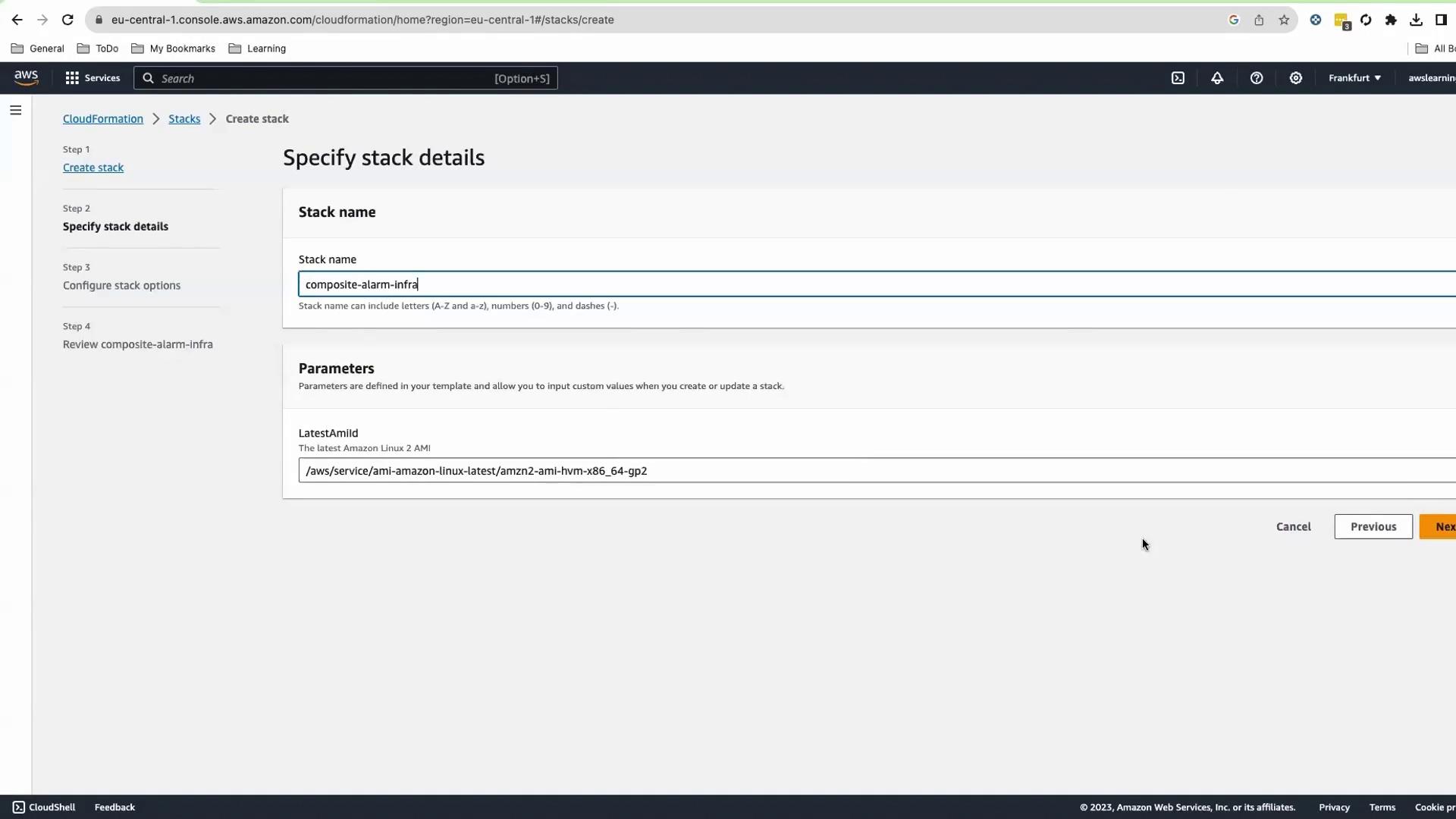
Ensure you define the
LatestAmiId parameter before deploying the stack. For example:CloudFormation Template Overview
This CloudFormation template provisions the following AWS resources:| Resource | Description | CloudFormation Type |
|---|---|---|
| Security Group | SSH access for EC2 instances | AWS::EC2::SecurityGroup |
| Launch Configuration | Launches t2.micro instances with latest AMI | AWS::AutoScaling::LaunchConfiguration |
| Auto Scaling Group (ASG) | Scales between 2 and 20 instances, 1-minute metrics | AWS::AutoScaling::AutoScalingGroup |
| Scale-Up Policy | Increases ASG capacity by 1 instance | AWS::AutoScaling::ScalingPolicy |
| CloudWatch Alarm: HighCPU | Triggers when CPU > 80% | AWS::CloudWatch::Alarm |
| CloudWatch Alarm: VeryHighCPU | Triggers when CPU > 90% | AWS::CloudWatch::Alarm |
| CloudWatch Alarm: HighASGSize | Triggers when ASG size > 10 | AWS::CloudWatch::Alarm |
Core Resources
CloudWatch Alarms Definition
| Alarm Name | Metric | Threshold | Period | Namespace |
|---|---|---|---|---|
| HighCPUUsage | CPUUtilization | 80% | 300s | AWS/EC2 |
| VeryHighCPUUsage | CPUUtilization | 90% | 300s | AWS/EC2 |
| HighASGSize | GroupTotalInstances | 10 | 300s | AWS/AutoScaling |
Outputs
Although the ASG can scale up to 20 instances, our threshold is set at >10 for demonstration.
Deploy the CloudFormation Stack
- Open the AWS CloudFormation Console.
