This article explains how to enable Azure Resource Locks—a powerful yet often underutilized Azure security feature—to protect your critical resources from accidental modifications or deletions. Resource locks are essential for maintaining the stability of production environments, and they can be configured to meet your specific requirements.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Azure resource locks serve as a safeguard against unintended changes. For example, if a production database is mistakenly modified or removed, a resource lock will restrict such actions and enhance the security and resilience of your environment.Understanding Inheritance in Azure Locks
Similar to Azure RBAC, resource locks provide flexible deployment options. They can be applied at various scopes:- Subscription
- Resource Group
- Individual Resource
Types of Resource Locks
There are two primary types of Azure resource locks, each serving a specific purpose:-
Read-only Lock
A read-only lock permits you to view the resource details but prevents any modifications. This lock is ideal for configurations that should remain unchanged. For instance, a Network Security Group meeting organizational compliance can be safeguarded against modifications by applying a read-only lock. -
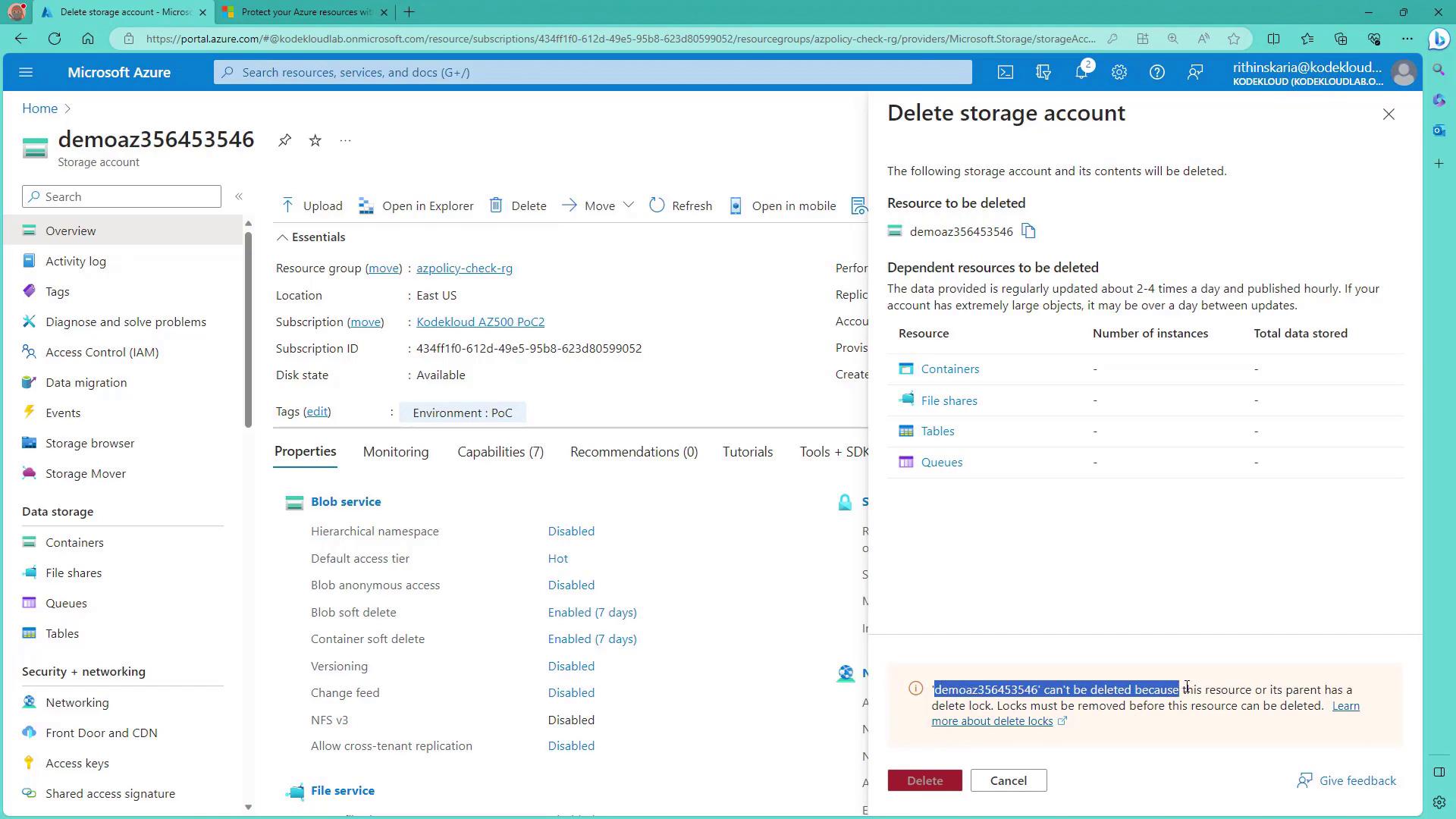
Delete Lock
A delete lock allows modifications but prevents the resource from being deleted. This is particularly useful for resources that require frequent updates, such as virtual machines running critical applications, but must never be accidentally deleted.
