In Kubernetes, the kubelet acts as the “captain” on each worker node. It:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Registers the node with the control plane.
- Starts and stops containers per Pod specs.
- Monitors Pod and container health, reporting back to the API Server.
- Install and configure the kubelet securely
- Inspect its running configuration
- Harden authentication, authorization, and network access
1. Role & Installation of the Kubelet
Key Responsibilities
- Node Registration
- Pod Lifecycle Management
- Health Reporting
Manual Installation
Download the kubelet binary and set up asystemd unit:
With kubeadm (v1.10+), most flags migrate into
/var/lib/kubelet/config.yaml and are maintained automatically during kubeadm join.Dedicated Config File
--config=/var/lib/kubelet/config.yaml to your service’s ExecStart. Command-line flags will always override the YAML settings.
2. Inspecting the Active Configuration
On any worker node, verify the kubelet invocation and configuration:3. Kubelet API Endpoints
| Port | Endpoint Type | Access | Recommendation |
|---|---|---|---|
| 10250 | Secure API | TLS + AuthN/AuthZ required | Keep enabled and locked down |
| 10255 | Read-only metrics | Unauthenticated, HTTP only | Disable in production |
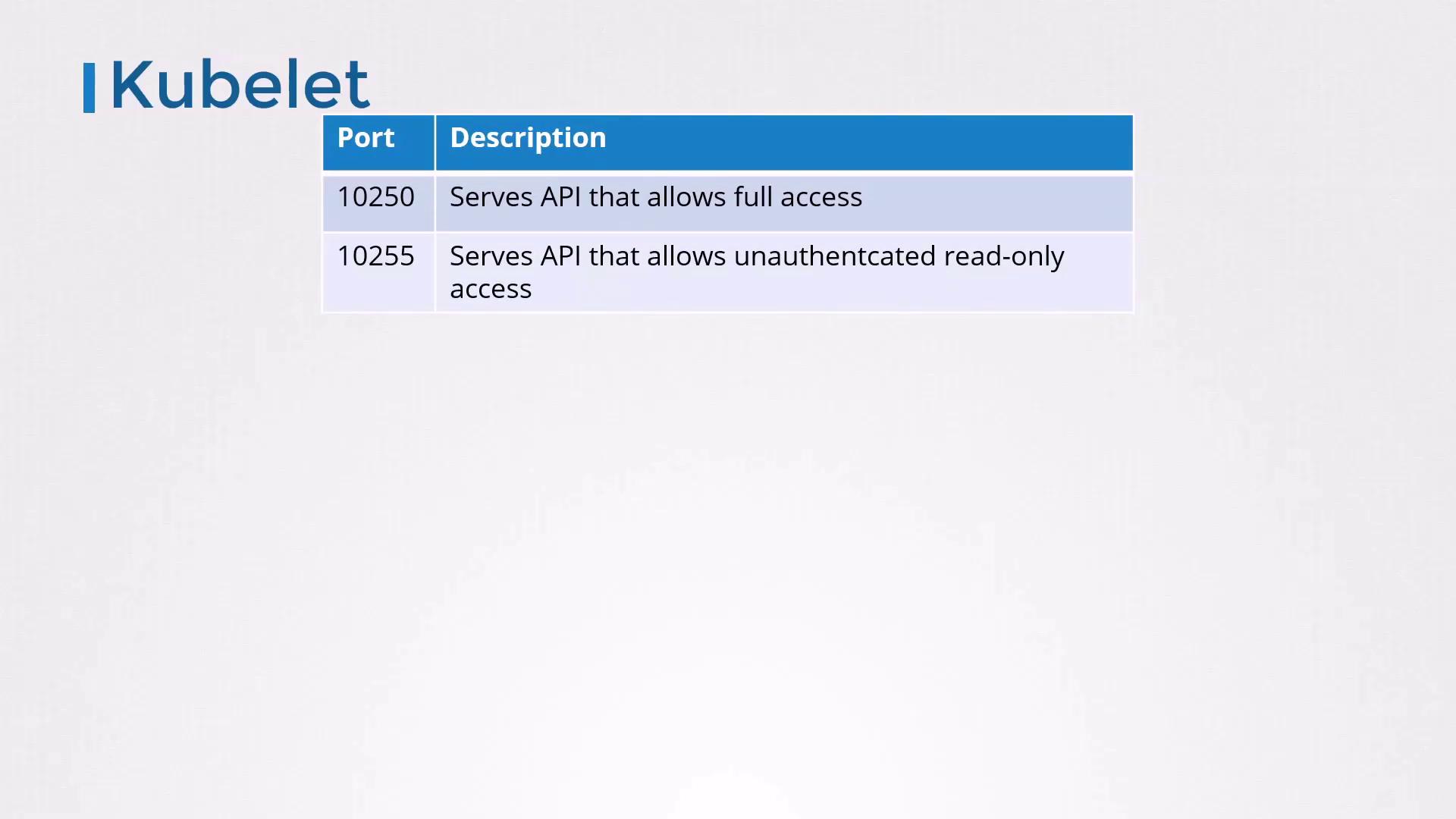
Port
10255 is unauthenticated and exposes sensitive metrics. It should always be disabled in production.4. Authentication Configuration
By default, the kubelet permits anonymous requests (system:anonymous). Disable this to force clients to present credentials.
Disable Anonymous Access
Via flags in yoursystemd unit:
/var/lib/kubelet/config.yaml:
Certificate-Based Client Auth
- Generate a CA and sign a kubelet-serving certificate.
-
Distribute the CA bundle with
--client-ca-file=/path/to/ca.crt. -
Test with:
-
Ensure the API Server has credentials to call the kubelet:
5. Authorization Modes
Out of the box, the kubelet usesAlwaysAllow (no authorization). Switch to Webhook to delegate decisions to the API Server.
6. Disabling the Read-Only Port
To completely turn off port10255:
Always set
readOnlyPort: 0 in production to prevent unauthenticated access to metrics.7. Summary of Hardening Steps
| Security Aspect | Recommended Setting |
|---|---|
| Anonymous Auth | --anonymous-auth=false |
| TLS Client AuthN | clientCAFile: /path/to/ca.crt |
| Authorization | --authorization-mode=Webhook |
| Read-Only Port | readOnlyPort: 0 |
| Certificate Rotation | rotateCertificates: true |