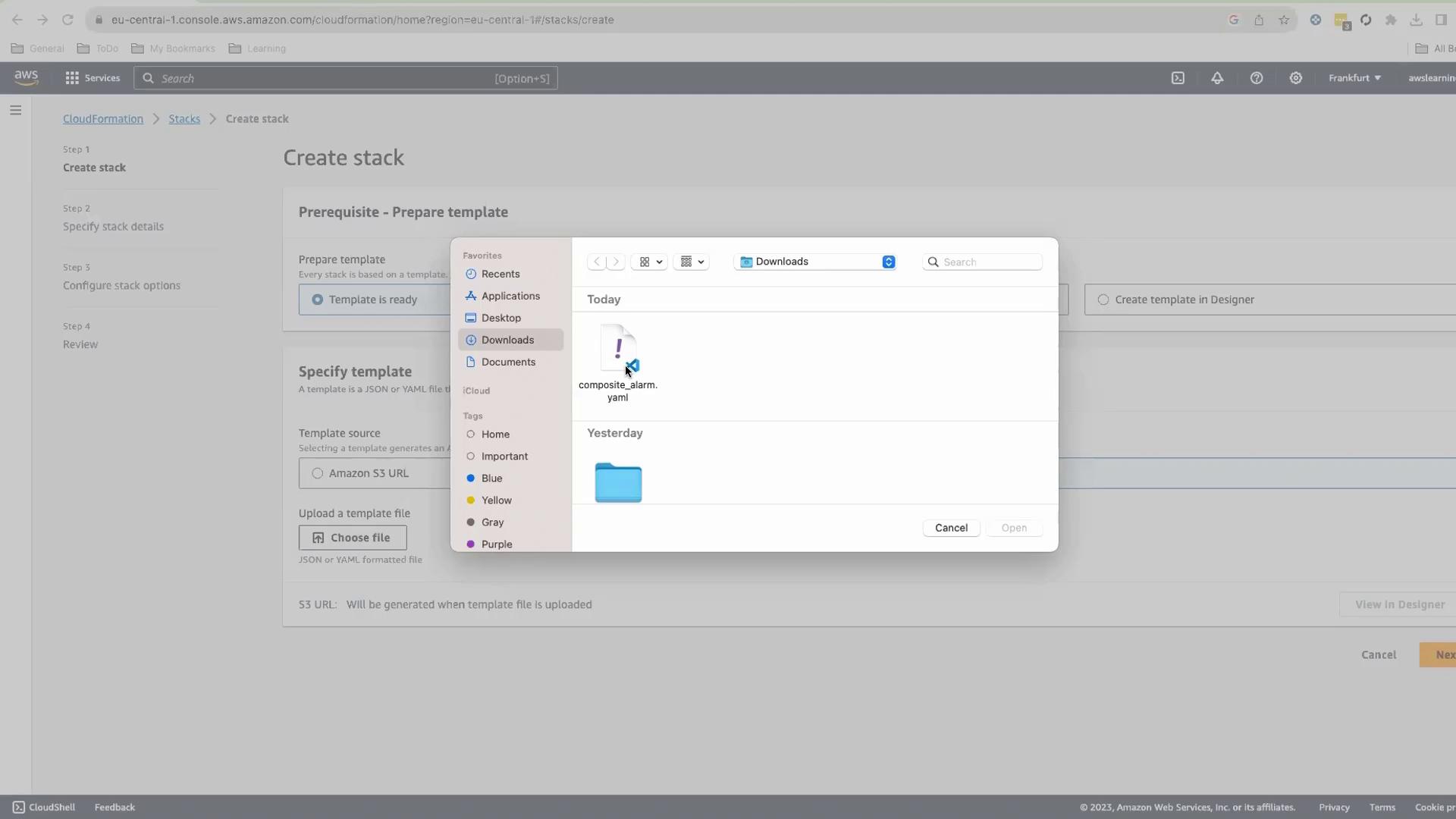
- Choose Create stack > Upload a template file, and select your
composite_alarm.yaml.
- Click Next, set Stack name to
CompositeAlarmInfra, and keep default parameters.
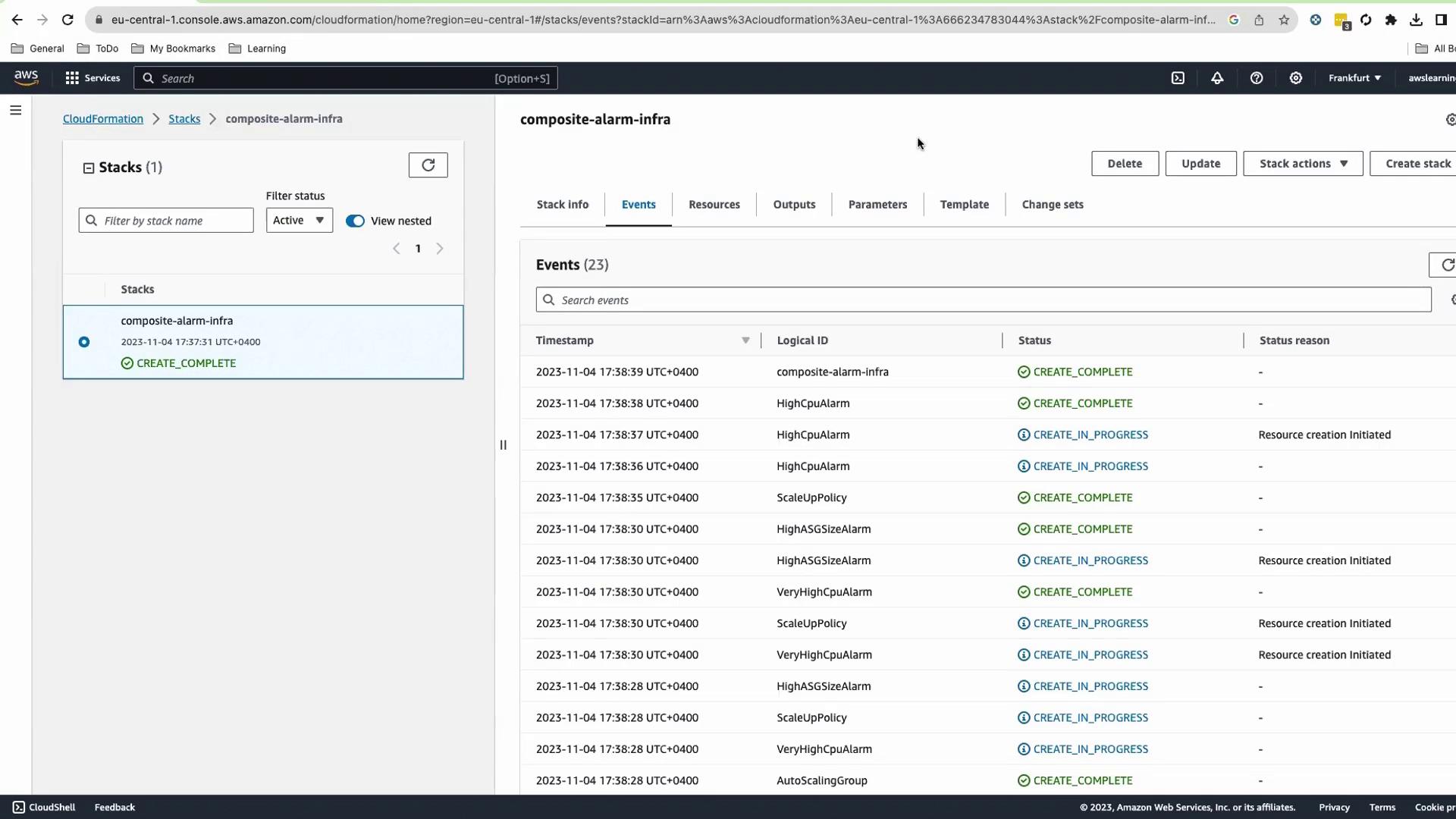
- Submit and wait ~4–5 minutes until status is
CREATE_COMPLETE.
