This article explains the four primary categories of security controls, how they differ, and where they fit in a layered security program. Two categories are implemented by people, and two are implemented by systems or devices.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Managerial controls (implemented by people)
- Operational controls (implemented by people)
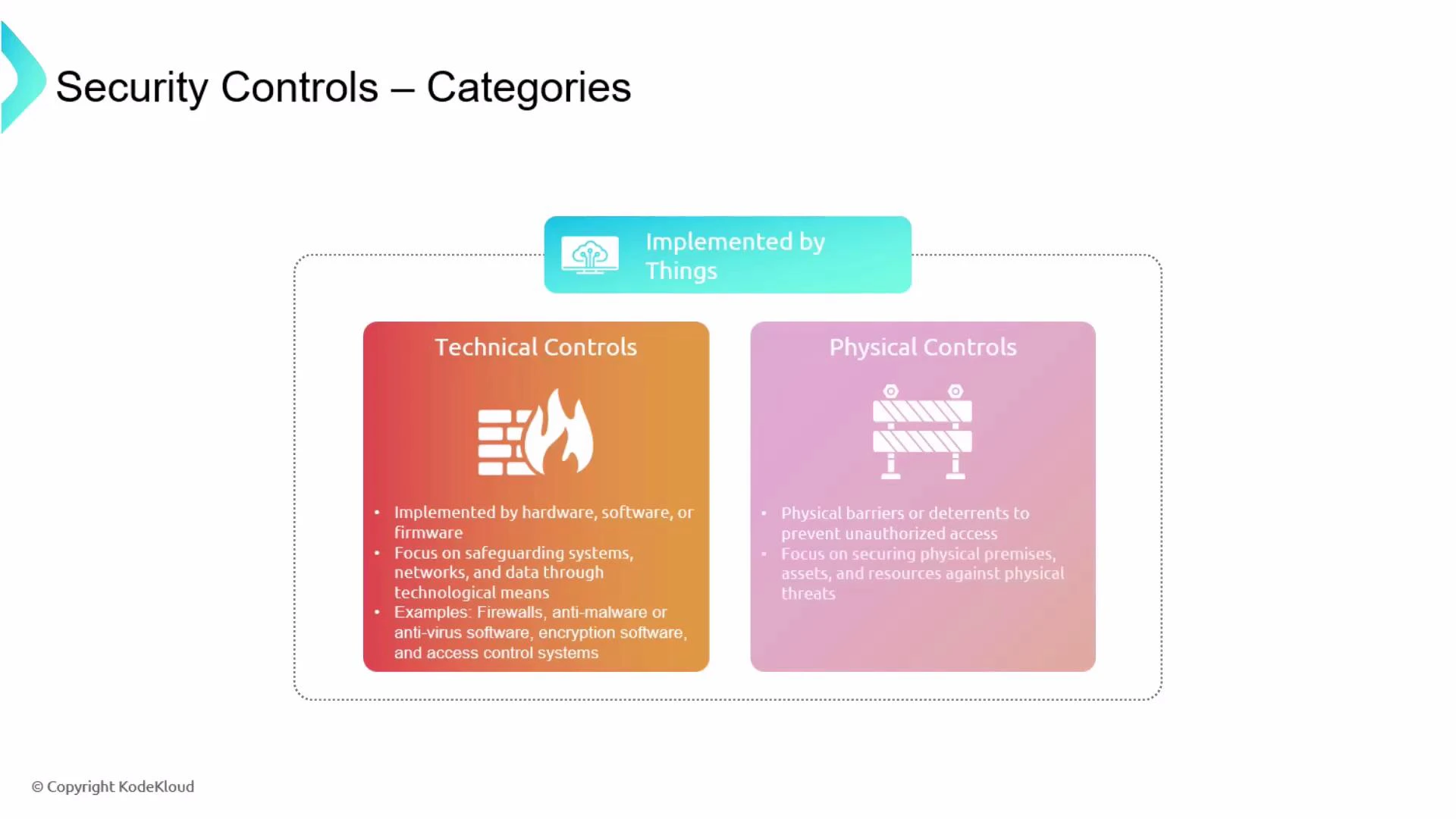
- Technical controls (implemented by things)
- Physical controls (implemented by things)
| Control Category | Implemented By | Purpose / Use Case | Examples |
|---|---|---|---|
| Managerial | People (leadership/management) | Define policies, governance, risk tolerance, and responsibilities | Security policy, risk assessments, governance frameworks |
| Operational | People (staff/operations) | Day-to-day execution of security tasks and procedures | Incident response, backups, change control, data classification |
| Technical | Systems (hardware/software/firmware) | Enforce security automatically at a technical level | Firewalls, IDS/IPS, authentication, encryption |
| Physical | Things (physical devices/structures) | Prevent or deter unauthorized physical access and tampering | Locks, fences, badge readers, CCTV, lighting |
Managerial Controls (implemented by people)
Managerial controls are set by organizational leadership to define what must be done and who is accountable. They build the foundation for a security program and typically include:- Policies, standards, and procedures
- Security governance and oversight
- Risk assessments, business impact analysis, and acceptance criteria
- Security planning and resource allocation
- Vendor/third-party risk management
Operational Controls (implemented by people)
Operational controls are the everyday security-related activities performed by staff to implement managerial direction. They typically focus on processes and human behavior:- Incident response and forensics
- Change management and configuration control
- Asset management and inventory
- Data labeling, classification, and handling
- Physical security patrols and identity verification
Technical Controls (implemented by things)
Technical controls are implemented via hardware, software, or firmware. They are designed to automatically enforce security policies and reduce human error:- Network defenses: firewalls, IDS/IPS, network segmentation
- Endpoint protections: antivirus/anti-malware, EDR
- Access controls: authentication, authorization, access control lists (ACLs)
- Data protection: encryption (at-rest and in-transit), tokenization
- Monitoring and logging systems
Physical Controls (implemented by things)
Physical controls protect facilities, systems, and personnel from physical threats. They are implemented as tangible barriers and detection systems:- Structural: fences, gated perimeters, walls
- Entry controls: locks, badge readers, turnstiles, vestibules
- Environmental: lighting, secure enclosures, tamper-evident seals
- Detection: cameras (CCTV), motion sensors, alarms
- Human: security guards, reception screening
Deception-based Controls (honeypots and honeynets)
Deception-based controls are designed to lure, observe, and analyze attackers. A honeypot is a deliberately vulnerable or enticing system deployed to attract adversaries so defenders can study attacker behavior and tactics without risking production assets. Key considerations for honeypots:- Isolate them from production networks to prevent lateral movement.
- Instrument honeypots with detailed logging and monitoring.
- Treat honeypots as research and detection tools, not replacements for hardening real systems.
- Consider legal and privacy implications before recording or interacting with attackers.
Honeypots require careful design and legal consideration: they must be isolated to prevent attackers from pivoting into production, and monitoring/collection must comply with privacy and legal requirements.
Further reading and references
| Resource | Why it helps |
|---|---|
| NIST Cybersecurity Framework | Guidance on risk-based cybersecurity governance and control selection |
| CompTIA Security Resources | Practitioner-focused security topics and certification materials |
| OWASP Cheat Sheets | Best practices for technical controls and application security |