In this lesson we perform an initial security audit of an Express login demo using Claude Code. The goal is to generate a repeatable, shareable Markdown audit you can review, convert (Google Docs / PDF / Word), and hand off to developers for remediation. This workflow will help you:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Create an
audits/folder to store findings - Run a project-structure analysis to identify entry points, routes, middleware, DB connections, and more
- Optionally run
npm auditto detect vulnerable dependencies - Produce
audits/SECURITY_AUDIT_REPORT.mdcontaining a high-level risk assessment and recommended fixes
What you’ll produce
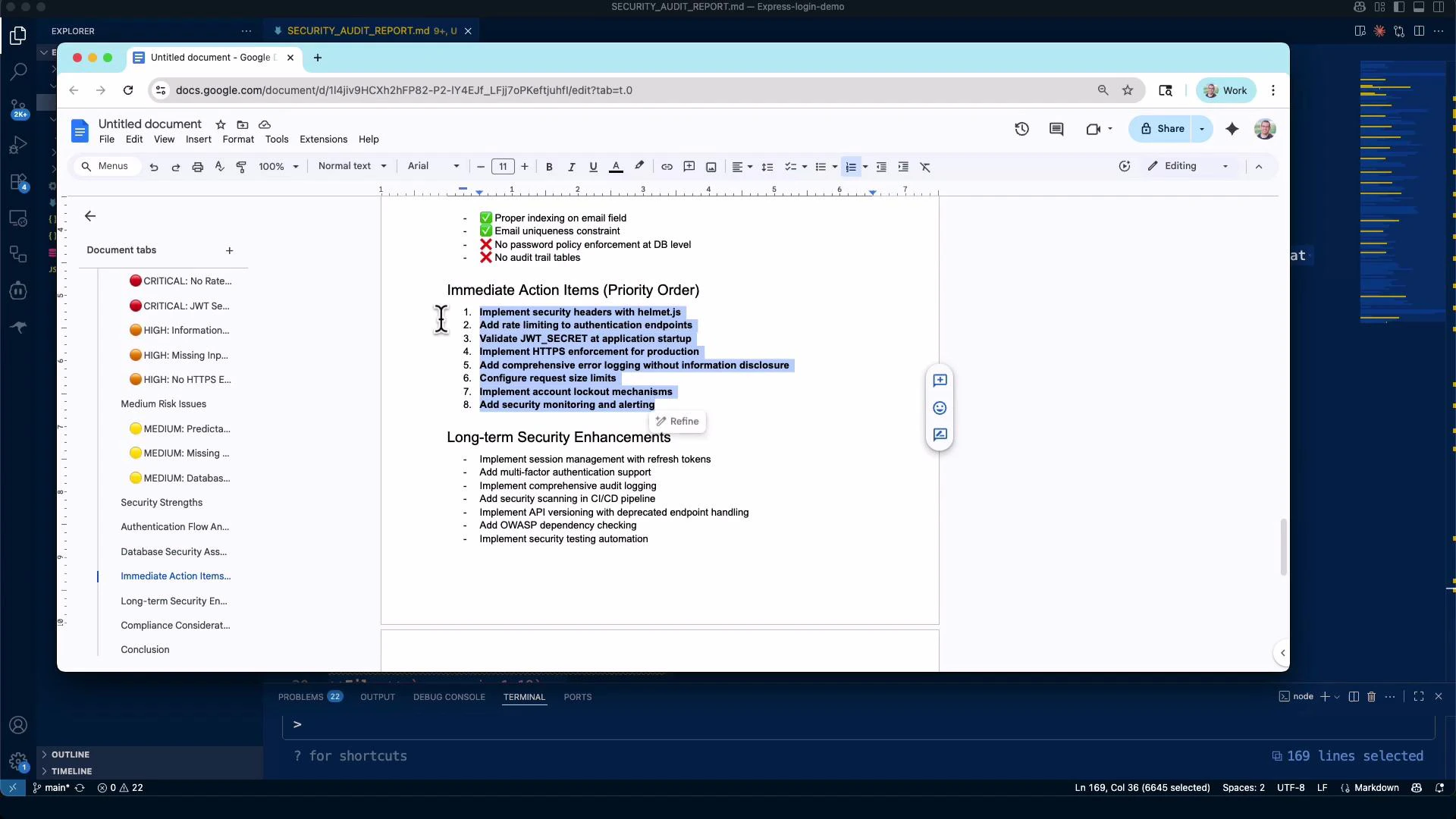
- audits/SECURITY_AUDIT_REPORT.md — a structured Markdown audit with an executive summary, project structure analysis, prioritized findings (Critical/High/Medium), and remediation guidance.
- Optional: artifacts from
npm auditor other tooling (dependency vulnerability reports).
Create the audits folder and run the initial analysis
Create a folder to store audit artifacts and outputs:package.json, server.js, routes/*, middleware/*, config/database.js, schema.sql) and may prompt to run commands such as npm audit to detect vulnerable dependencies.
If you choose to run interactive commands (like
npm audit) from the audit environment, ensure you understand any npm scripts or postinstall hooks. Running tools may modify lockfiles or node_modules—use a safe environment or a CI job when possible.audits/SECURITY_AUDIT_REPORT.md and open it for review.
Example: Generated Security Audit Report (excerpt)
Claude Code produces a structured Markdown report. Below is an excerpt of a generatedaudits/SECURITY_AUDIT_REPORT.md to illustrate the expected format and level of detail.
