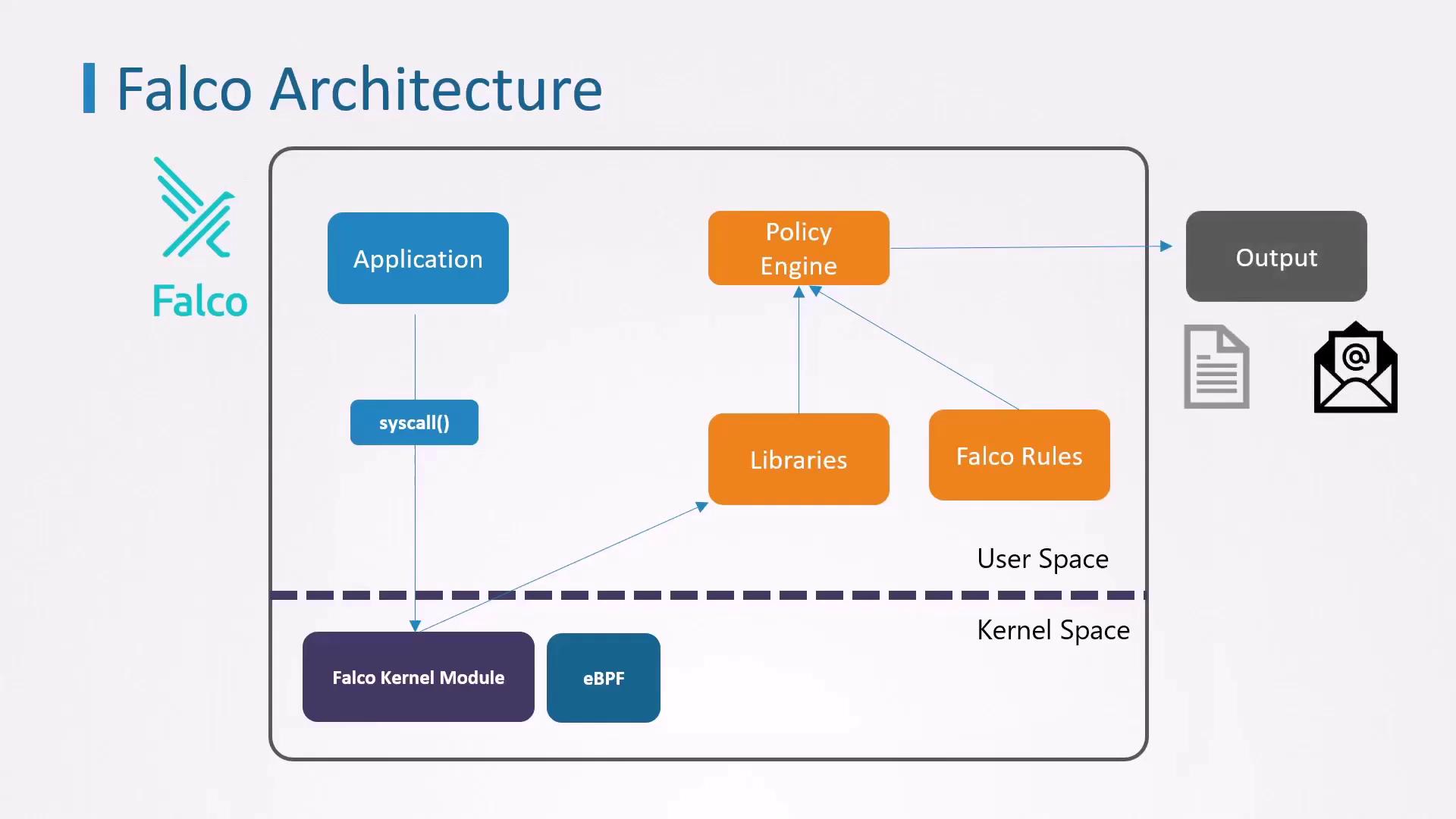
In this guide, you’ll learn how to install Falco to enhance threat detection and analysis in your Kubernetes environment. Falco is an open-source runtime security tool that inspects system calls from user-space applications, applying customizable rules to identify suspicious behavior.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
How Falco Works
Falco captures kernel events via two primary methods, then filters them through its policy engine:| Capture Method | Description | Pros & Cons |
|---|---|---|
| Kernel Module | Inserts a module into the Linux kernel to intercept syscalls. | Pros: High performance Cons: Intrusive; may be restricted on managed clusters |
| eBPF | Uses Extended Berkeley Packet Filter to attach probes to kernel functions. | Pros: Safer, non-intrusive Cons: Slightly higher overhead |
Installation Methods
You have two common ways to deploy Falco, depending on your access level and platform restrictions:| Method | Use Case | Advantages |
|---|---|---|
| Native Linux Installation | Full root access to a Linux node | Isolated from Kubernetes control plane |
| Kubernetes DaemonSet via Helm | Managed clusters or restricted environments | Easy upgrades and centralized management via Helm |
Installing Falco on a Linux Node
Use this approach if you can install packages and kernel modules directly on your host. It ensures Falco remains operational even if your Kubernetes control plane is compromised.Ensure you have the correct
linux-headers-$(uname -r) package. Mismatched headers can prevent the Falco kernel module from building.Deploying Falco in Kubernetes via Helm
If you’re on a managed Kubernetes service or prefer Kubernetes-native deployment, use Helm to install Falco as a DaemonSet:You can customize Falco’s configuration by passing values files (
-f values.yaml) to helm install.Next Steps
- Customize or create Falco rules to detect specific threats.
- Integrate alerts with your SIEM, Slack, or PagerDuty for real-time notifications.
- Monitor Falco logs and metrics to fine-tune performance and rule accuracy.