In this tutorial, you’ll learn how to leverage HashiCorp Vault’s AWS Secrets Engine to manage IAM user credentials dynamically. We cover enabling the secrets engine, configuring and rotating Vault’s root AWS credentials, defining roles for on-demand IAM users, and revoking credentials both individually and in bulk.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
1. Enable the AWS Secrets Engine
First, enable the AWS engine at theaws/ path:
2. Prepare Vault’s AWS Permissions
Vault requires AWS credentials capable of managing IAM users, policies, and optional EC2/KMS operations.Least Privilege
In production, attach an IAM role to the Vault server using instance profiles. Only use an IAM user for demos or CI pipelines.
2.1 Core AWS Permissions
Grant Vault rights to describe EC2 instances and decrypt KMS keys if needed:2.2 IAM Management Permissions
To let Vault create, attach policies, and delete IAM users/key pairs dynamically:2.3 Demo: Create an IAM User
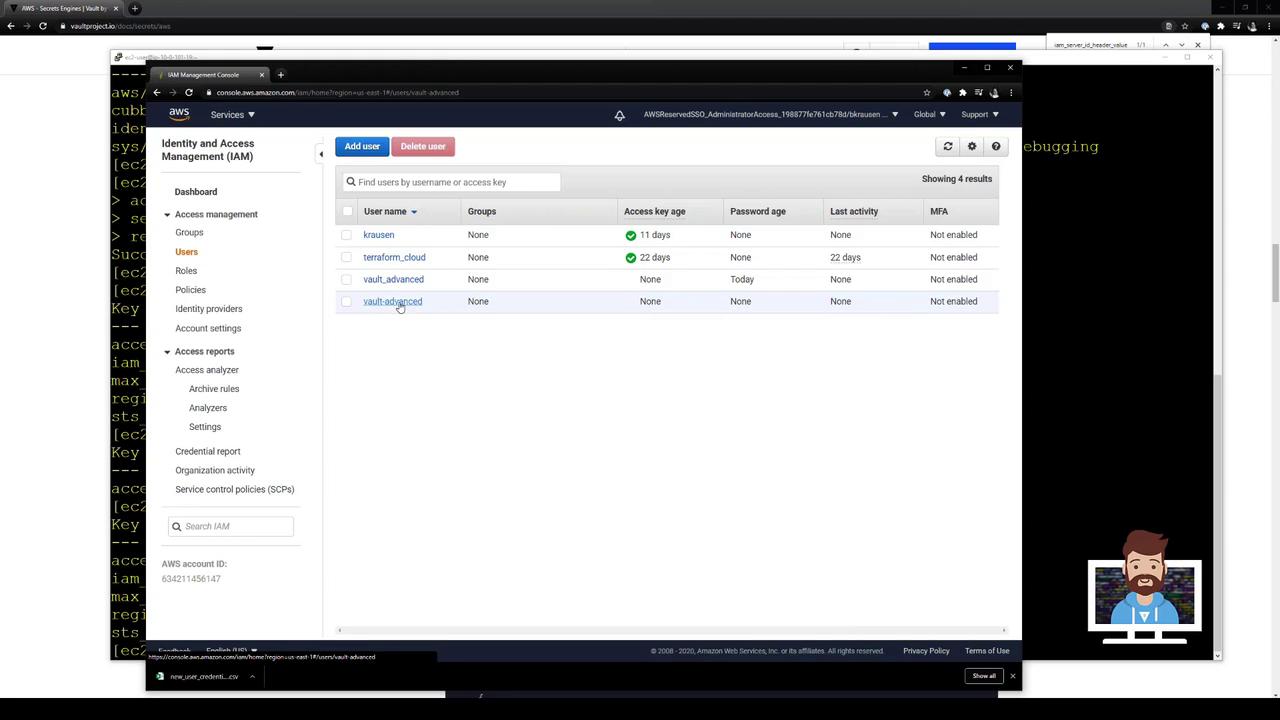
For this demonstration, create a Vault-specific IAM user with broad privileges:- In AWS Console, navigate to IAM → Users → Add user.
- Enable Programmatic access and click Next.
