In this lesson, we begin by discussing the key design requirements for authentication and authorization in modern applications. Our discussion will cover essential components such as Azure AD, Azure AD B2B, Azure AD B2C, and Conditional Access. We will also explore identity governance, access reviews, managed identities, and their application in securing access to KeyVault. Given that the AZ-305: Microsoft Azure Solutions Architect Expert exam emphasizes solution design, this lesson is structured around a real-world customer scenario.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
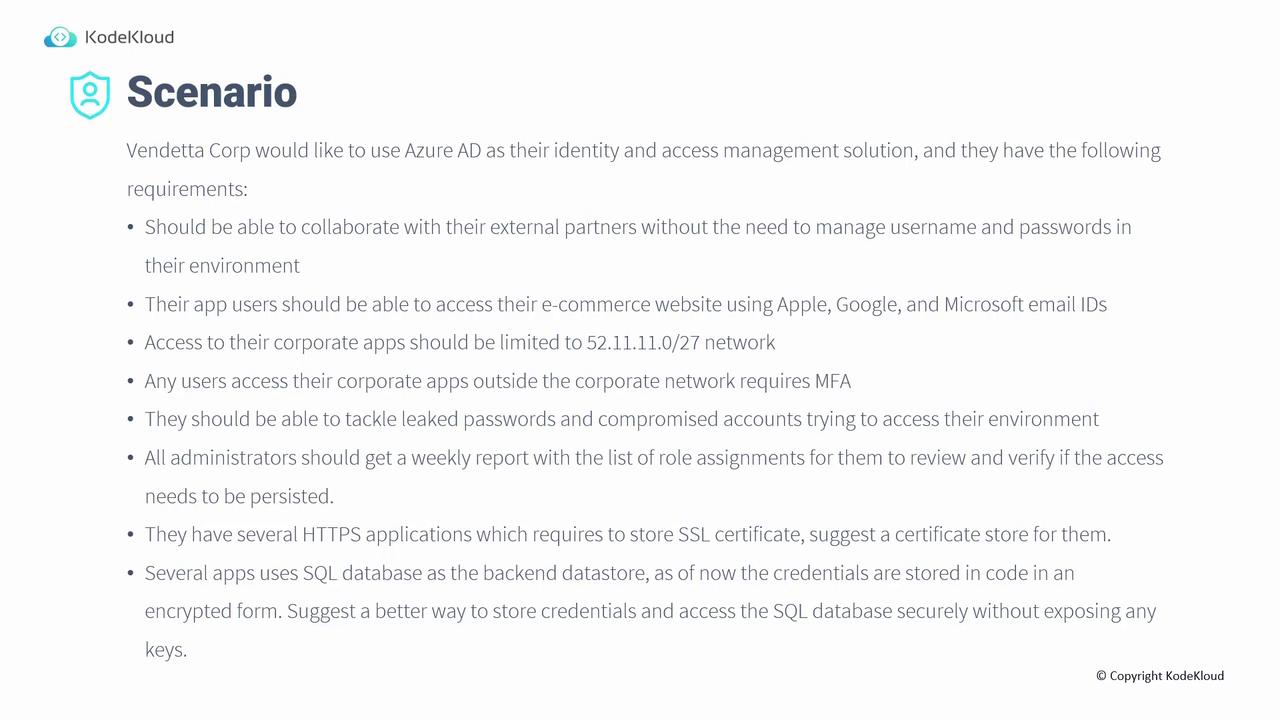
Vendata Corp plans to leverage Azure AD for their identity and access management needs. Their solution requirements are as follows:
- Collaborate with external partners without managing individual usernames and passwords.
- Allow application users to access their e-commerce website using Apple, Google, and Microsoft email accounts.
- Restrict access to corporate applications to the specific IP range 52.11.11.0/27.
- Enforce multi-factor authentication for users accessing corporate applications from external networks.
- Mitigate risks associated with leaked passwords and compromised accounts.
- Provide administrators with a weekly report of role assignments to verify and review access rights.
- Manage several HTTPS applications requiring secure storage of SSL certificates.
- Securely store credentials for multiple application users who rely on an SQL backend, thus eliminating the need to hardcode encrypted credentials.