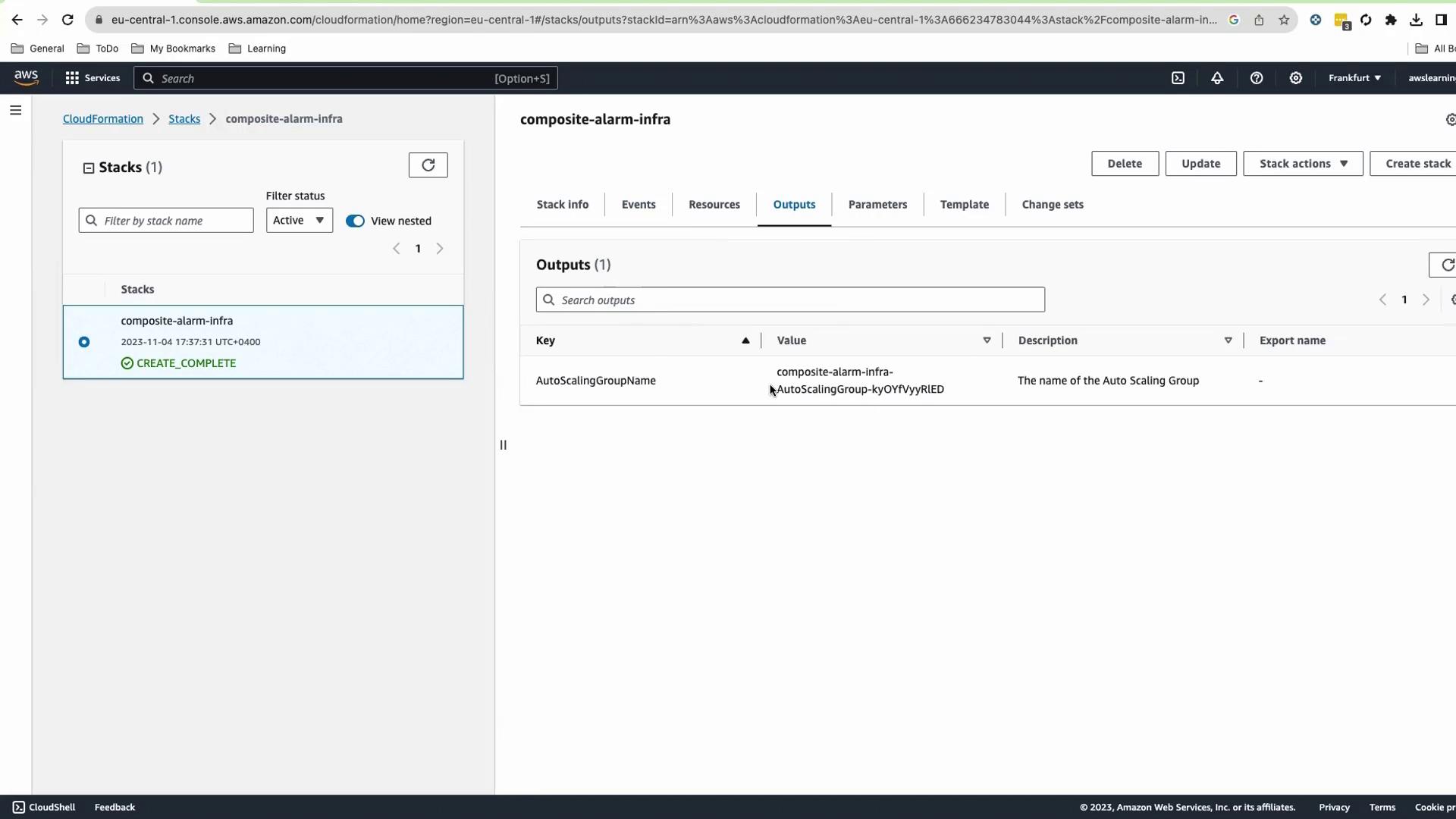
- On Outputs, copy the AutoScalingGroupName.
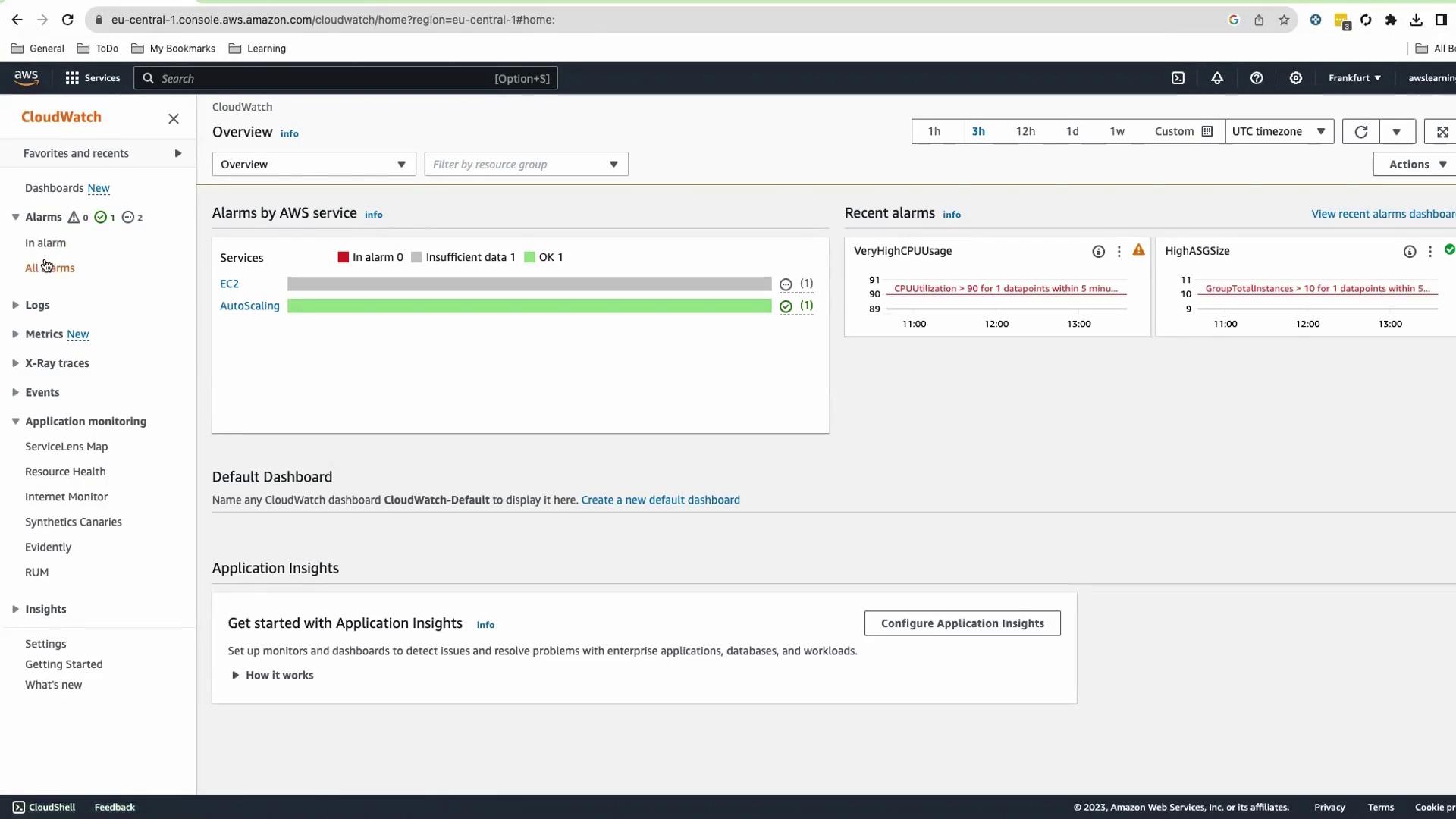
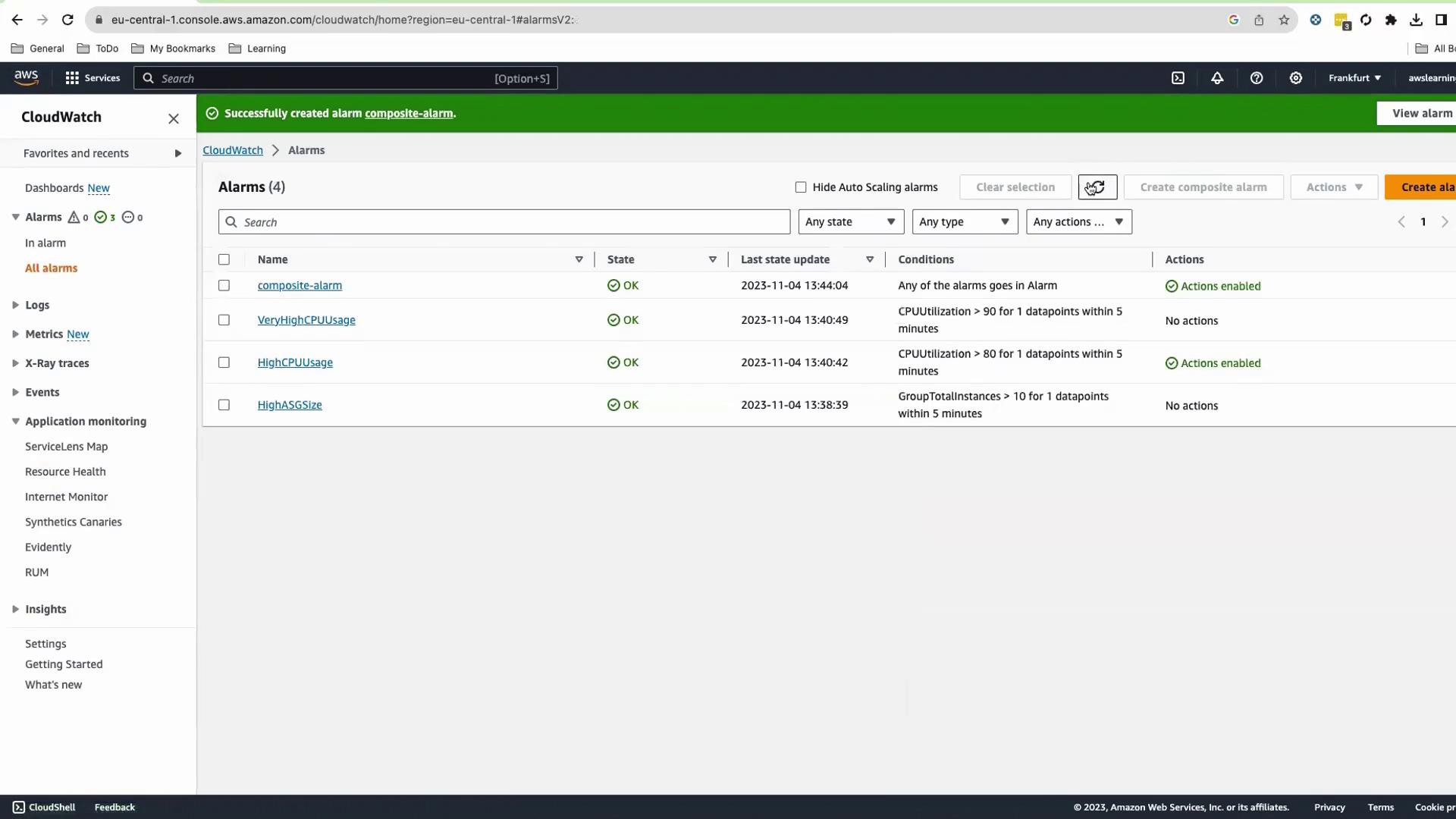
Verify CloudWatch Alarms
Navigate to CloudWatch > Alarms. You should see:- HighASGSize
- HighCPUUsage
- VeryHighCPUUsage
OK or Insufficient Data.
