In this article, we provide a clear and comprehensive guide to generating and managing a Software Bill of Materials (SBOM). This guide covers the entire process—from SBOM generation and secure storage to vulnerability scanning, detailed analysis, remediation, and continuous monitoring. Integrating these practices helps you maintain a secure, compliant software supply chain throughout the development lifecycle.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
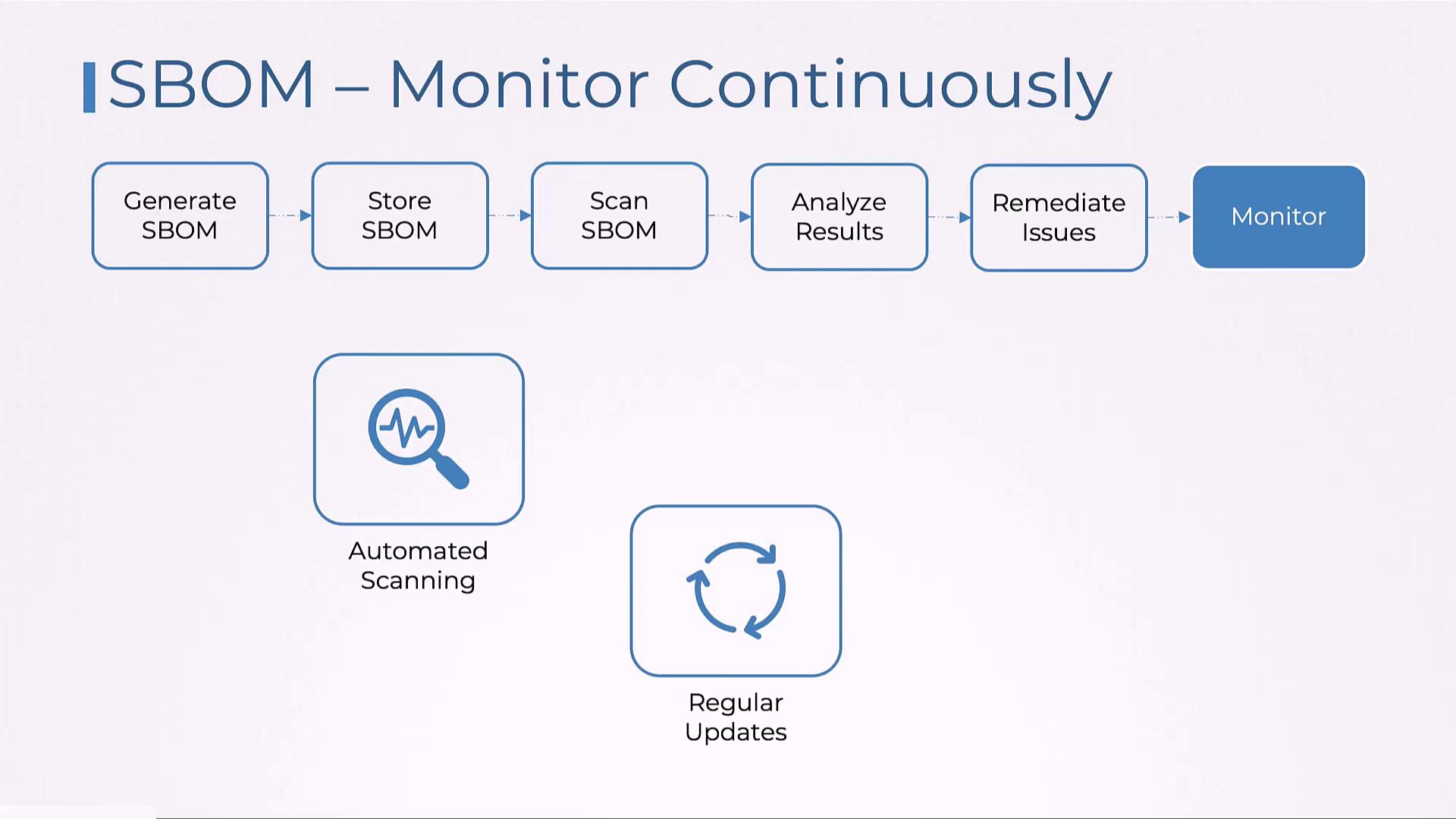
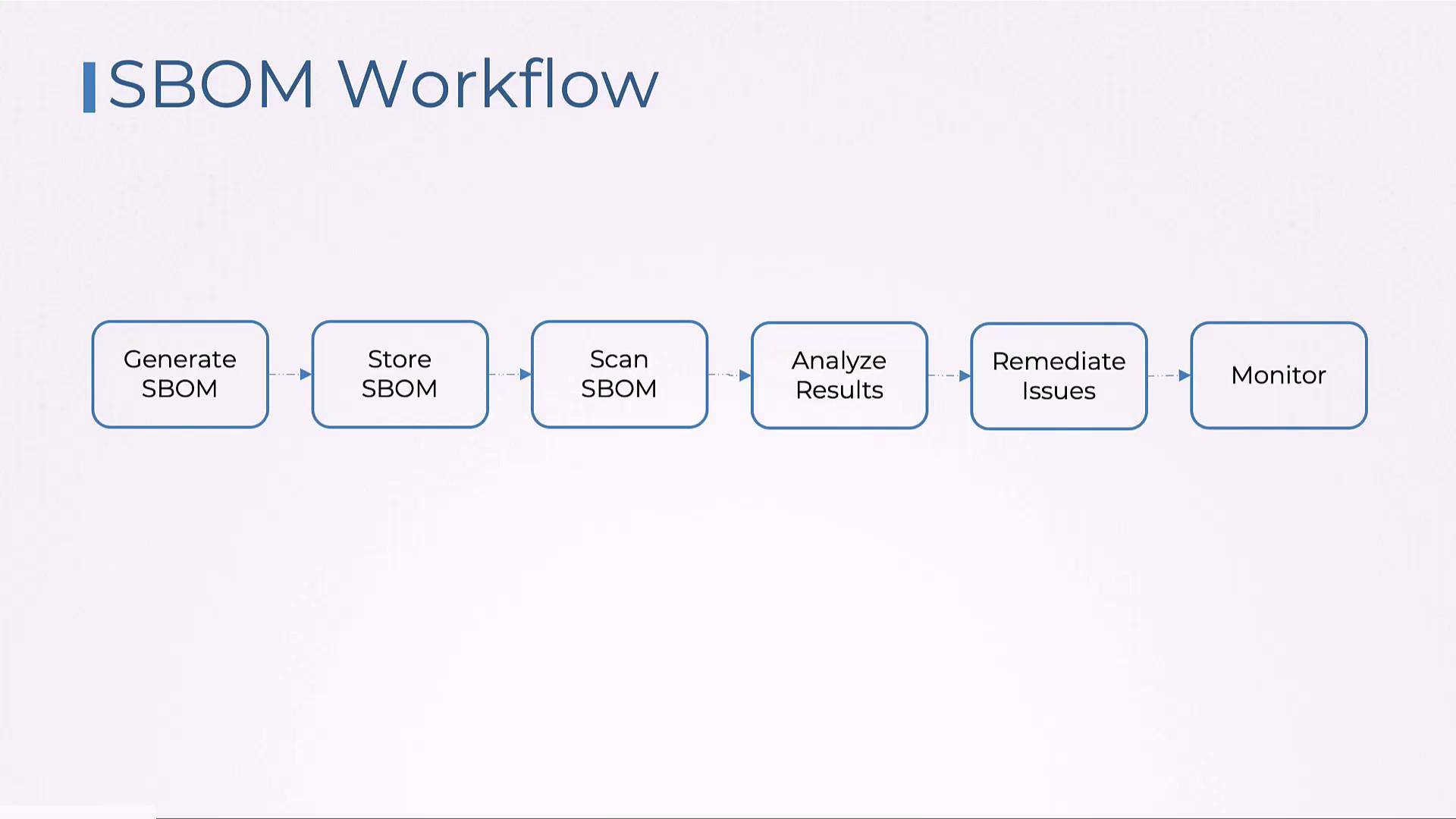
Overview of the SBOM Process
The SBOM process is comprised of the following key steps:- Generate the SBOM.
- Securely store the SBOM.
- Scan the SBOM for vulnerabilities.
- Analyze the scan results.
- Remediate the identified issues.
- Continuously monitor the SBOM.
- Use SPDX for open-source projects and enterprises that require licensing compliance, trace software origins, audit security, and manage vulnerabilities.
- Opt for CycloneDX to enhance vulnerability management across the software lifecycle and to ensure software integrity.

Generating an SBOM
Syft is a widely used tool for generating SBOMs. To get started, download Syft from the official site. It supports scanning both Docker images and local source code directories. Use the commands below as examples:Scanning the SBOM
After storing the SBOM securely, the next step is vulnerability scanning. Grype is an excellent tool for this purpose. Follow these steps:Review the output carefully to understand the nature of any vulnerabilities detected.