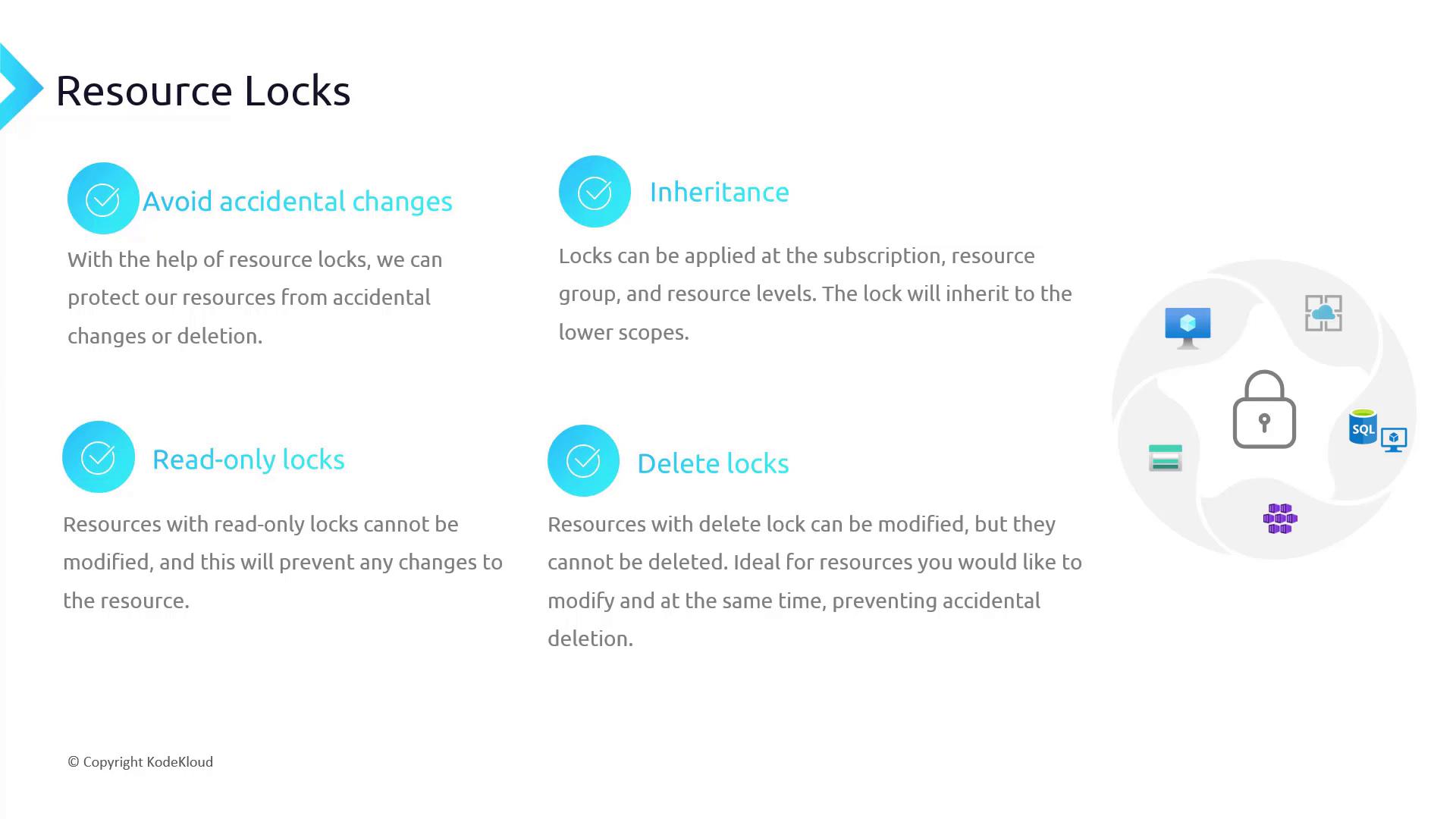
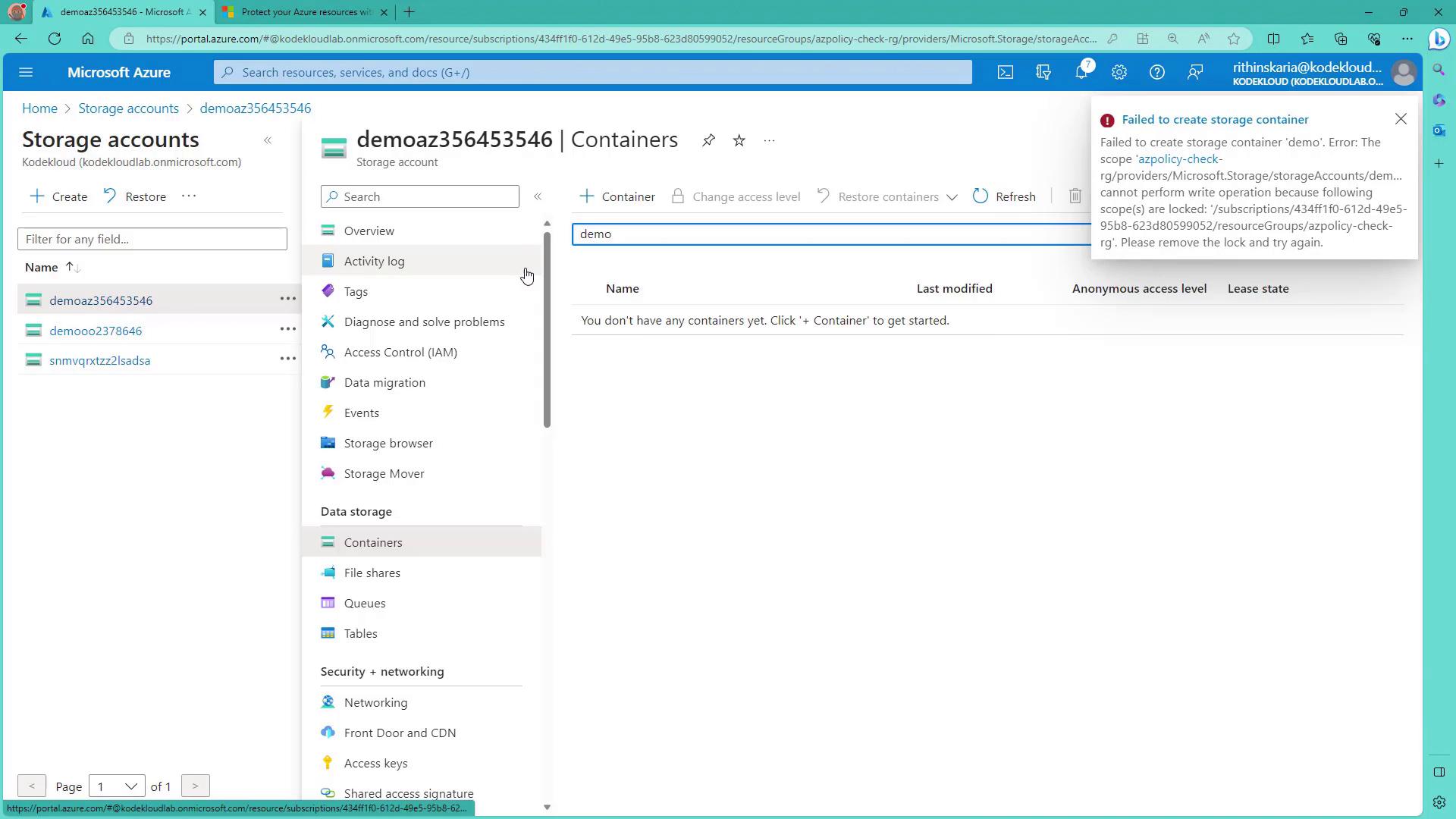
When using resource locks on shared environments, always review possible limitations. For instance, a read-only lock on a storage account prevents the creation of a blob container, and a read-only lock on app servers may interfere with file interactions in Visual Studio Server Explorer.
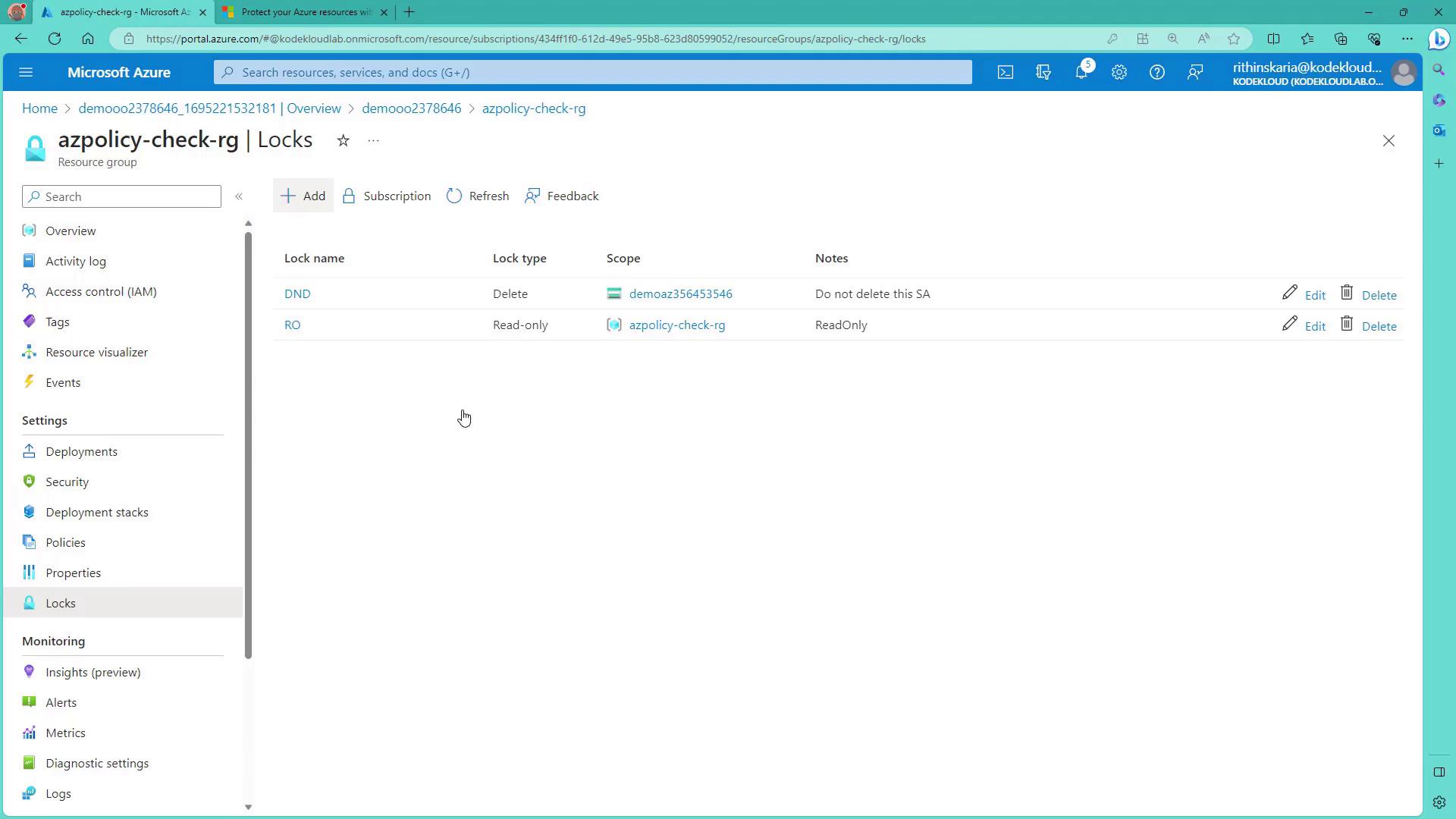
Configuring Azure Resource Locks
Azure resource locks are configured directly from the Azure portal. To add a lock, navigate to the desired resource and click on “Add