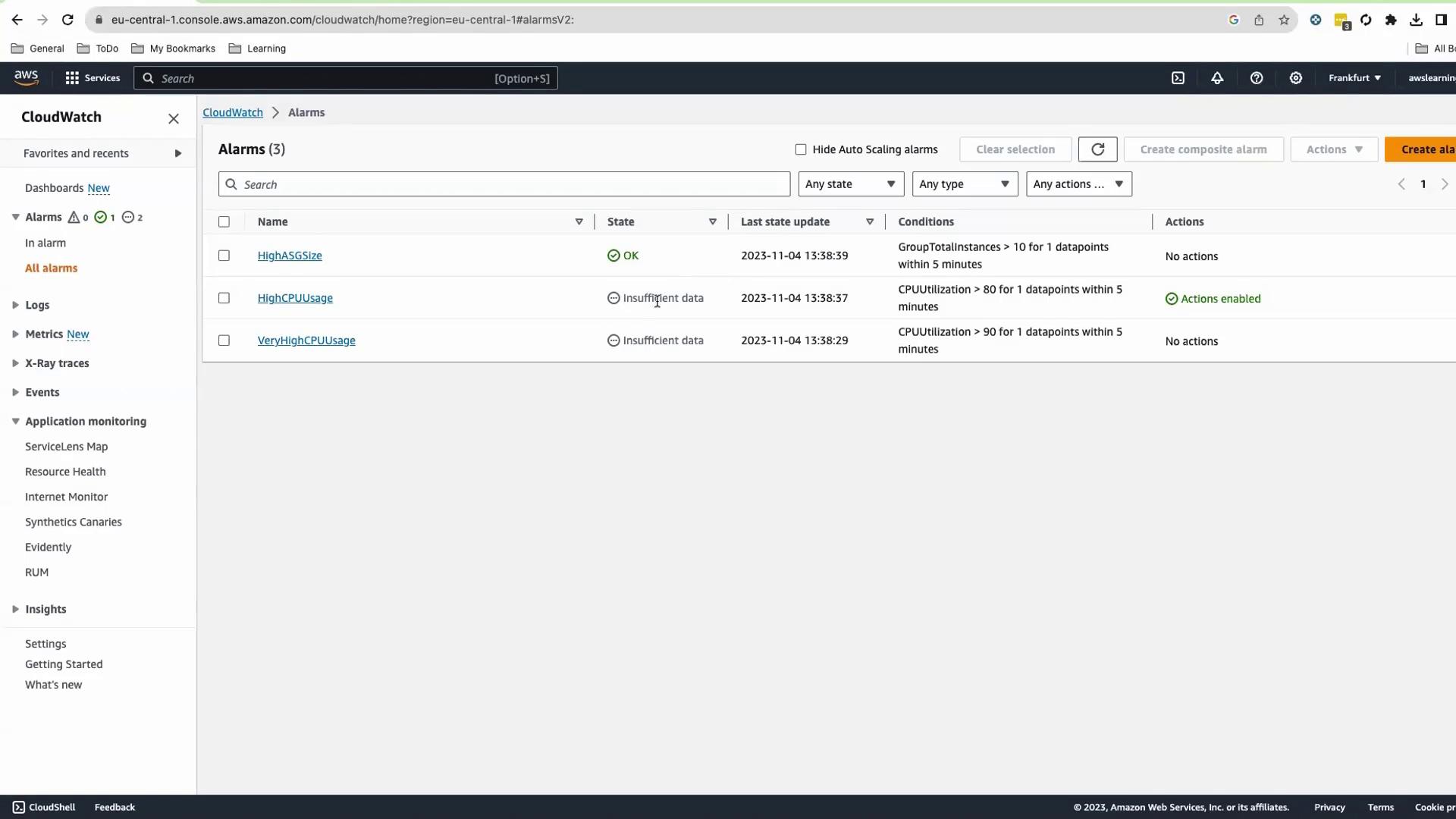
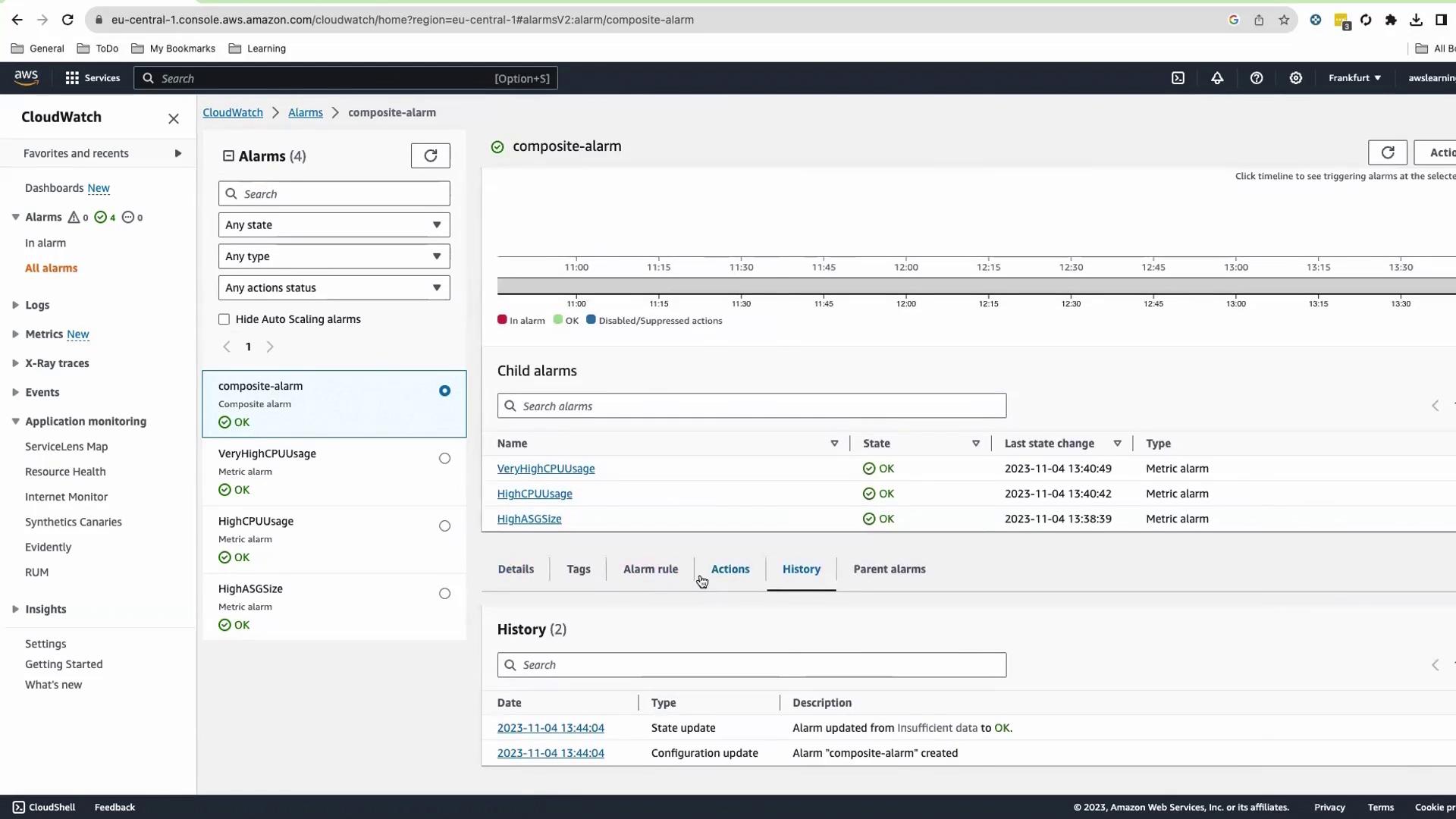
Create the Composite Alarm
- Select the three child alarms.
- Go to Actions > Create composite alarm.
- Define the rule:
- Configure notifications (e.g., an SNS topic) and an optional suppressor alarm.
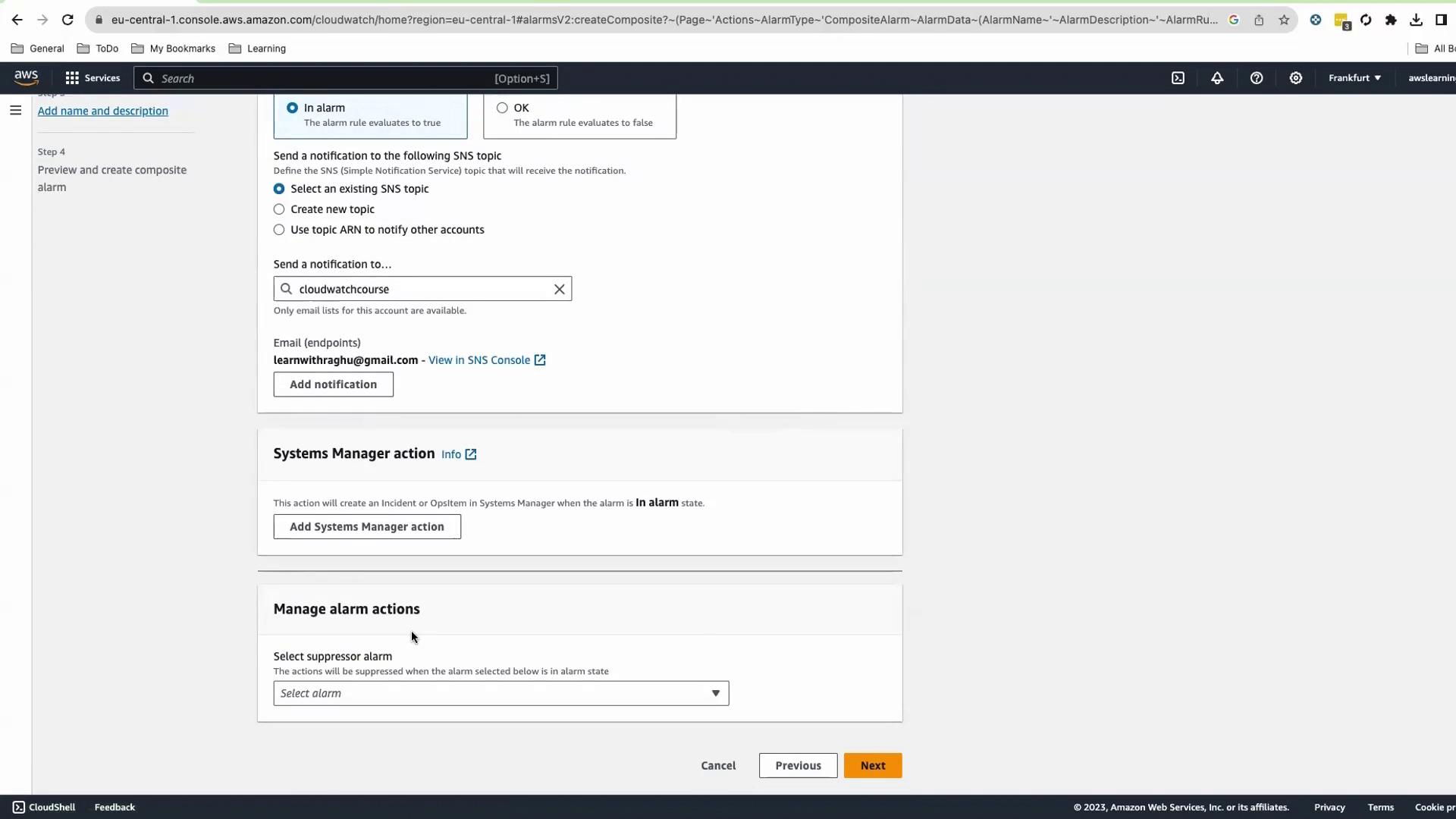
- Enter Name and Description (Markdown supported).
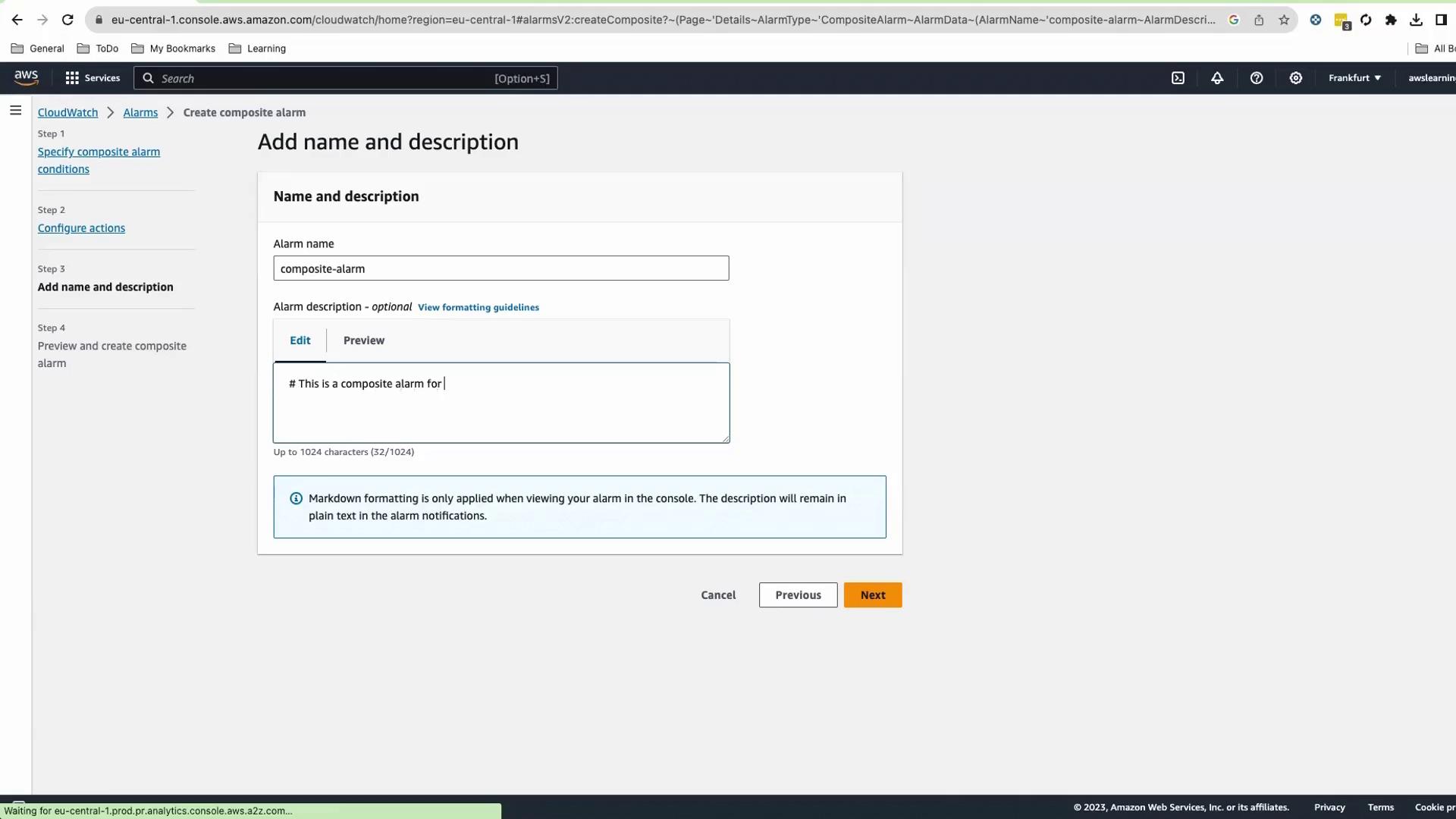
OK state.
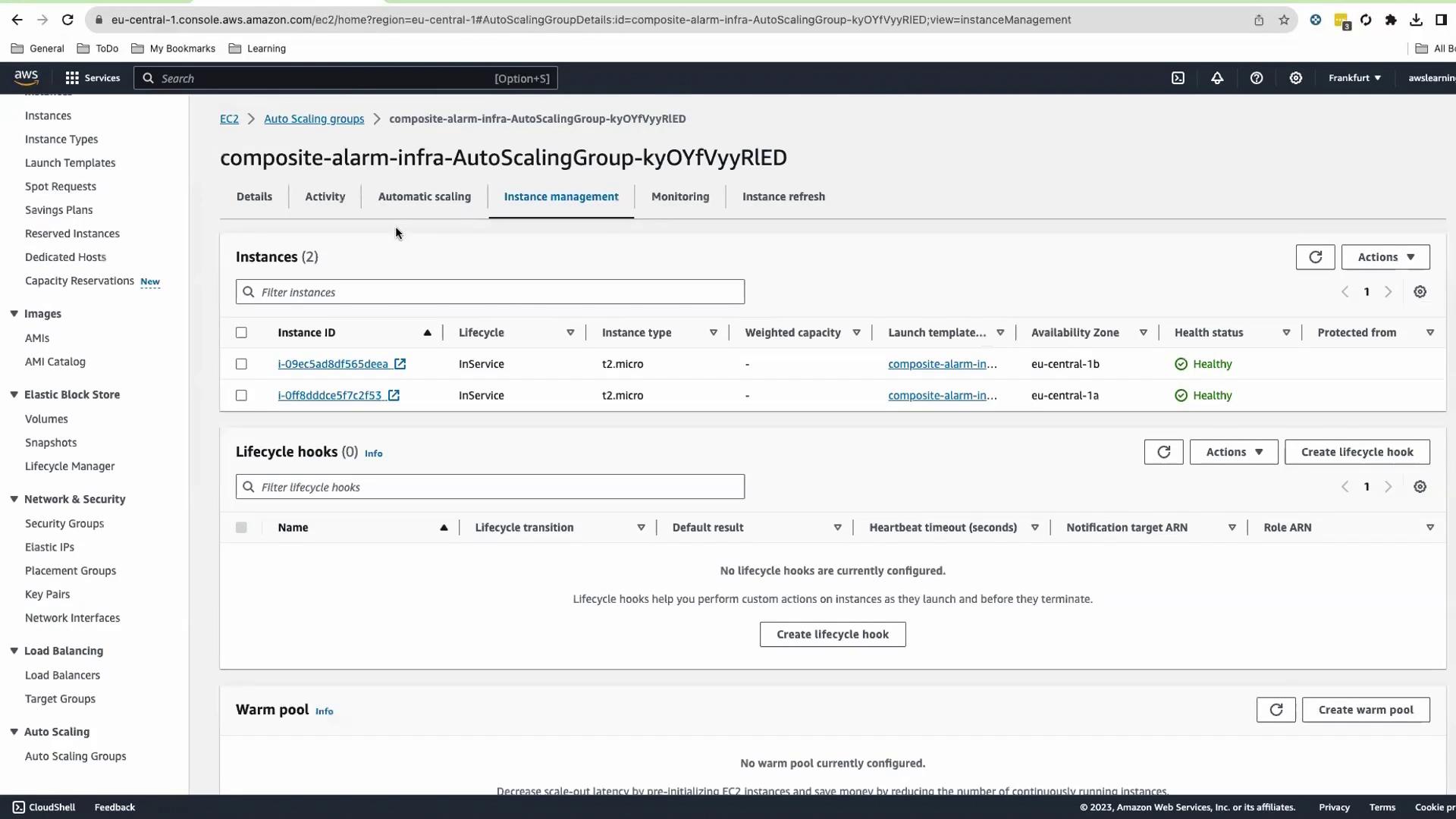
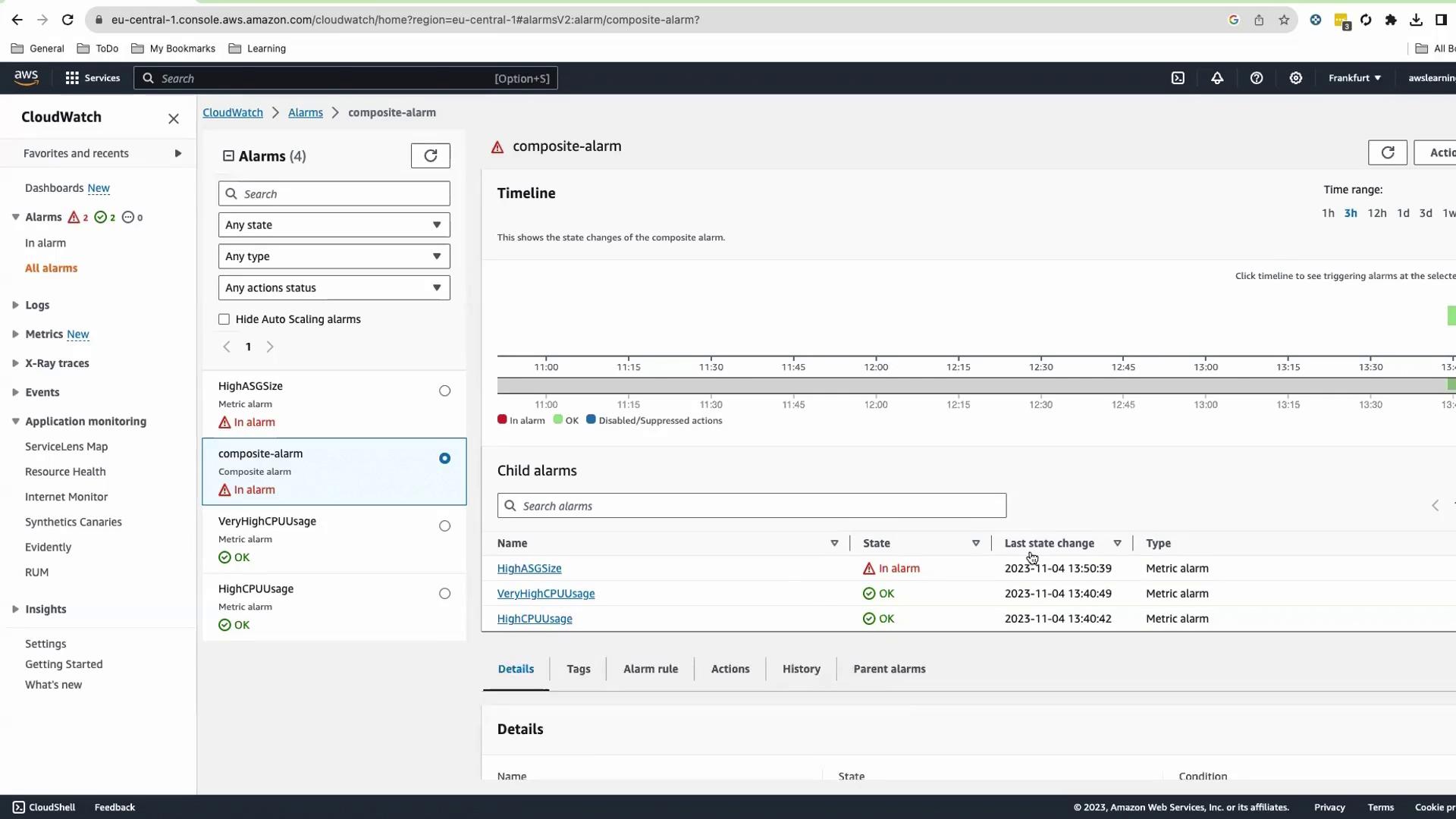
Test the Composite Alarm
To trigger the alarm:- In the EC2 Console, open your ASG > Details > Edit.
- Set Min and Desired capacity to
12, then save.
Cleanup
