This lesson summarizes a comprehensive authentication security review of an Express.js login demo (Postgres + JWT). The review was guided by a structured audit prompt that enumerates common pitfalls, remediation guidance, and test recommendations. Below you’ll find the audit prompt used to drive the analysis, an executive summary, prioritized findings, concrete remediation snippets, recommended tests, and operational next steps.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Note: the audit focused on authentication hardening patterns relevant to most Express-based demos: password hashing, JWT handling, refresh-token rotation, session invalidation, brute-force protection, input validation, and secure cookie/CSRF practices.
Structured audit prompt (representative)
This article focuses on actionable fixes for Express.js authentication flows: secure password storage, robust JWT handling, refresh-token rotation, brute-force defenses, safe cookie/CSRF configuration, and input validation. Use the snippets below as minimal drop-in improvements and adapt them to your project structure.
Executive summary (high level)
- Primary focus: authentication flow hardening for an Express demo with PostgreSQL and JWTs.
- Main risks found (representative):
- Hard-coded or weak JWT secret — Critical
- Plaintext password storage or missing hashing — Critical
- Missing brute-force/rate-limiting on login/reset — High
- Long-lived access tokens / no refresh-token rotation — High
- Insufficient input validation / potential account enumeration — Medium-High
- Recommended priorities:
- Replace weak/hard-coded secrets; use environment or secret manager and rotate keys.
- Ensure passwords are hashed (bcrypt with async salts ≥12) before persistence.
- Implement RT rotation + reuse detection, shorten access TTL.
- Add rate-limiting and consistent, generic error messaging to prevent enumeration.
- Harden cookies, CSRF protections, and input validation.
Key checks — what to inspect and why
| Area | Why it matters | Quick check |
|---|---|---|
| Password hashing | Prevents exposure of plaintext credentials on breach | Ensure bcrypt async hash on register and update, salt rounds ≥ 10 (12 recommended) |
| JWT management | Weak secrets enable token forgery; alg/config misuse leads to bypass | No hard-coded secrets; env-managed keys; explicit verify options (alg, iss, aud) |
| Token TTLs & rotation | Limits window of compromise; rotation reduces risk of leaked RTs | Access 5–15m; RT 7–30d with rotation on use, hashed RTs at rest |
| Refresh token strategy | Proper rotation + reuse detection prevents session hijacking | Track RT per device, rotate on use, revoke family on reuse |
| Session invalidation | Users must be logged out on password reset/change | Maintain session version or token revocation list invalidated on password change |
| Brute force & enumeration | Prevents automated account takeover and username discovery | Per-user+IP rate limits (Redis), generic errors, timing stability |
| Password reset security | Prevents token leakage and reuse | One-time tokens, short TTL, hashed at rest, do not log tokens |
| Injection & input validation | Prevents data exfiltration and privilege elevation | Parameterized queries, schema validation (zod/joi/express-validator) |
| Cookie & CSRF | Protects session tokens from XSS/CSRF | HttpOnly, Secure, SameSite, CSRF on state-changing endpoints |
| Logging & telemetry | Redaction prevents credential leakage in logs | No logging of passwords/tokens/PII; structured logs and alerting |
- bcrypt: https://www.npmjs.com/package/bcrypt
- Redis: https://redis.io
- express-rate-limit: https://www.npmjs.com/package/express-rate-limit
Example findings (representative)
-
Weak JWT Secret Management
- Severity: Critical | CWE-798 (Hard-coded Credentials)
- Evidence:
.envincludedJWT_SECRET=your_jwt_secret_key_here. - Remediation: Replace with a cryptographically strong secret stored in environment or secret manager; rotate keys and use asymmetric keys (RS256/ES256) if feasible.
-
No password hashing on registration
- Severity: Critical
- Evidence: Registration flow persisted plaintext password.
- Remediation: Use bcrypt.hash() (async) with salt rounds ≥ 12 before persisting.
-
Missing brute force protection on login
- Severity: High
- Evidence: No rate limiting or lockouts on login/reset endpoints.
- Remediation: Add express-rate-limit with Redis backing; block after threshold and present generic error messages.
-
Excessive token lifetimes / no RT rotation
- Severity: High
- Evidence: Long-lived access tokens; refresh tokens not rotated.
- Remediation: Shorten access TTL, implement RT rotation with reuse detection and per-device tracking.
Concrete remediation snippets
Place these snippets into appropriate files (e.g.,routes/auth.js, middleware/, or a config file). They are minimal and intended to be adapted to your project style and error handling.
1) Register with bcrypt hashing (async)
2) Rate limit login attempts (express-rate-limit + Redis)
3) HTTPS redirect middleware (enforce TLS in production)
4) Generic server-side error logging and client response
5) Strong JWT verification (explicit algorithms and claim checks)
6) Password validation rules (express-validator)
Immediate actions (next 48 hours): replace weak/hard-coded JWT secrets, ensure passwords are hashed before persistence, add login rate-limiting, shorten access token TTL, and implement refresh-token rotation. These address the highest-impact findings.
