Explore how HashiCorp Vault’s Transit Secrets Engine provides encryption-as-a-service, centralizing key management while keeping your applications agnostic of encryption details.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
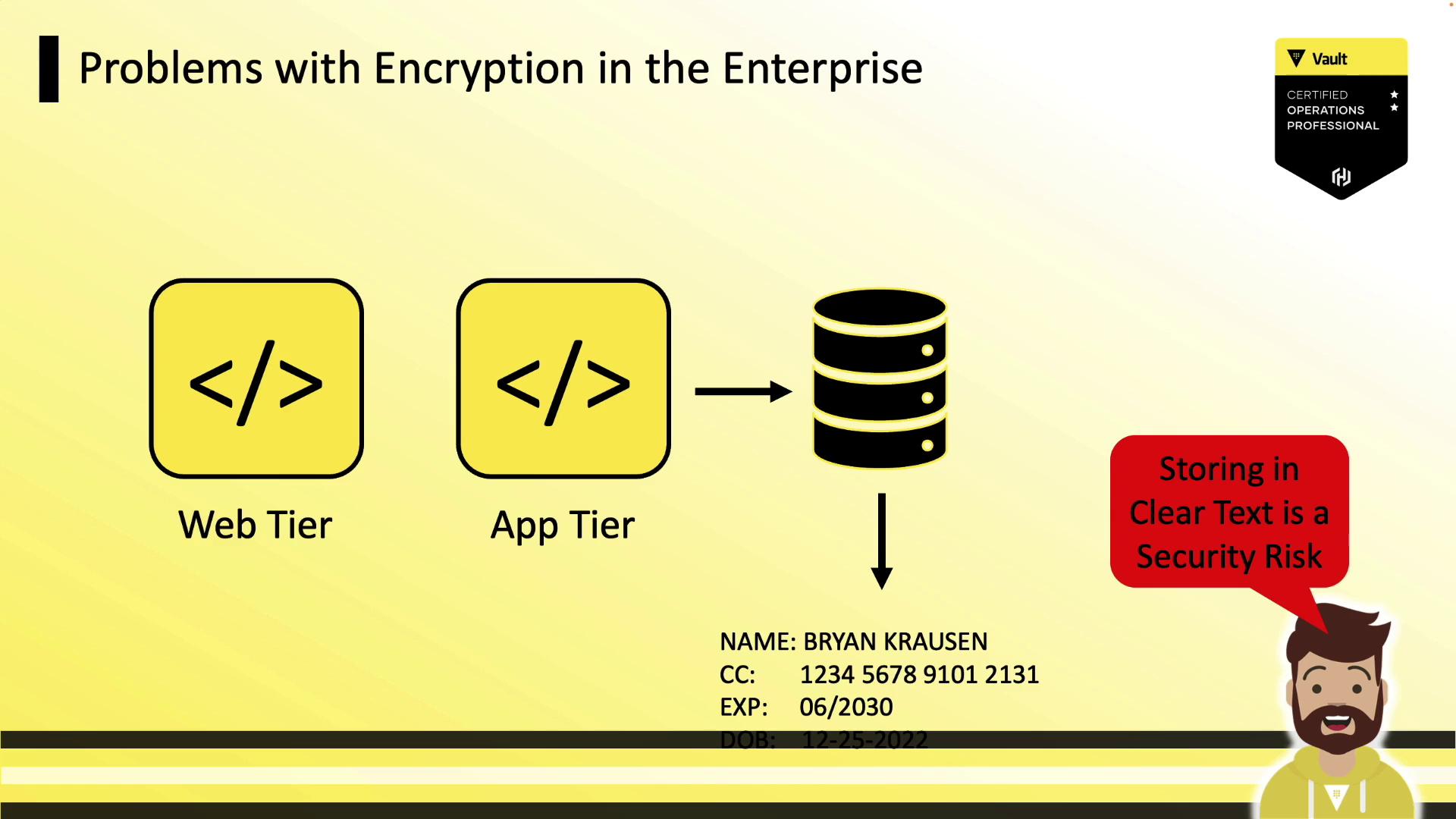
Enterprise Encryption Challenges
Most enterprises deploy three-tier applications (web tier → app tier → database). Storing sensitive data (PII, credit cards) in clear text poses a serious security risk.Storing sensitive data in plaintext can lead to breaches if your database is misconfigured or compromised.
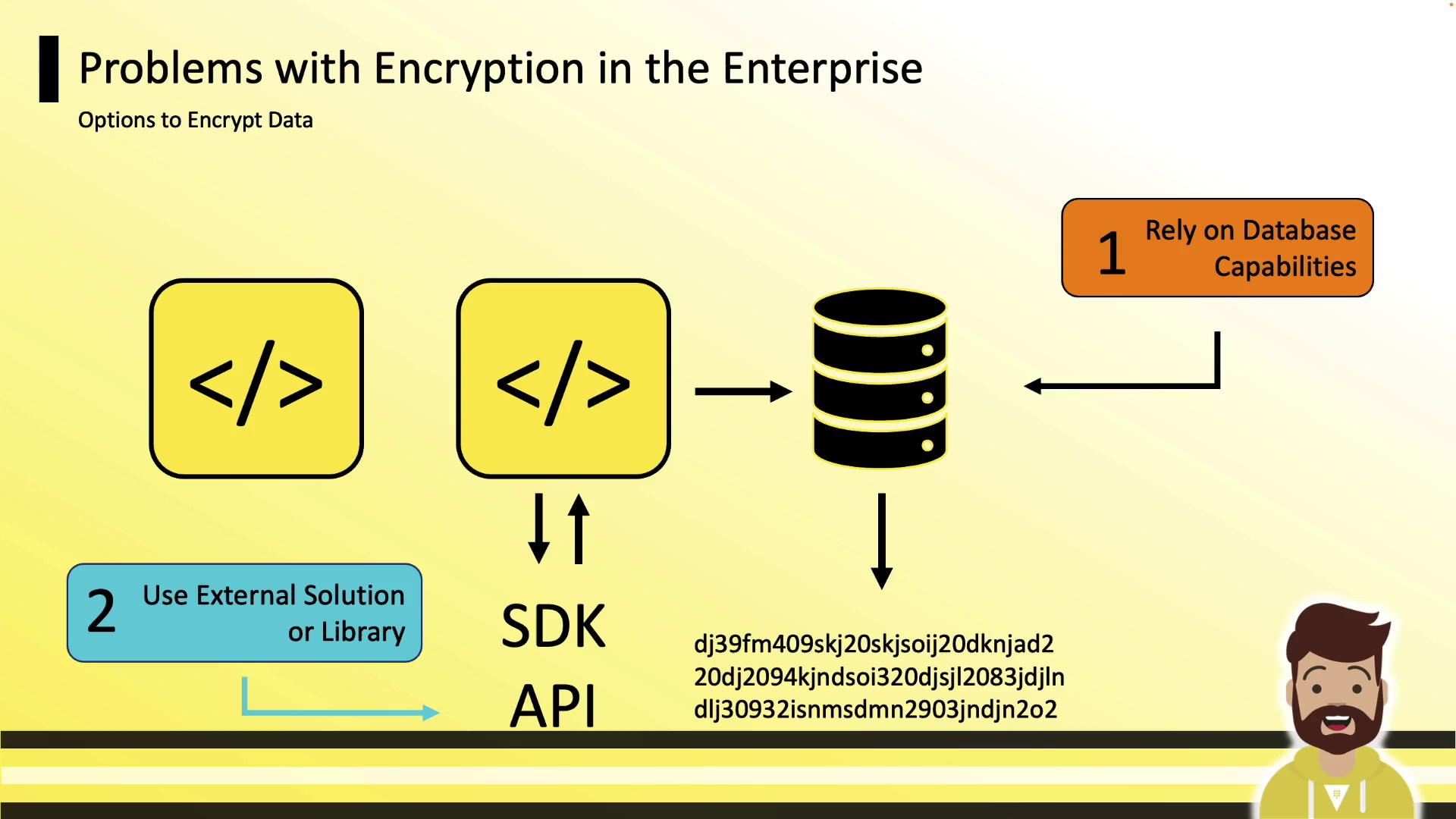
Encryption Options for Data at Rest
To protect data at rest, teams typically choose between:- Database-native encryption
- Application-level encryption using external SDKs or APIs
Drawbacks of Database-Native Encryption
Relying on built-in database features can lock you into a specific platform. For example, you might choose Cassandra for scale but switch to MSSQL solely for encryption support.