This lesson gives a clear, concise overview of the Cilium Certified Associate (CCA) exam: who should take it, what competencies it validates, how the exam is delivered, and the domain breakdown you should study. It’s aimed at platform and cloud engineers working with Kubernetes who want foundational knowledge in networking, security, and observability using Cilium. Cilium Certified Associate (CCA) is an entry-level certification that validates your ability to connect, secure, and observe Kubernetes clusters using Cilium. Passing demonstrates familiarity with Cilium’s architecture, features, common use cases, and the basic operational commands and troubleshooting patterns.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
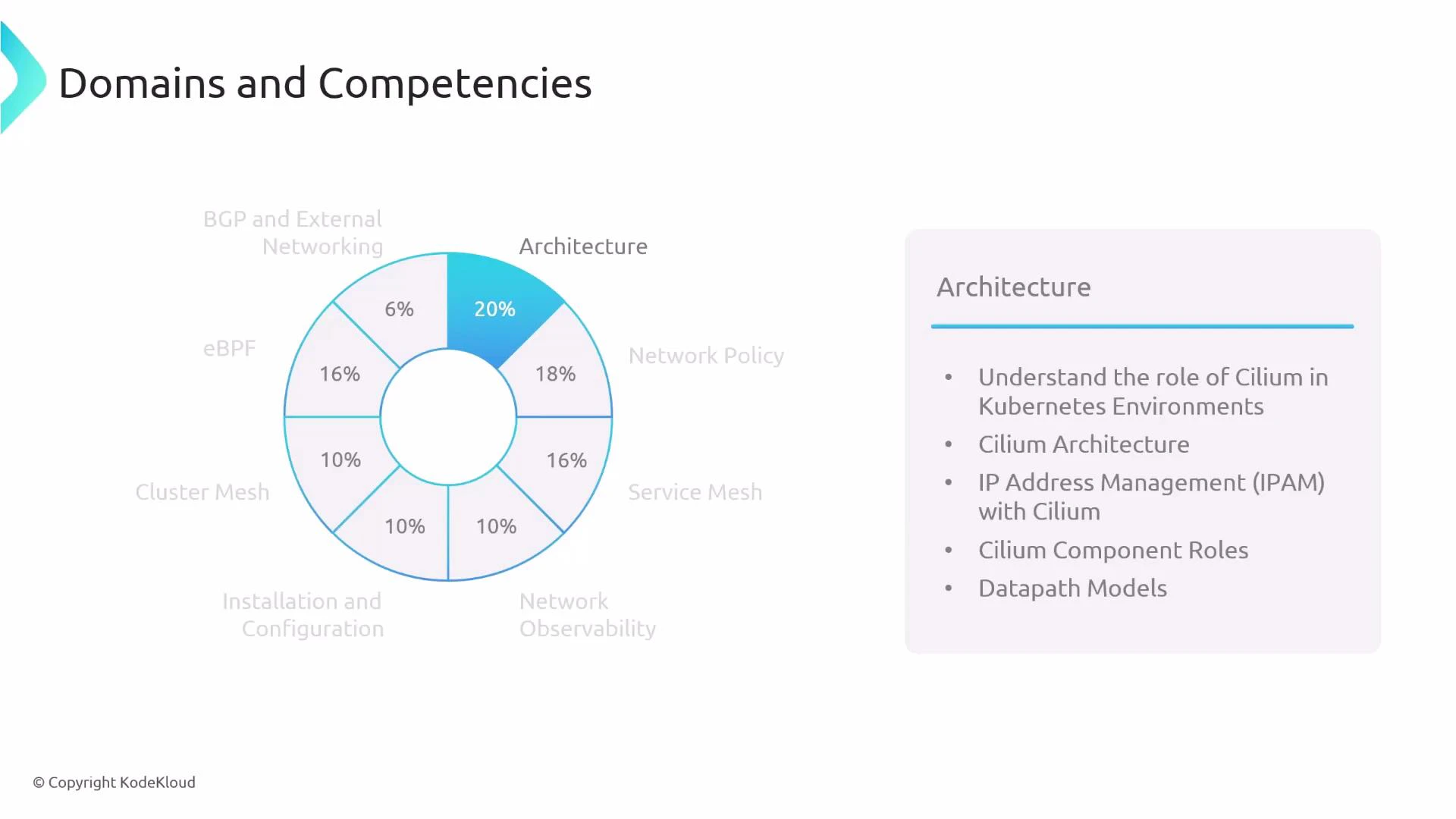
This overview focuses on the knowledge you’ll be expected to demonstrate: Cilium architecture, network policy, observability (Hubble), eBPF fundamentals, installation/operations, Cluster Mesh, and external networking (BGP). Use the domain weights below to prioritize study time.
