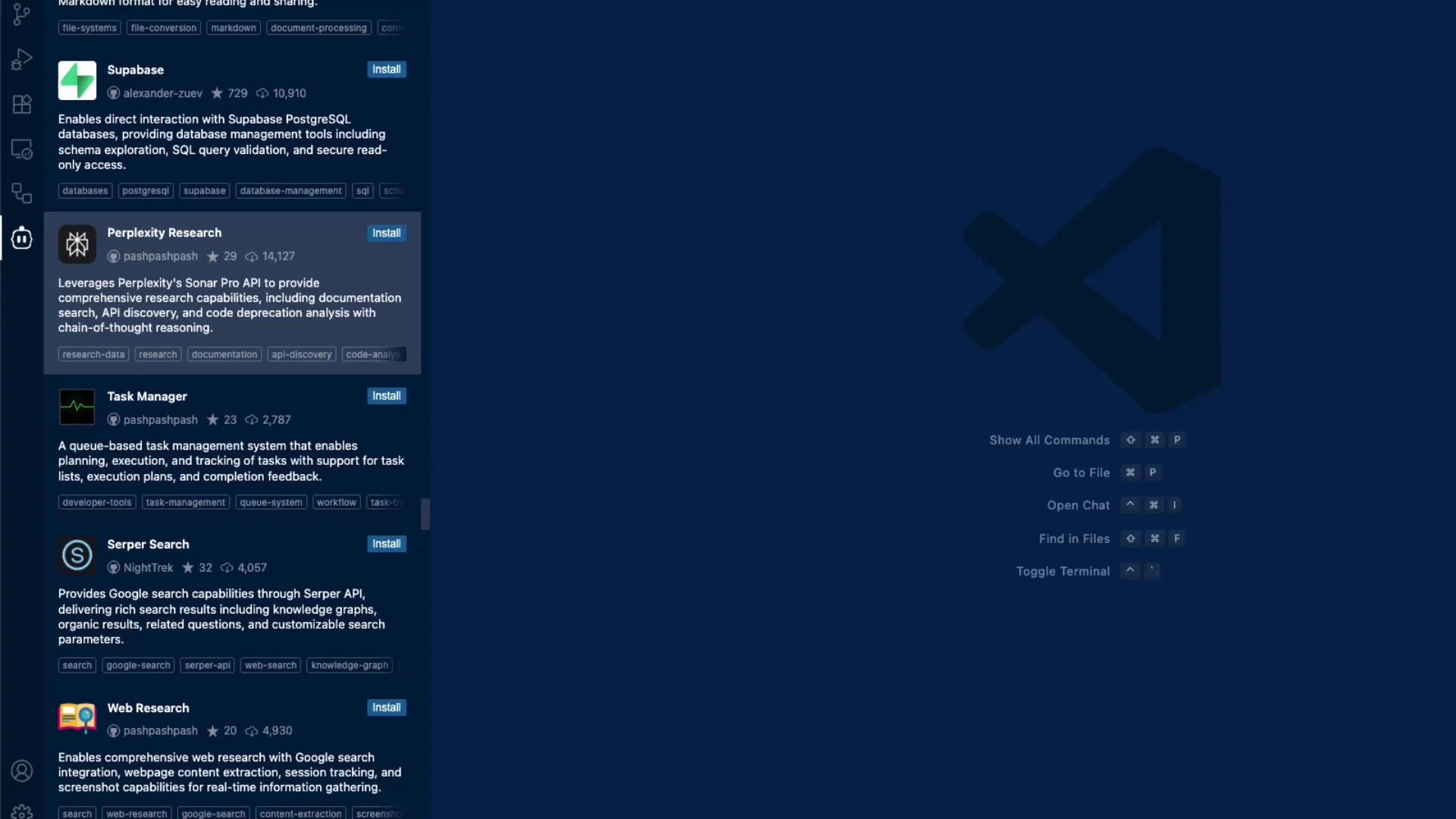
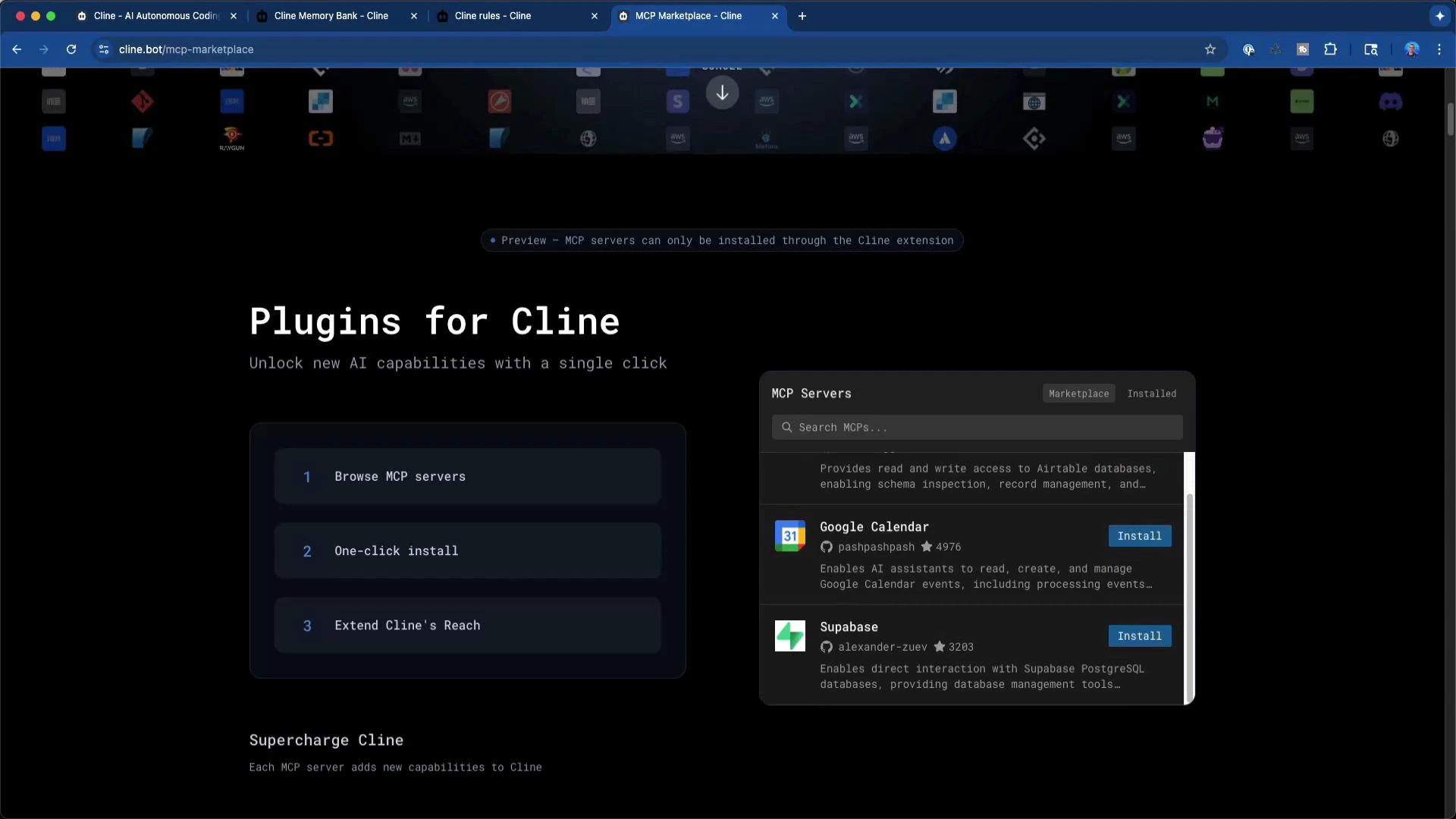
In this lesson we’ll explore MCP servers — a flexible, consistent way to connect external services to your LLM workflows. MCP servers expose a common protocol so language models and tools can interact with APIs, databases, observability systems, calendars, and other services. Because they standardize communication, MCP servers make it easy to mix APIs, LLMs, and tooling in a single, predictable interface. There is a large catalogue of MCP servers available. Popular examples include Perplexity Research (excellent for web research), Supabase (hosted databases), Prometheus Query (metrics), Cost Explorer, and many utility tools like Dice Rollers. You can add engines such as Perplexity Research to improve research capabilities or install small tooling servers for utility tasks.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