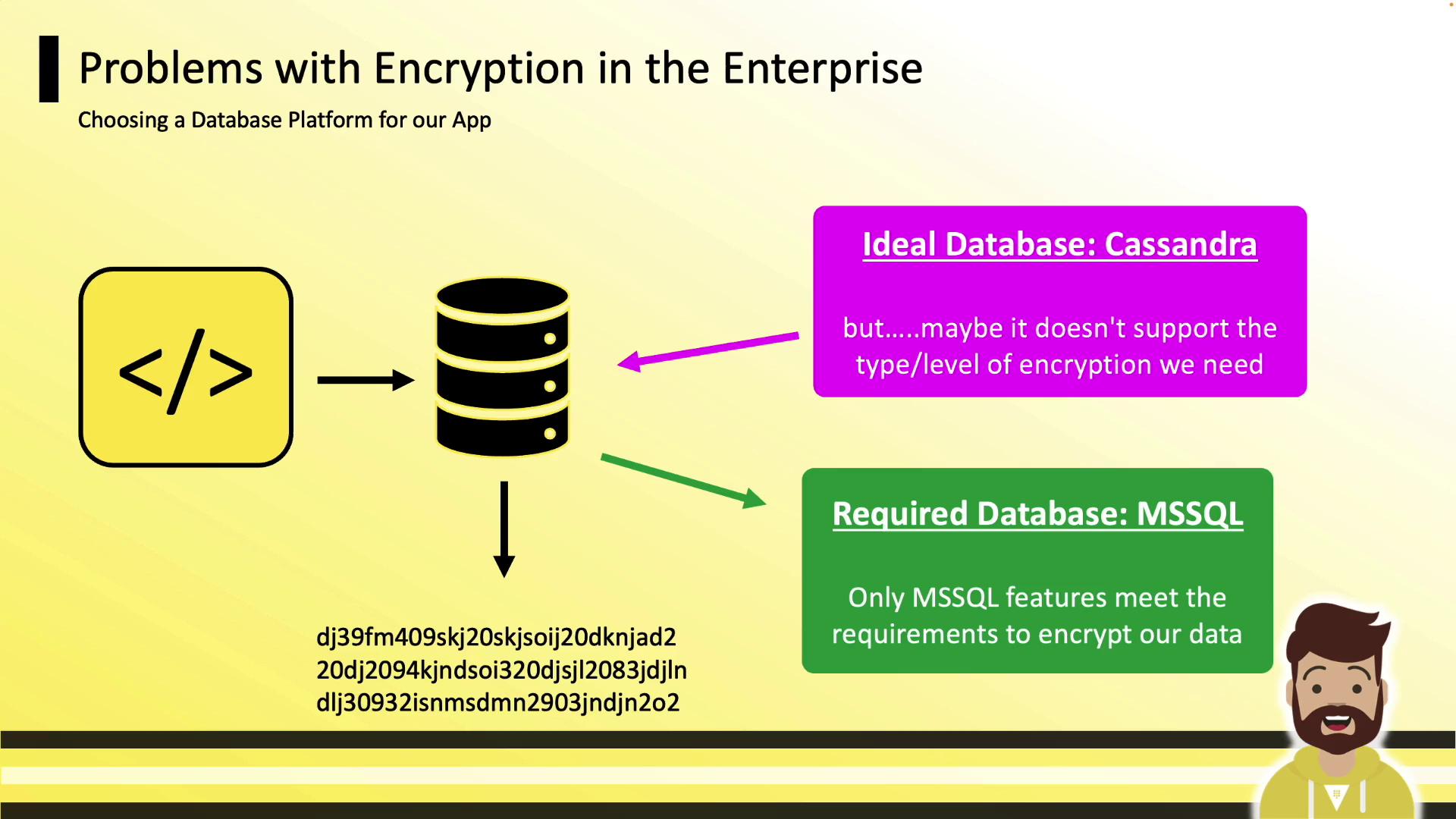
Siloed Developer Encryption
When each team implements its own solution, you end up with:- Team A: OpenSSL
- Team B: Go libraries
- Team C: .NET APIs
- Team D: In-house tool
- Team E: Third-party service
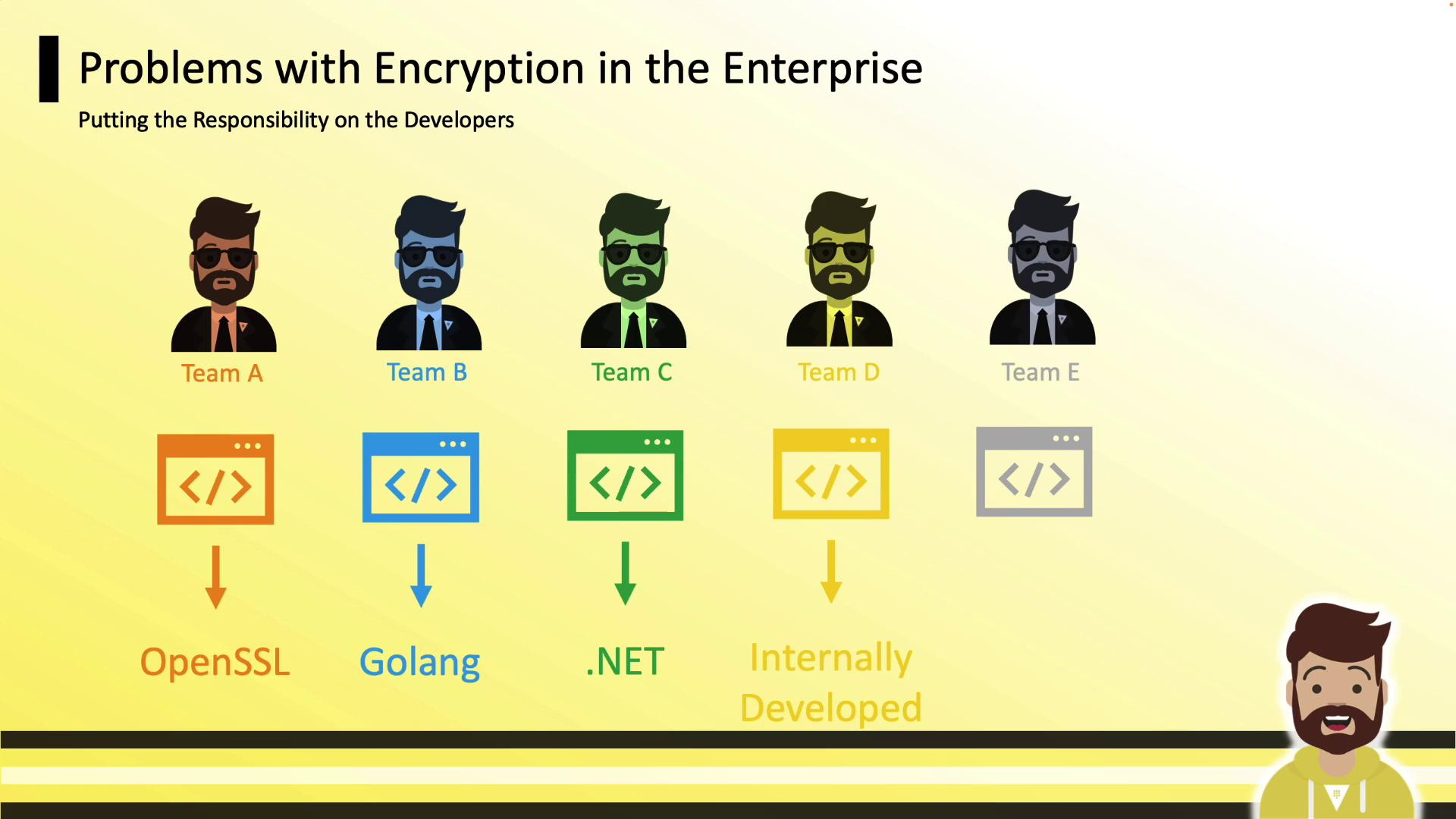
Security teams specialize in cryptography. Let Vault handle keys and operations so developers focus on code.
