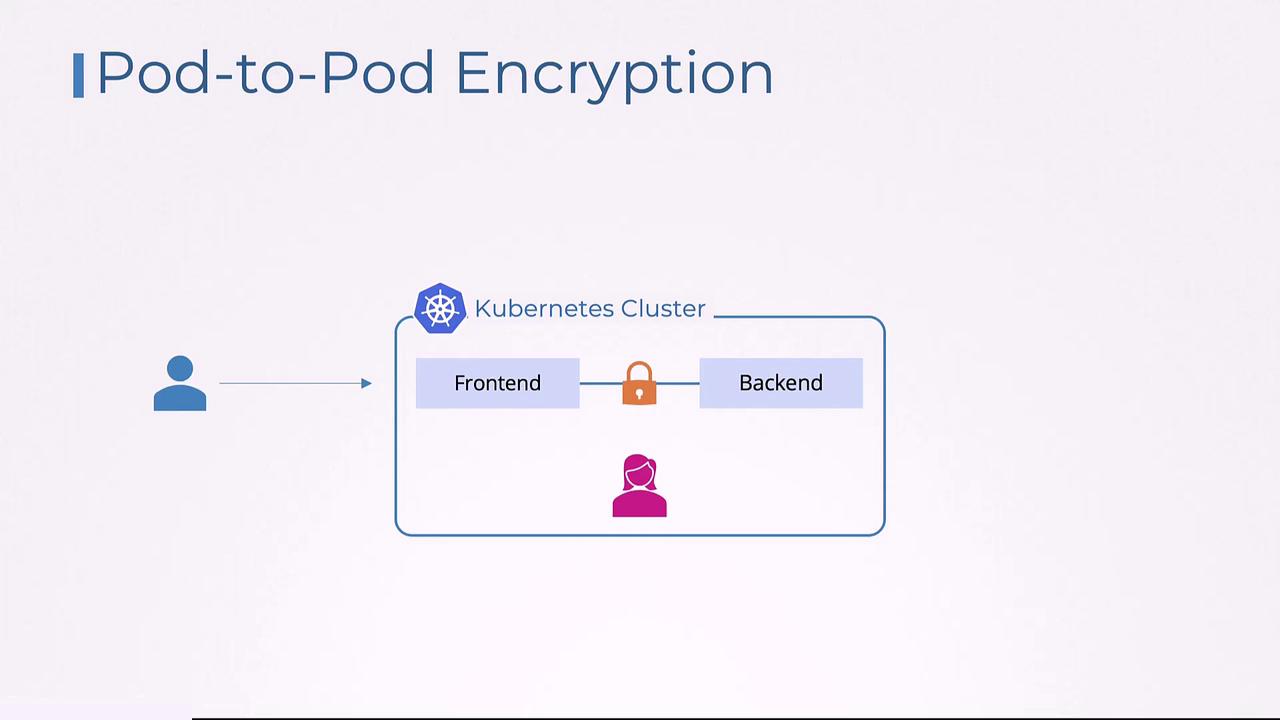
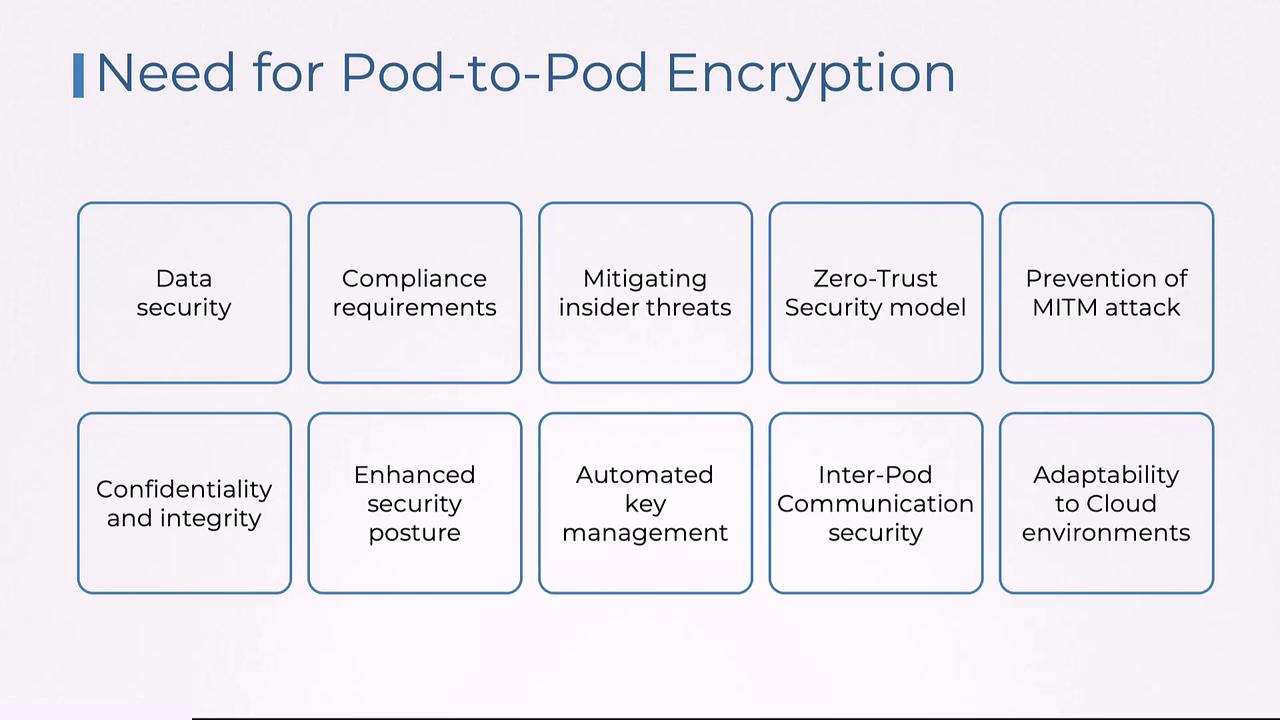
Pod-to-pod encryption is a critical security measure in Kubernetes clusters. It ensures that communication between pods—whether within the same namespace or across different namespaces—is encrypted, maintaining the confidentiality and integrity of transmitted data. This security mechanism is especially vital in multi-tenant environments where sensitive data flows between services. Imagine an e-commerce application deployed on Kubernetes with two main components: a front-end pod that manages customer orders and a back-end pod that processes payment information. When a customer places an order, the front-end pod sends sensitive payment details, including credit card information, to the back-end pod. Without