Analyzing Vulnerabilities
A detailed analysis of the scan results is essential for effective remediation. Below is an example JSON snippet that details a specific vulnerability:Remediating Vulnerabilities
After analyzing the vulnerabilities, the next step is remediation. This may involve updating the affected package to a secure version or replacing it with an alternative solution.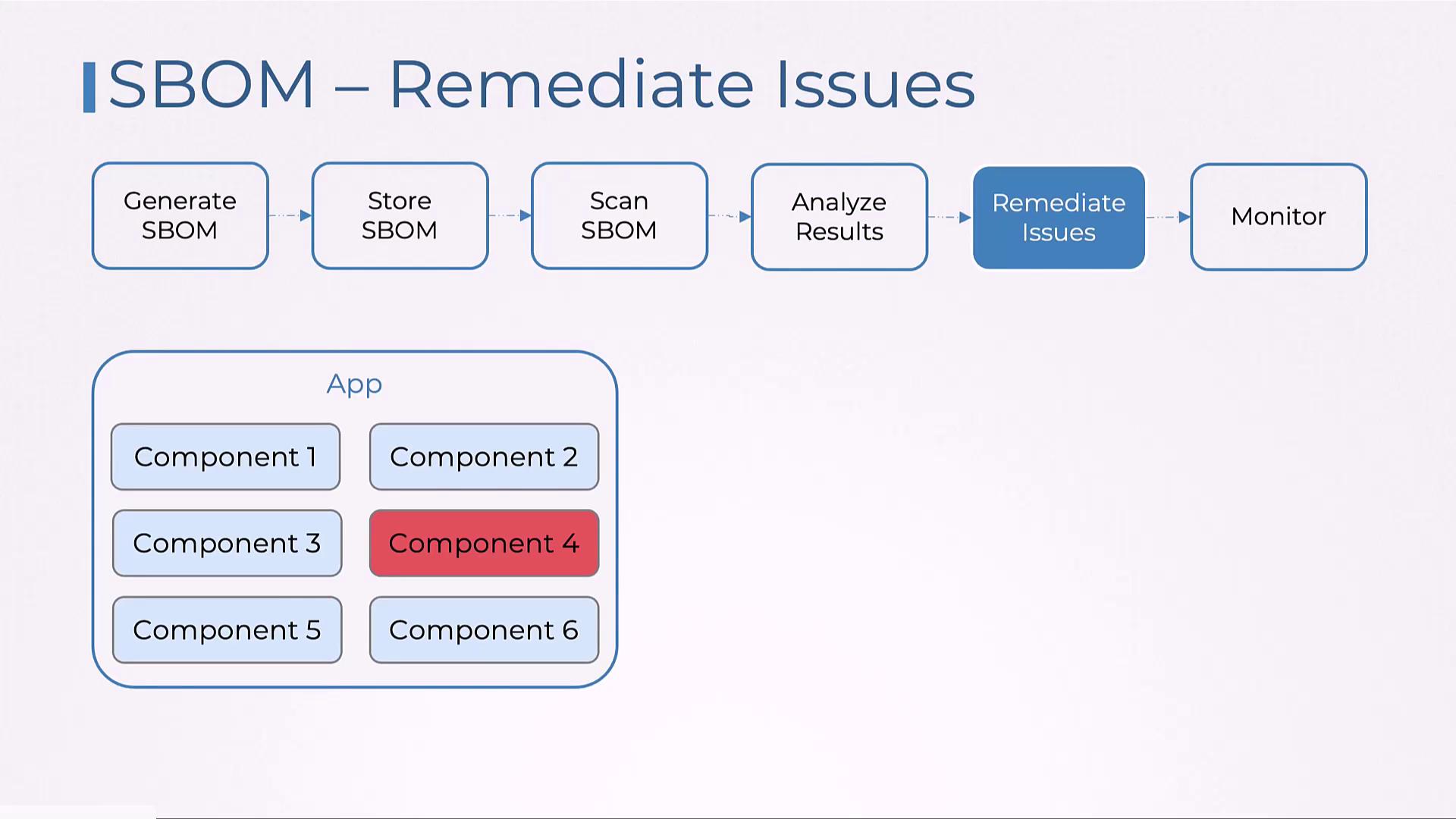
Ensure that remediation actions are tested in a controlled environment before deploying into production.
Continuous Monitoring and Alerts
The final step in the SBOM workflow is to establish continuous monitoring and automated alerts within your CI/CD pipelines. This ensures that dependencies are regularly updated and that any new vulnerabilities or compliance issues are quickly addressed.