Test recommendations (examples)
- Refresh token reuse detection (pseudo-test)
- Brute force protection test
- Password reset flow test
- Create a short-TTL reset token, assert it’s hashed at rest, use once, and verify it’s invalid afterwards.
Report generation & operational checklist
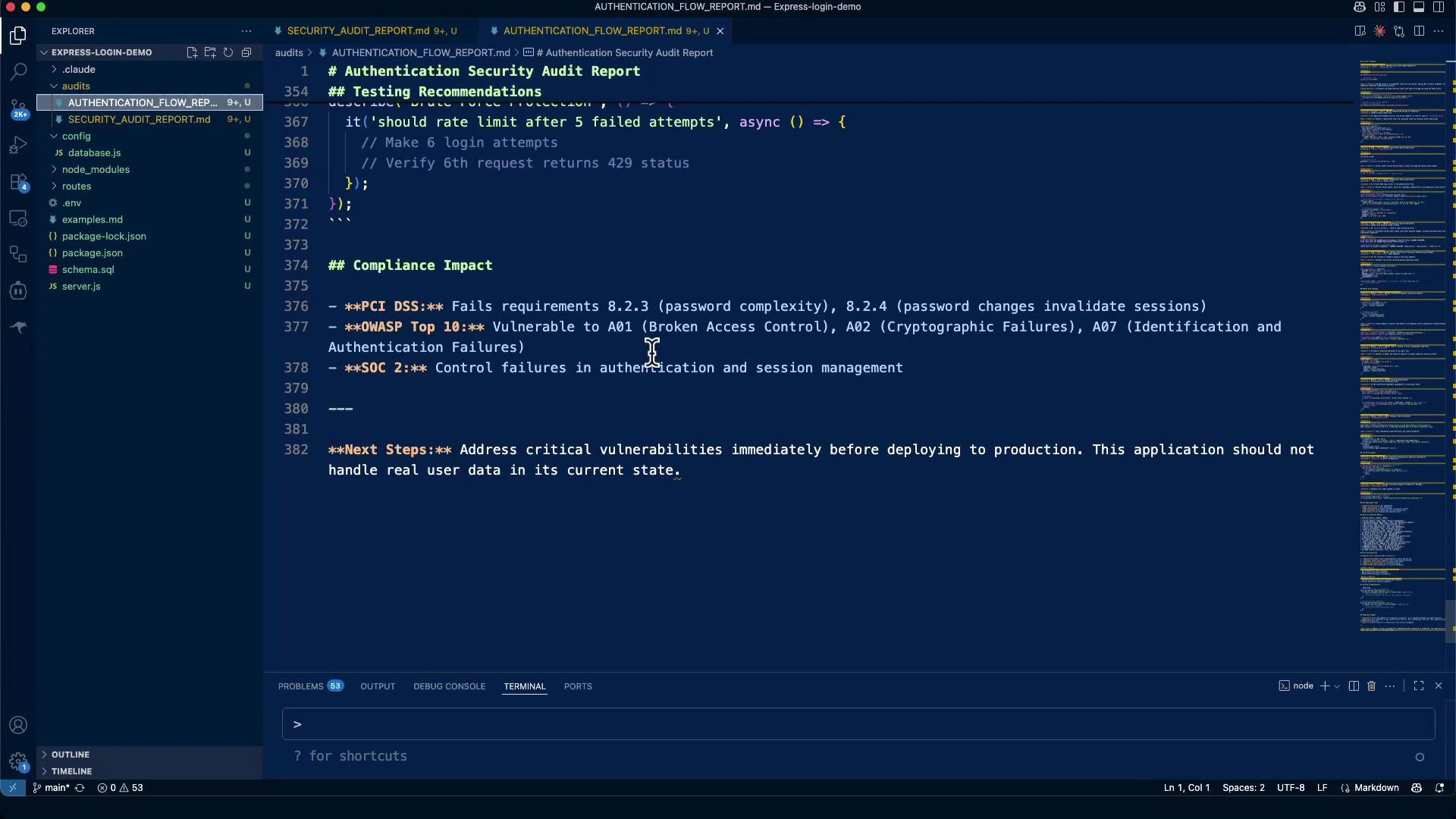
The audit output should be committed as a structured markdown report (example filename:audits/AUTHENTICATION_FLOW_REPORT.md) and include:
- Executive summary and risk score
- Critical & high severity findings with CWE references
- Evidence (file/line references where available)
- Minimal remediation snippets and suggested timelines:
- Immediate (48 hours): replace JWT secret with strong key; add bcrypt hashing on registration and updates; add brute-force protection; shorten access token TTL; add refresh-token rotation.
- Within 1 week: implement session invalidation on password change; comprehensive input validation; JWT middleware and claim verification.