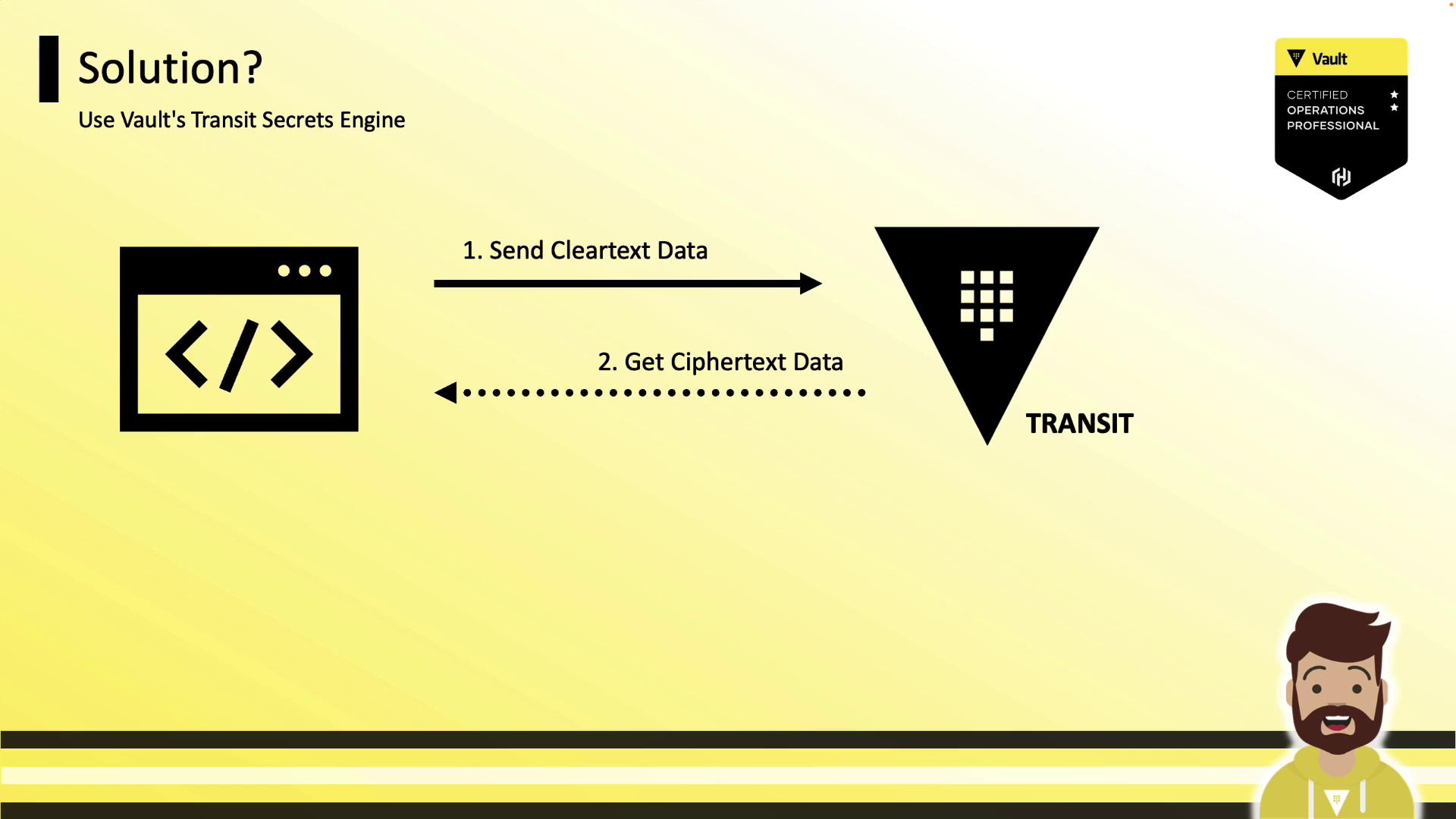
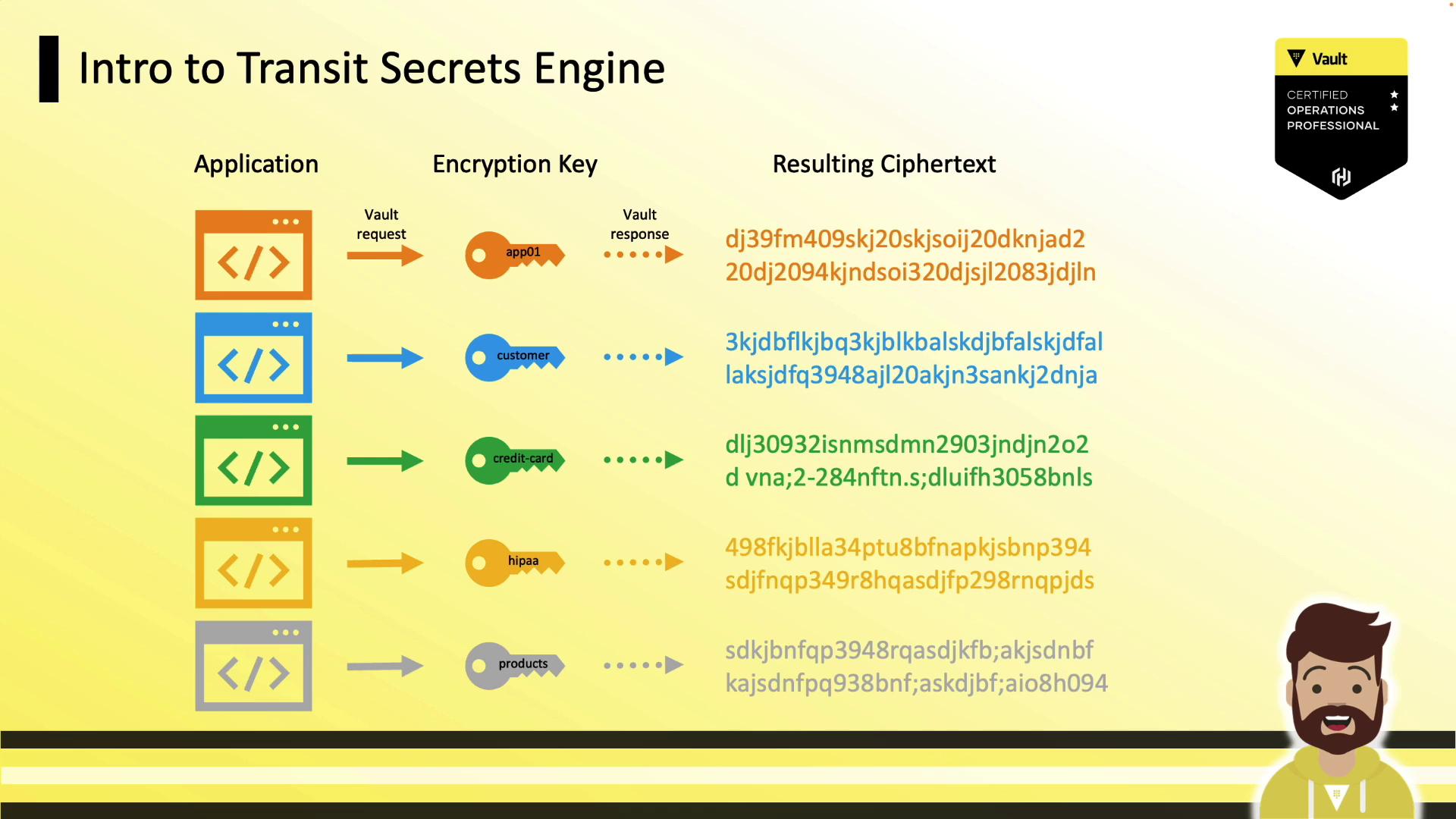
Introducing the Transit Secrets Engine
Vault’s Transit Secrets Engine offers a unified encryption service:- Applications send plaintext data to Vault over TLS
- Vault encrypts with a centrally managed key
- Vault returns ciphertext
- Applications store ciphertext anywhere (DB, object store, etc.)