encryption, an attacker could intercept this communication during a man-in-the-middle attack, leading to a potential data breach.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Enabling pod-to-pod encryption ensures that even if data is intercepted, it remains unreadable and tamper-proof because it is securely encrypted.
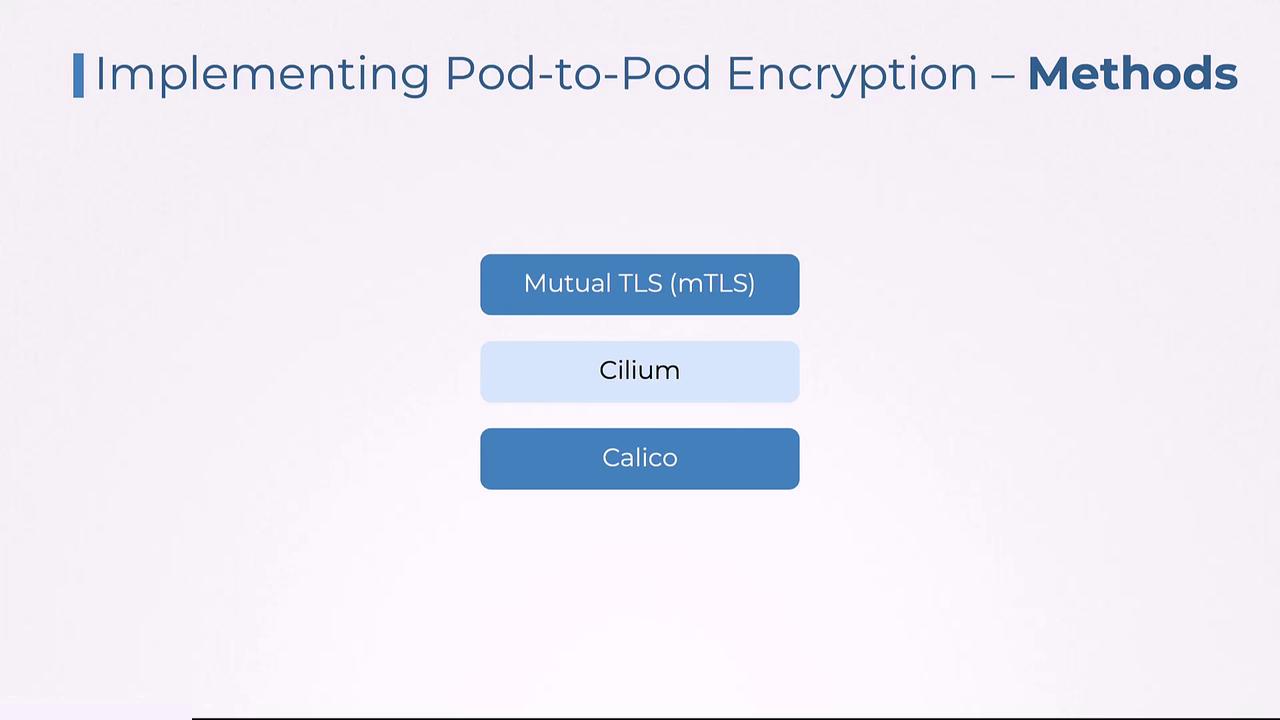
- Mutual TLS (mTLS): Commonly implemented via service meshes like Istio or Linkerd.
- Cilium Encryption: Utilizes IPsec or WireGuard protocols.
- Calico Encryption: Leverages IPsec for secure communication.
Implementing pod-to-pod encryption is a key best practice for securing Kubernetes deployments. It not only safeguards sensitive data against external attacks but also reinforces trust in internal communications.