Lock”. Below is an example of creating a delete lock named “dnd” (do not delete) on a storage account.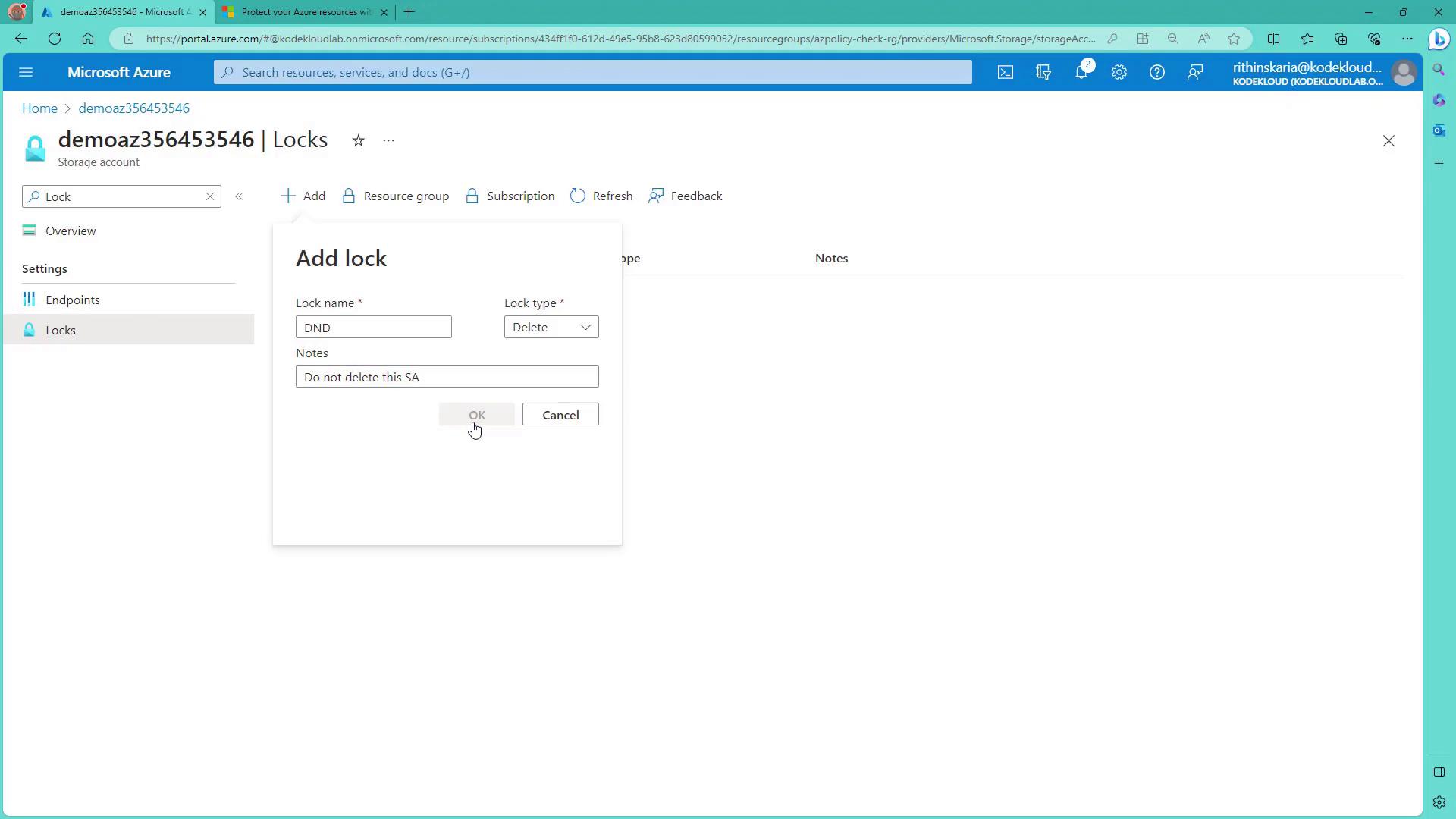
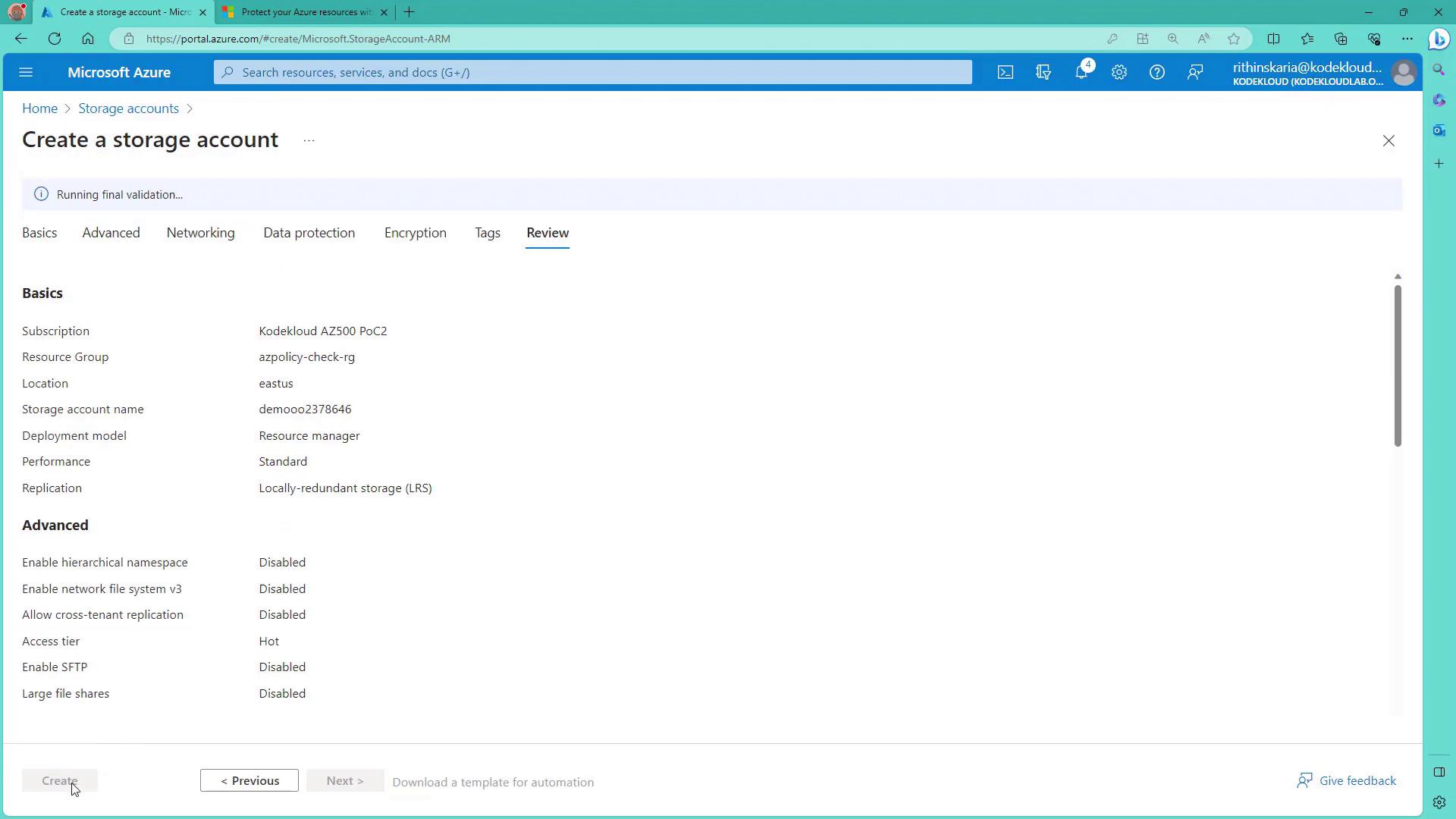
Demonstration: Creating and Locking a Storage Account
Before applying locks at the resource group level, you can create a new storage account. Use the following Azure CLI command to check policies and ensure the storage account name is unique: