In our previous guide, we covered the basics of setting up Privileged Identity Management (PIM). In this article, we delve deeper into the configuration settings that control role activations and assignments in PIM, enhancing both security and flexibility. When assigning a role, eligible status is defined by default. However, for heightened security—such as enforcing Azure Multi-Factor Authentication (MFA) for access to critical databases or setting a maximum activation duration—these advanced configuration settings are crucial. Below is a screenshot that outlines these configuration settings before transitioning to a detailed walkthrough in the Azure portal.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
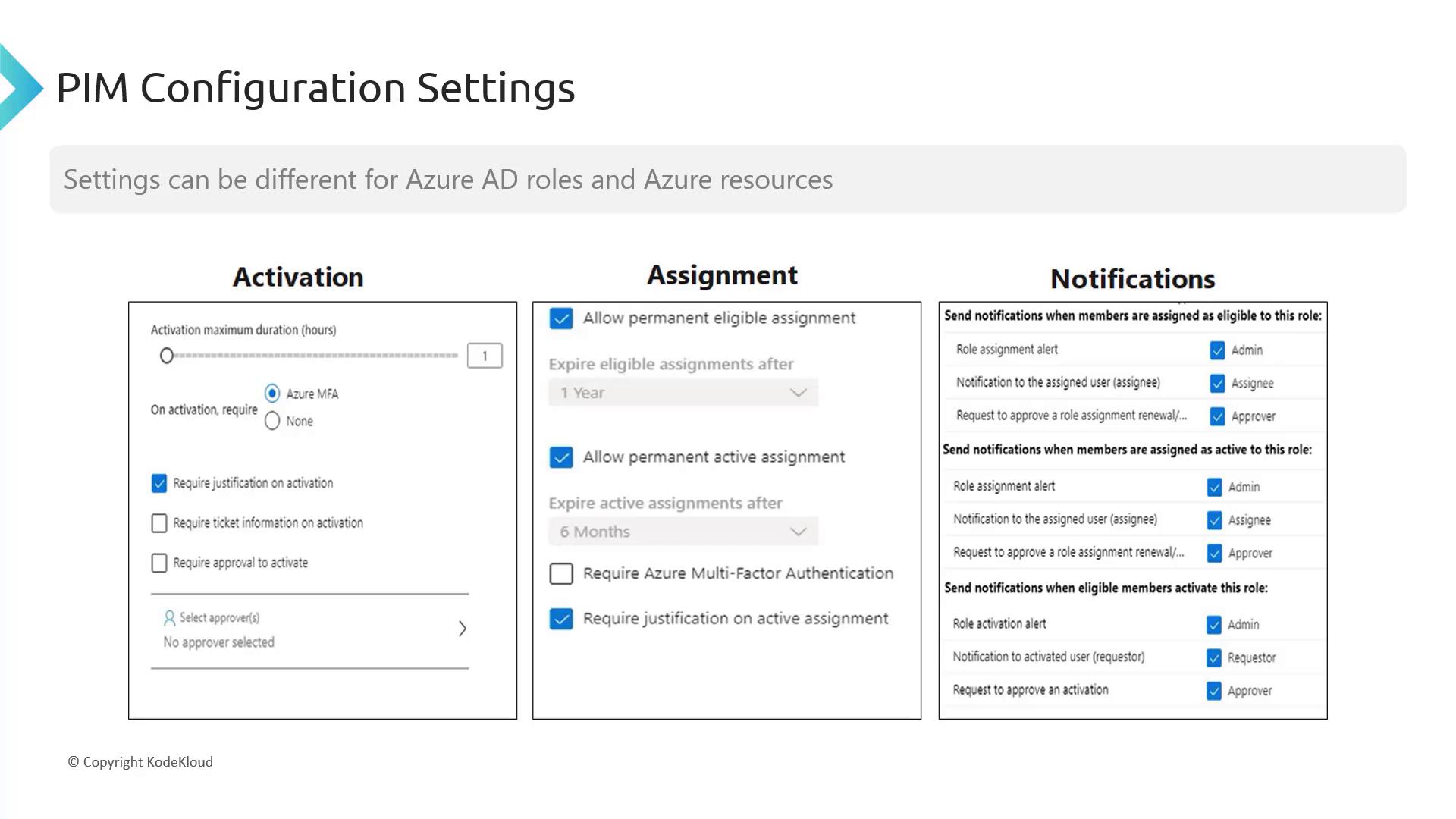
Overview of Configuration Options
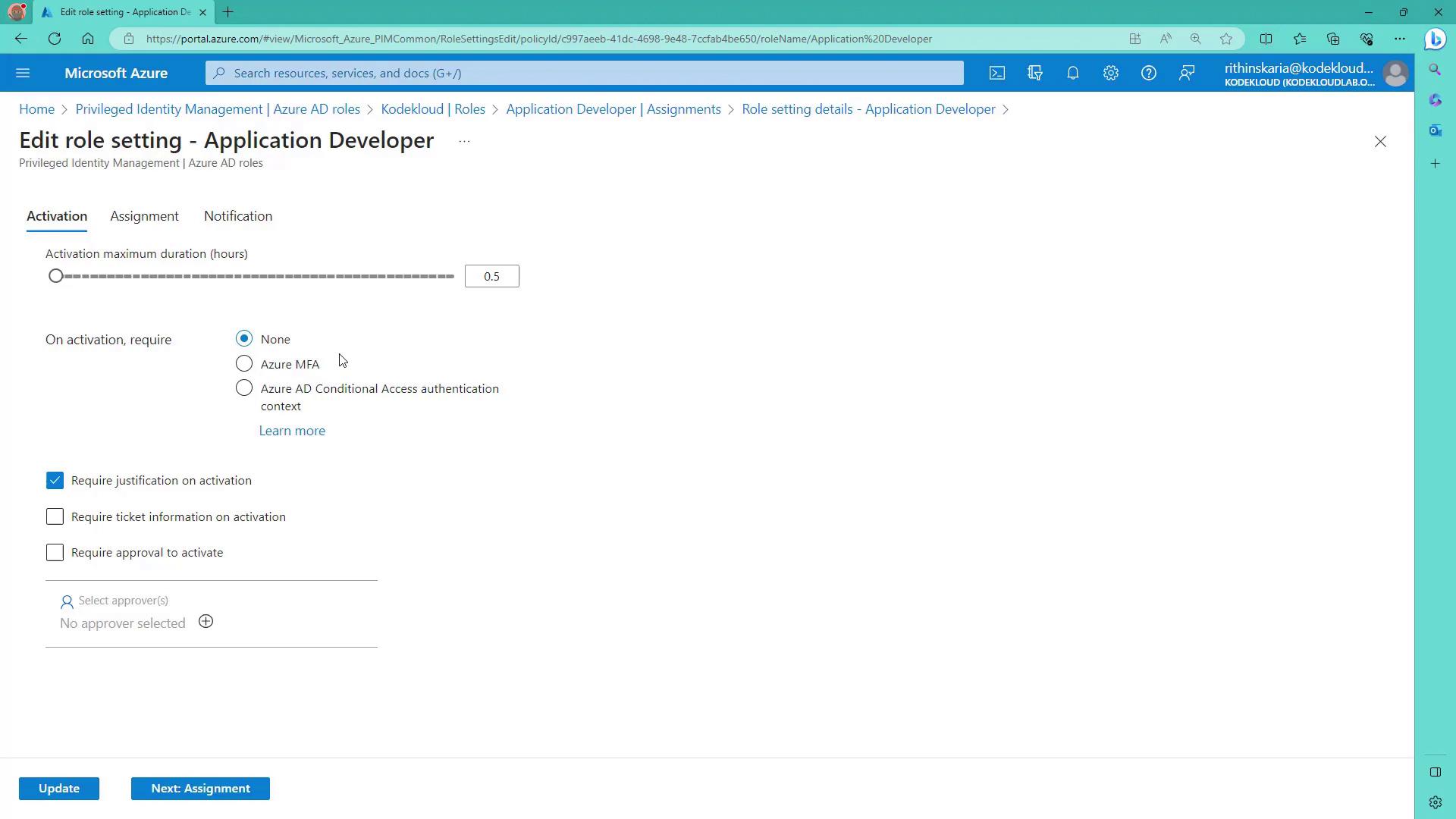
PIM configuration settings are scoped by type. Azure AD roles and Azure resources each have specific settings. Here are some key configuration options:- Activation Settings: Define a maximum duration (e.g., two or three hours) for which a user can maintain access after activation. Once this duration expires, reactivation is required.
- Security Enhancements: Enforce Azure MFA during activation, require justification, or mandate ticket information from internal systems for auditing purposes.
- Approval Process: Configure approvers (such as global administrators) to validate role activations. If approvals aren’t needed, activations are processed automatically.
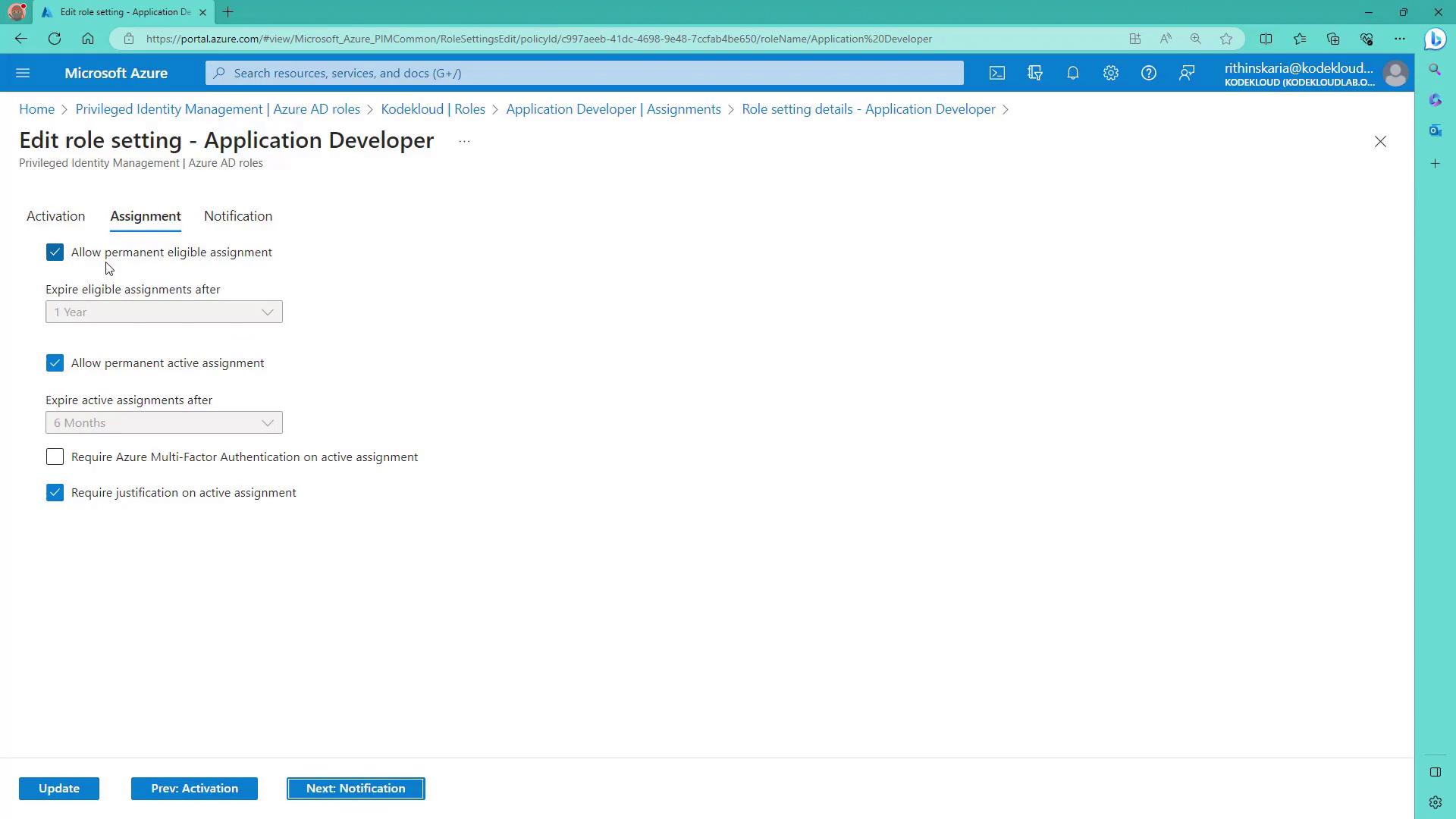
- Allow permanent eligible or active assignments.
- Require MFA during assignment.
- Demand justification for active assignments.
- Set up comprehensive notifications for role assignments and activation events.
Configuring PIM in the Azure Portal
Navigate to Azure AD Privileged Identity Management and select Azure AD Roles. You will find options to assign, activate, approve, and audit roles.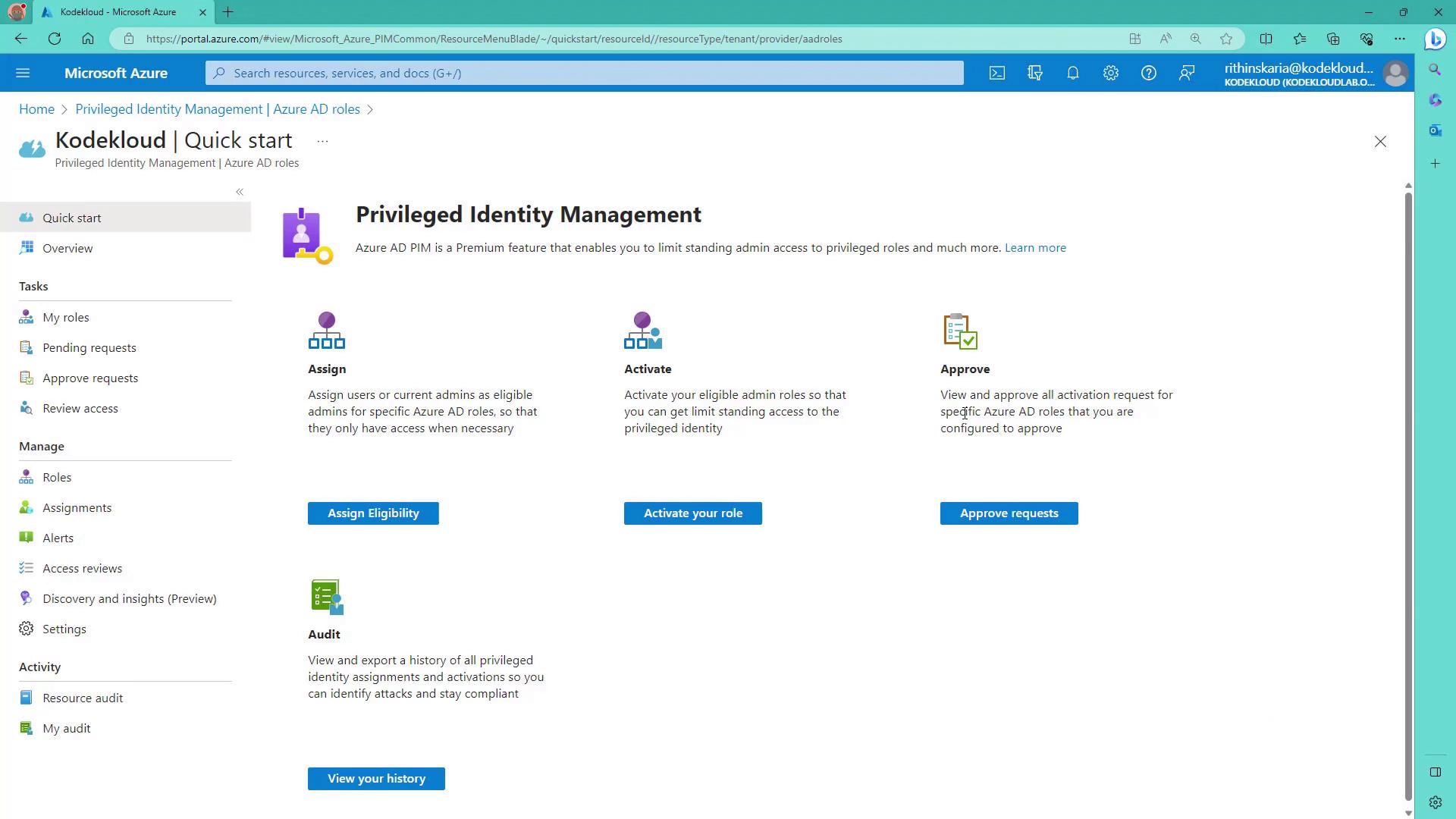
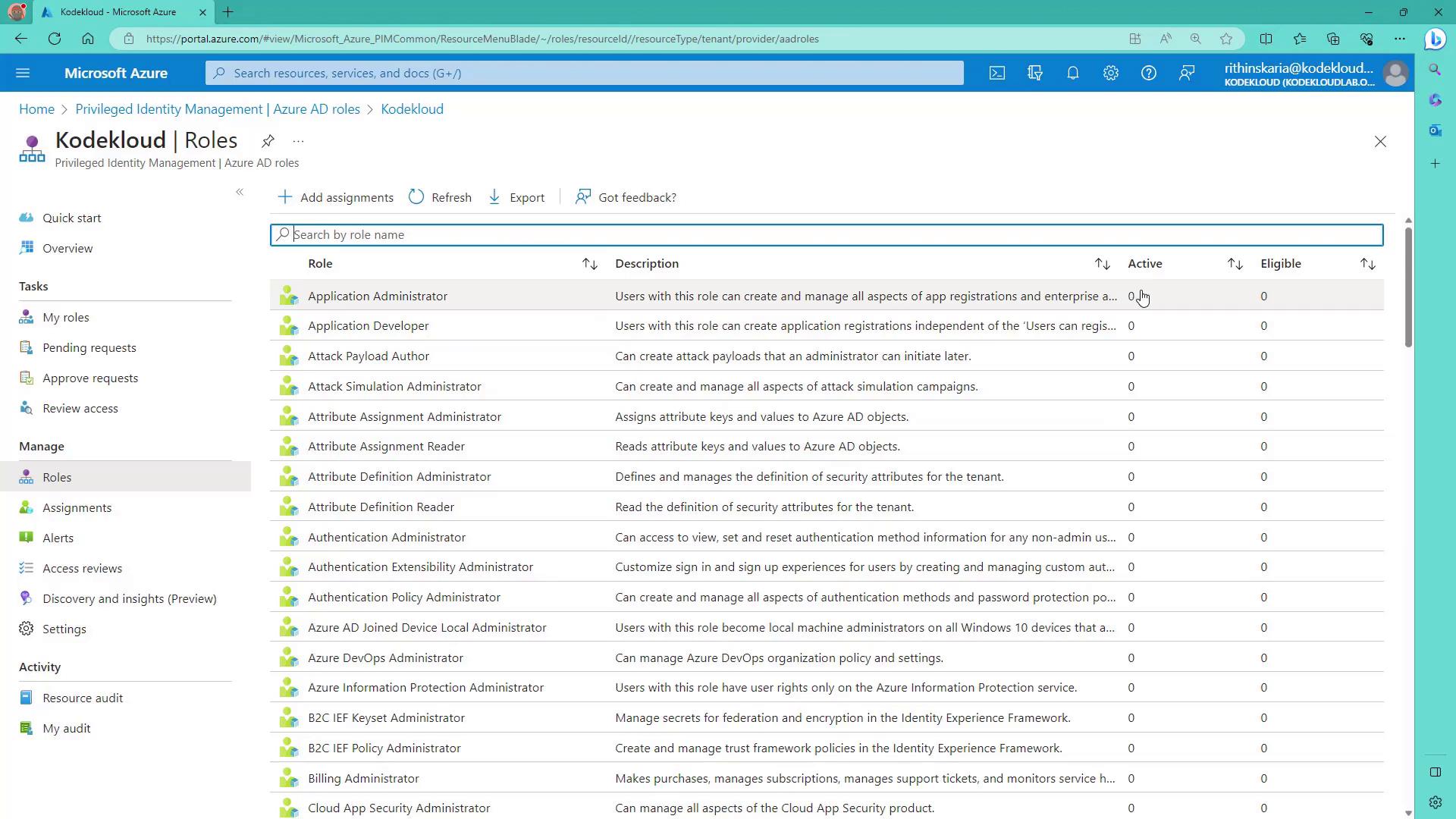
Customizing Role Settings
For example, to configure the “Application Developer” role, click on the settings at the top of the screen to review the predefined configuration options. You can adjust parameters such as:- Maximum activation duration
- Requirement for Azure MFA
- Necessity of additional information (e.g., justification or ticket details)
- Option for role activation approvals
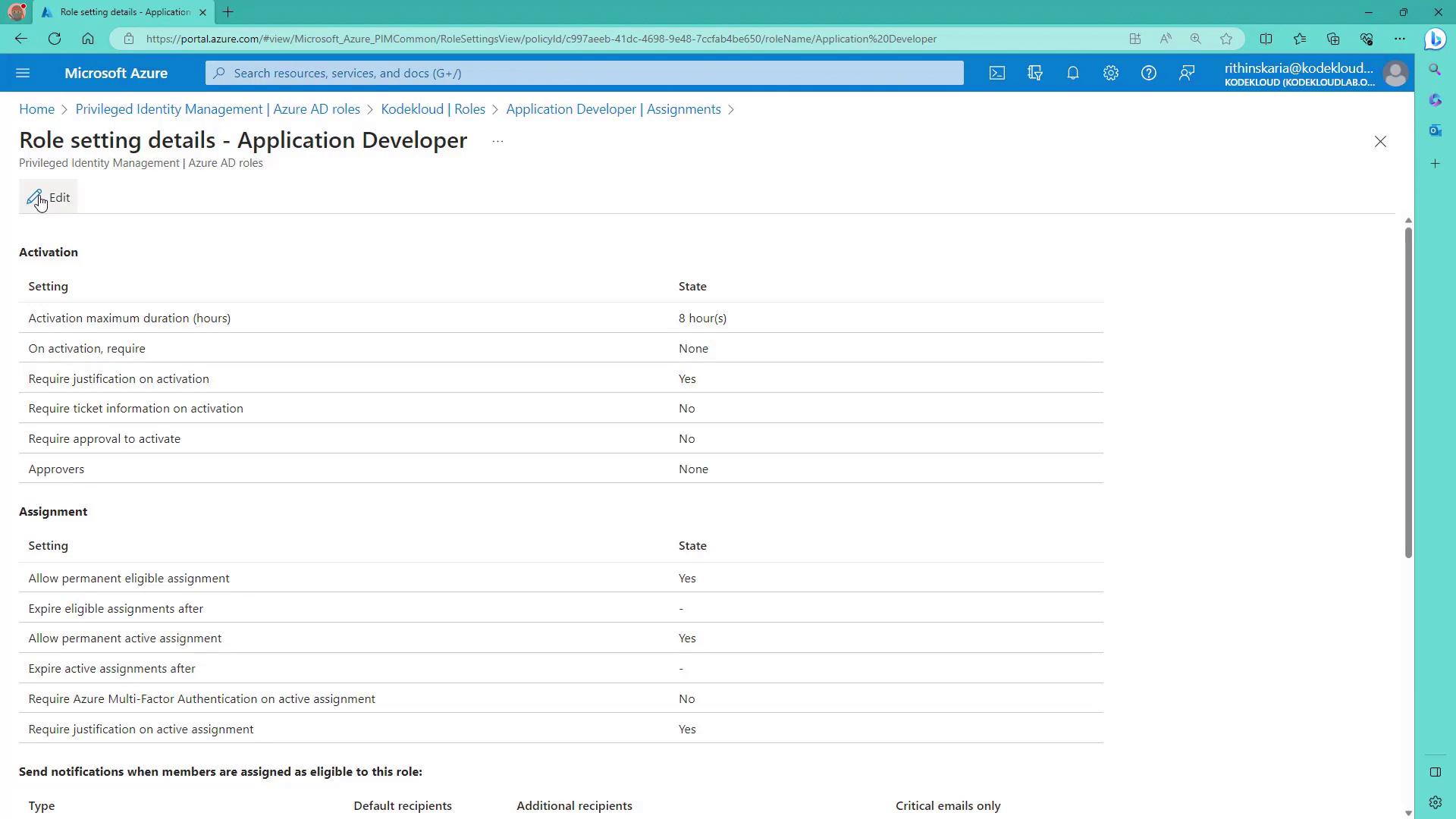
- Allowing permanent or active assignments.
- Requiring MFA upon assignment.
- Enforcing justification for active assignments.
- Customizing notification settings for assignment and activation events.
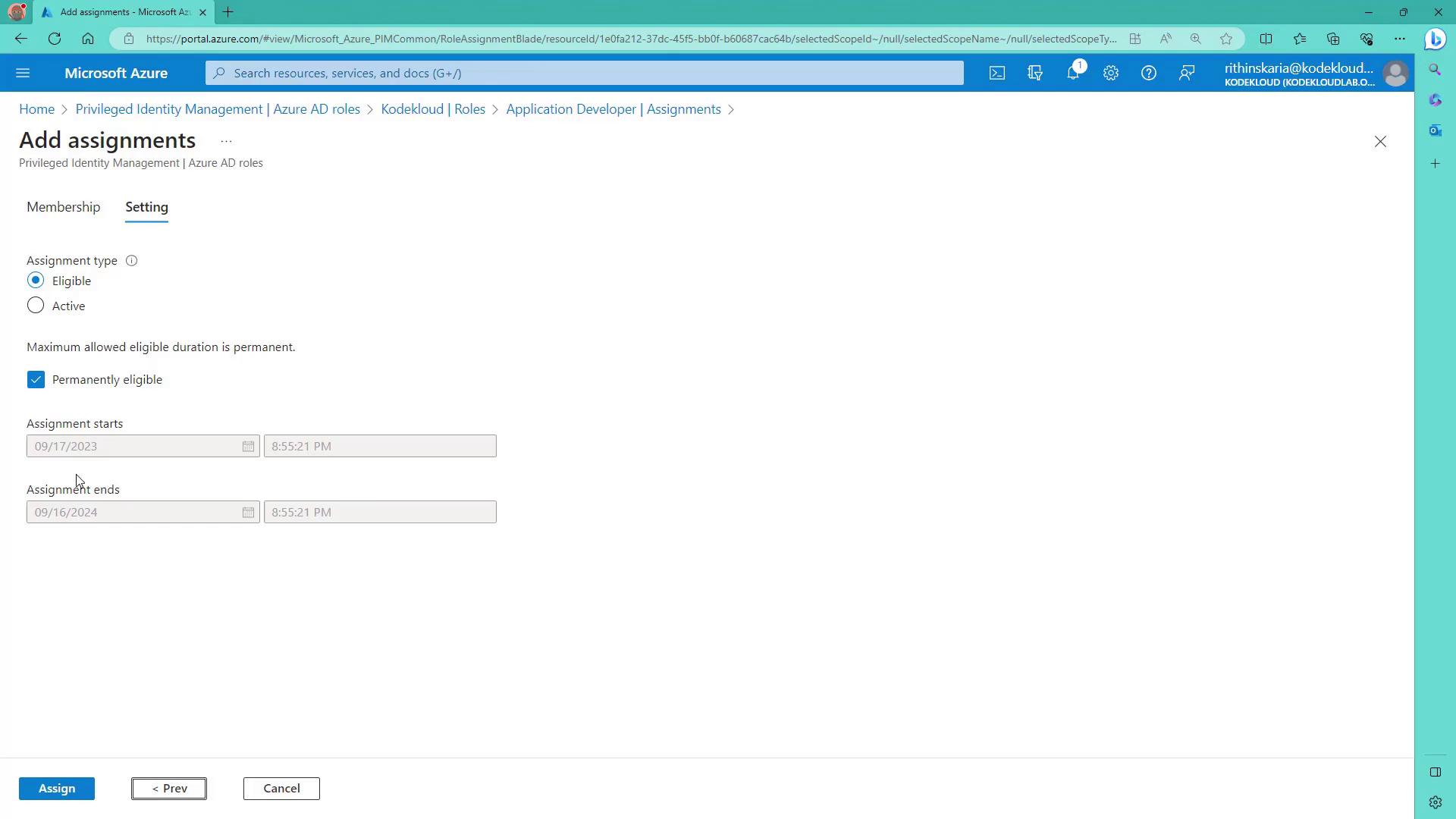
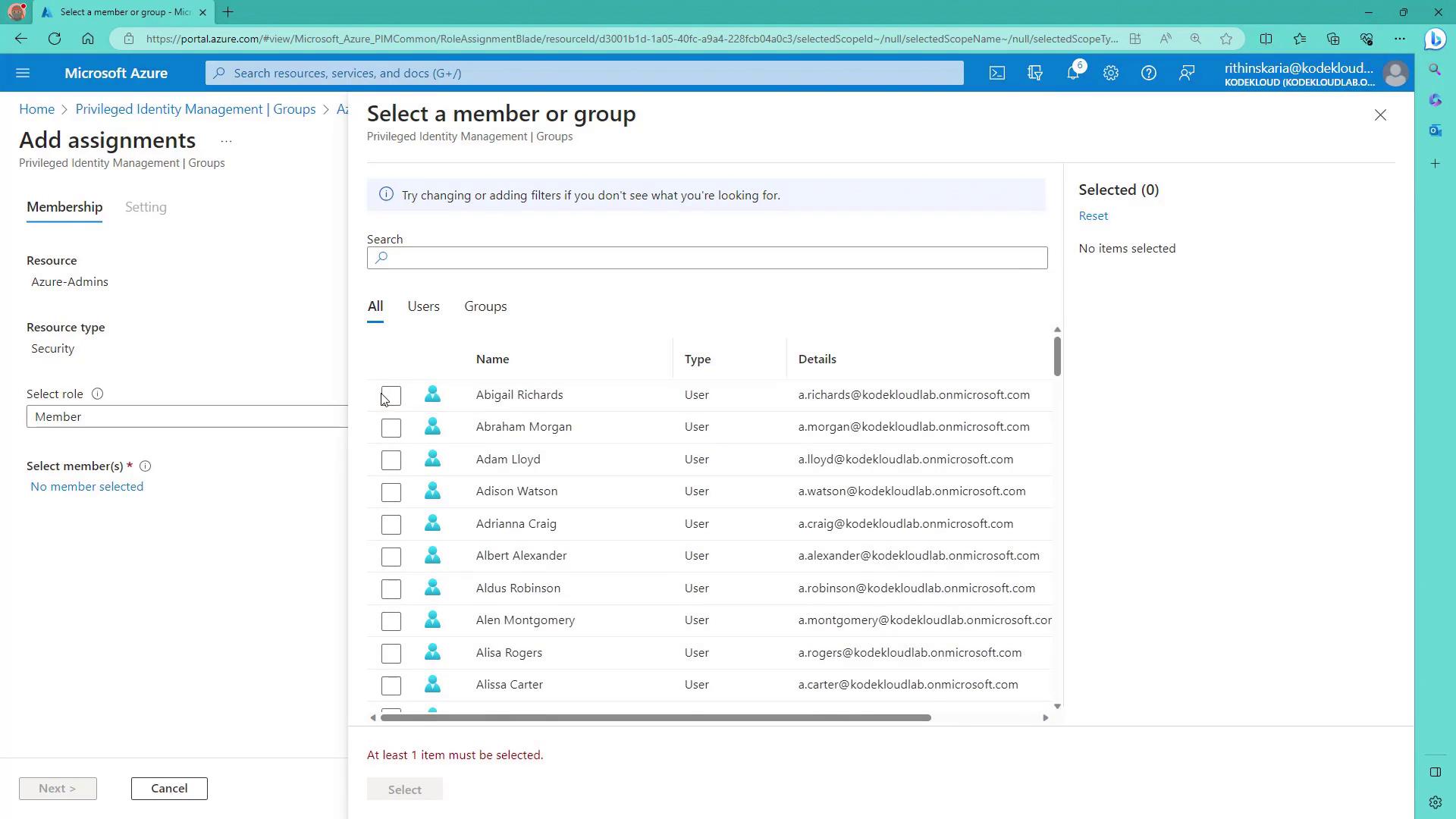
Assigning a Role
To assign a role, click on Add Assignment. The process resembles previous assignment steps but includes options for:- Defining the maximum activation duration
- Requiring justification
- Setting up the approval process
- Select the appropriate member.
- Choose the eligibility type (e.g., permanently eligible).
- Adjust the duration if desired (the default might be one year).
- Click Assign.
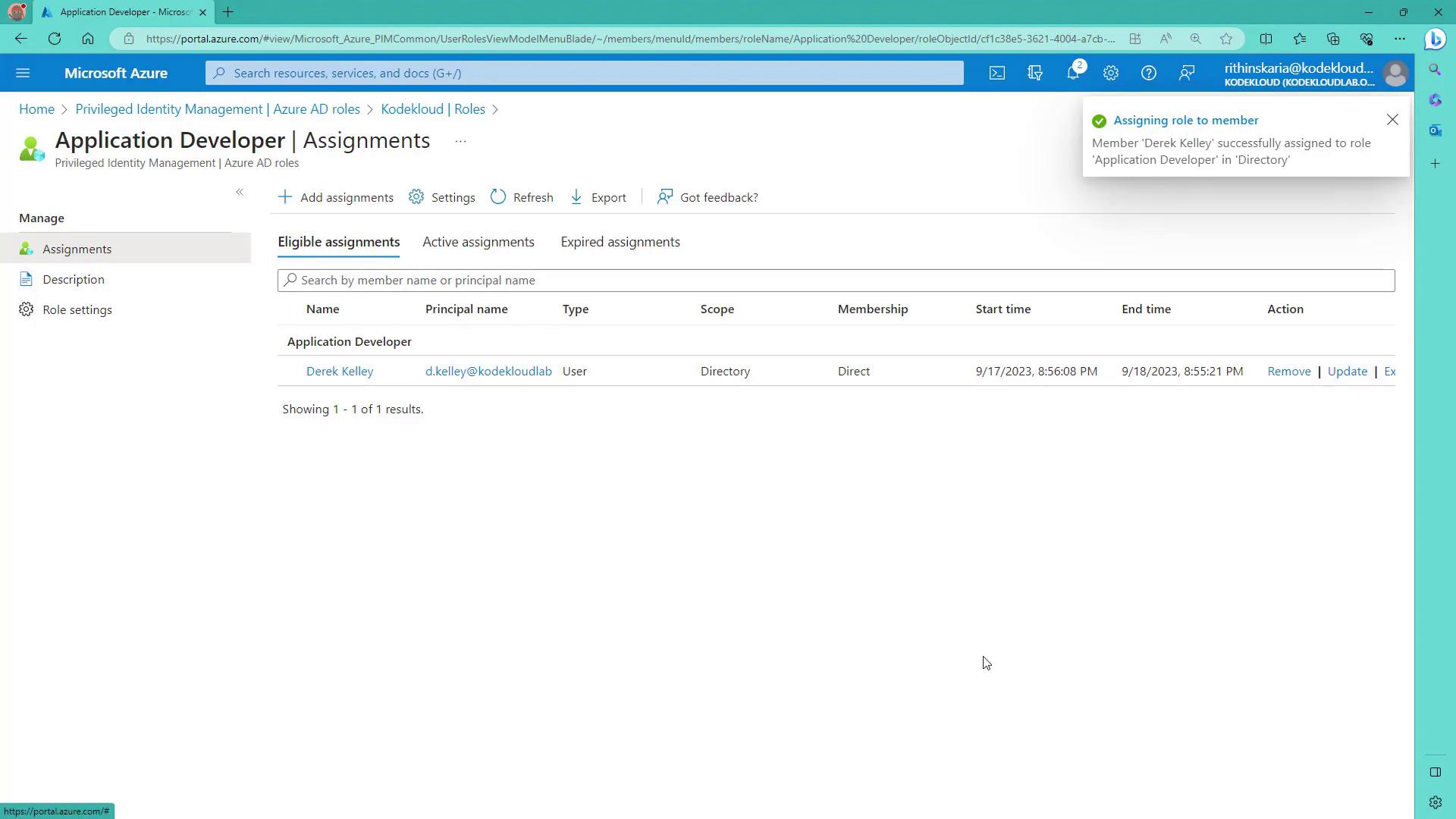
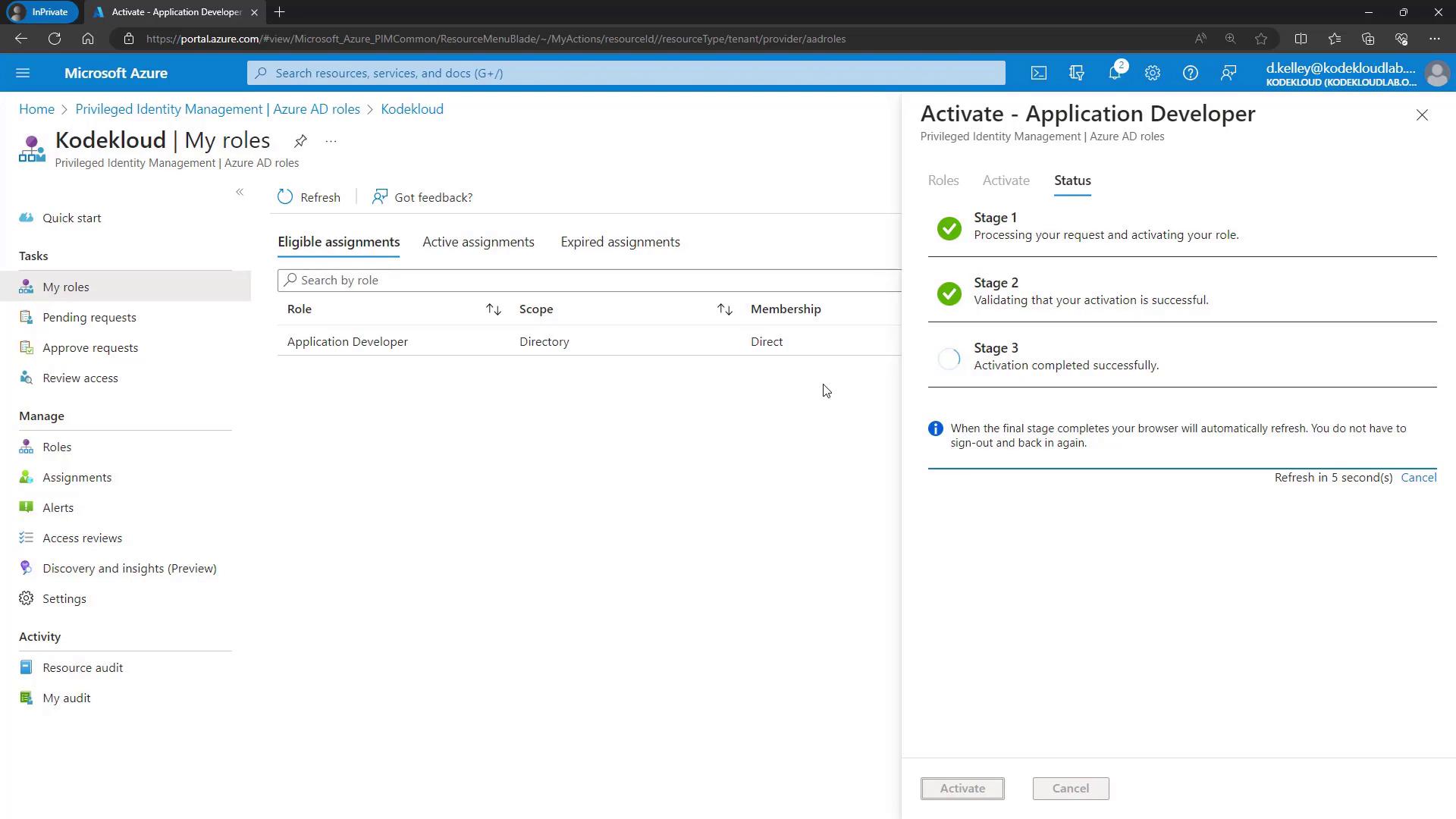
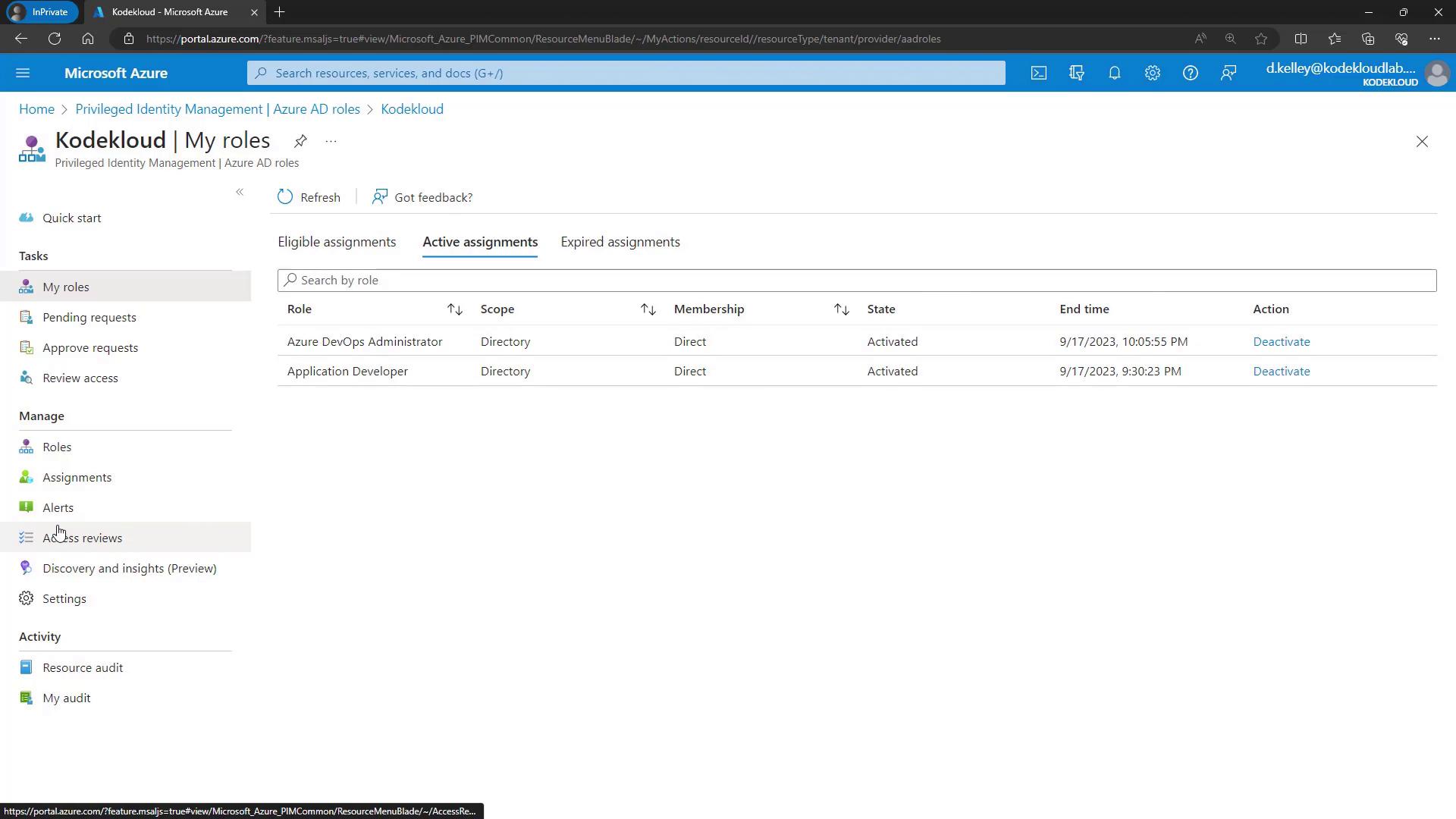
Activating the Role
Next, let’s examine the activation process from the end-user standpoint. When Derek logs into the Azure portal, his role is inactive by default. To activate his “Application Developer” role:- Go to Privileged Identity Management → Azure AD Roles.
- Select Activate.
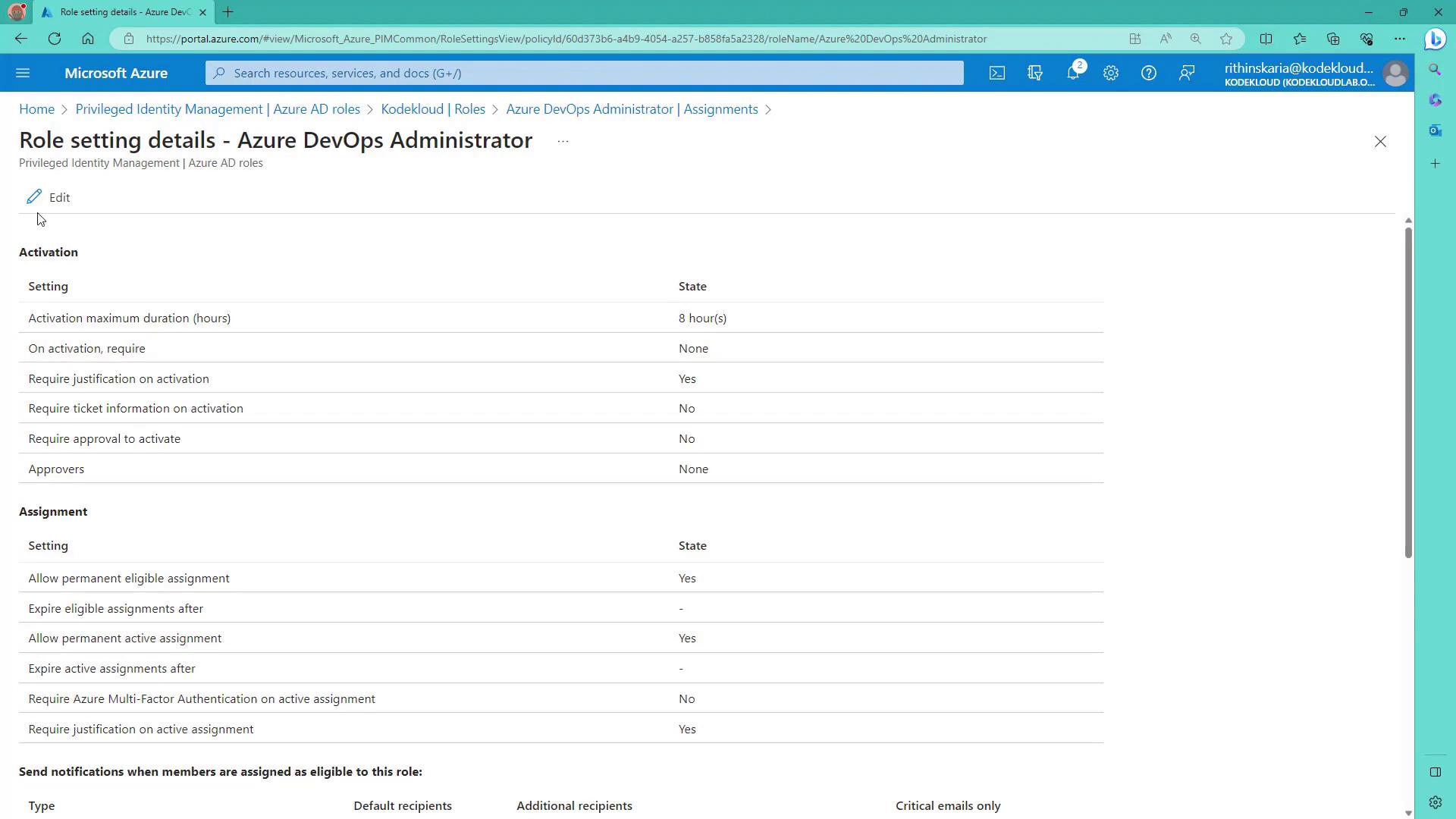
Configuring the Azure DevOps Administrator Role
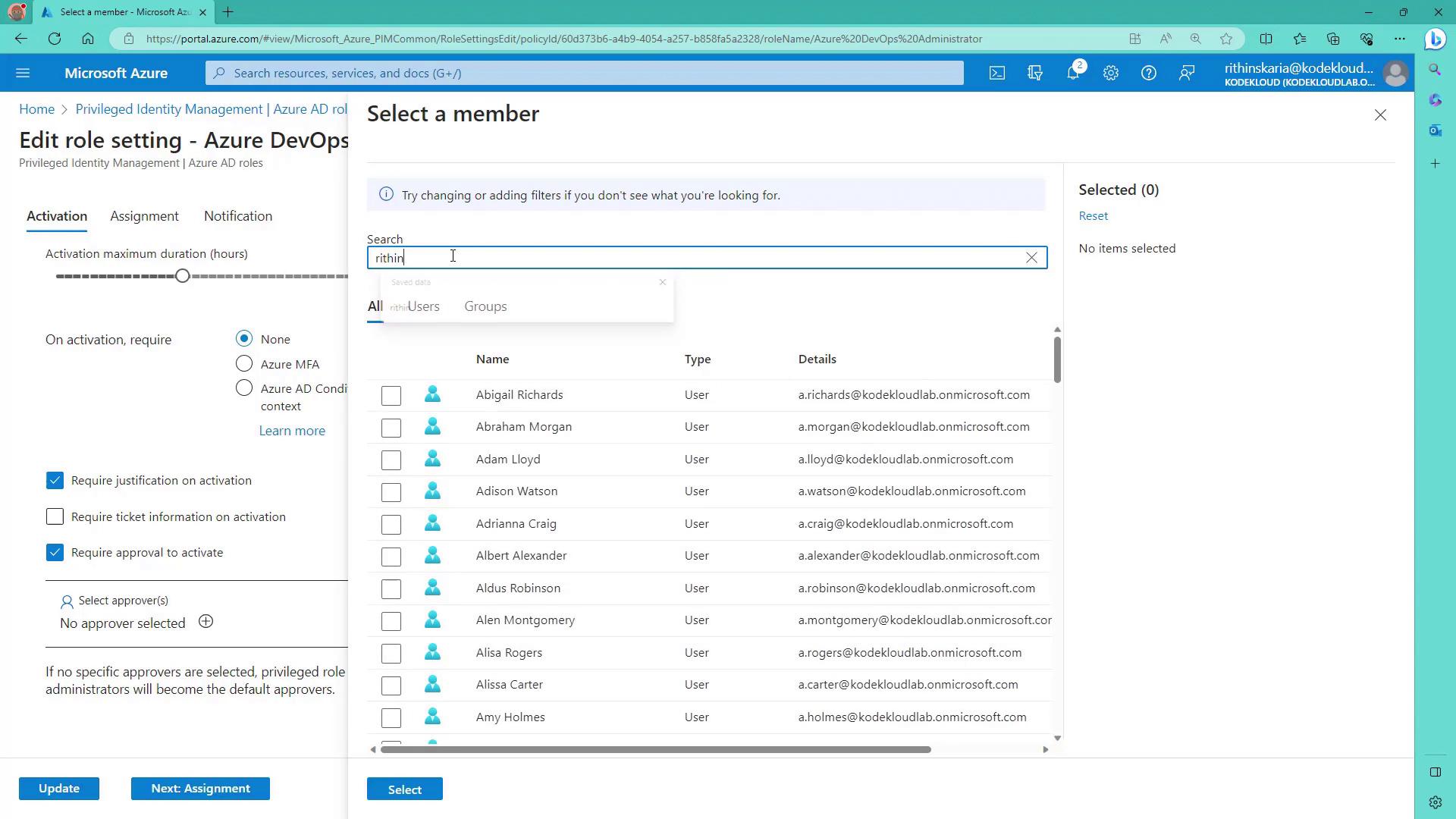
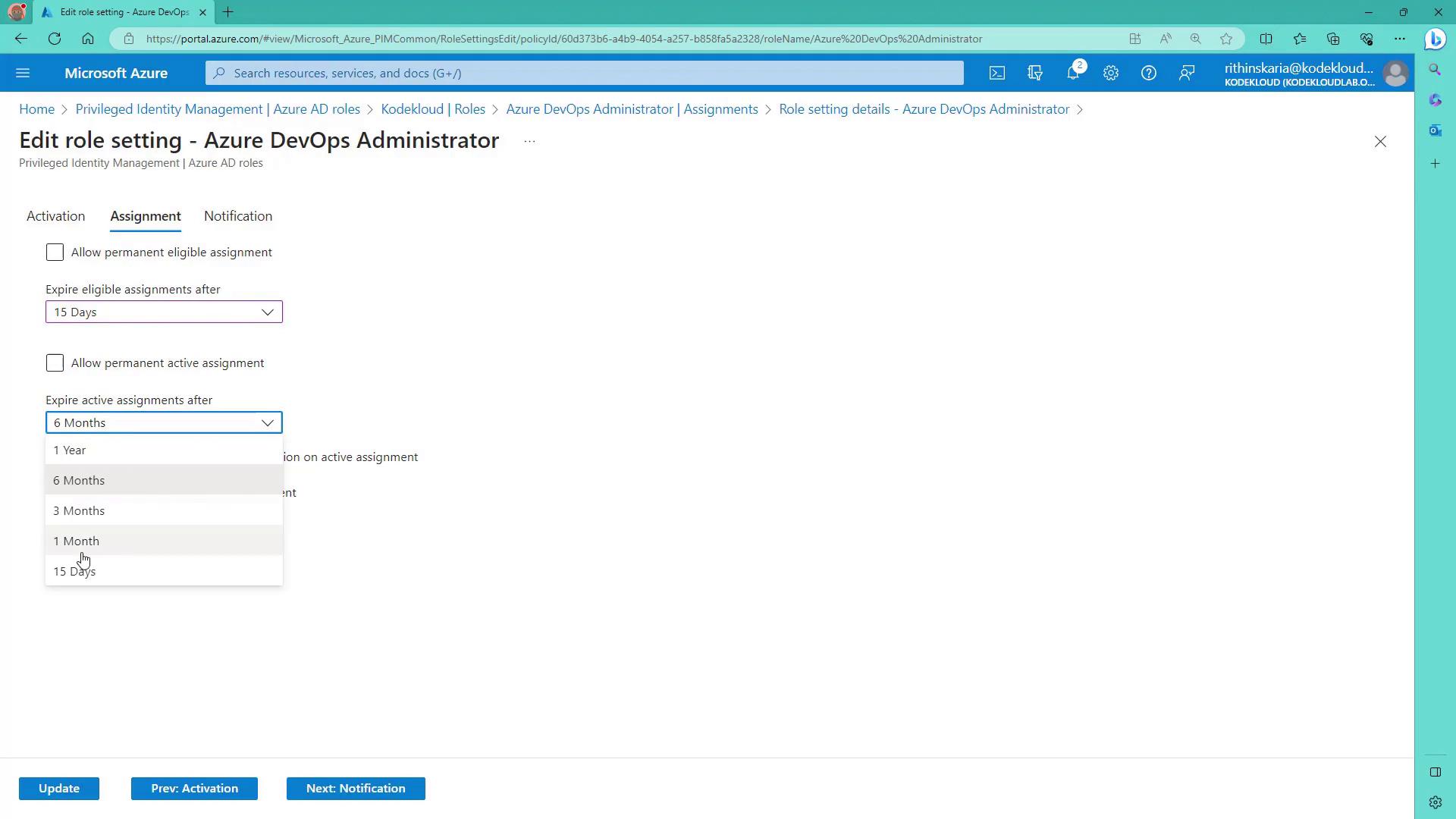
Now, let’s examine the configuration process for the Azure DevOps Administrator role. In the Azure portal under Privileged Identity Management → Azure AD Roles:- Select the Azure DevOps Administrator role.
- Modify settings to include an approval step.
- Set the maximum activation duration to two hours.
- For assignments, specify a maximum duration of 15 days.
Managing PIM for Groups