- Within 1 month: logging redaction; monitoring/alerting for RT reuse; penetration testing and key rotation procedures.
- Tests to validate fixes (RT reuse, invalidation after password change, bruteforce detection).
- Checklist diff showing before/after and file-level changes.
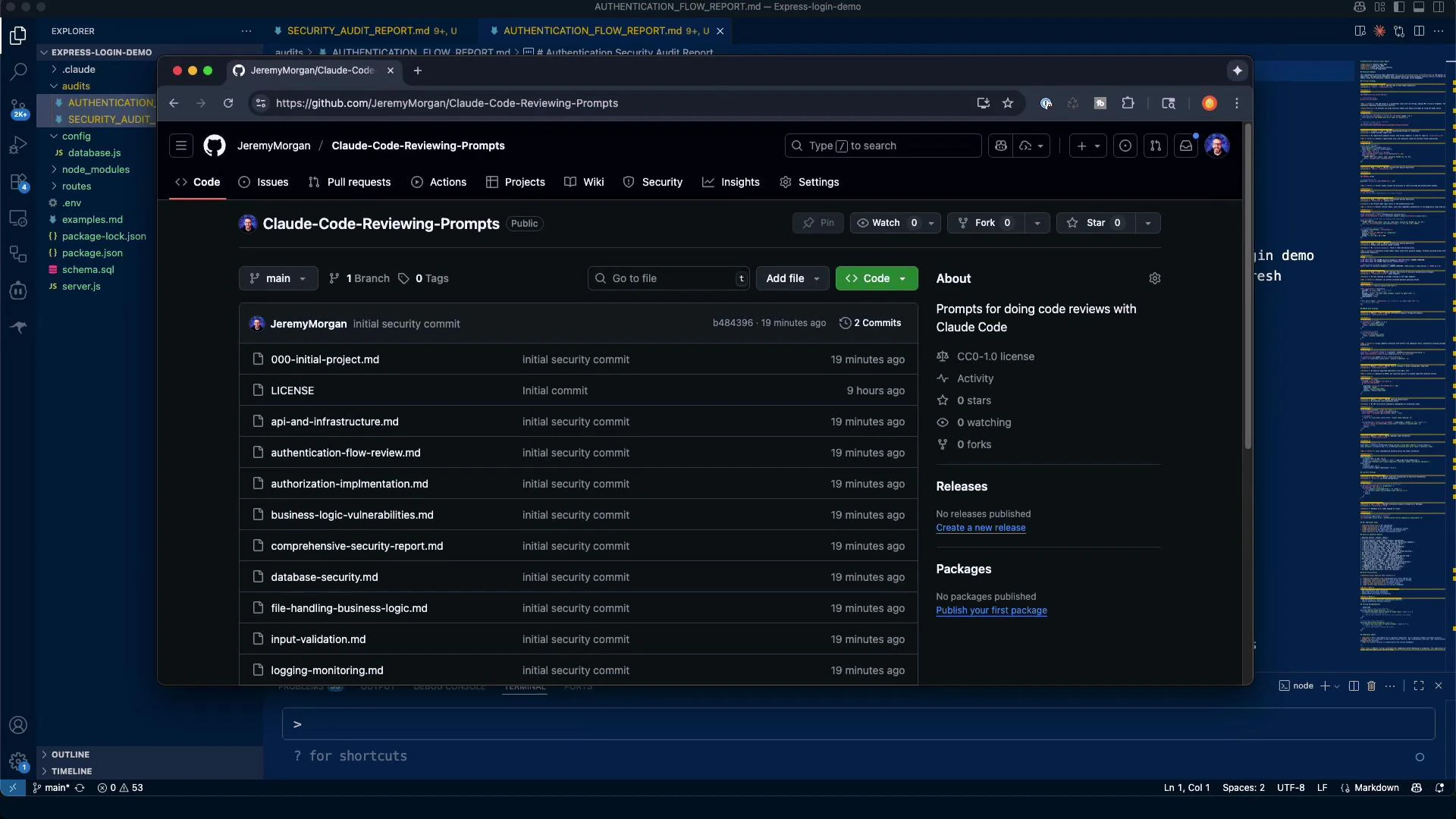
Where to find prompts and next steps
All prompts used for these reviews were kept in the repository for reuse and iteration. Recommended operational next steps:- Replace placeholder secrets with production-grade secrets (secrets manager or KMS).
- Implement the code fixes above and run the tests suggested.
- Add monitoring and alerting for refresh-token reuse and anomalous auth patterns.
- Schedule a secondary audit after fixes are merged and tests pass.
Final notes
- Not every check applies to every application. Mark items “Unable to Verify” where required context or files are missing.
- Prioritize concrete, minimal fixes that can be validated with tests and rolled out progressively.
- Preserve the practice of never exposing secrets or tokens in logs and enable key rotation and monitoring.