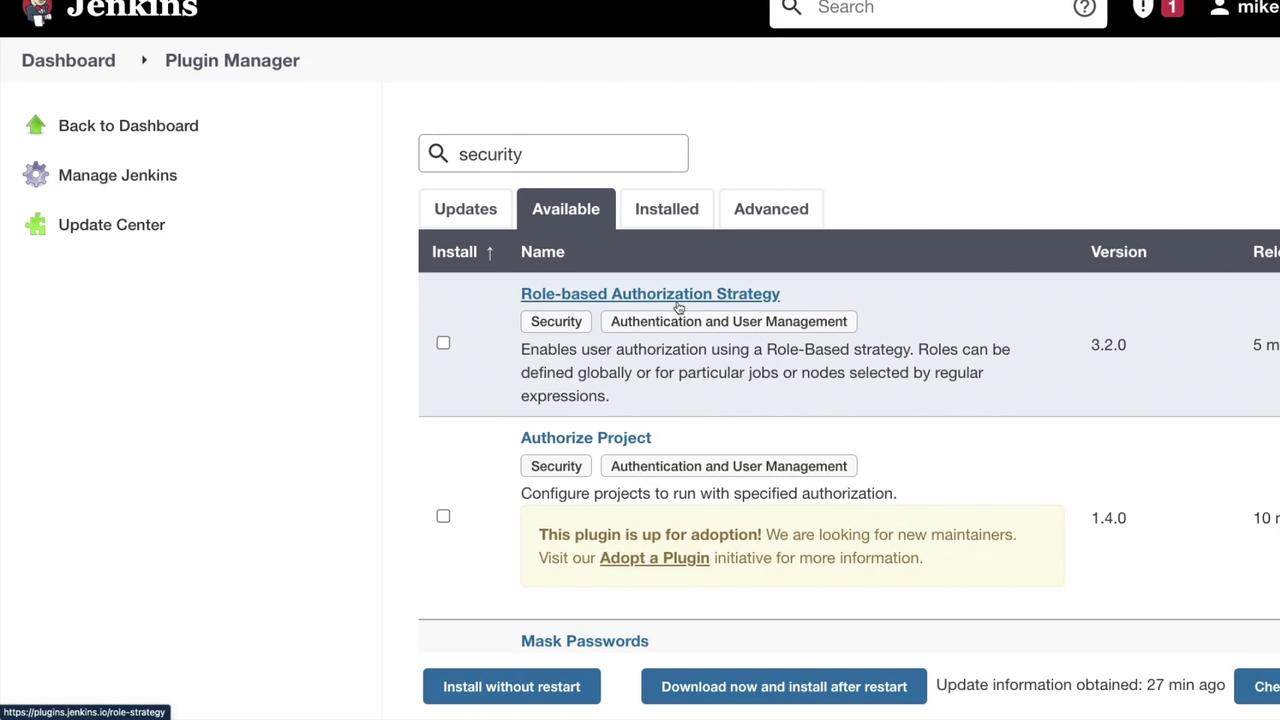
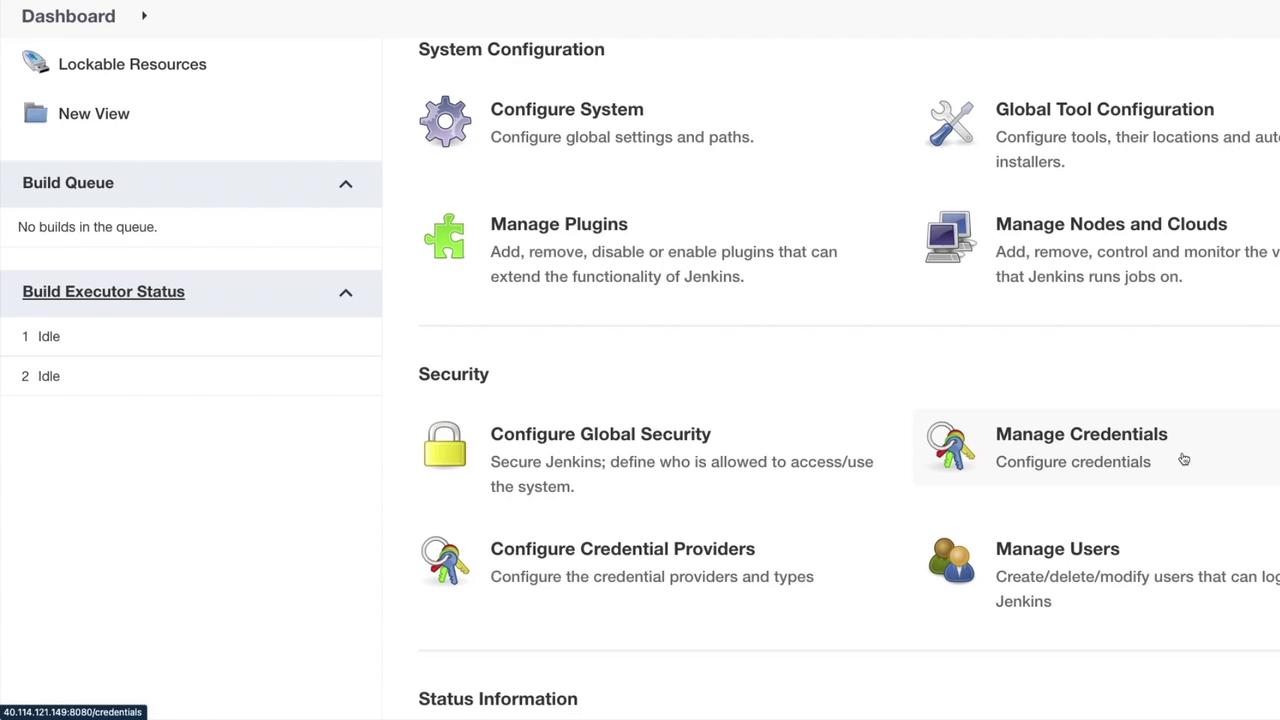
Managing and securing Jenkins is a critical aspect of system administration. While developers may not interact with every security detail, ensuring robust code security remains essential. In this article, we explore the various security options available in Jenkins, covering both global security settings and plugin-based implementations. When you navigate to the “Manage Jenkins” section, you’ll notice a dedicated area for security. To further enhance your setup, consider exploring the security-related plugins available under “Manage Plugins.” By searching for terms like “Role-based Authorization Strategy,” “Authorize Project,” “Mask Passwords,” “GitHub Authentication,” and “OWASP Dependency Check,” you can find multiple approaches tailored to different security needs.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
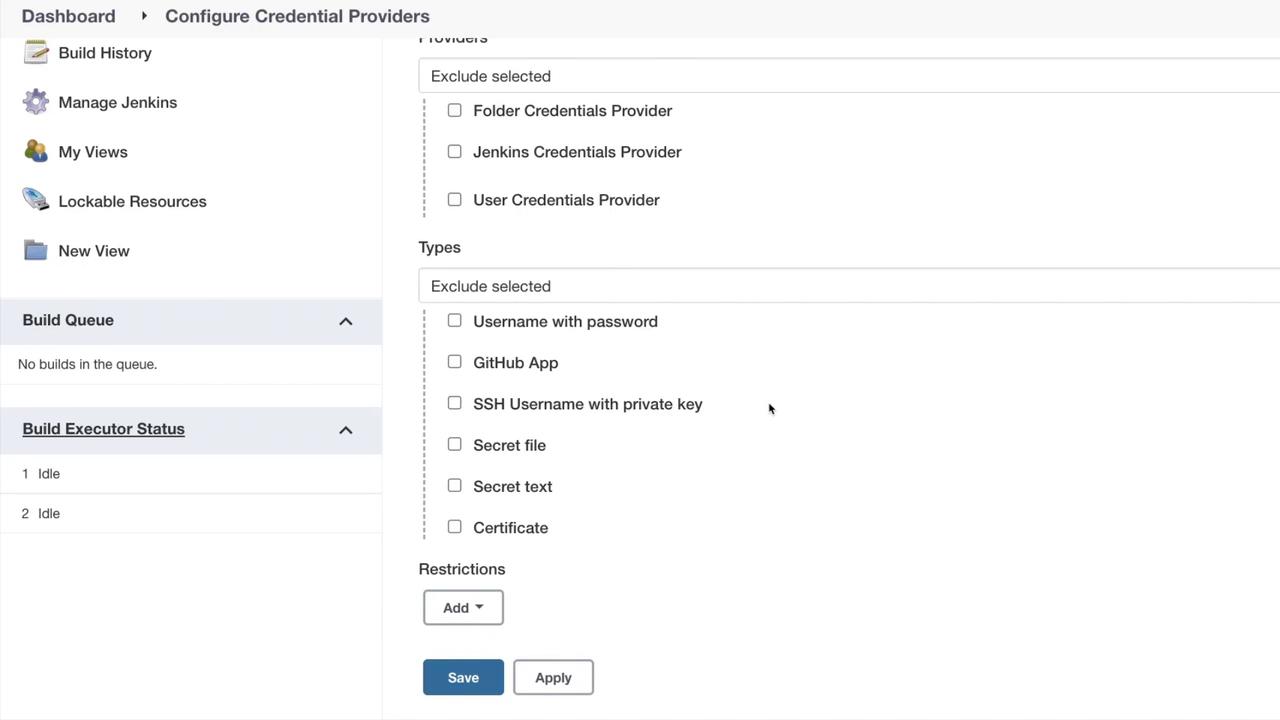
- Manage Credentials
- Configure Credential Providers
- Manage Users
- Configure Global Security
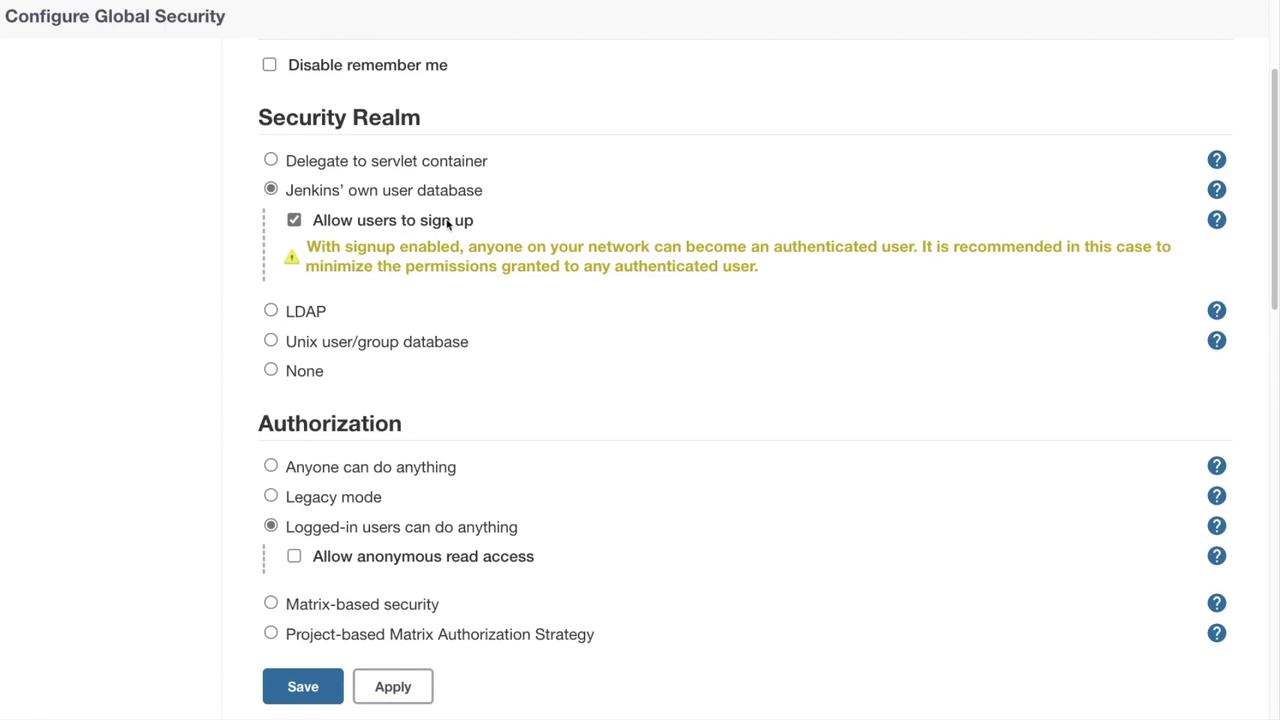
- Authentication Options: Disable features like “Remember Me” (which caches credentials similar to Gmail) to minimize security risks and ensure users re-enter their credentials each session.
