Vault Policies are the core mechanism for enforcing authorization in HashiCorp Vault. By defining fine-grained permissions on Vault paths and operations, policies uphold the principle of least privilege. This ensures that diverse clients—DBAs creating dynamic database credentials, Packer builds pulling secrets, reporting applications querying data, CI/CD pipelines provisioning cloud resources, and administrators performing routine tasks—receive only the access they need.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Why Use Vault Policies?
- Enforce Role-Based Access Control (RBAC)
- Segregate duties across automation tools and human operators
- Protect sensitive paths and actions
- Minimize blast radius by granting minimal required capabilities
Always follow the principle of least privilege: grant only the permissions necessary for each client.
For detailed syntax and examples, see the official Vault Policy Syntax documentation.
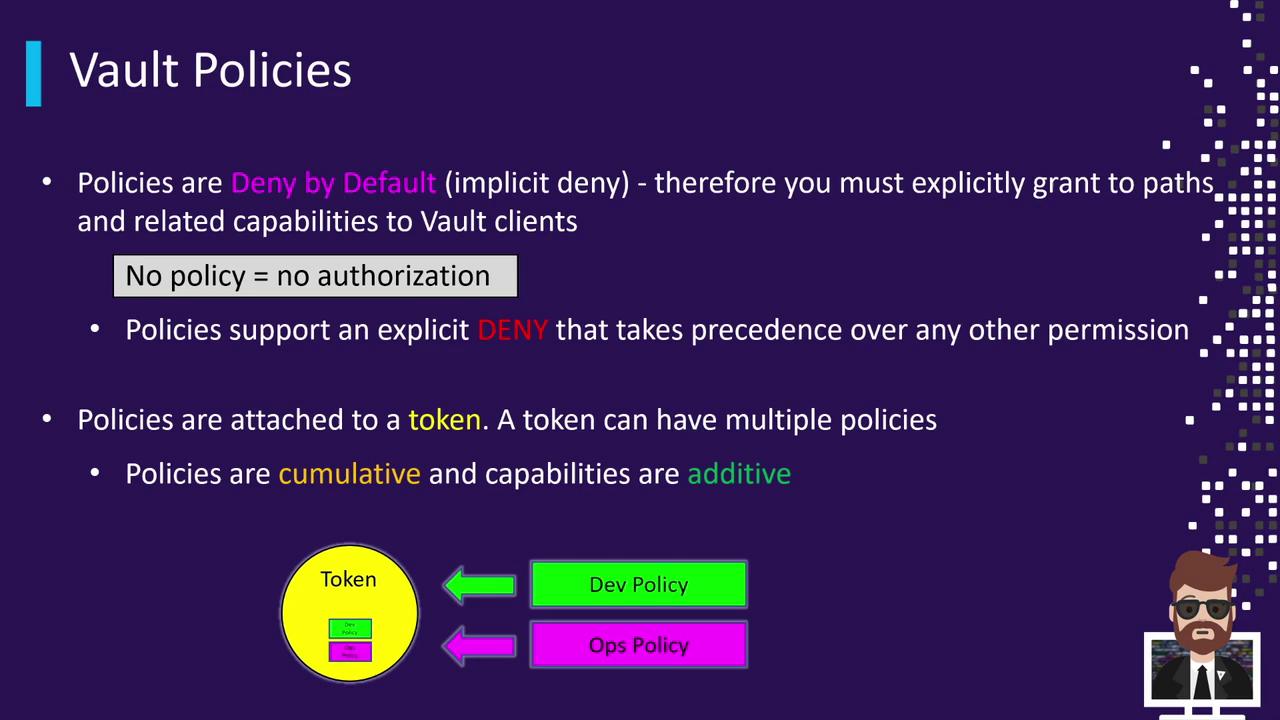
| Feature | Description |
|---|---|
| Deny by Default | Any access not explicitly granted is automatically denied. |
| Explicit Deny | You may override allow rules by explicitly denying specific paths or capabilities. |
| Cumulative | A token can have multiple policies attached; its effective permissions are the union of all. |
| Policy Name | Description | Modifiable | Attached To |
|---|---|---|---|
root | Grants unrestricted access to all Vault paths and actions. | No | All root tokens |
default | Allows basic token operations (lookup, renew, revoke). | Yes | All non-root tokens |
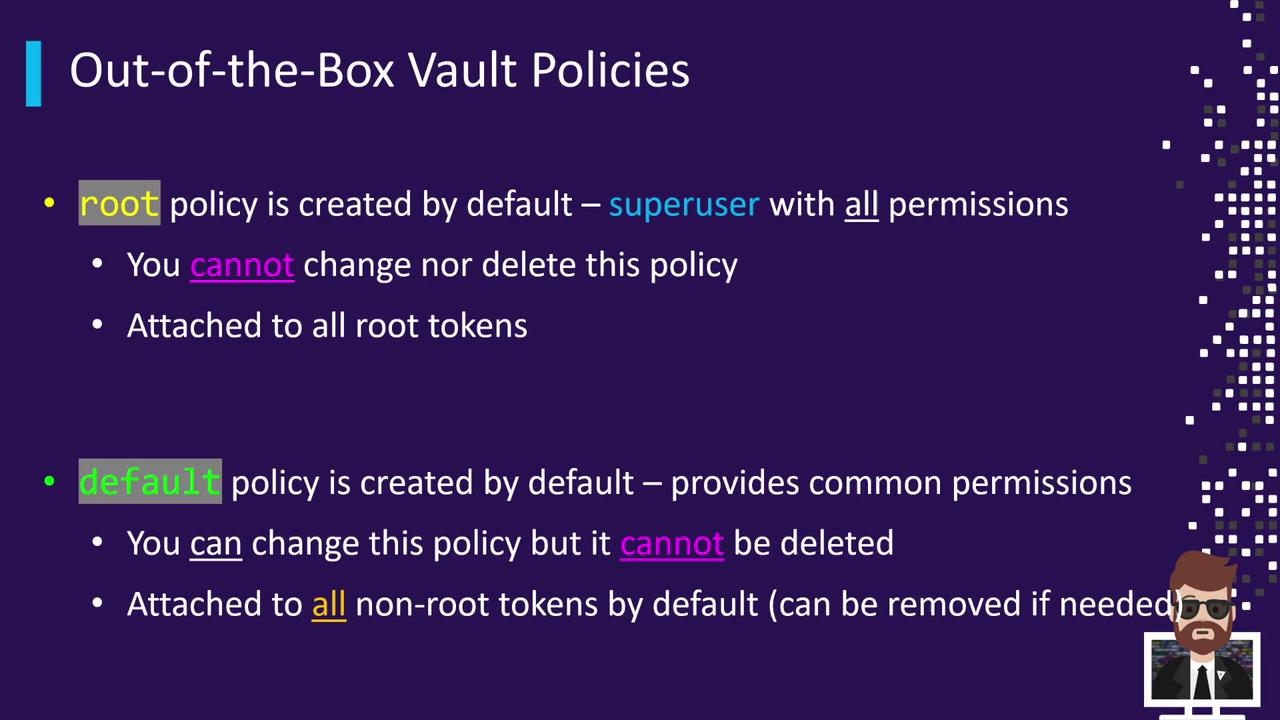
The
root policy is implicit and cannot be viewed, modified, or deleted.default policy:
root policy returns an error:
root policy behaves as if it contains: