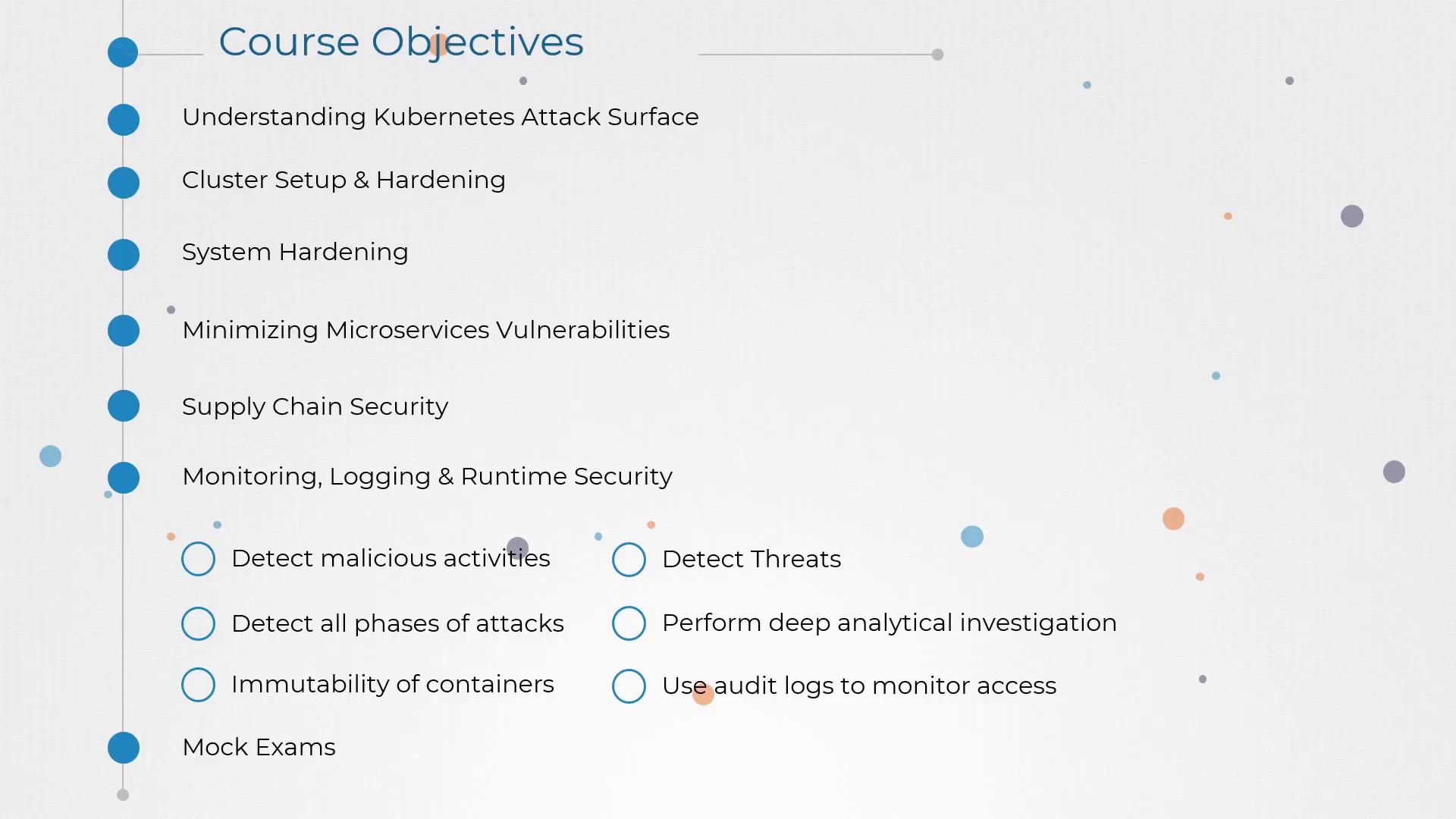
In this article, we delve into the critical aspects of monitoring, logging, and runtime security, with a special focus on behavior analytics for system calls and file activities at both the host and container levels. Our approach is designed to detect malicious activities early and effectively, reinforcing your overall security posture. We begin by exploring how tools such as Falco can help implement robust defense-in-depth strategies. These techniques ensure comprehensive threat detection by covering multiple components, including:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Physical infrastructure
- Applications
- Networks
- Data
- Users
- Workloads
The integration of multiple security layers—ranging from host-level system call monitoring to container runtime security—enhances your ability to quickly identify and neutralize threats.