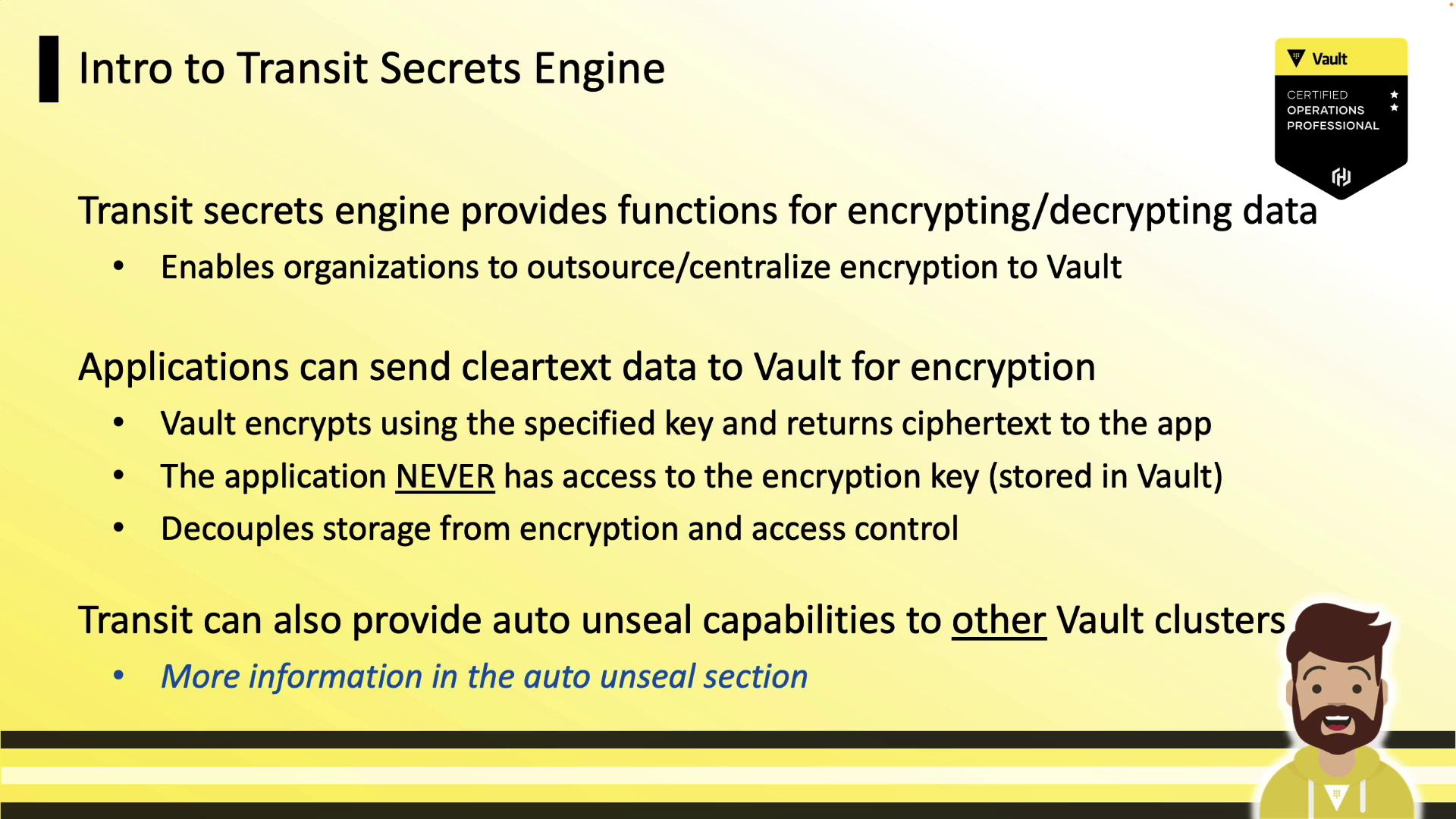
Key Features
- Encrypt/decrypt over HTTP API
- Centralized key management inside Vault
- Auto-unseal support with Cloud KMS integrations
- Stateless engine—Transit doesn’t store data
Supported Key Types
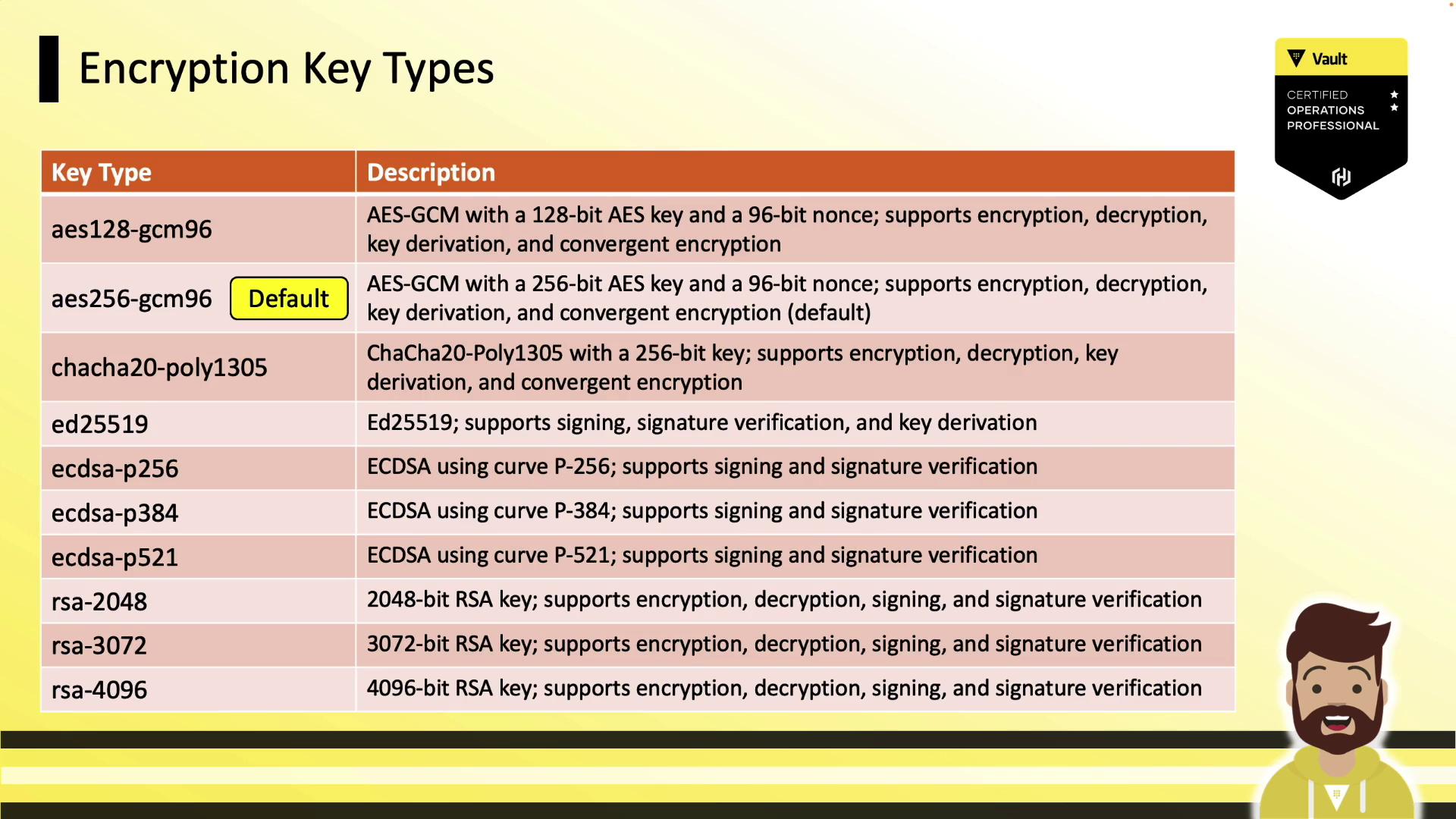
| Key Type | Use Case | Notes |
|---|---|---|
| aes256-gcm96 | Symmetric encryption | Default |
| chacha20-poly1305 | Symmetric encryption | High performance |