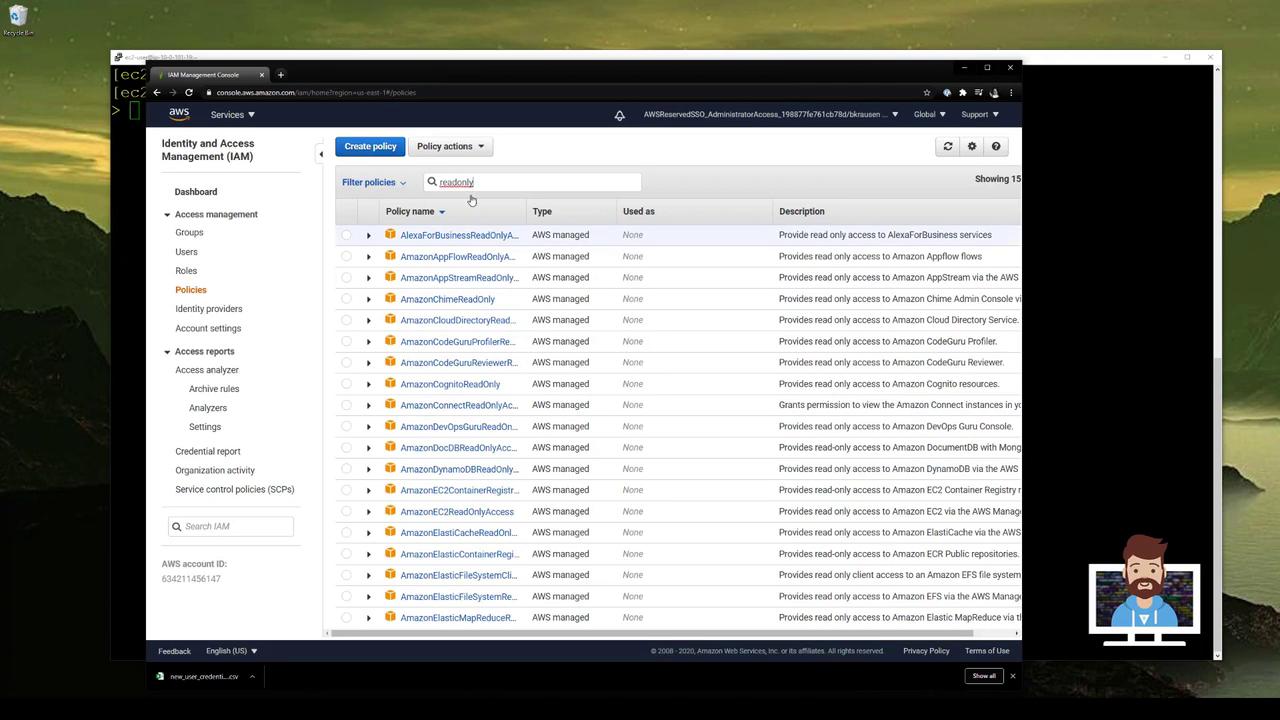
- Under Set permissions, choose Attach existing policies directly and select AdministratorAccess.
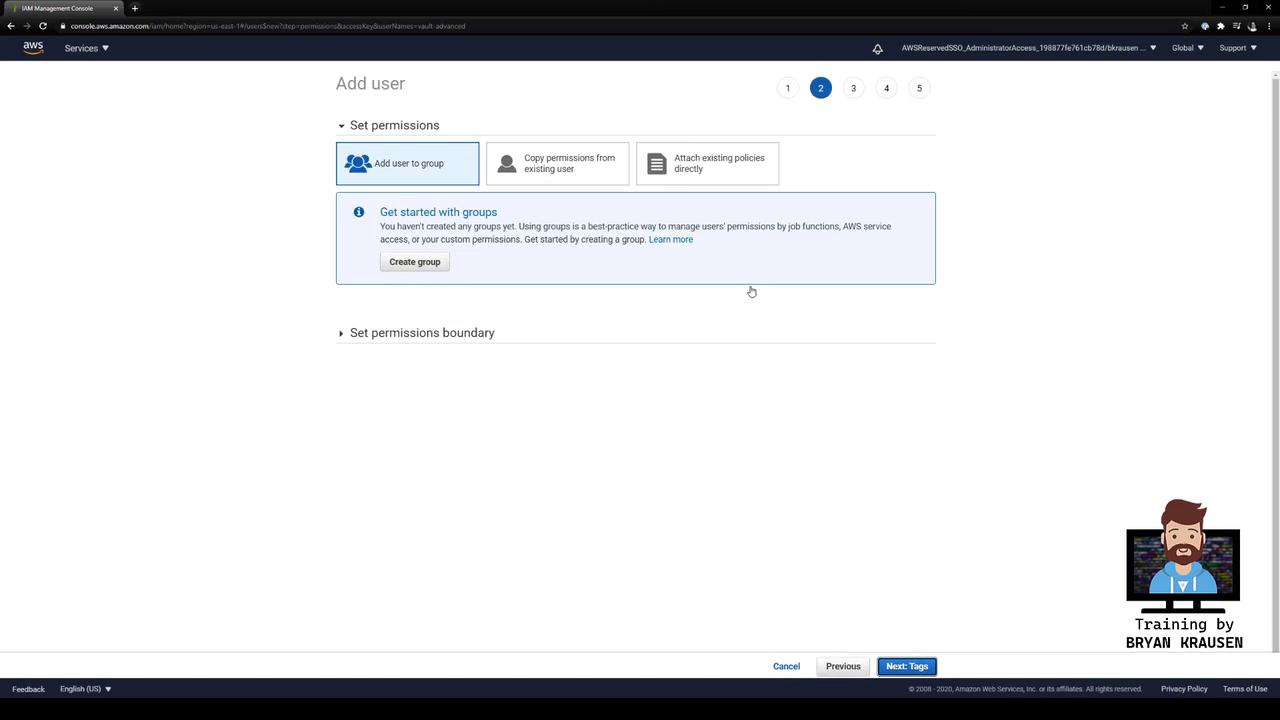
- Complete the wizard and download the access key ID and secret access key.

3. Configure Vault’s Root AWS Credentials
Point Vault at your new IAM user:4. Rotate Vault’s Root Credentials