PIM also supports roles for groups, which is especially useful when multiple users require the same roles. To onboard groups:- Navigate to Privileged Identity Management and select Groups.
- Discover available groups in Azure Active Directory.
- Click Discover Groups.
- Select the appropriate group.
- Once onboarded, assign eligible or active assignments through PIM to streamline role management for multiple users.
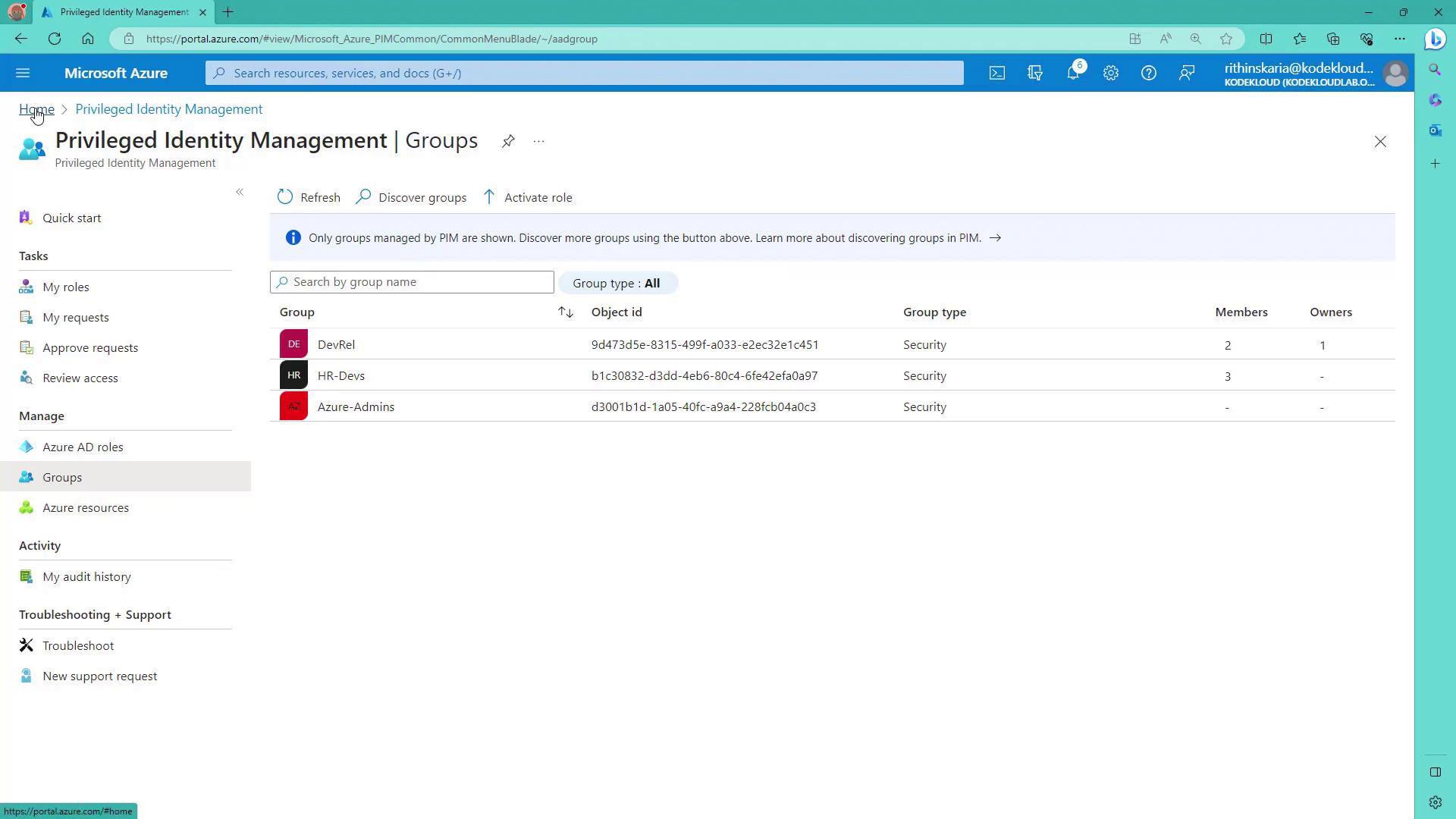
When creating groups in Azure AD for role assignments, ensure the flag for role assignment is set to “Yes” during creation. If this setting is not enabled initially, you will need to recreate the group for PIM compatibility.