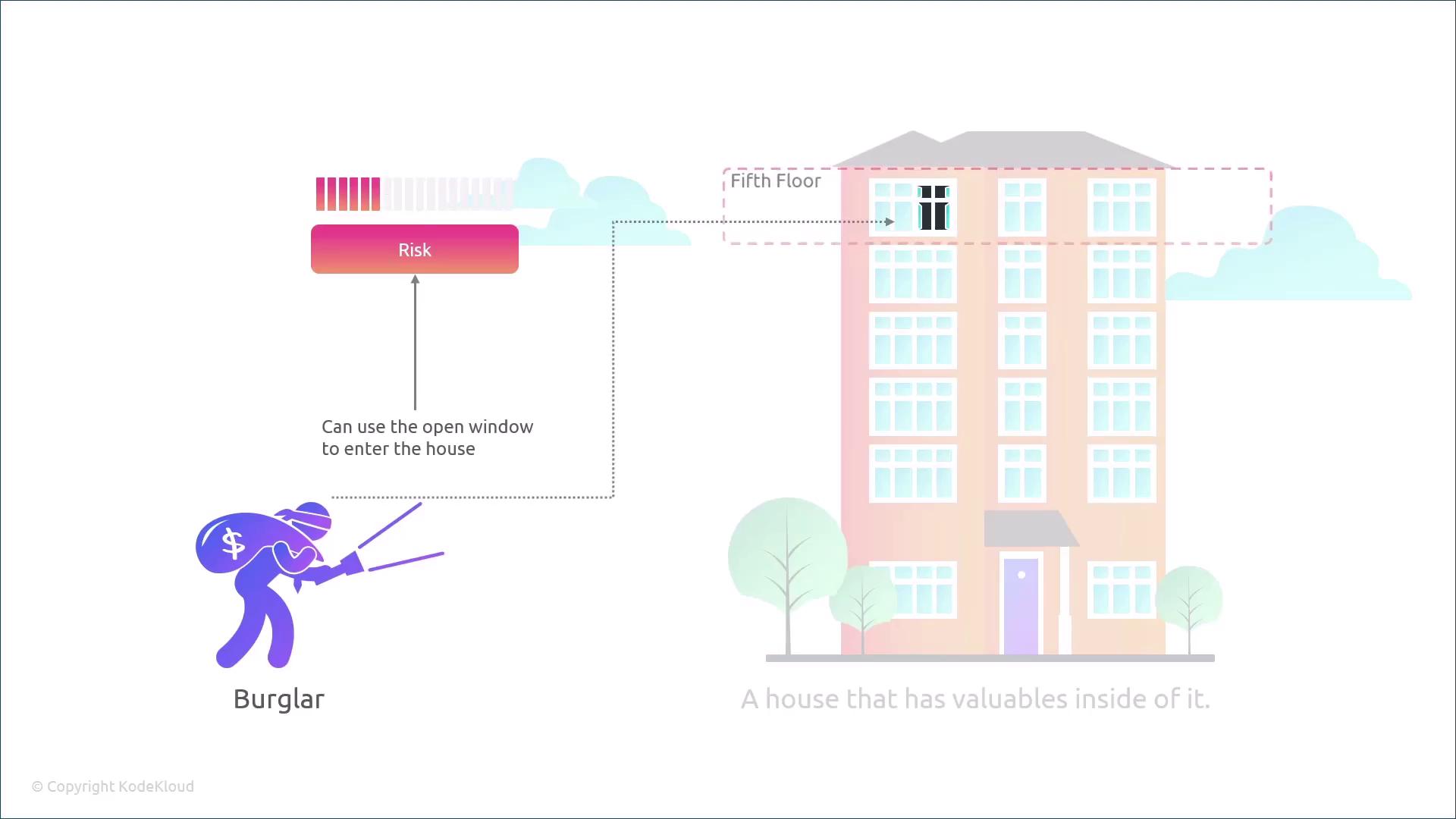
In this lesson, we examine the various threat actors in today’s security landscape, their motivations, and how they exploit vulnerabilities. Understanding these concepts is crucial for analyzing and mitigating security risks in any environment. Imagine you own a house filled with valuables. Now, picture an open window in that house. This open window represents a vulnerability—a weakness that an attacker can exploit—even if every other entry point is well secured. Later in this course, we will explore vulnerabilities in depth, covering weaknesses in hardware, software, networks, and physical security. Now, consider a burglar planning to break into the house. This burglar is the threat actor. With both a vulnerability (the open window) and a threat actor (the burglar), there exists a potential threat: the risk that an intruder could exploit the vulnerability. A threat is defined as the potential for someone to exploit a vulnerability. The risk level depends on the likelihood of the threat actor’s successful exploitation and the possible impact. For instance, if the open window is on the ground floor, the risk is considerably higher.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
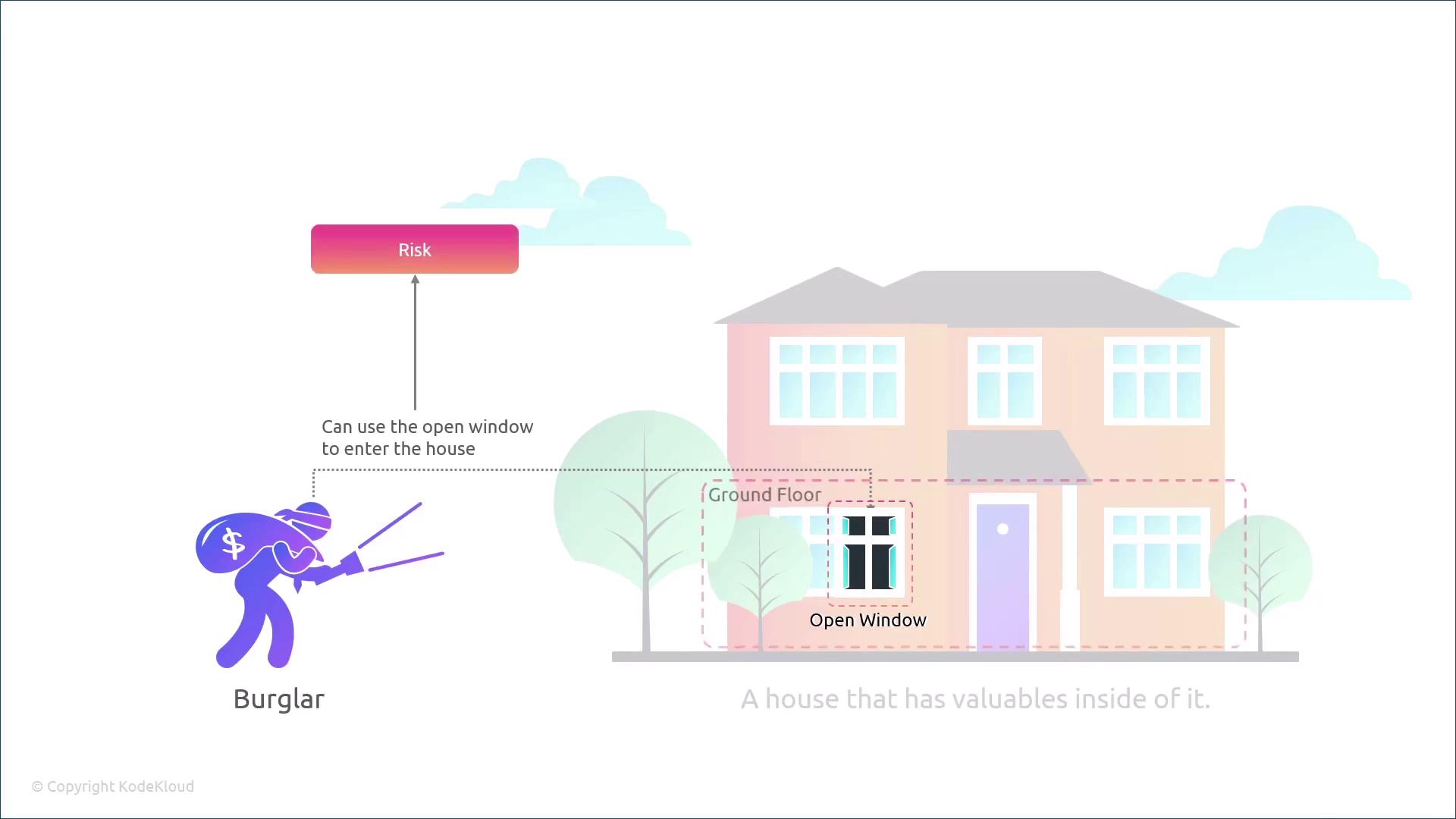
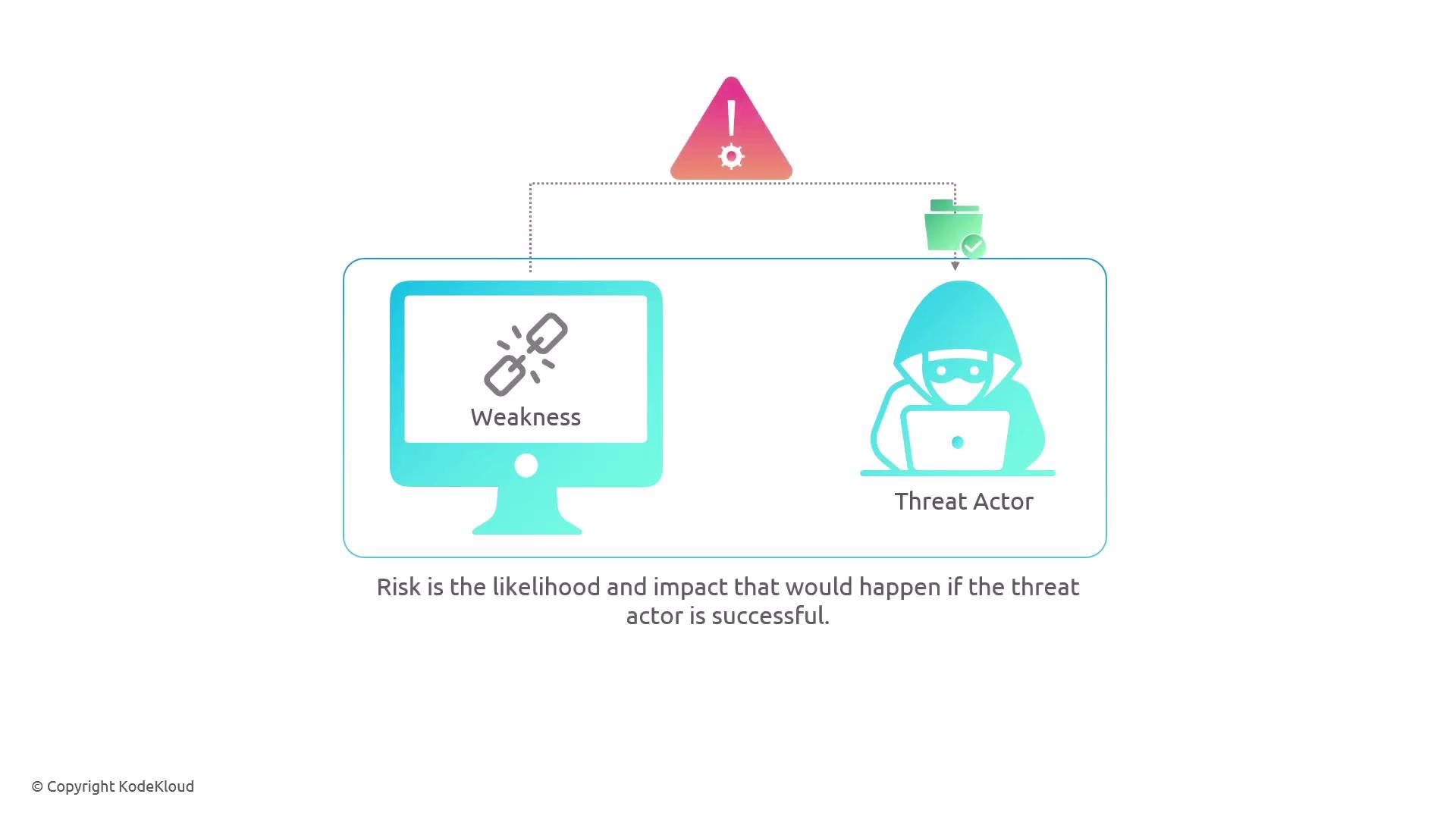
Before diving deeper into threat actors, it is important to understand the differences between vulnerabilities, threats, and risk:
- A vulnerability is a flaw or weakness.
- A threat involves a threat actor who is willing and able to exploit a vulnerability.
