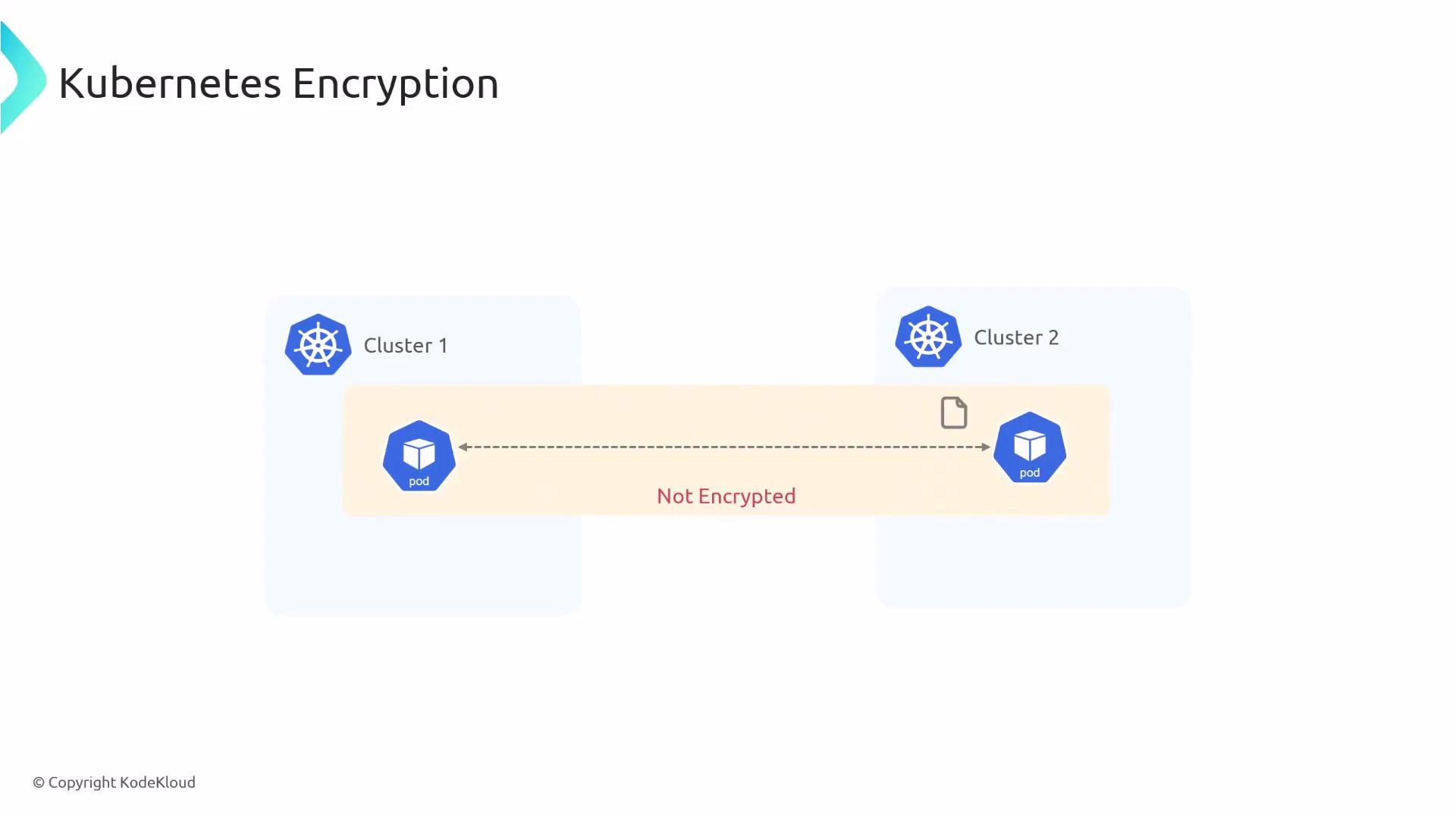
In this lesson you’ll learn how to enable transparent pod-to-pod encryption in Kubernetes using Cilium. By default, pod traffic inside a cluster is unencrypted, so an attacker who can capture network packets may be able to read sensitive data. Cilium provides two built-in methods to secure inter-node pod traffic:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- IPsec
- WireGuard
| Feature | IPsec | WireGuard |
|---|---|---|
| Performance | Mature, widely supported | High-performance, simpler codebase |
| Key management | Secret keys in Kubernetes | Keys managed by Cilium (peer-based) |
| Compatibility | Works across many kernels | Requires WireGuard support in kernel or module |
| Typical use case | Stable enterprise setups | High-throughput, low-latency environments |
Before you begin: ensure you have kubectl access to the cluster, Cilium installed (via Helm, CiliumOperator/CiliumConfig, or daemonset), and permissions to create secrets in the kube-system namespace.
Creating the IPsec key secret
Cilium expects an IPsec secret in Kubernetes with the following format: key-id algorithm psk-in-hex key-size The command below generates a random PSK (in hex) and stores it in thekube-system namespace as the secret cilium-ipsec-keys. The example creates one key entry (key ID 1) using RFC4106 AES-GCM with a 128-bit key.
