In this guide, we’ll walk through the essential components and steps required to install and run HashiCorp Vault. You’ll learn how to:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Prepare your system and environment
- Create and manage configuration files
- Initialize, seal, and unseal the Vault
- Choose storage backends and interfaces
Supported Platforms
- Kubernetes (self-hosted or managed services such as AKS, EKS)
- Cloud-based VMs (AWS EC2, Azure VM, Google Compute Engine)
- VMware virtual machines
- Physical servers (for isolated CPU and memory)
- Local workstations (laptops and desktops for development)
Supported Operating Systems

| Operating System | Typical Use Case |
|---|---|
| Linux | Production servers (Ubuntu, RHEL, etc.) |
| macOS | Local development on Apple hardware |
| Windows | Development or Windows-based servers |
| FreeBSD/NetBSD/OpenBSD/Solaris | Specialized or legacy environments |
Installation Workflow
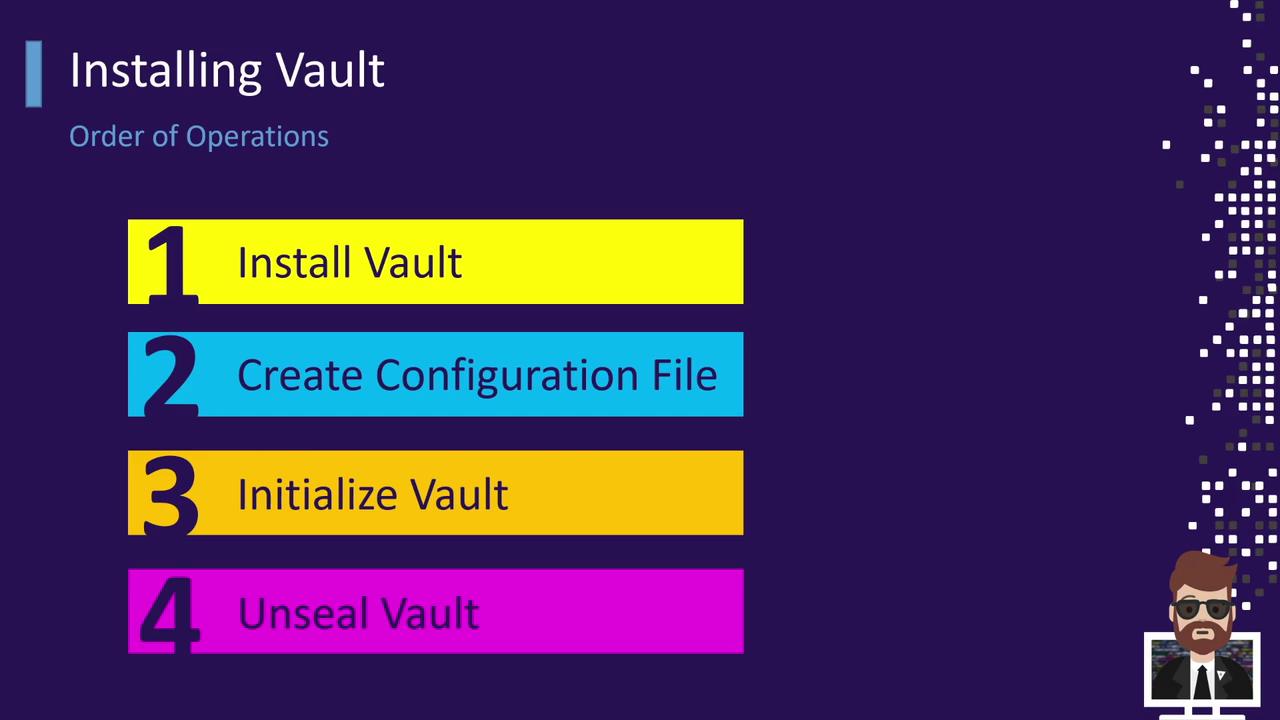
- Install the Vault binary
- Create or update the Vault configuration file
- Start the Vault server process
- Initialize the Vault (generates root tokens and unseal keys)
- Unseal Vault (use unseal keys to decrypt the storage)
Automating these steps with tools like Terraform, Ansible, or Helm can ensure consistency across environments.
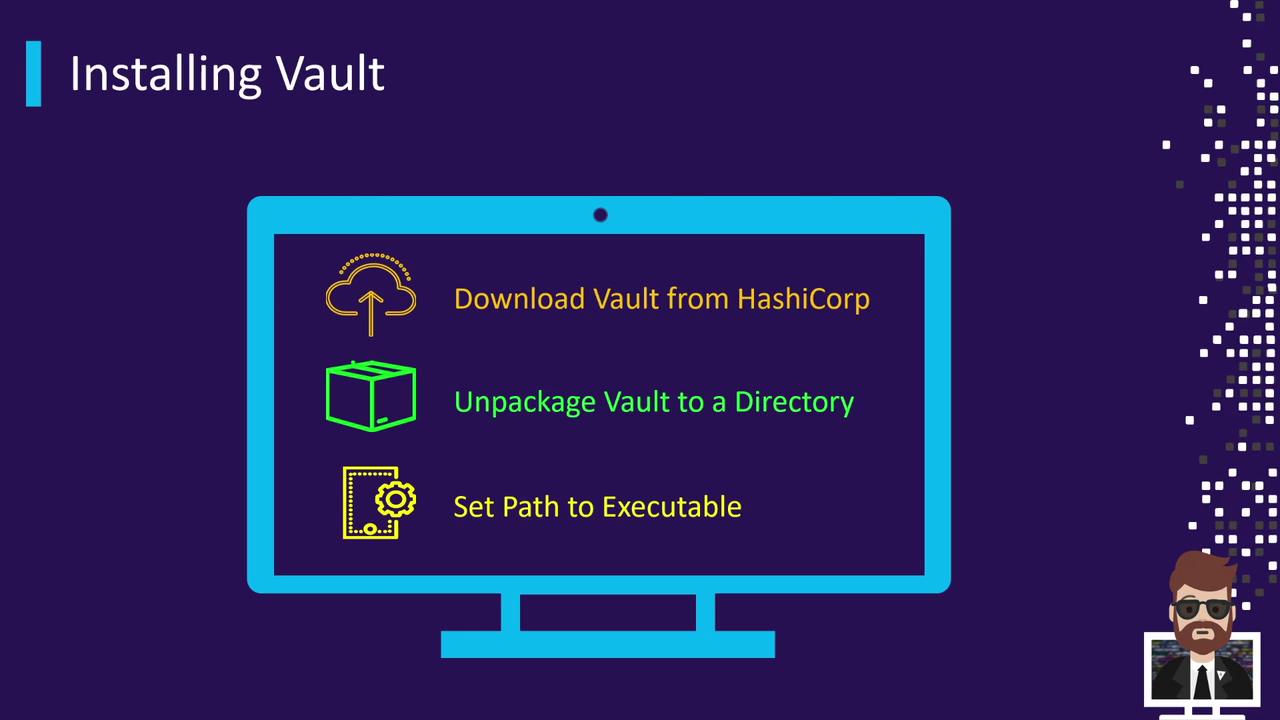
Installing Vault
You can install Vault in several ways: via system packages, Helm charts, or manual download. Choose the method that fits your environment.Using APT on Debian/Ubuntu
vault CLI into your system PATH.
Using Helm on Kubernetes
Manual Download and Installation
Next Steps
- Create a Vault configuration file (
vault.hcl) - Start the Vault server:
vault server -config=vault.hcl - Initialize:
vault operator init - Unseal:
vault operator unseal