Welcome to this lesson on authenticating access to a Kubernetes cluster. A cluster consists of multiple physical or virtual nodes and several internal components working together to run your workloads. It’s crucial to secure management access by verifying identities for anyone or anything interacting with the API server. Actors interacting with the cluster:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
| Actor | Description | Examples |
|---|---|---|
| Administrators | Manage infrastructure and policies | Cluster operators, DevOps engineers |
| Developers | Deploy and maintain applications | CI/CD engineers, application owners |
| Robotic Clients | Automated systems accessing the API server | Monitoring tools, pipelines |
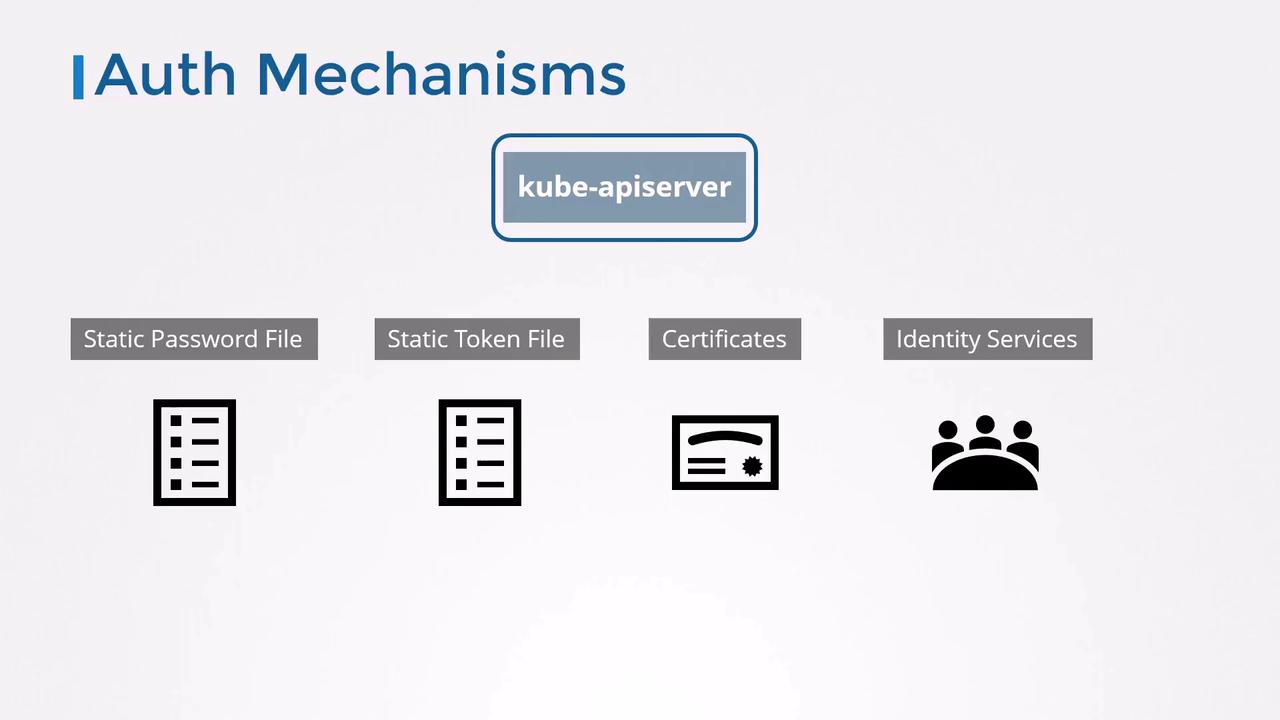
| Method | Description |
|---|---|
| Static Password File | CSV listing username, password, UID, [optional groups] |
| Static Token File | CSV listing bearer token, username, UID, [optional groups] |
| Client Certificates | X.509 certificates for users |
| External Identity Service | LDAP, OIDC, webhook token authentication |
1. Static Password File
The simplest approach uses a CSV file with one line per user:Configuring the API Server
Choose your setup:-
Systemd unit (
/etc/systemd/system/kube-apiserver.service): -
kubeadm (edit
/etc/kubernetes/manifests/kube-apiserver.yamlunderspec.containers.command):
Testing Password Authentication
2. Static Token File
Bearer tokens offer another static method. Create a CSV containing tokens:Testing Token Authentication
Storing usernames, passwords, or tokens in plain text is not recommended for production. Use secure vaults or external identity providers for sensitive environments.
Security Considerations
- For kubeadm clusters, mount your credential files into the API server Pod via a volume.
- Protect files with restrictive filesystem permissions (
chmod 600). - After authenticating users, configure Role-Based Access Control (RBAC) to grant least-privilege permissions.
Next, we’ll explore certificate-based authentication and how Kubernetes components use TLS certificates to secure communication.