| Category | Use cases | Examples |
|---|---|---|
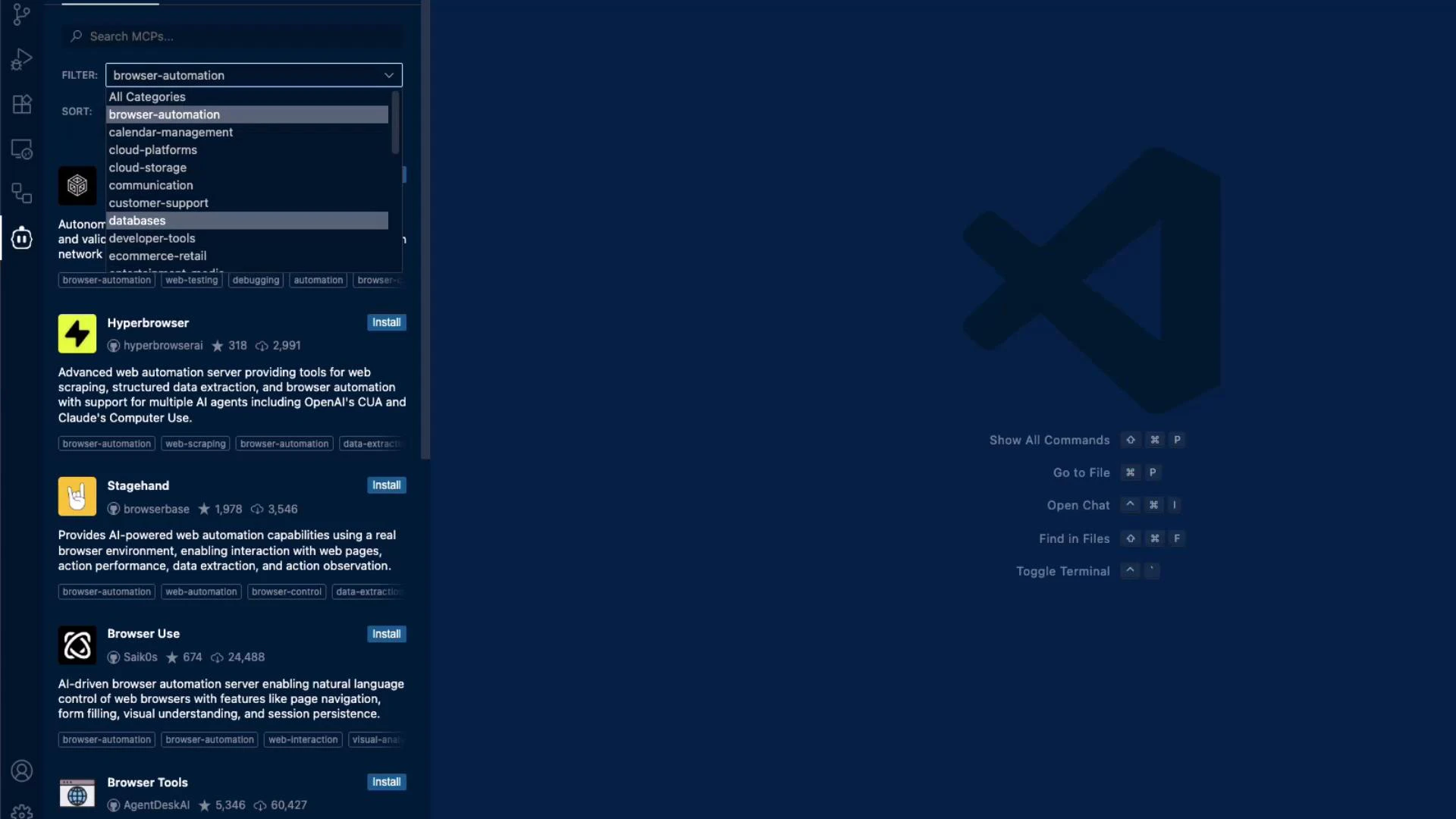
| Browser Automation | Web scraping, E2E testing, UI automation | Hyperbrowser, Stagehand |
| Calendar Management | Read/write calendar events, scheduling | Google Calendar MCP |
| Cloud Platforms | Cloud APIs, resource management | AWS, GCP, Azure MCPs |
| Communication | Messaging, notifications | Slack, Teams MCPs |
| Developer Tools | Code search, task automation | Task Manager, CI integrations |
| Databases | Query and manage data | Supabase, Neo4j MCPs |
| Observability | Metrics, logs, tracing | Prometheus Query, Cost Explorer |
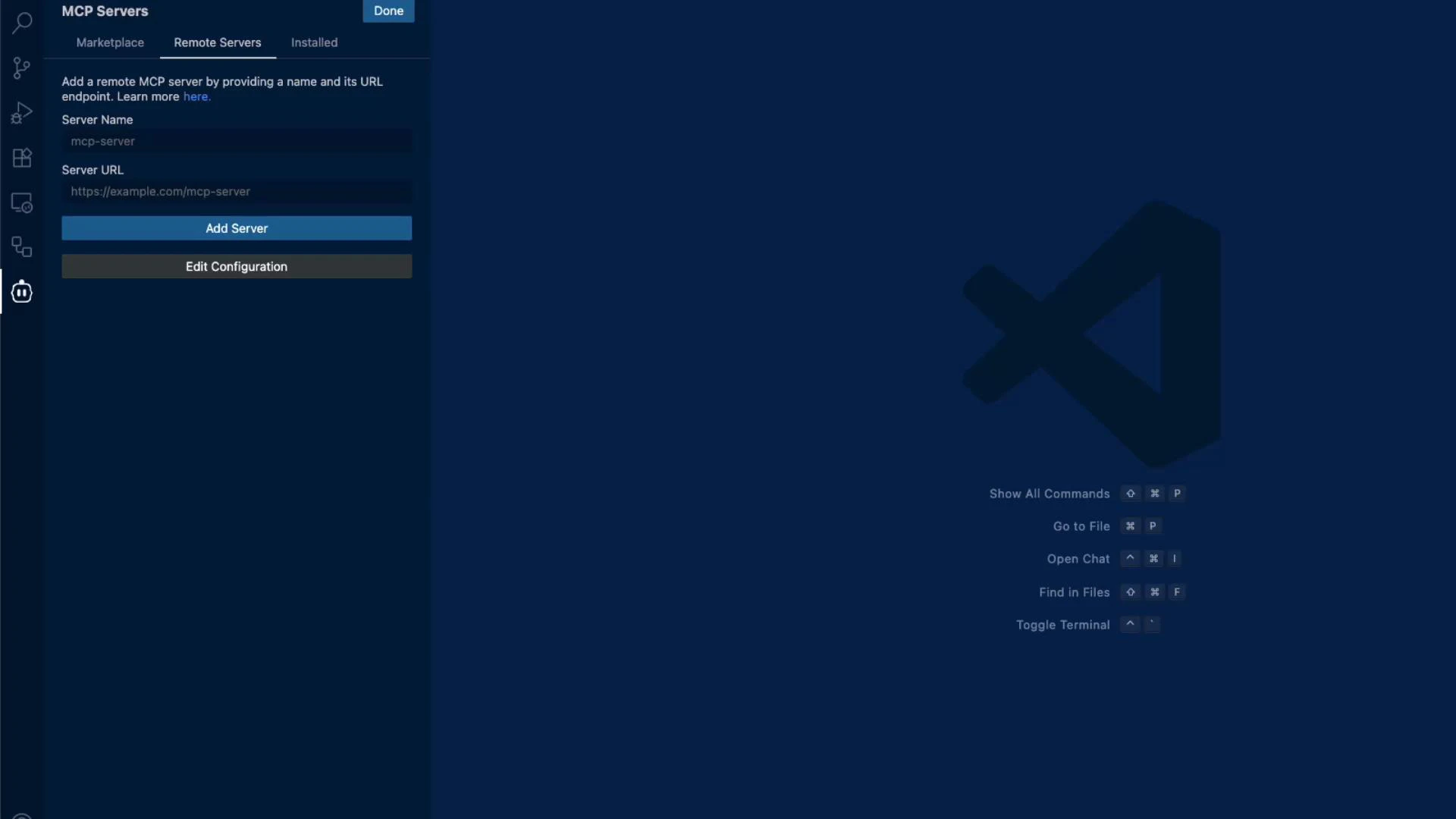
