In this lesson we cover the Kubernetes Gateway API and how Cilium implements it. We’ll first examine why the Gateway API was created (the limitations of the traditional Ingress) and then walk through Gateway API concepts, manifests, Cilium-specific configuration, and runtime expectations.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Why Gateway API? Limitations of Kubernetes Ingress
Kubernetes Ingress is widely used but has constraints that motivated a more expressive, extensible API:- Route matching is limited to host and path only — no request-header or query-parameter matching, no method-based routing, and no weighted traffic-splitting.
- Focused primarily on HTTP; lacks standardized first-class support for other protocols such as TCP and gRPC, or richer behaviors (e.g., standardized WebSocket handling).
- Minimal standardized request/response manipulation: no built-in, consistent mechanism for header rewrites, redirects, or rate limiting across implementations.
- Controller-specific configuration is commonly buried in annotations, mixing platform/operator concerns with application routing configuration.
- TLS and routing rules often live in the same Ingress resource, reducing separation of concerns and clear responsibility boundaries.
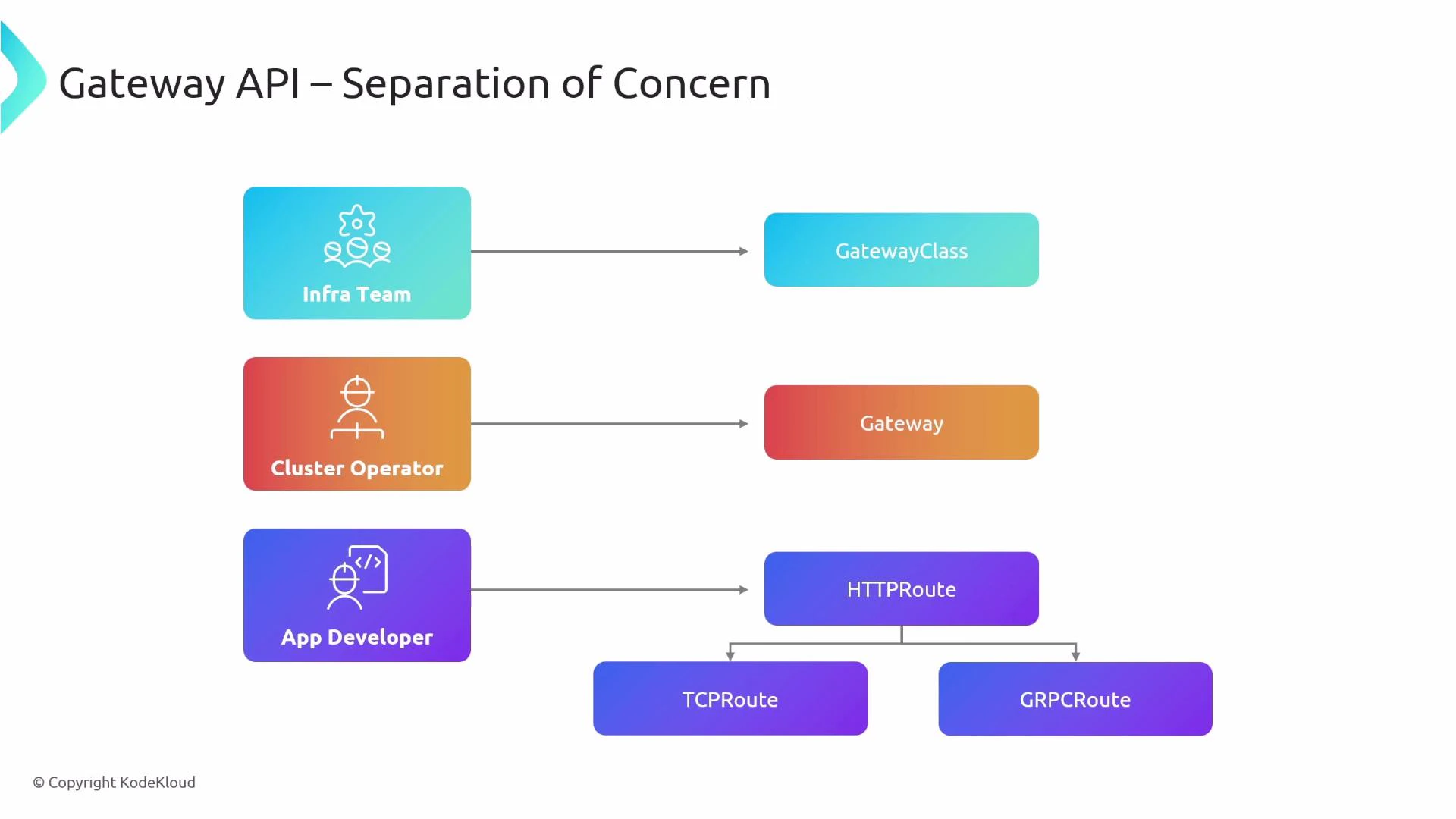
Gateway API: Separation by design
The Gateway API was designed to address these issues by splitting responsibilities into multiple resources so different teams can manage different concerns. Key Gateway API resource types and responsibilities:| Resource Type | Purpose | Typical Owner |
|---|---|---|
| GatewayClass | Declares available gateway controllers in the cluster. | Infra / platform teams |
| Gateway | Instantiates and configures a gateway instance (listeners, ports). | Cluster operators |
| Route types (HTTPRoute, TCPRoute, GRPCRoute, etc.) | Define routing policy: hostnames, matches, backends. | Application developers |
Cross-namespace routing and restrictions
Gateway API supports richer cross-namespace semantics and explicit restrictions:- A Gateway can be created in an infrastructure namespace and permit Routes from other namespaces to attach to it.
- Gateways can restrict which namespaces’ Routes are allowed to bind to them via
allowedRoutes.namespaces.from(e.g.,Same,All, orFromList). - This prevents arbitrary namespaces from attaching routes to a shared gateway and centralizes operator control.
Gateways can tightly control which namespaces may bind Routes. If you expect cross-namespace routing, verify the Gateway’s
allowedRoutes policy and, if needed, explicitly include the namespaces allowed to attach Routes.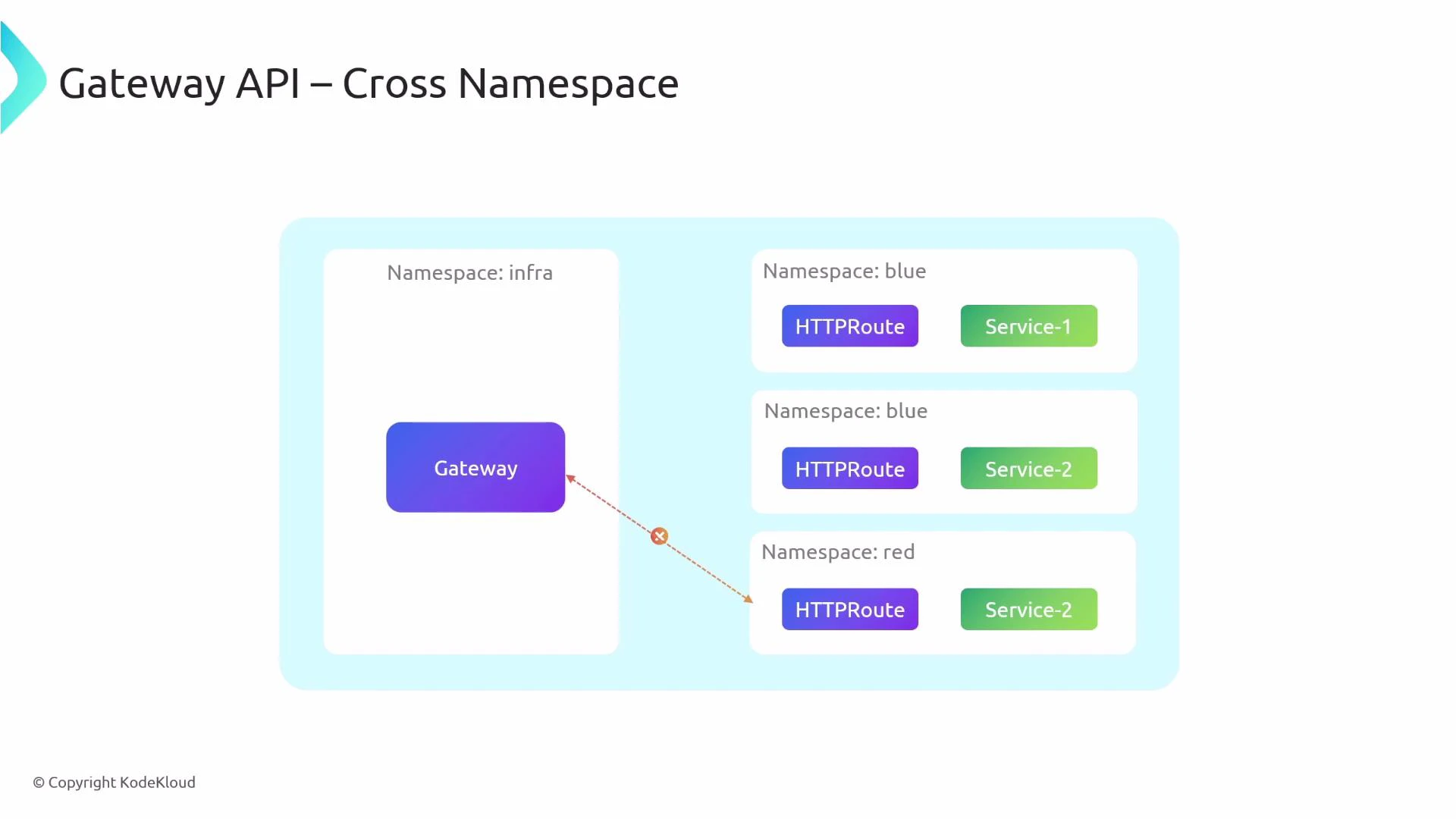
How-to: Basic Gateway API manifests
Below is a typical flow for deploying Gateway API resources. These examples show the separation of roles and their respective manifests.- Define a GatewayClass (created by infra/platform):
- Create a Gateway instance (created by the cluster operator). Example: listens on HTTP port 80 and only allows Routes from the same namespace.
- Application developers create an HTTPRoute that binds to the Gateway and instructs it how to route specific hostnames and paths to services:
Cilium’s Gateway API implementation
Cilium supports the Gateway API and provides a controller implementation you can enable via its Helm values or other configuration mechanism. Example Helm values snippet to enable NodePort and Gateway API support:After enabling gatewayAPI in Cilium, Cilium will automatically create a GatewayClass named cilium (or a similar name) for its controller. Use that GatewayClass name when creating Gateway resources intended to be handled by Cilium.
Typical runtime behavior with Cilium
- Cilium installs/creates a GatewayClass (for example
cilium) for its controller. - When you create a Gateway that references that GatewayClass, Cilium provisions the gateway runtime (which can include a LoadBalancer Service).
- Create HTTPRoute (or other route types) that reference the Gateway; the gateway then forwards traffic to the backend services.
172.19.255.3), point your DNS entries at that IP so external traffic reaches the gateway.
Example Gateway + HTTPRoute for Cilium
Using thecilium GatewayClass:
Gateway manifest:
Quick comparison: Ingress vs Gateway API
| Capability | Ingress | Gateway API |
|---|---|---|
| Protocol support | Primarily HTTP | HTTP, TCP, gRPC, extensible |
| Matching | Host + Path | Host, Path, Headers, Query params, Methods, weighted splits (depending on implementation) |
| Ownership model | Single resource mixes concerns | Clear separation: GatewayClass, Gateway, Route |
| Namespace scoping | Limited | Explicit allowedRoutes and cross-namespace options |
| Controller config | Annotations (controller-specific) | Controller model with GatewayClass and typed fields |
Summary
- Gateway API resolves many Ingress limitations by separating responsibilities, enabling richer routing semantics, and supporting multiple protocols.
- Use GatewayClass (infra), Gateway (operators), and Route resources (developers) to establish clear ownership.
- Cilium provides a Gateway API implementation. Enable
gatewayAPIand, if needed,nodePortin Cilium configuration, then create Gateway and Route resources that reference the Cilium GatewayClass.