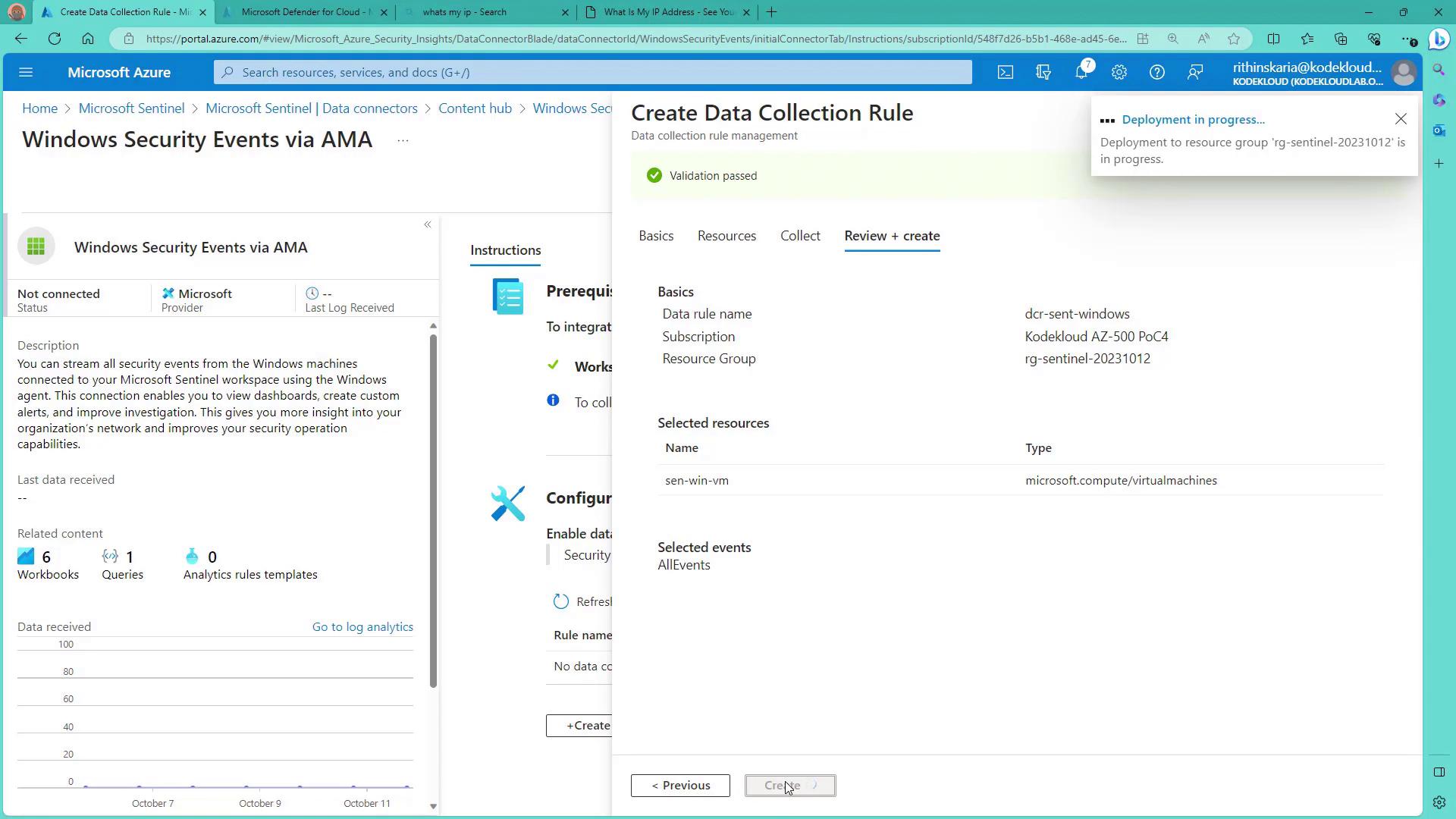
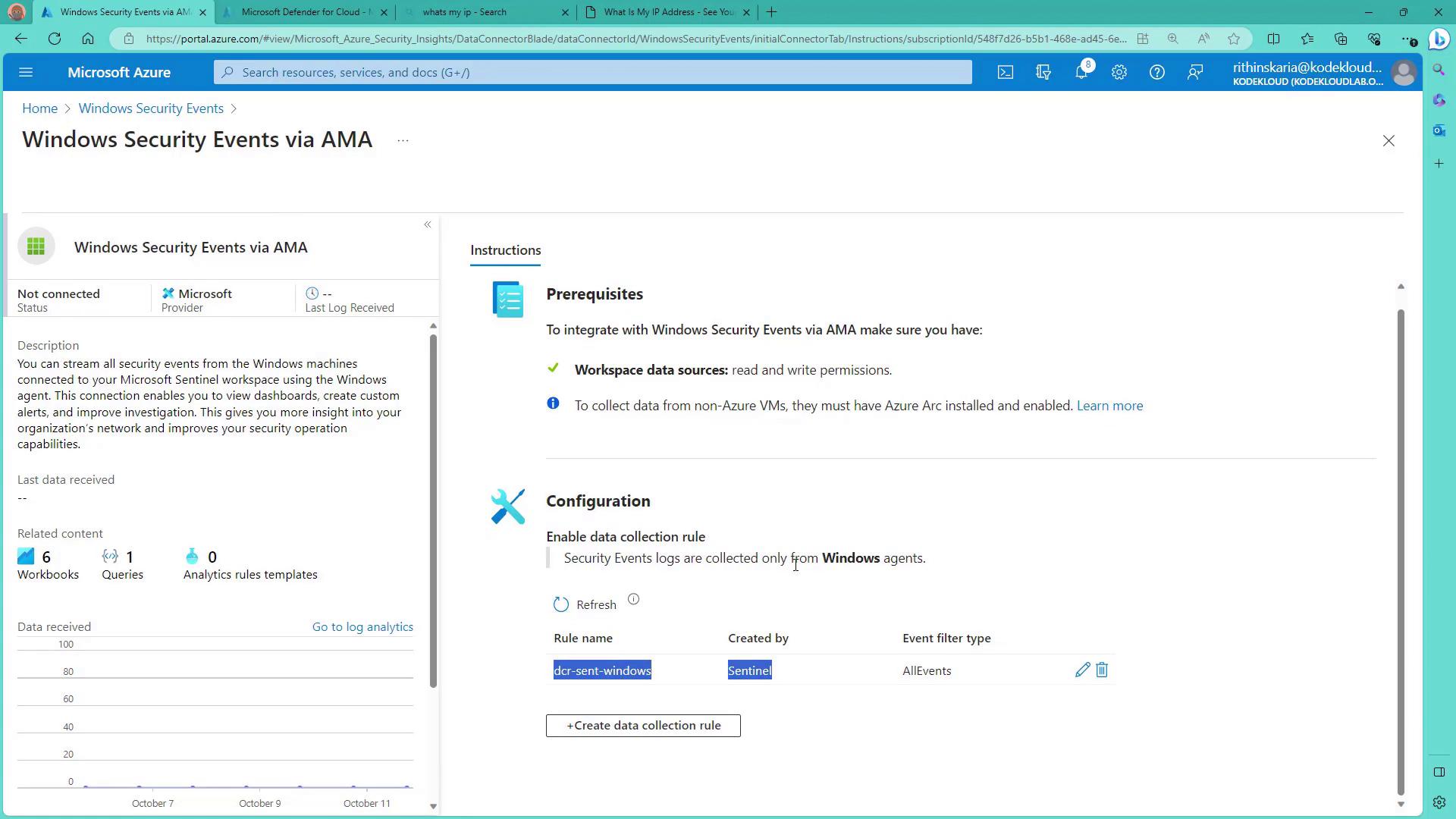
Configure data connections to Microsoft Sentinel by setting up connectors that serve as secure bridges between Sentinel and various data sources. These connectors enable Sentinel to receive logs and data from Microsoft solutions, third-party services, cloud providers, or on-premises infrastructure. In doing so, Sentinel builds a