Protect your PSKs: store/retrieve secrets using secure tooling (e.g., external KMS or sealed-secrets) and rotate keys periodically. Exposing PSKs compromises all encrypted traffic.
Enabling IPsec in the Cilium Helm values
Update your Cilium configuration (Helmvalues.yaml or CiliumConfig/DaemonSet settings) to enable encryption and set the type to ipsec:
Verify IPsec encryption
Exec into a Cilium agent pod and run the Cilium debug command to inspect encryption state and keys in use:Enabling WireGuard
To enable WireGuard instead of IPsec, set thetype to wireguard in the same configuration area:
Encryption behavior
Cilium only encrypts pod-to-pod traffic that traverses the network between different nodes. Pods communicating on the same node exchange traffic locally and this traffic is not encrypted by Cilium. This design reduces overhead and is based on the assumption that an attacker who can read local node traffic likely already has privileged access to that node.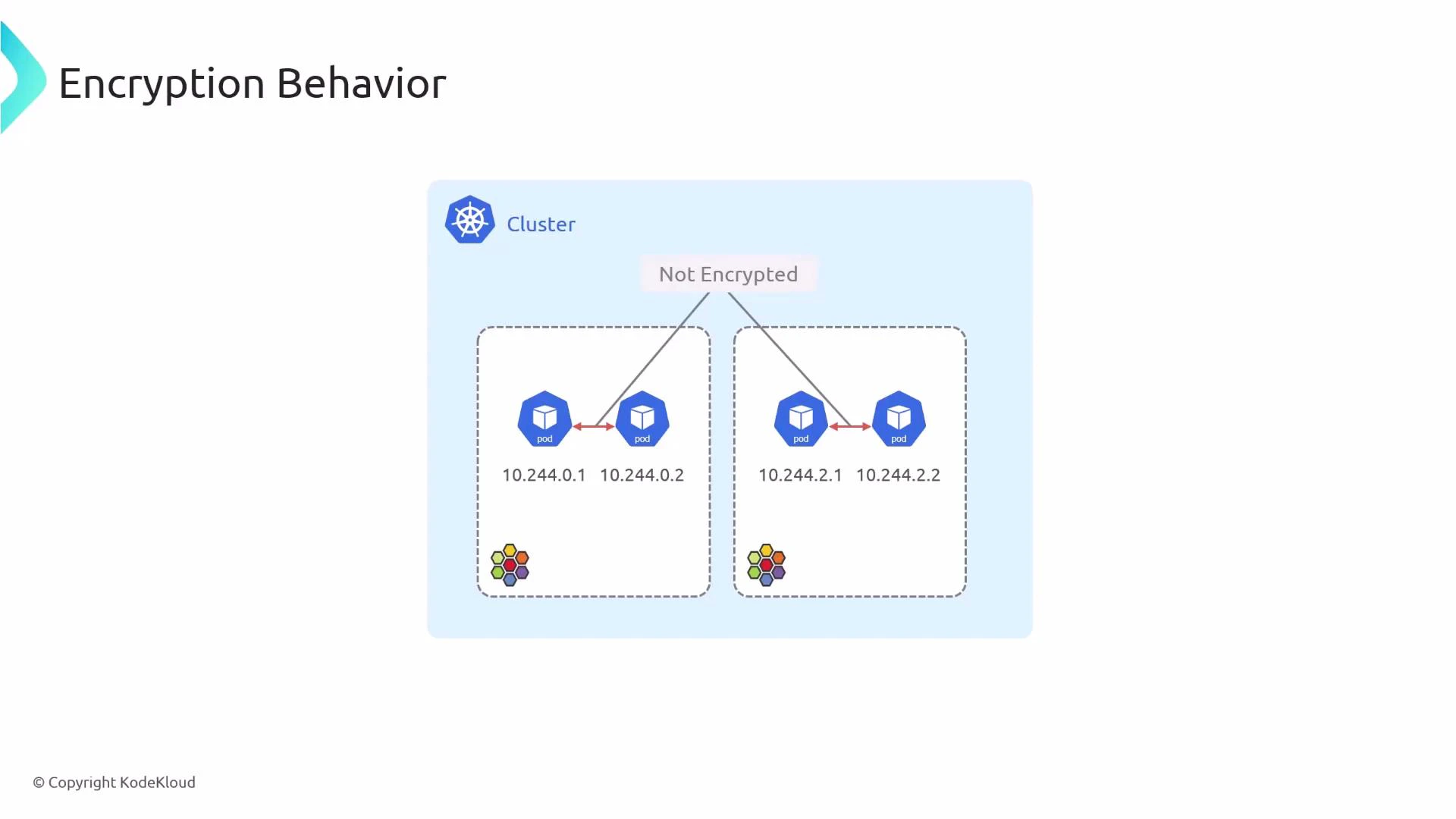
Traffic between pods on the same node is left unencrypted because protecting it would not stop an attacker who already has root on that node. Cilium focuses on encrypting inter-node pod traffic — the traffic that traverses the network where interception is possible without node compromise.
- Cilium encryption docs: https://docs.cilium.io/en/stable/concepts/encryption/
- WireGuard: https://www.wireguard.com/
- IPsec overview: https://datatracker.ietf.org/wg/ipsecme/about/