| Item | Details |
|---|---|
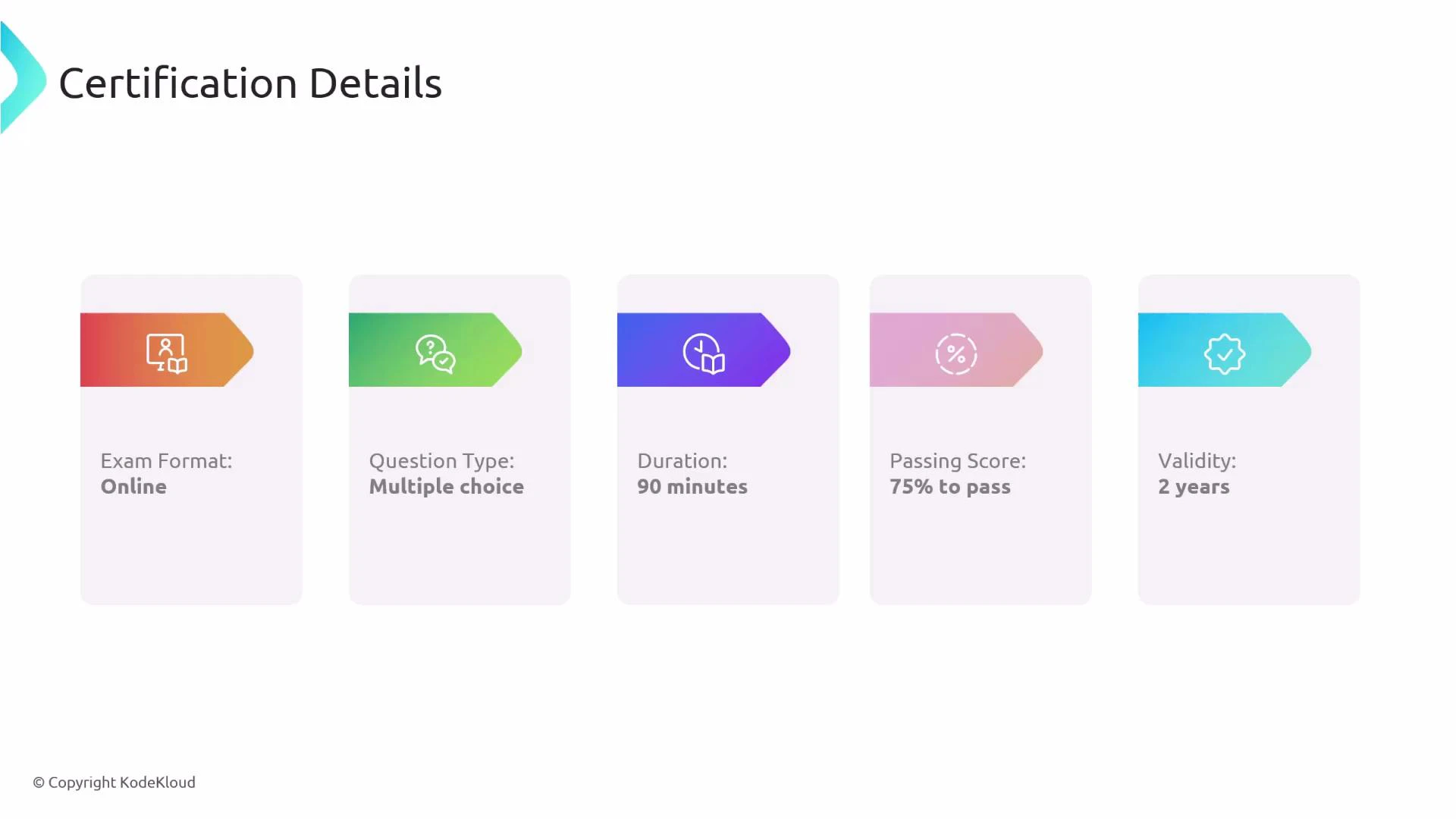
| Delivery | Online, proctored |
| Question type | Multiple-choice only (no hands-on labs) |
| Duration | 90 minutes |
| Passing score | 75% |
| Certification validity | 2 years |
The exam is proctored — the proctor has access to your webcam and microphone. Prepare your environment (lighting, background, and ID) and follow the proctor’s instructions to avoid interruptions or disqualification.
| Domain | Approx. weight |
|---|---|
| Architecture | 20% |
| Network Policy | 18% |
| eBPF | 16% |
| Service Mesh | 16% |
| Network Observability | 8% |
| Installation & Configuration | 8% |
| Cluster Mesh | 8% |
| BGP and External Networking | 6% |
- Understand Cilium’s role within a Kubernetes environment and how it complements the Kubernetes control plane and data plane.
- Know the major components and responsibilities: Cilium agent, Cilium operator, datapath components (e.g., eBPF programs), and clustering support.
- Understand IPAM approaches and the datapath models that Cilium supports (how pod addressing and routing are handled).
- Be able to reason about where policy enforcement and observability hooks exist in the architecture.
- Interpret and reason about Cilium Network Policies and the intent behind policy rules. See Cilium policy docs: https://docs.cilium.io/en/stable/policy/
- Understand Cilium’s identity-based security model (endpoints are selected by identity derived from labels) and how this differs from IP-only approaches.
- Know the structure of policy rules, selectors, L3/L4 vs. L7 controls, and enforcement considerations.
- Compare Kubernetes NetworkPolicy (IP-centric) vs. Cilium NetworkPolicy (richer L7 capabilities and flexible selectors): https://kubernetes.io/docs/concepts/services-networking/network-policies/ and https://docs.cilium.io/en/stable/policy/
- Know basic service mesh concepts and common use cases (mTLS, traffic routing, observability).
- Understand ingress routing using Kubernetes Ingress resources and the newer Gateway API; know why the Gateway API addresses limitations of legacy Ingress: https://gateway-api.sigs.k8s.io/ and https://kubernetes.io/docs/concepts/services-networking/ingress/
- Be familiar with Cilium options for encrypting traffic in transit and approaches to East-West and North-South encryption.
- Understand differences between traditional sidecar-based meshes and sidecar-less architectures and how Cilium can enable sidecar-less or lighter-weight proxying.
- Be familiar with Hubble (Cilium’s observability tool) and how it provides flow visibility and troubleshooting: https://www.cilium.io/docs/concepts/hubble/
- Know how to enable L7 protocol visibility, use Hubble CLI to inspect flows, and use the Hubble UI for graphical insights.
- Know how to install and configure Cilium using the Cilium CLI and common workflows for verifying health and connectivity: https://docs.cilium.io/en/stable/gettingstarted/
- Be able to perform common operational checks and run connectivity tests.
- Understand Cluster Mesh concepts and how it enables multi-cluster connectivity and service discovery across clusters: https://docs.cilium.io/en/stable/concepts/clustermesh/
- Know how Cluster Mesh supports cross-cluster load balancing and the trade-offs involved (consistency, latency, and operational overhead).
- Understand the role of eBPF in Cilium’s architecture: how kernel eBPF programs implement networking, security, and observability features.
