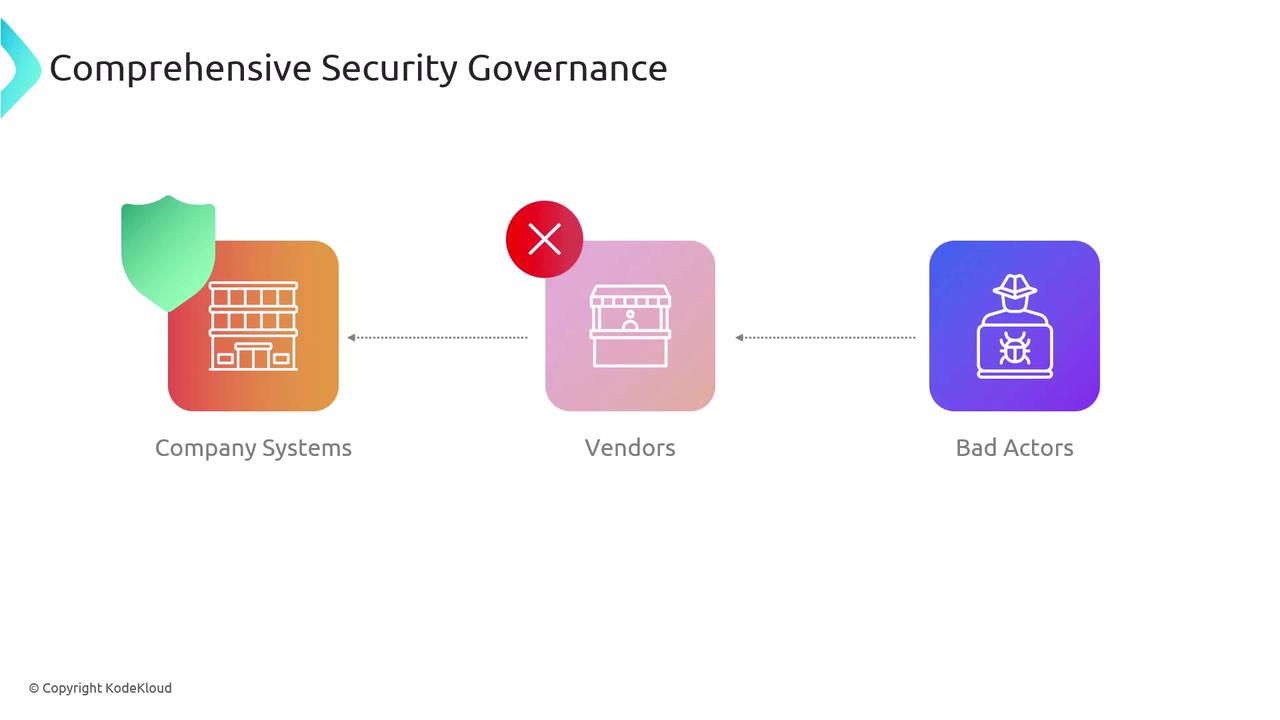
Comprehensive security governance goes beyond evaluating your own systems—it must also include a thorough assessment of your vendors. Cyber attackers often exploit vulnerabilities within vendor infrastructures as a gateway to compromise your company systems or access sensitive data. By integrating vendor assessments into your security strategy, you can significantly mitigate this risk.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Penetration Testing
Penetration testing offers a proactive method to uncover vulnerabilities before attackers can exploit them. You have two main options:- Perform internal penetration tests to simulate external attacks.
- Request that your vendor submits evidence of successful penetration tests conducted on their systems.
Penetration testing not only highlights vulnerabilities but also helps prioritize risk mitigation efforts by demonstrating which areas require immediate attention.
Right to Audit Clauses
Including a right to audit clause in your vendor contracts is another critical strategy. This clause legally authorizes your company to perform audits and assessments on the vendor’s systems, ensuring they comply with relevant regulations and contractual requirements. You can either conduct these audits internally or rely on independent third-party auditors to verify compliance.Regular audits—whether internal or third-party—are essential for maintaining an up-to-date understanding of your vendors’ security practices.
Supply Chain Analysis
A comprehensive supply chain analysis examines all interconnected systems and networks involved in the creation, distribution, and delivery of your goods or services. This approach should cover every link in your product ecosystem, including suppliers, manufacturers, transporters, and retailers, to identify potential weak points or security vulnerabilities.