Avoid long-lived credentials by rotating automatically:access_key—Vault created a fresh key pair in AWS and removed the old one.
5. Define a Vault Role for Dynamic IAM Users
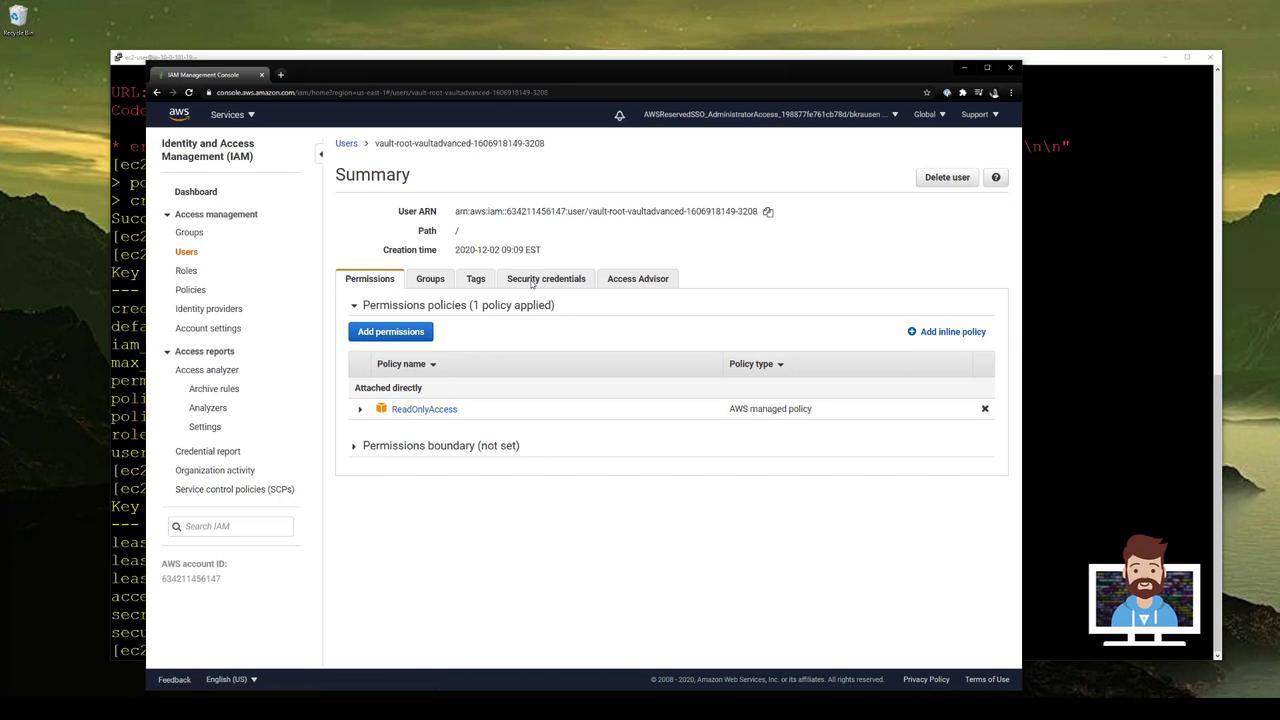
Each Vault role maps to one or more AWS IAM policies. Let’s createvaultadvanced using AWS’s ReadOnlyAccess managed policy:
6. Generate Dynamic IAM Credentials
Request a short-lived IAM user and keys:vaultadvanced-… with ReadOnlyAccess attached.