comprehensive security overview by correlating events, detecting anomalies, and responding promptly to potential threats. Setting up connectors is simple and intuitive. With only a few clicks, you can integrate multiple services to ensure that every data source is monitored. For example, the Azure Kubernetes Service (AKS) connector allows you to link AKS with Sentinel, importing all the log data stored in Log Analytics. Some connectors are deployed exclusively through solutions; Microsoft provides a comprehensive catalog, and you can also find community-built connectors on the Microsoft Sentinel GitHub repository if you need additional data integrations. In this guide, you will learn how to onboard Windows and Linux servers to Azure Monitor and analyze their logs using Azure Sentinel. The first step involves enabling the Azure Monitoring Agent (AMA) on your virtual machines by creating a Data Collection Rule (DCR).Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
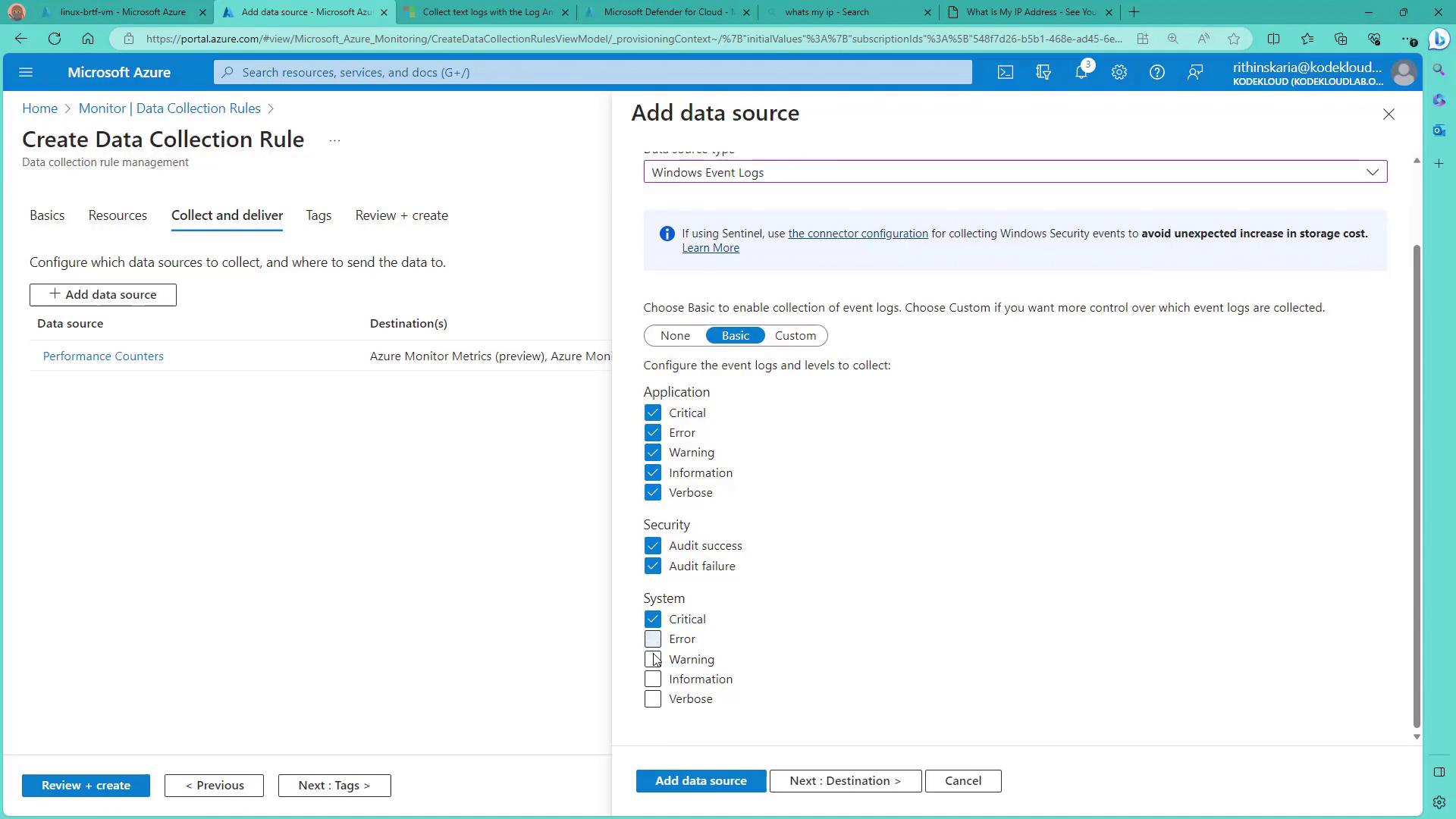
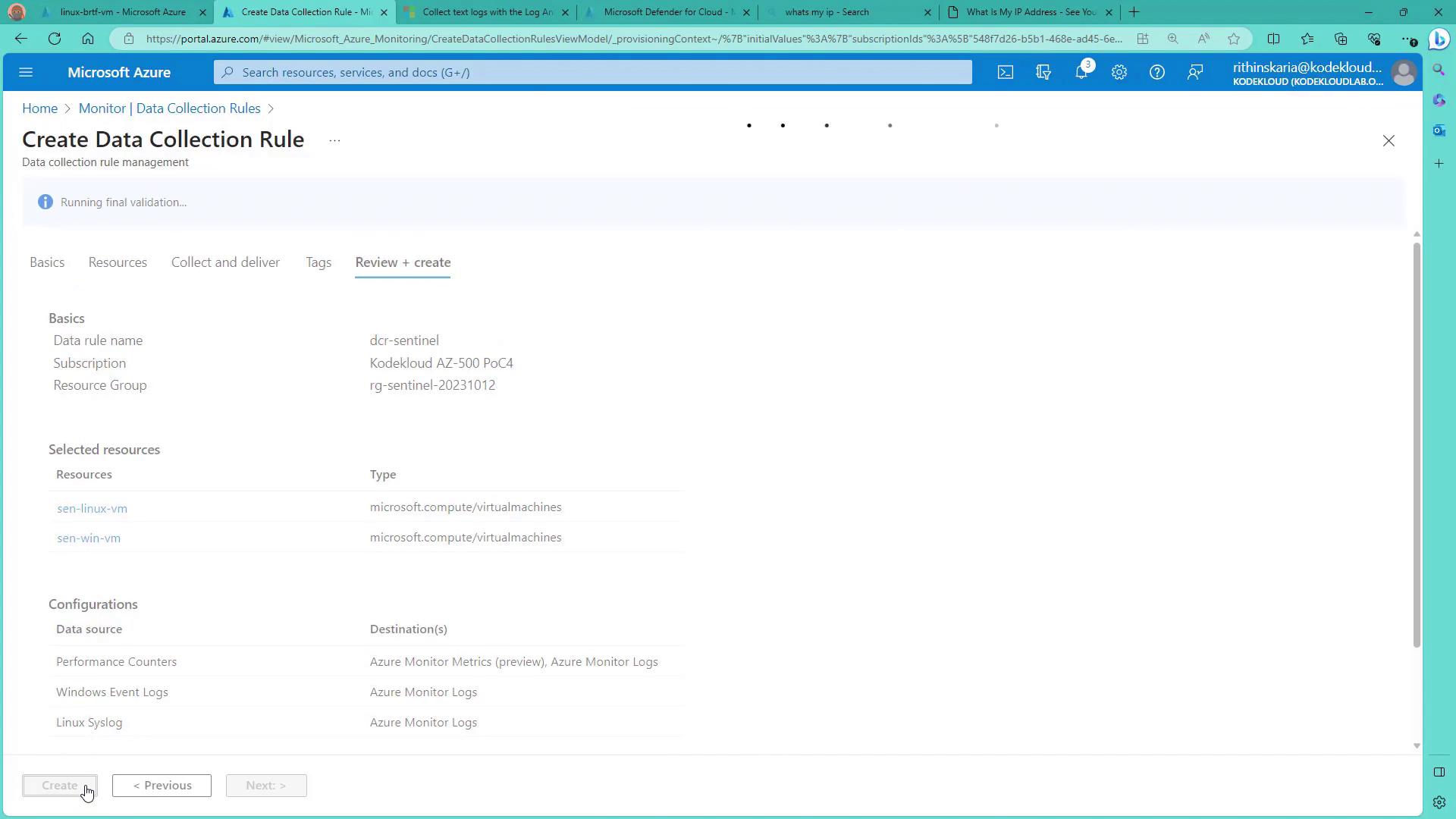
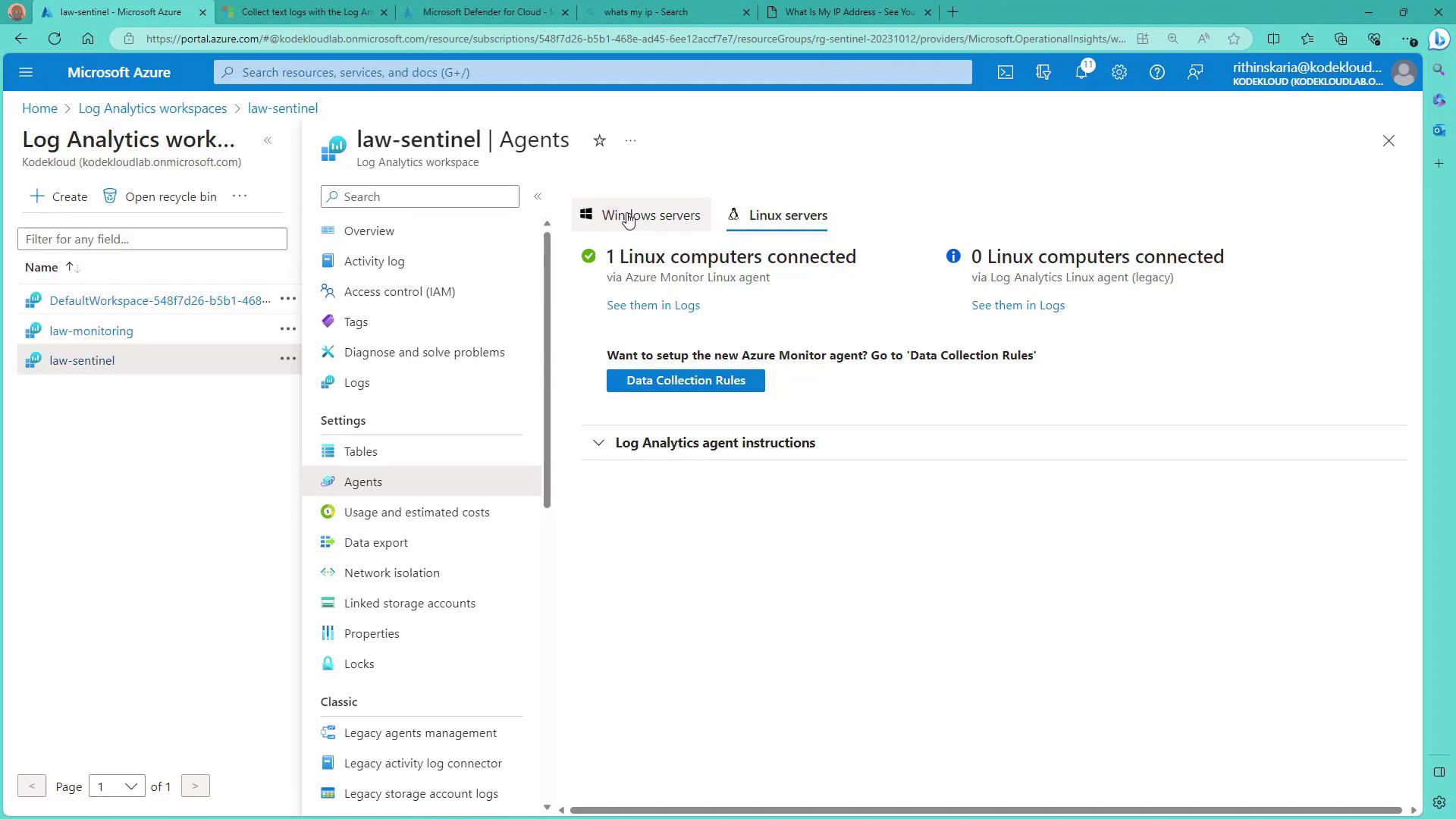
Navigate to the Monitor section to create a Data Collection Rule. Name the rule (e.g., “DCR for Sentinel”) and assign it to the Sentinel resource group. This rule applies to all your servers and requires the creation of a Data Collection Endpoint to handle data collection—especially for Linux machines that do not support direct connectivity using AMA. Although Ubuntu 22.04 does not support MFA, a Data Collection Endpoint can still link it to your Linux service. Under Resources, add both Windows and Linux servers; then, under Collect and Deliver, select all available data sources such as performance counters, application logs, security logs, and system logs. The destination for this collected data is your Sentinel workspace.
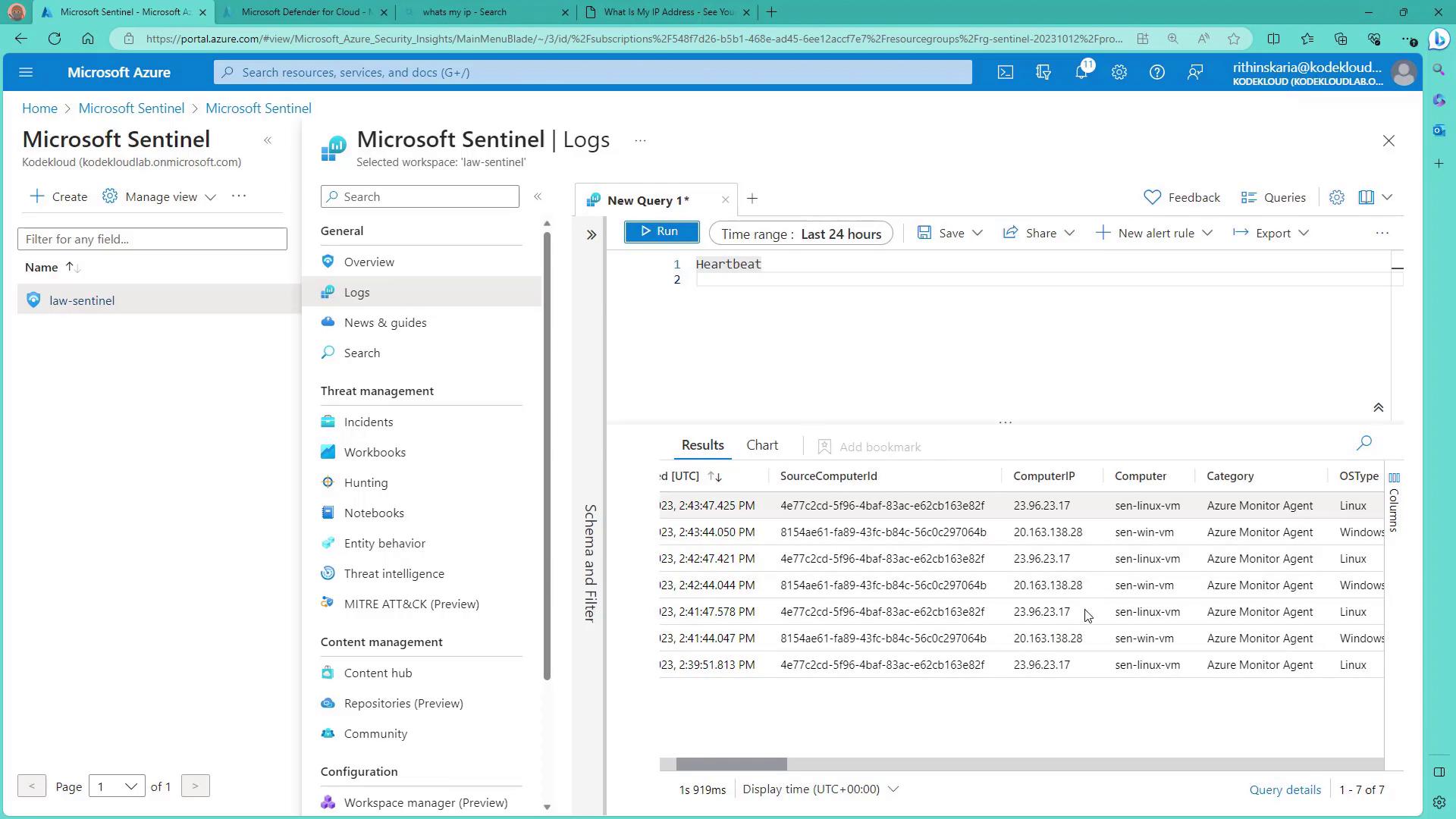
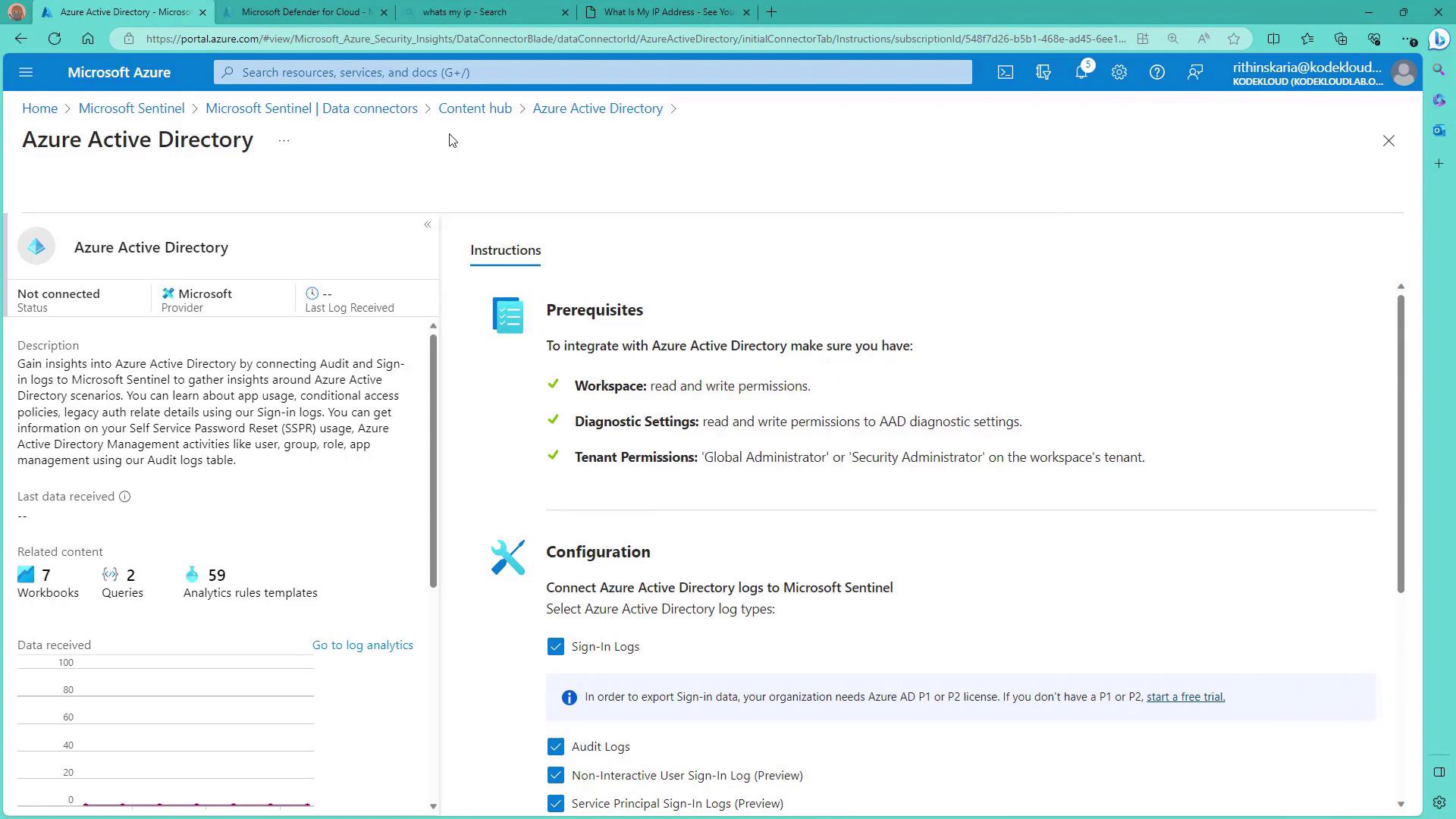
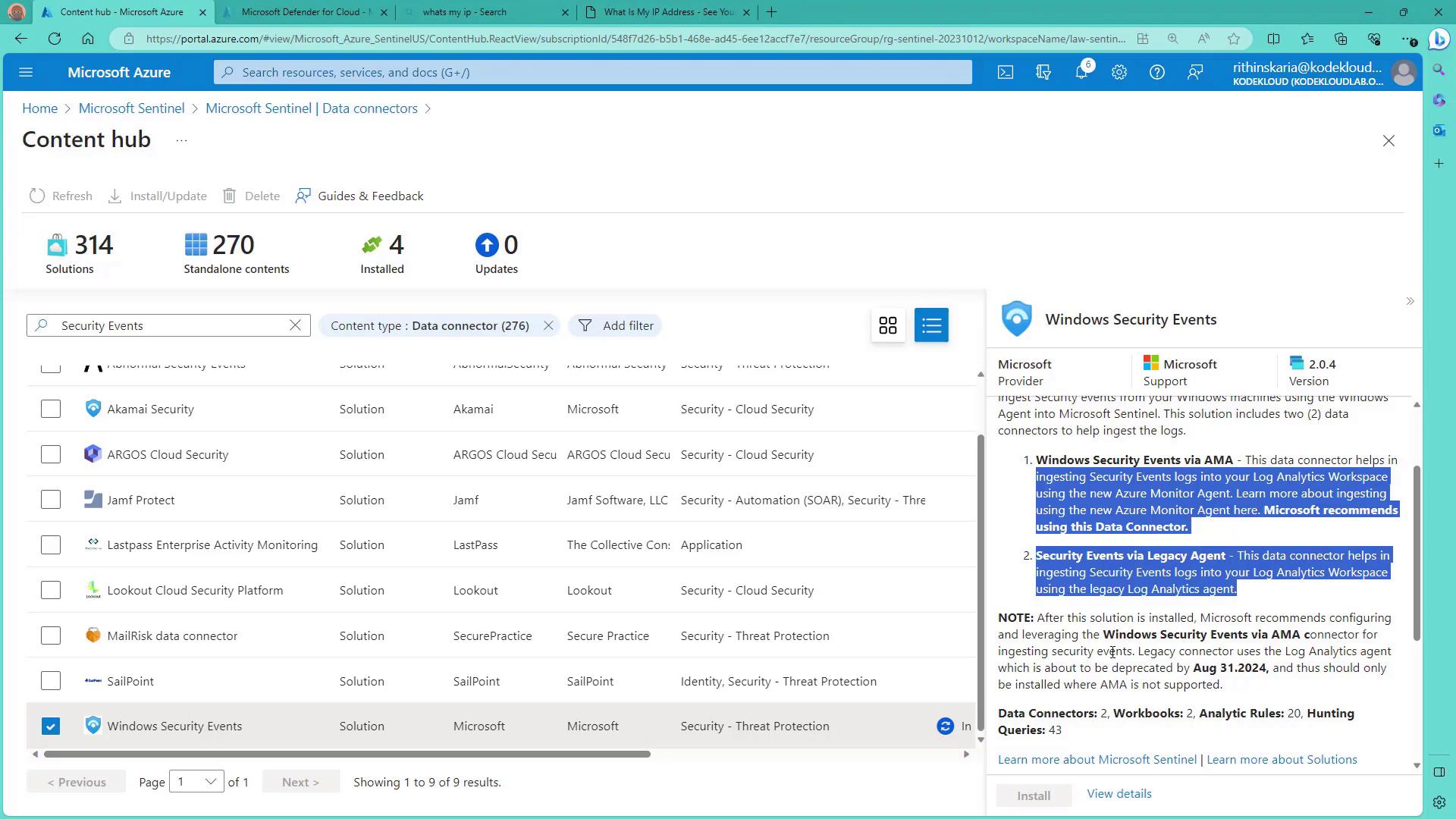
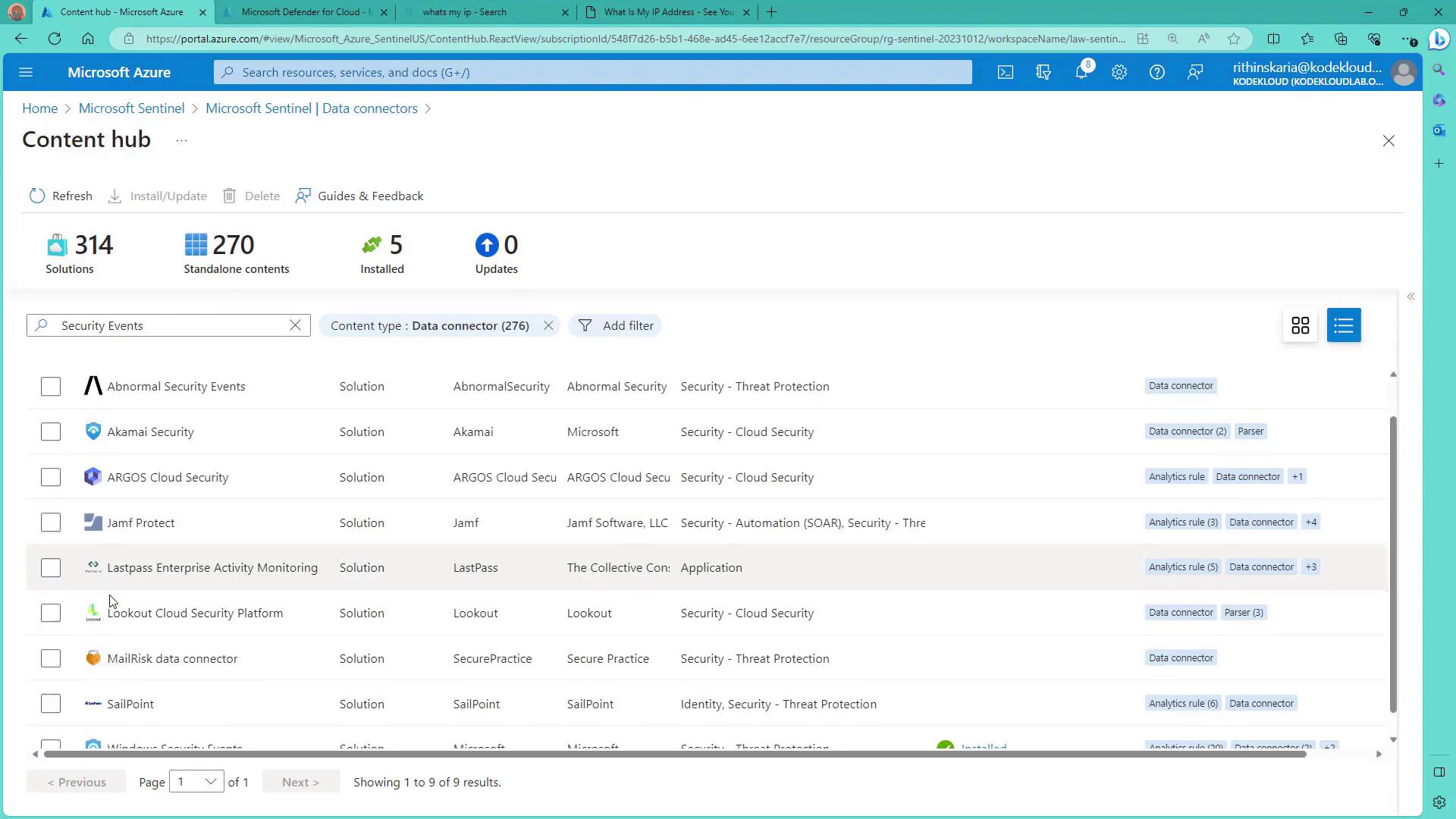
Next, go to the Connectors section in Sentinel to view the available data connectors. Under Featured Data Connectors, you can onboard essential services such as Azure Activity, Azure Active Directory, Microsoft Defender, Defender for Cloud, and various security events. Begin by installing the Azure Active Directory connector, then proceed with Azure Activity and other connectors. Once the installations are complete, your Sentinel instance is ready to process the incoming logs. For the Azure Active Directory connector, navigate to its Manage section. Here, you will see details like “Connect Azure Active Directory logs to Sentinel.” Note that exporting sign-in data may require P1 or P2 licenses. If you do not have a license yet, you can start with a trial to enable the necessary features.
Consider creating custom workbooks to visualize your log data more intuitively. Workbooks can provide enhanced insights compared to raw queries.