Hi, and welcome back! In this lesson, we explore the Social Engineering Toolkit (SET) to demonstrate how to clone websites—a common technique used in social engineering attacks. SET is a comprehensive suite of penetration testing tools designed to identify vulnerabilities in your network. In this lab, our focus is on website cloning and credential harvesting.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview of Social Engineering with SET
Social engineering attacks frequently rely on phishing, where attackers send emails that appear to be from reputable organizations (e.g., banks or financial institutions). These emails typically urge the target to click on a link leading to a cloned webpage. The cloned site closely resembles the authentic site, tricking users into entering their login credentials. Once entered, these credentials are captured by the attacker for misuse.Lab Walkthrough
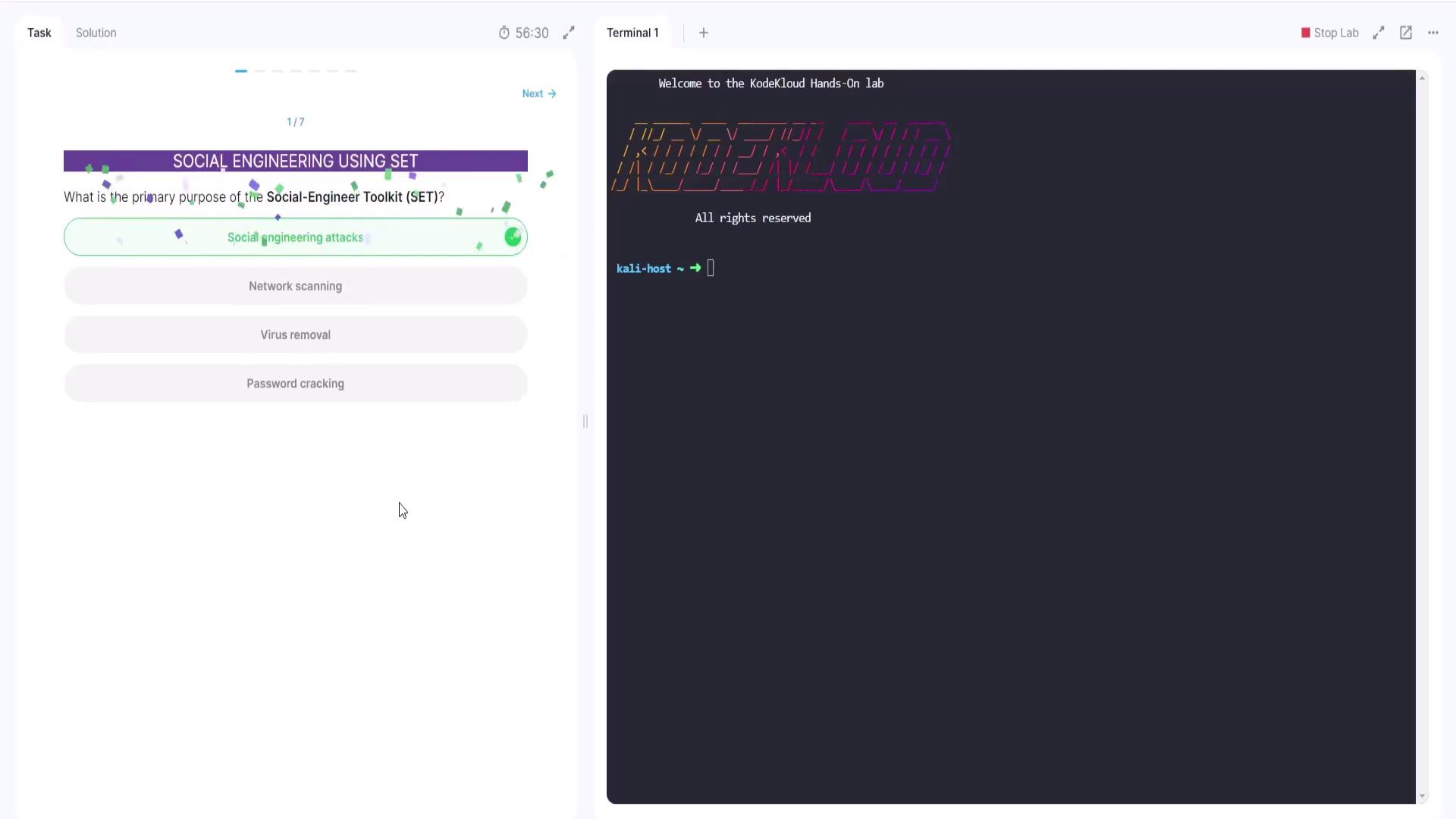
Question 1: Primary Purpose of SET
The first question asks: What is the primary purpose of the Social Engineering Toolkit? The options include:- Social engineering attacks
- Network scanning
- Virus removal
- Password cracking
Question 2: Common Attack Vector in SET
Next, the lab asks: Which of the following is a common attack vector used in SET? The available options are:- Buffer overflows
- SQL injection
- Credential harvester
- Denial of service
Question 3: Purpose of the Website Attack Vectors Module
The third question asks: What does the website attack vectors module in SET primarily aim to do? Its main function is to create fake (cloned) websites designed to capture user credentials. The correct answer is that it generates cloned websites. A sample output from the lab illustrates:Question 4: Goal of the Credential Harvester Attack Method