7. Revoke a Single Lease
To delete one credential before it expires:8. Revoke All Leases for a Role
After issuing multiple credentials: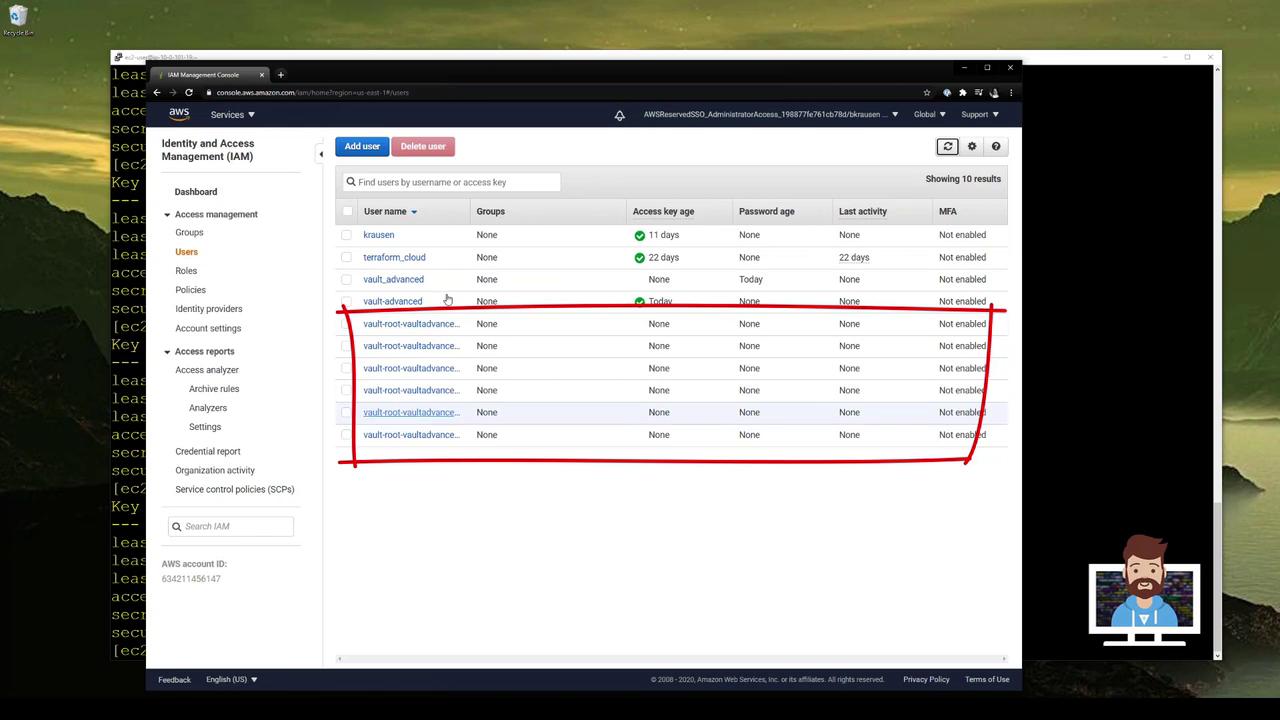
vaultadvanced:
Vault AWS Secrets Engine Endpoints
| Endpoint | Use Case | Example |
|---|---|---|
| aws/config/root | Configure root AWS credentials | vault write aws/config/root … |
| aws/config/rotate-root | Rotate root AWS credentials | vault write -force aws/config/rotate-root |
| aws/roles/<role> | Define dynamic IAM roles | vault write aws/roles/vaultadvanced … |
| aws/creds/<role> | Generate dynamic IAM credentials | vault read aws/creds/vaultadvanced |
| aws/creds/<role> (prefix revoke) | Bulk revoke IAM credentials | vault lease revoke -prefix aws/creds/vaultadvanced |