- Security Realm: Choose from various options:
- Delegate to Servlet Container (utilizes the container’s authentication system)
- Jenkins’ own user database (with an optional sign-up feature)
- LDAP configuration
- Unix user group database
- None (not recommended)
- Agent Protocols: Configure TCP ports for inbound connectivity and control the display of security warnings.
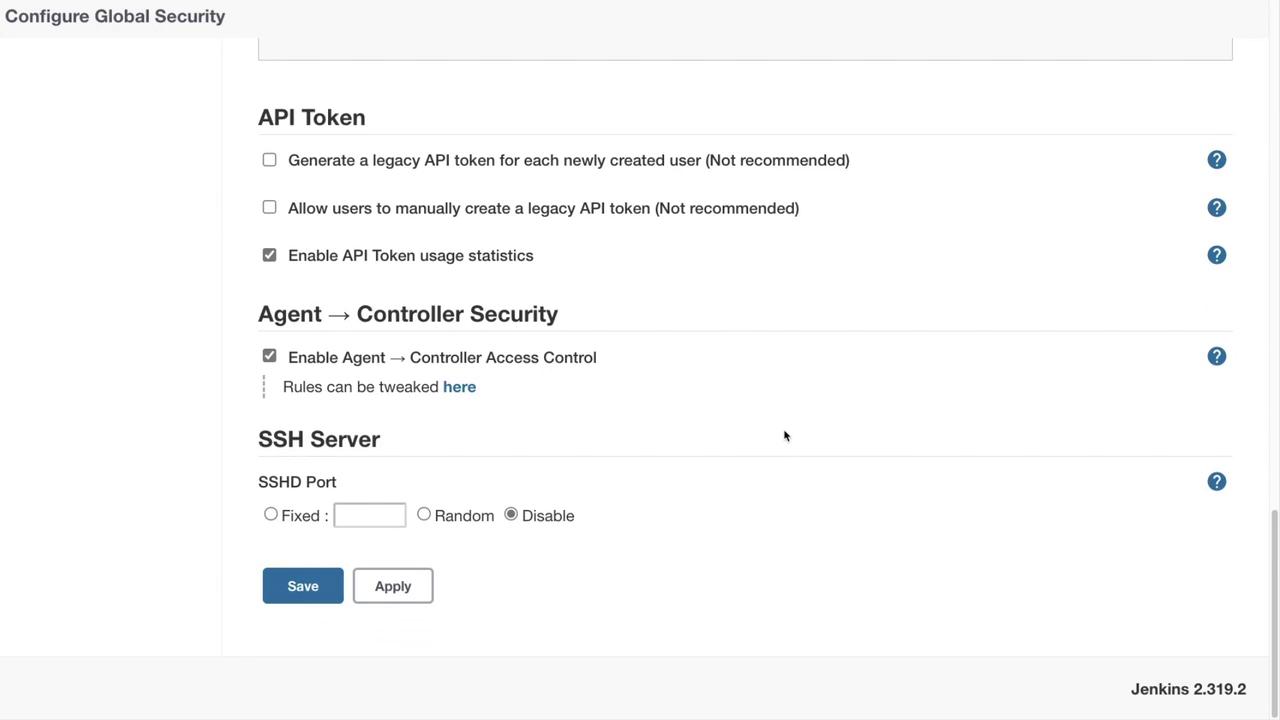
- API Options: While creating legacy API tokens or manual generation is discouraged, enabling API token usage statistics can enhance security monitoring.
- Agent Controller Access: Enable this if you plan on using build agents for your pipelines.
- Jenkins as an SSH Server: Although Jenkins can act as an SSH server for Jenkins Cloud commands, it is disabled by default. Current recommendations suggest keeping it disabled for better security.
Appropriately configuring global security settings is essential for protecting your Jenkins environment. Always assess your organization’s requirements before modifying security features.