Quick summary table (example)
| Outcome | Why it matters | Action |
|---|---|---|
| Missing security headers | Exposes app to XSS, clickjacking | Add helmet, configure CSP/HSTS |
| No rate limiting | Enables brute-force / credential stuffing | Add express-rate-limit + account lockout |
| Weak/missing JWT secret | Session compromise | Validate secret at startup; rotate secrets |
| Dependency vulnerabilities | Remote code execution / privilege escalation | Run npm audit, patch or upgrade deps |
How to use the report
- Use the report as a prioritized remediation checklist for development and ops teams.
- Convert the Markdown to Google Docs or PDF for stakeholder review or compliance artifacts.
- Prioritize CRITICAL items (helmet, rate limiting, JWT secret validation, HTTPS enforcement) before deploying to production.
- Attach the audit file to tickets or CI/CD pipelines to track progress.
Validate environment secrets and fail fast: ensure JWT_SECRET is present and meets complexity requirements at app startup. Also add helmet and express-rate-limit for immediate mitigation.
Repository and prompts
The repository accompanying this lesson includes reusable prompt templates and examples tailored to Express/Node.js applications. Reuse or adapt them to your codebase and security requirements.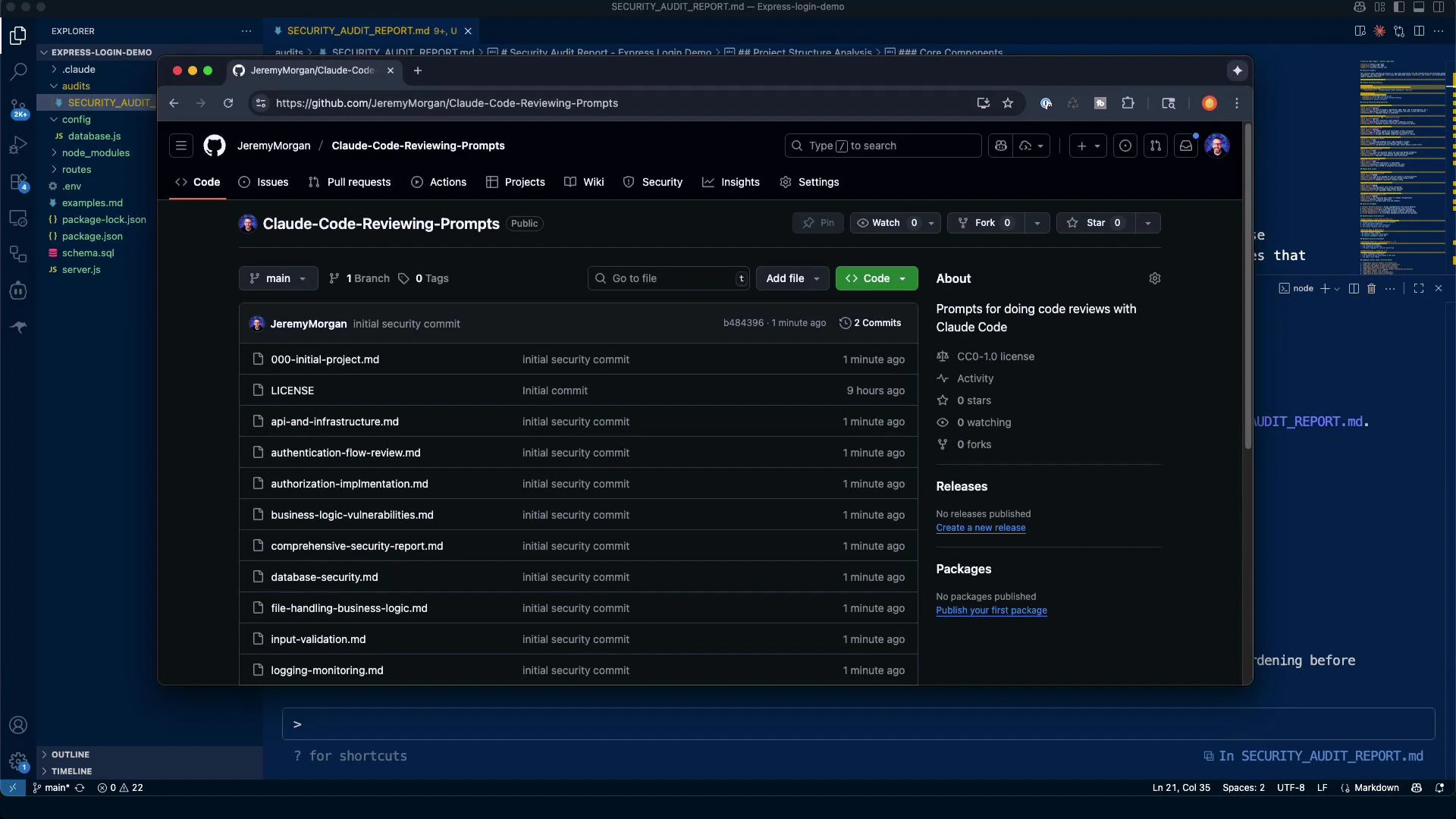
- 000-initial-project.md
- api-and-infrastructure.md
- authentication-flow-review.md
- authorization-implementation.md
- business-logic-vulnerabilities.md
- comprehensive-security-report.md
Next steps
This lesson focused on the initial scan and reporting workflow. Recommended follow-ups:- Deep-dive into authentication and authorization flows (JWT best practices, refresh tokens, session invalidation)
- Implement recommended middleware: helmet, express-rate-limit, cors (with secure configuration)
- Harden error handling and logging to avoid information disclosure
- Integrate automated audits into CI (npm audit / Snyk / Dependabot) for continuous dependency monitoring
- Express.js — Getting started
- Helmet — Security middleware for Express
- express-rate-limit — Basic IP rate-limiting middleware
- OWASP Top Ten — Web Application Security Risks