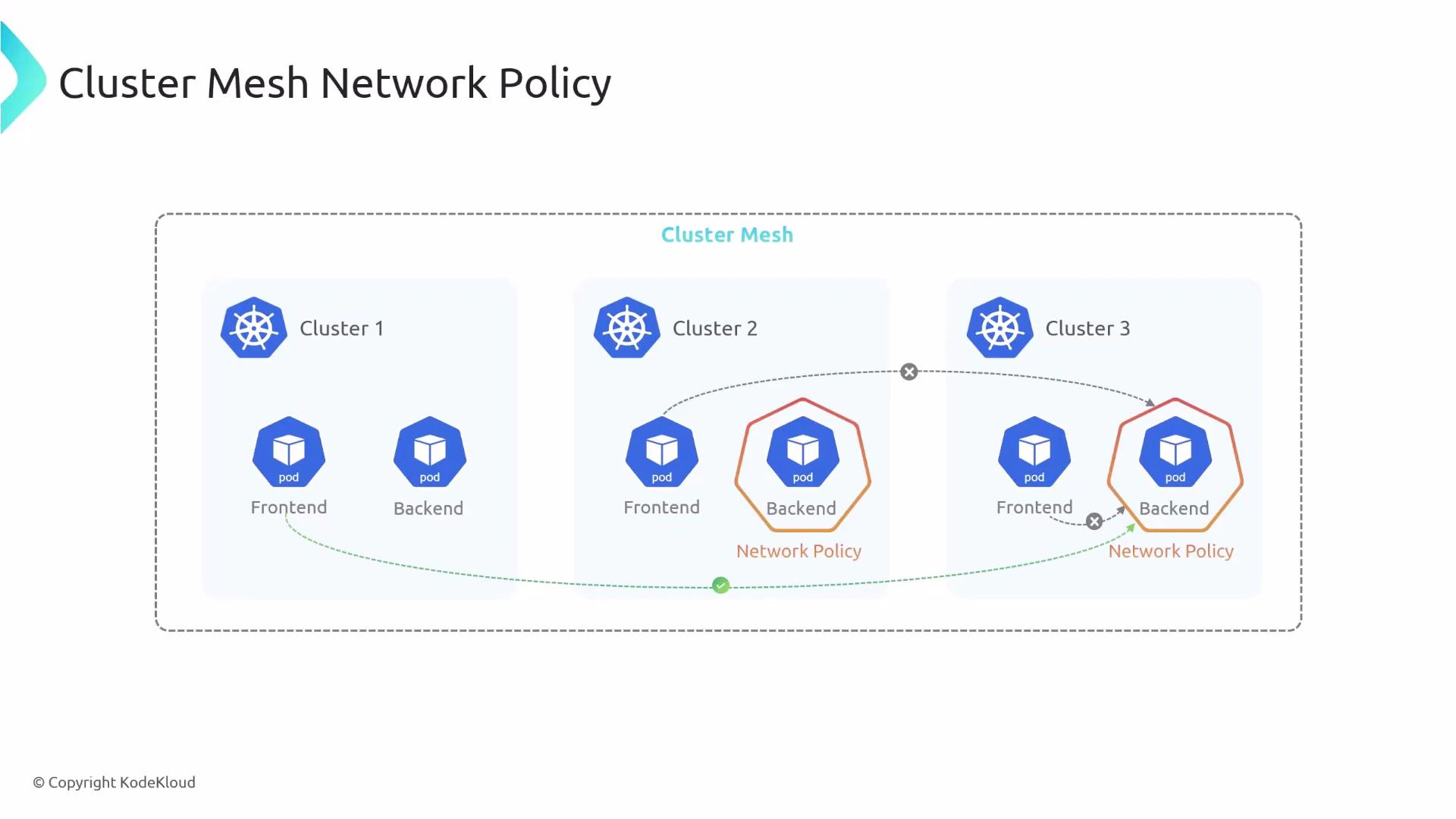
In this lesson we examine how Cilium network policies behave in a Cluster Mesh. When multiple Kubernetes clusters are joined into a Cilium Cluster Mesh, workloads can communicate across clusters, but policy enforcement remains per-cluster. That means deploying a CiliumNetworkPolicy on one cluster does not automatically propagate that policy to other clusters in the mesh—you must apply the same manifest on each cluster where you want it enforced. Below is a concrete example: a Cluster Mesh spanning three clusters (cluster1, cluster2, cluster3). Each cluster runs aDocumentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
frontend pod and a backend pod. The CiliumNetworkPolicy shown is applied on Cluster Two and selects backend endpoints there, allowing ingress only from frontend endpoints that carry a specific origin-cluster label (io.cilium.k8s.policy.cluster: cluster1). Effectively, this permits only frontends from cluster1 to connect to backends on cluster2; frontends from cluster2 and cluster3 are denied by this policy.
- Scope: This manifest is applied on Cluster Two and restricts ingress to backend pods in Cluster Two.
- Behavior: Frontend pods from Cluster One (
cluster1) are allowed to reach backend pods on Cluster Two; frontends in Cluster Two and Cluster Three are denied by this rule. - Enforcement: To enforce the same restriction on backend pods in Cluster Three (or Cluster One), apply the identical manifest to those clusters as well.
| Topic | Explanation | Example / Command |
|---|---|---|
| Per-cluster enforcement | CiliumNetworkPolicy is evaluated by the Cilium agent running in each cluster. A policy applied in one cluster does not automatically apply in other clusters. | kubectl apply -f allow-cross-cluster.yaml --context=cluster2 |
| Matching by origin cluster | Use the label io.cilium.k8s.policy.cluster on endpoints to match traffic originating from a specific member cluster in the Cluster Mesh. | io.cilium.k8s.policy.cluster: cluster1 |
| Deploying to multiple clusters | Apply the same manifest to each cluster where you want identical enforcement. Use context switching or automation to distribute policies. | See example loop below. |
Network policies in a Cluster Mesh are enforced per cluster. You can match endpoint traffic by origin using the
io.cilium.k8s.policy.cluster label, but to enforce a policy across the mesh you must apply the same policy manifest in every cluster where enforcement is required.- Cilium Documentation — Network Policies: https://cilium.io/docs/
- Kubernetes Networking Concepts: https://kubernetes.io/docs/concepts/services-networking/network-policies/
- Cilium Cluster Mesh: https://cilium.io/blog/2020/10/29/cilium-clustermesh