- Know the advantages eBPF provides over legacy iptables-based approaches: improved performance, programmability, lower latency, and finer-grained control. Learn more at https://ebpf.io/
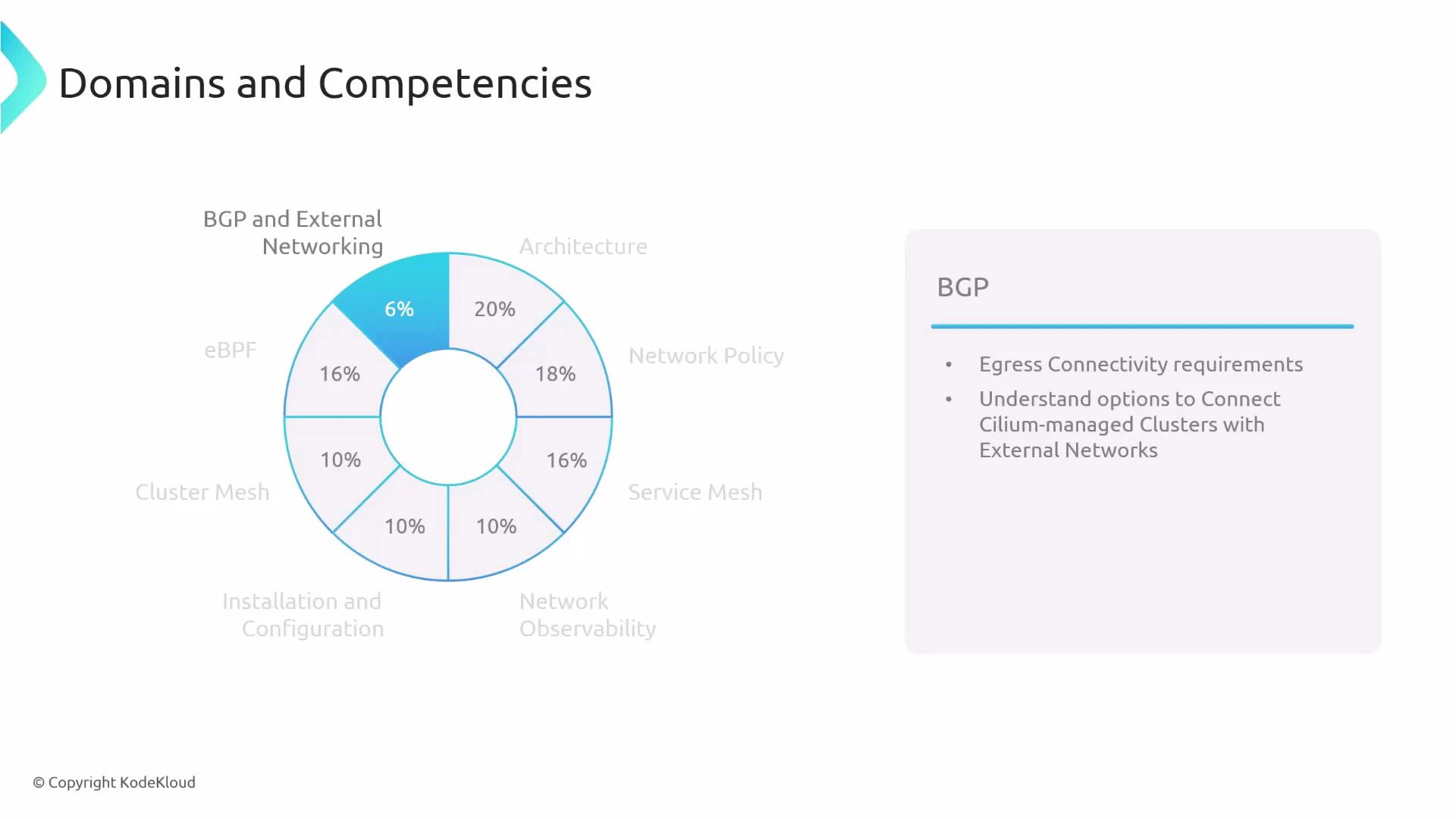
- Understand egress and external connectivity considerations and how Cilium integrates with external routers and networks.
- Know the basics of advertising services and routes to external networks (for example using BGP) so cluster services can be reachable outside the cluster.
- Start with conceptual understanding: architecture, identity-based security, and eBPF fundamentals.
- Practice reading and reasoning about policies — translate policy intent into expected behavior.
- Use the Cilium CLI to install a test cluster, inspect status, run connectivity tests, and explore Hubble flows.
- Prioritize domains by weight: focus first on Architecture, Network Policy, eBPF, and Service Mesh, then cover Observability, Installation, Cluster Mesh, and BGP.
- Cilium documentation: https://docs.cilium.io/
- Hubble (observability): https://www.cilium.io/docs/concepts/hubble/
- Cilium Network Policy: https://docs.cilium.io/en/stable/policy/
- Kubernetes NetworkPolicy: https://kubernetes.io/docs/concepts/services-networking/network-policies/
- Cilium Getting Started / CLI: https://docs.cilium.io/en/stable/gettingstarted/
- Cluster Mesh concepts: https://docs.cilium.io/en/stable/concepts/clustermesh/
- eBPF overview: https://ebpf.io/
- Gateway API: https://gateway-api.sigs.k8s.io/