In this guide, you’ll learn how to set up HashiCorp Vault to use Consul as its storage backend. Consul delivers a durable, highly available key–value store that scales independently, ensuring Vault’s data is stored reliably across clusters.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Why Choose Consul for Vault Storage
Consul offers robust features that enhance Vault’s resilience and scalability:| Feature | Benefit | Details |
|---|---|---|
| Durable KV Storage | High availability | Replicates data across 3–5 voting members for automatic failover. |
| Independent Scaling | Flexible capacity management | Scale Consul CPU and memory separately from Vault instances. |
| Built-in Integration | Service discovery & health | Vault registers itself in Consul for health checks and topology. |
| Automated Snapshots | Simplified backups | Create snapshots for backup and upgrades with minimal downtime. |
| Enterprise Support | Official HashiCorp support | Fully supported as a Vault backend in enterprise environments. |
Running a dedicated Consul cluster adds maintenance overhead—setup, ACLs, upgrades, and monitoring. However, with proper automation, it operates with minimal intervention.
Cluster Topology
- One Vault cluster ↔ One Consul cluster (no cross–data-center mixing)
- Odd number of nodes (3 or 5) ensures reliable leader election
- Leader nodes accept commits and replicate logs to followers
Dedicated Consul Cluster for Vault
To prevent resource contention and maintain performance, host Vault storage on a dedicated Consul cluster. Do not co-locate service discovery or mesh workloads on the same cluster.AWS Deployment Example
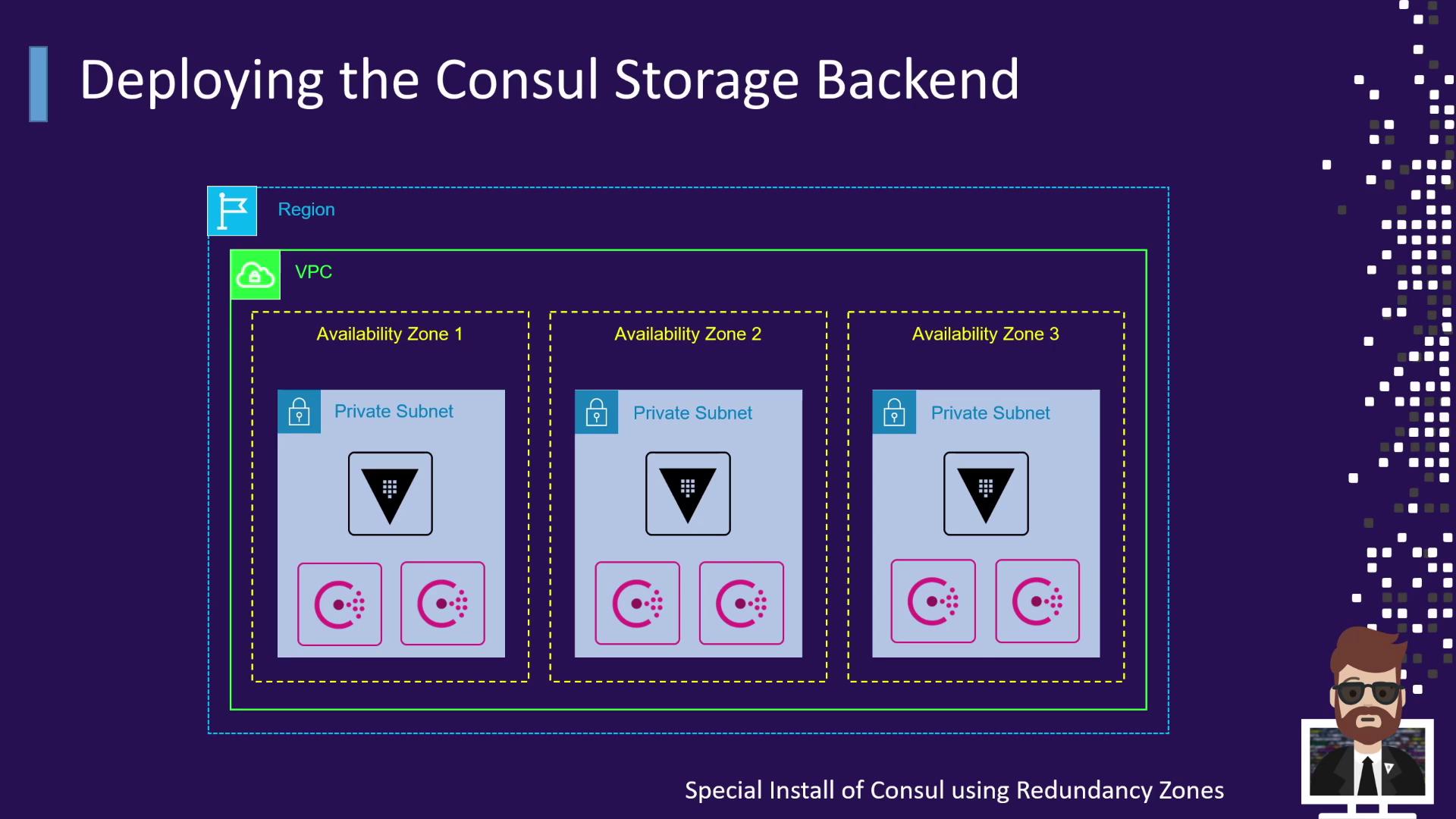
- Vault servers deployed in each AZ for redundancy
- Consul servers in each AZ, using enterprise Redundancy Zones
Vault Nodes & Local Consul Agents
Vault servers run a local Consul agent in client mode. Each agent joins the cluster and handles all API requests, so Vault always points to localhost: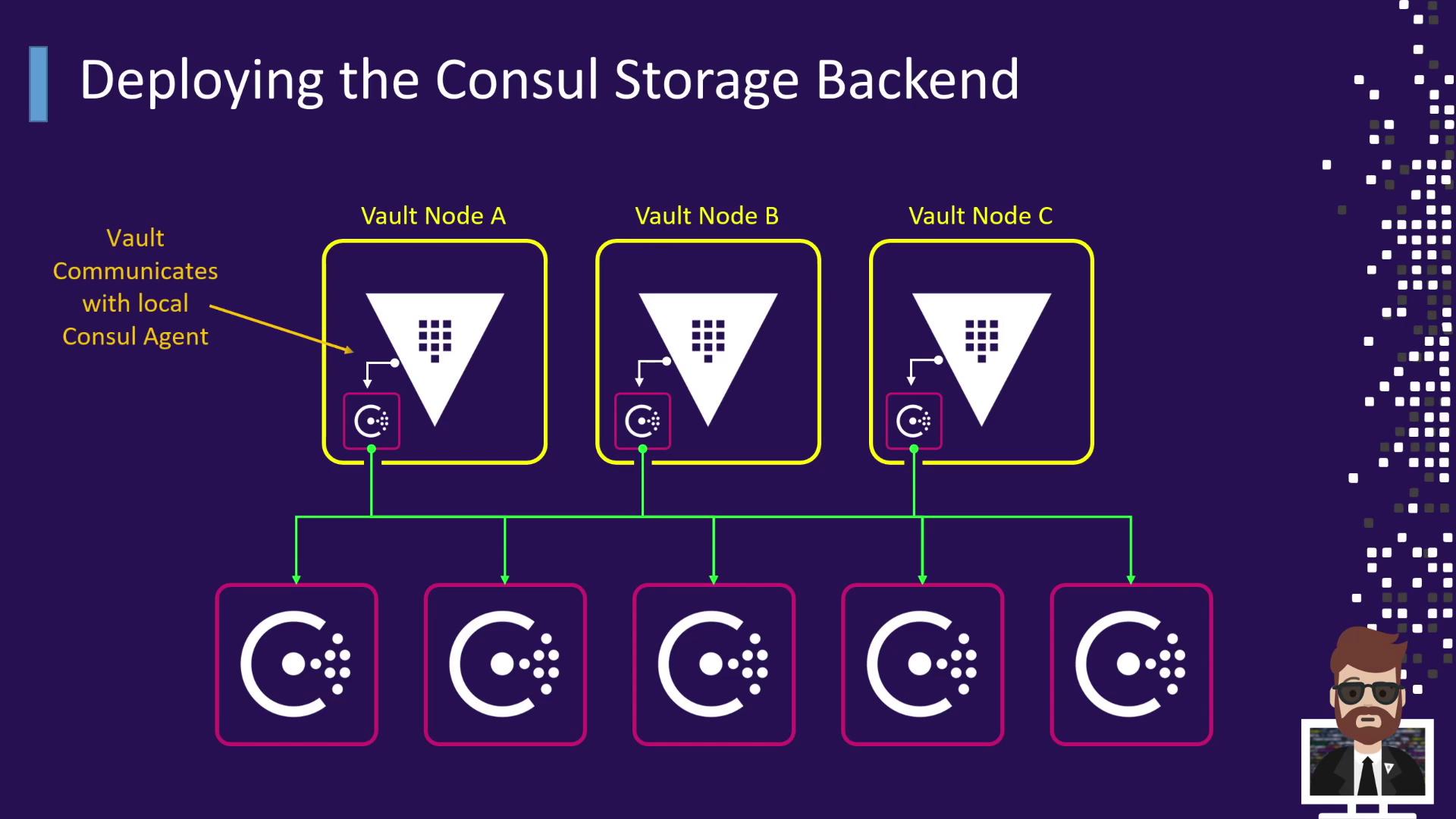
Vault Configuration Example
Below is a sample HCL configuration for Vault using Consul as the storage backend:Ensure the Consul ACL token has permissions scoped only to the
vault/ path. Rotate tokens periodically to maintain security.Consul Server Configuration Example
Place the following JSON in/etc/consul.d/server.json on each Consul server node: