In this lesson you’ll learn how Cilium’s policy audit mode works and how to enable it. Policy audit mode lets you observe what a CiliumNetworkPolicy would do (allow or deny) without actually dropping traffic. This is useful for validating policies safely before enforcing them in production. What does audit mode look like in practice? Consider three pods: frontend, backend, and db. You apply a policy that selects the db pod and allows ingress only from backend:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
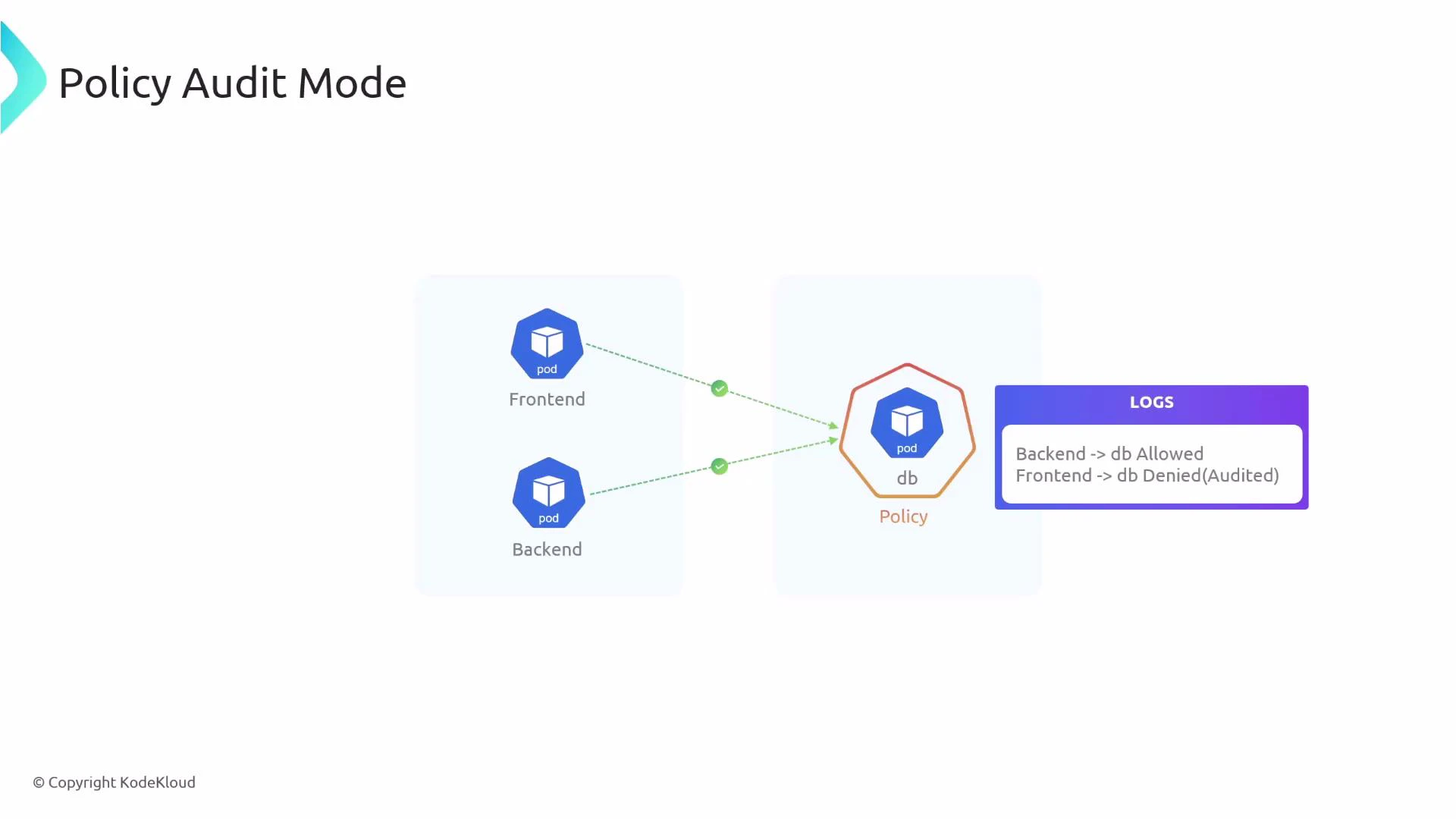
- Validate policies by observing “would-be” denies without impacting live traffic.
- Identify false positives or unintended blocks before switching to enforcement.
- Roll out complex network policies gradually and safely.
| Policy Verdict | Meaning |
|---|---|
| none (INGRESS AUDITED) | Traffic would be denied by policy, but audit mode allowed the flow and recorded the audited verdict. |
| L3-Only (INGRESS ALLOWED) | Traffic is allowed by the policy (L3 match) and is permitted. |
| other verdicts | May indicate more specific L4/L7 evaluation — inspect Hubble logs for details. |
- Globally (all endpoints) via Helm — requires restarting Cilium components.
- Per-endpoint (specific endpoints) using cilium-dbg — no cluster-wide restart required.
- Edit your Cilium Helm chart values to turn on audit mode:
- After updating Helm values, restart the Cilium operator and agent so the change takes effect:
- Use cilium-dbg inside a cilium-agent pod to change a single endpoint’s configuration. Replace variables with your values:
Policy audit mode is ideal for testing and validating network policies safely. Use it to identify unexpected denies and tune your rules before switching to enforcement.
Audit mode does not provide network isolation or enforce security controls. Do not rely on audit mode for protection — enable policy enforcement only after you have validated the behavior.
- Cilium Helm chart values: https://docs.cilium.io/en/stable/gettingstarted/helm/
- cilium-dbg tool: https://docs.cilium.io/en/stable/tools/cilium-dbg/
- Hubble (observability): https://docs.cilium.io/en/stable/gettingstarted/hubble/
- Cilium documentation: https://docs.cilium.io/