mcpServers section to your workspace configuration. This registers server names, endpoints, and keys so your tools and workflows can call them consistently. A minimal workspace example:
Use the marketplace to preview MCP servers and review integration documentation before adding them to your workspace — it helps ensure you configure required credentials and scopes correctly.
- Only add endpoints you trust; validate the host and certificate.
- Store API keys and secrets in secure vaults or environment variables, not in public repositories.
- Limit scope and permissions of tokens to the minimum required.
- Use network controls (VPCs, IP allowlists) for self-hosted MCP endpoints.
Be careful when adding remote MCP servers: ensure the endpoint is trusted, use secure credentials, and verify network exposure. Do not expose sensitive API keys in public repositories or shared workspace files.
- Verify provider documentation and required credentials.
- Confirm required OAuth scopes or API key permissions.
- Test the endpoint in a staging workspace before using in production.
- Rotate and audit keys regularly.
- Perplexity Research: https://www.perplexity.ai/
- Supabase: https://supabase.com/
- Prometheus documentation: https://prometheus.io/docs/
- MCP servers standardize how LLMs and tools access external services, making integrations predictable and reusable.
- Discover servers via the IDE, filter by category, or browse the Cline Marketplace.
- Add private or self-hosted servers via the workspace
mcpServersconfiguration and follow security best practices when registering endpoints and credentials.