| ed25519 | Signing & verification | Modern elliptic |
| rsa-2048 | Signing & verification | Asymmetric |
All plaintext must be Base64-encoded before sending to Transit (this is encoding, not encryption).
Hands-On: Enable, Create Key, Encrypt & Decrypt
Enable the Transit engine:training:
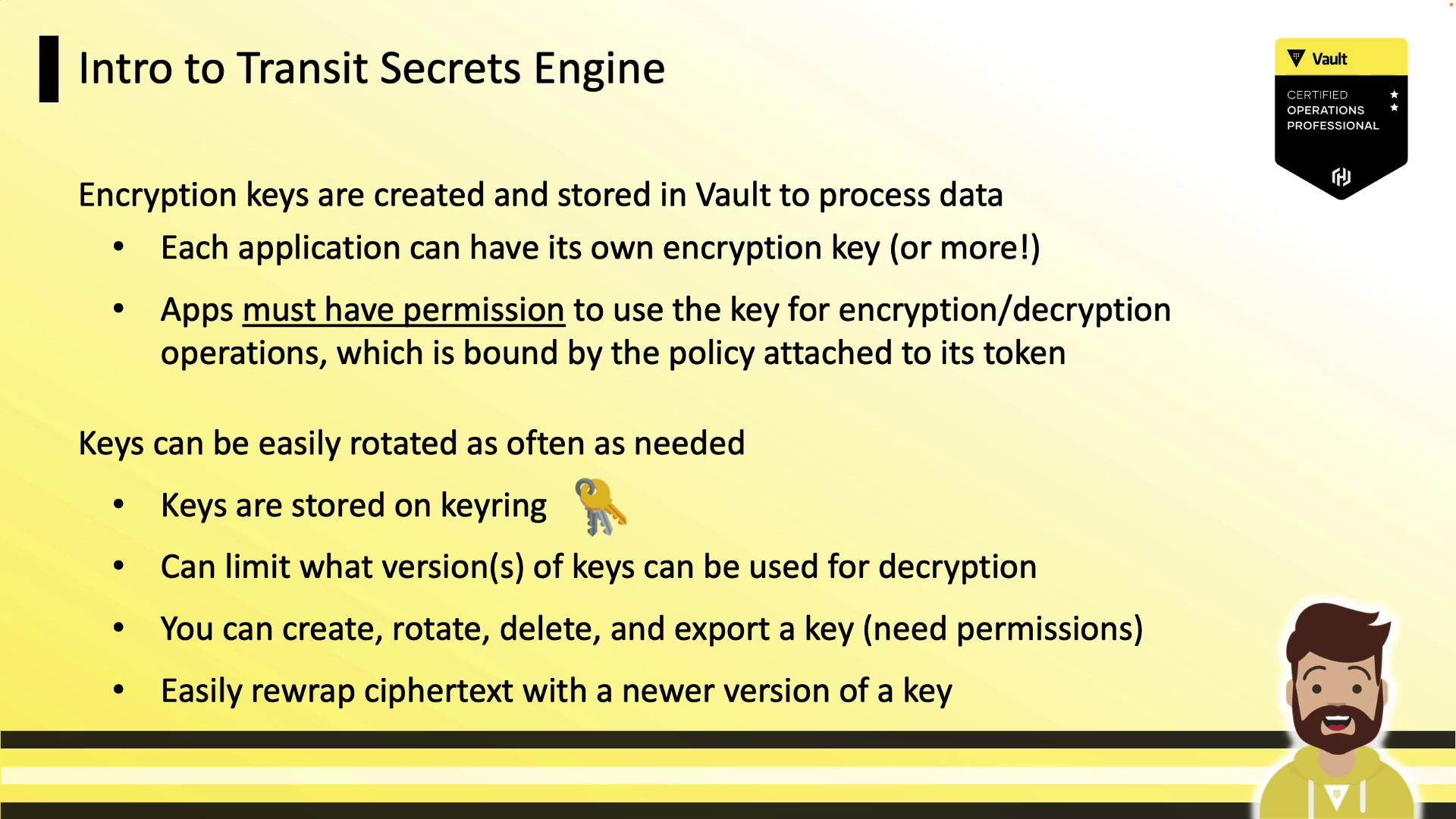
Rotating & Configuring Keys
Rotate a key (manual or viaauto_rotate_period):
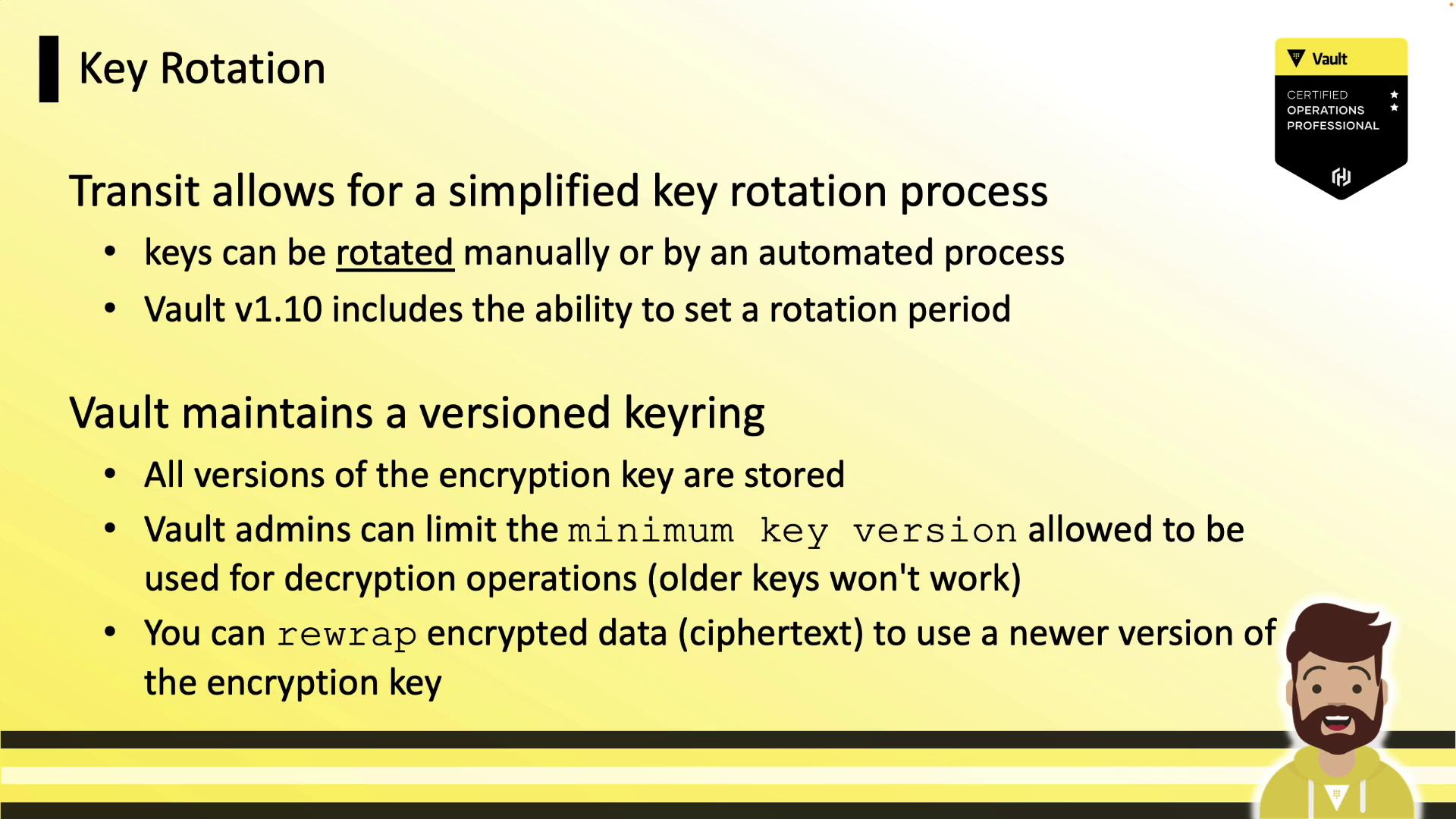
Rewrapping Ciphertexts
To upgrade existing ciphertext to the latest key version—without exposing plaintext—userewrap:
Policy Example
Grant an application the ability to encrypt and decrypt usingtraining:
Links and References
- HashiCorp Vault Transit Secrets Engine
- Vault HTTP API
- Vault Tokens and Policies
- HashiCorp Certified: Vault Associate