The fourth question asks: What is the main goal of the credential harvester attack method? The correct answer is to capture sensitive credentials.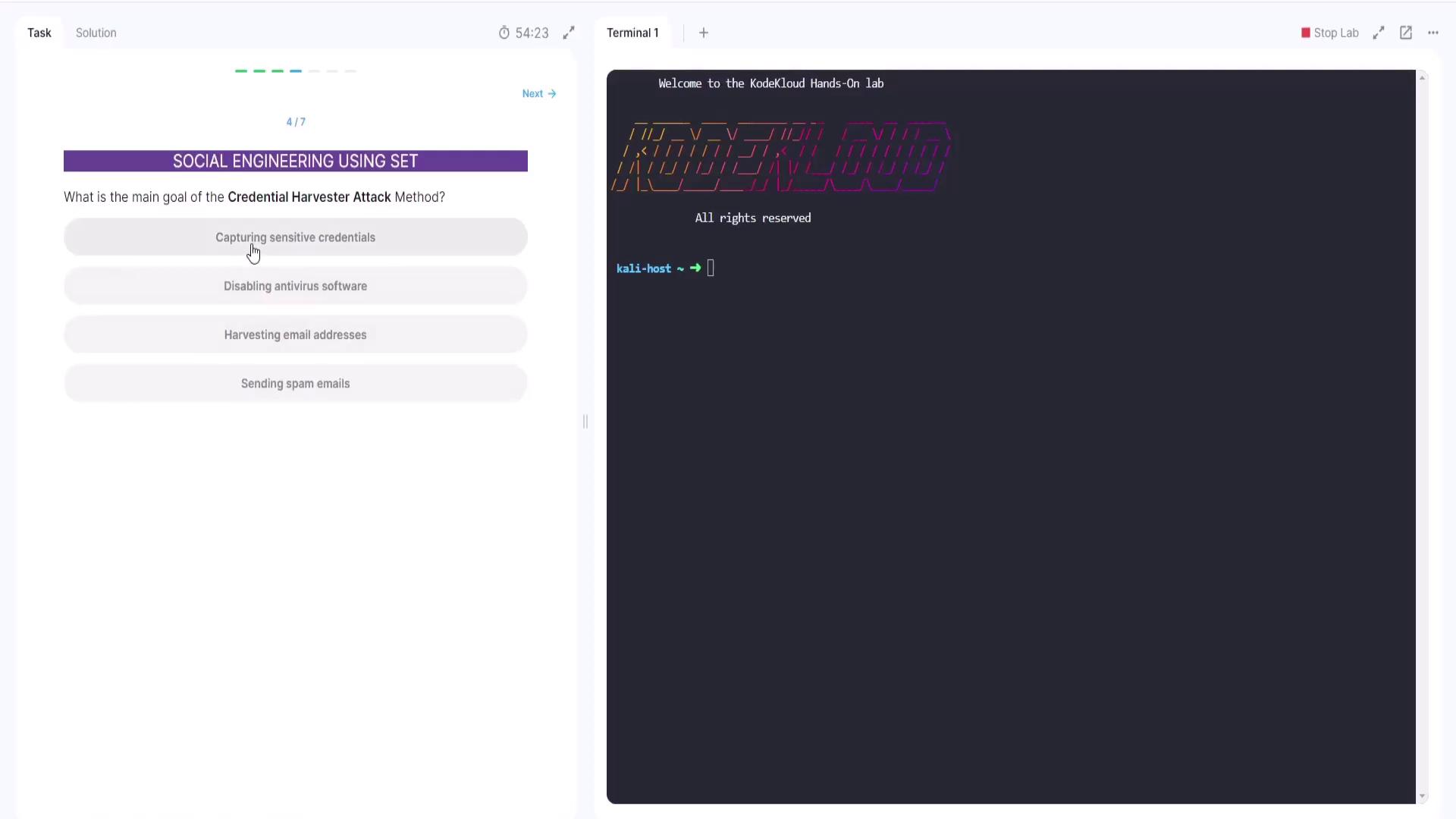
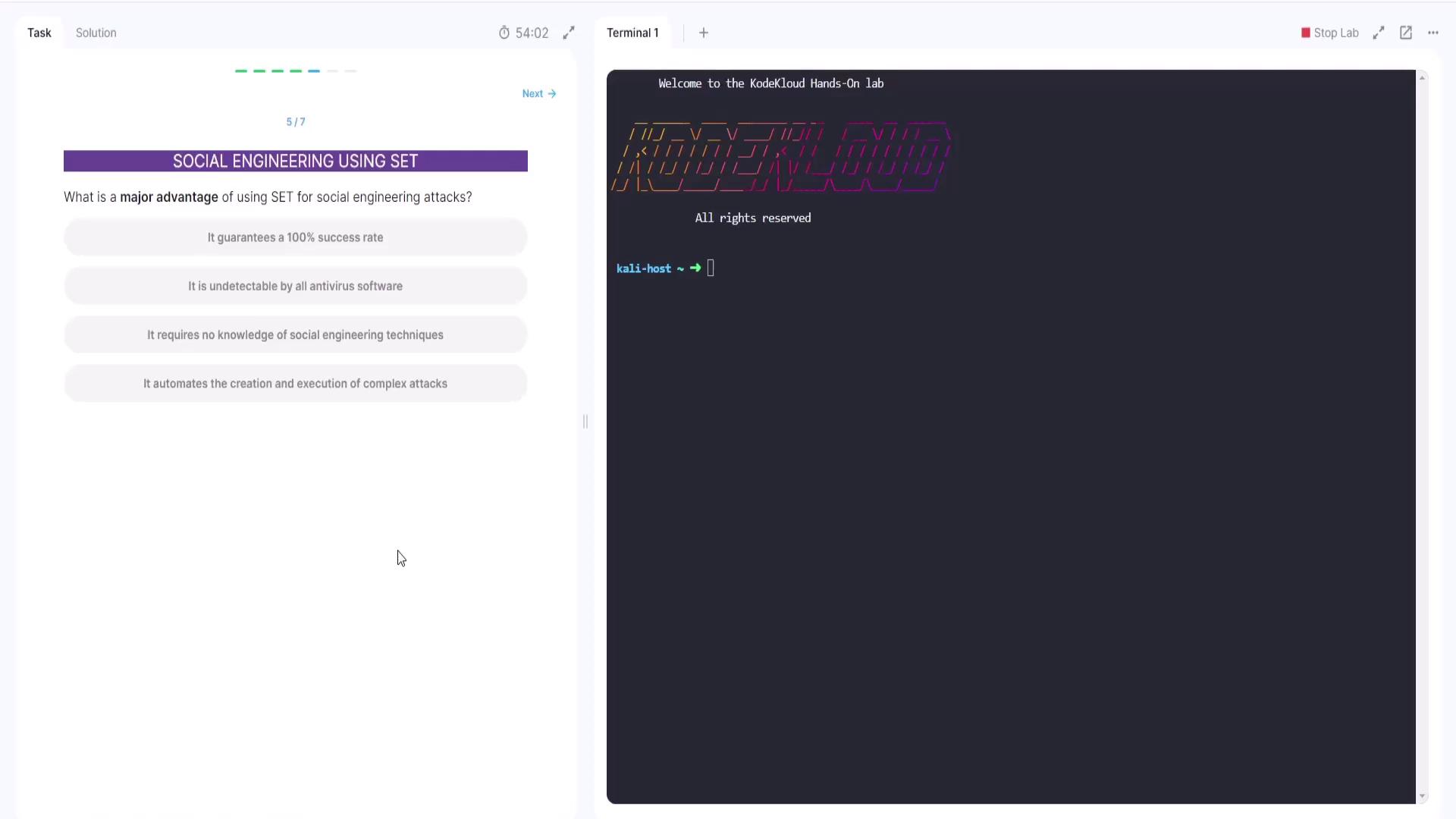
Question 5: Advantage of Using SET for Social Engineering
The next question evaluates the advantages of using SET. The options include:- Guarantees a 100% success rate
(Incorrect – no method can guarantee complete success as the target must be deceived into clicking the link.) - Undetectable by antivirus software
(Not entirely correct – this attack does not typically involve installing malware detectable by antivirus software.) - Requires no knowledge of social engineering techniques
(Incorrect – successful use of SET requires an understanding of social engineering principles.) - Automates the creation and execution of complex attacks
(Correct – SET streamlines and automates various stages of the attack process.)
Cloning a Website Using SET
In this section, we demonstrate how to use SET to clone a website and launch a social engineering attack aimed at harvesting user credentials. First, visit the target website that you want to clone. The following screenshot shows a legitimate login page: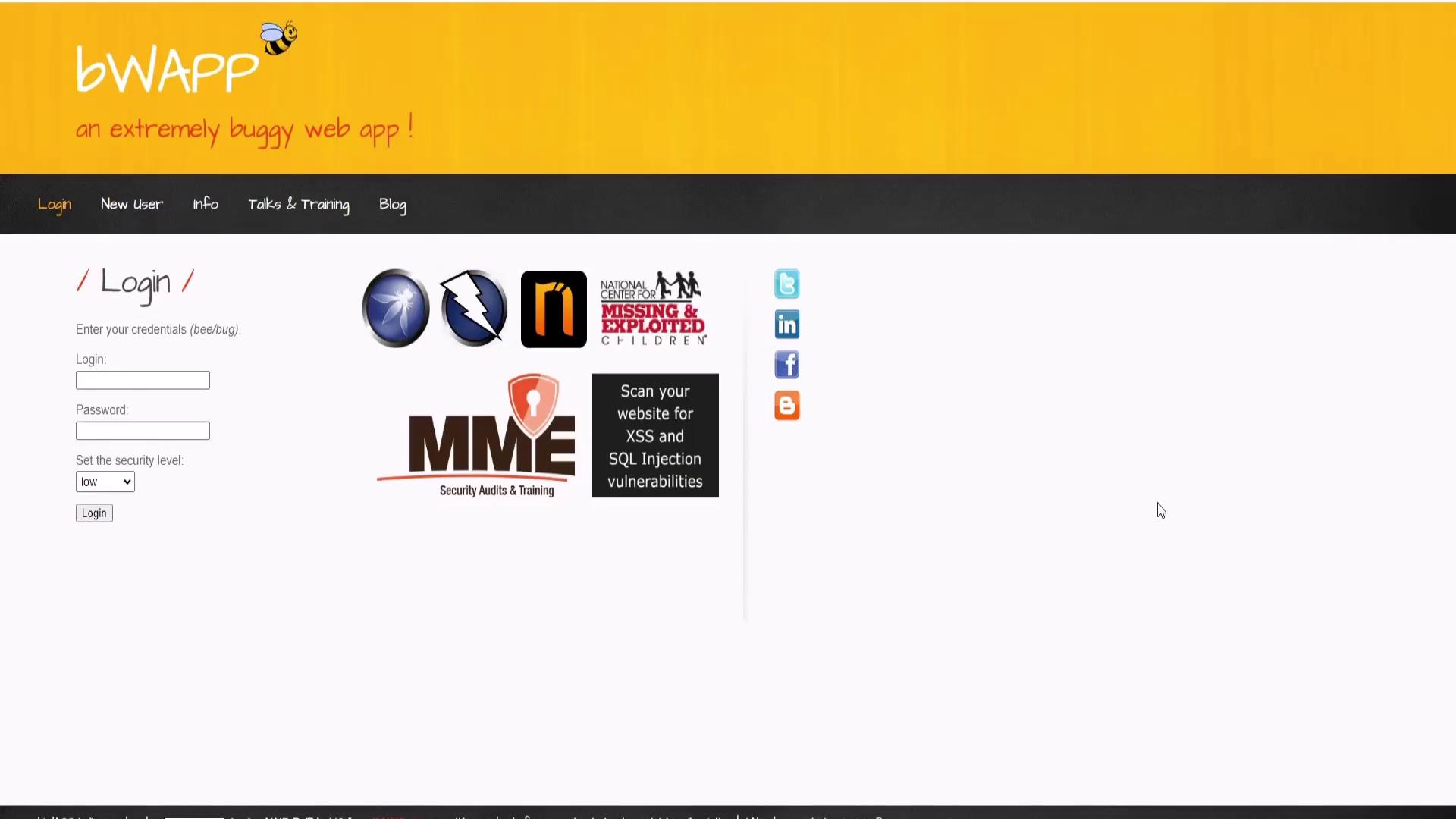
Step 1: Launch SET
Begin by launching SET with root privileges. Open your terminal and run:Step 2: Choose Website Attack Vectors
From the subsequent menu, choose the Website Attack Vectors option:Step 3: Provide POST Back Information
If you are using the credential harvester, SET will prompt you for the IP address for POST back. You can press Enter to use the default settings or input a custom URL as provided in your instructions. For example:Ensure you follow all legal guidelines when conducting tests with SET. This demonstration is intended for authorized and ethical use only.
Thank you for joining this lab walkthrough. Now it’s your turn to complete the lab using the provided instructions and tools. Happy testing!