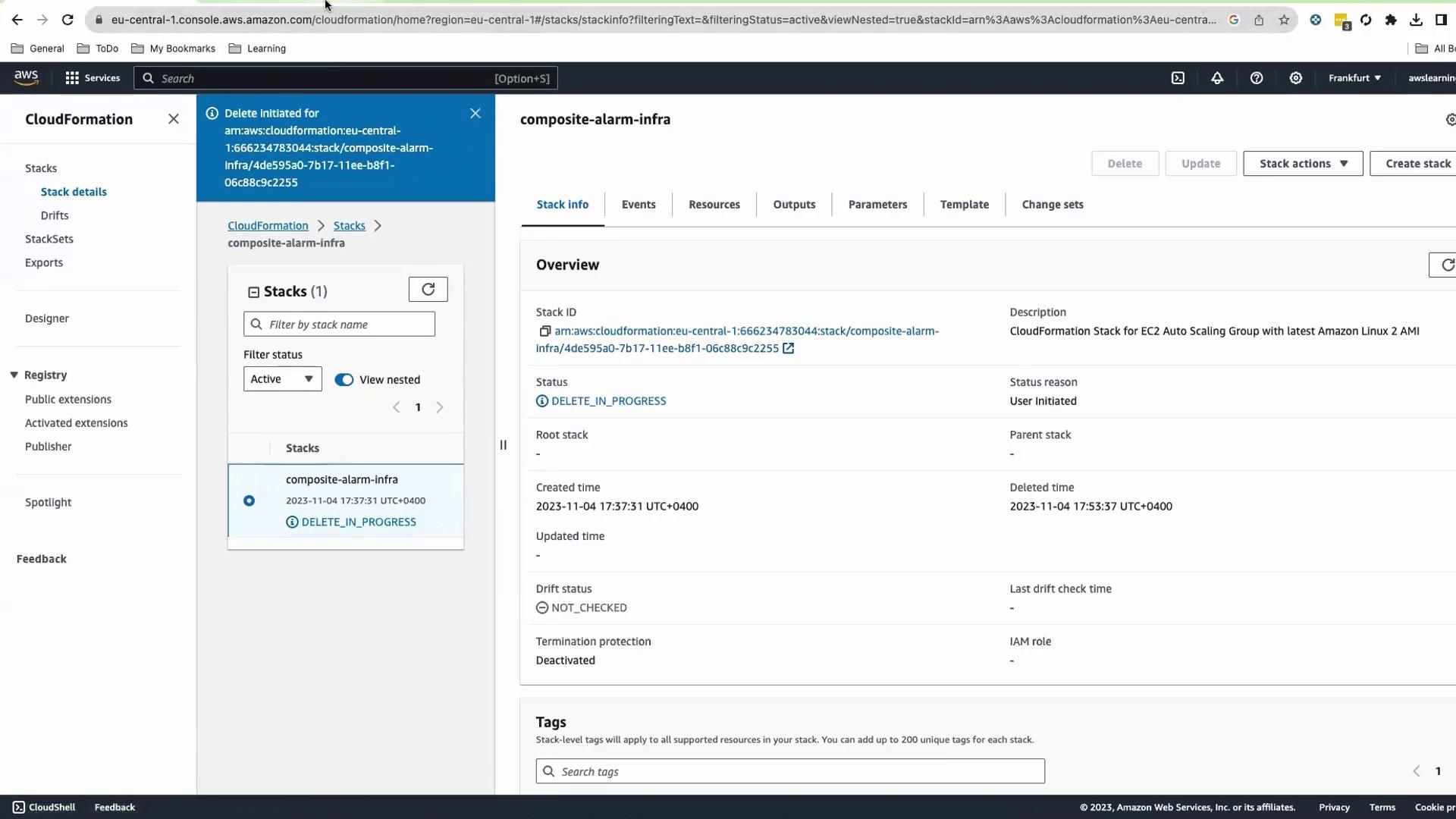
- Delete the CloudFormation stack.
- In CloudWatch, select the composite alarm and choose Actions > Delete.
Deleting the composite alarm must be done manually—it is not removed by the CloudFormation stack.