- Risk is determined by the likelihood of the exploitation and the potential impact.
- The likelihood that a threat will exploit a vulnerability.
- The potential impact if the exploitation is successful.
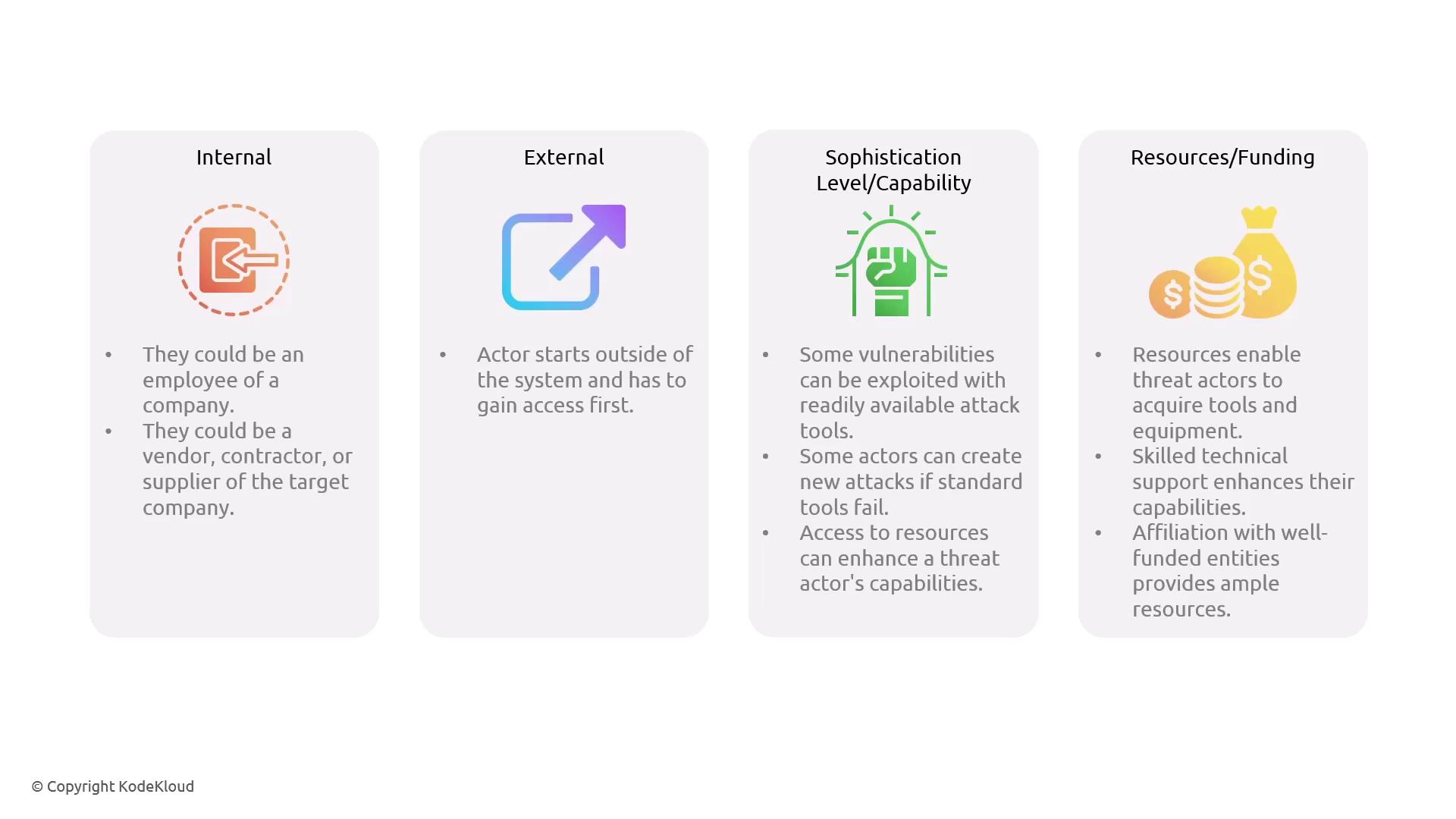
- Internal Threat Actors: These individuals already have access permissions within the system. This category includes employees, vendors, contractors, or suppliers.
- External Threat Actors: These attackers must first gain access to the system before attempting to exploit vulnerabilities.