Understanding software vulnerabilities is critical to securing your IT infrastructure. Vulnerabilities are one of the most significant attack vectors, often stemming from coding flaws that can be exploited if not corrected. As software evolves with new features and continuous updates, the risk of introducing vulnerabilities increases. Addressing these vulnerabilities requires a robust patching system that rapidly identifies issues, thoroughly tests patches, and implements fixes promptly.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
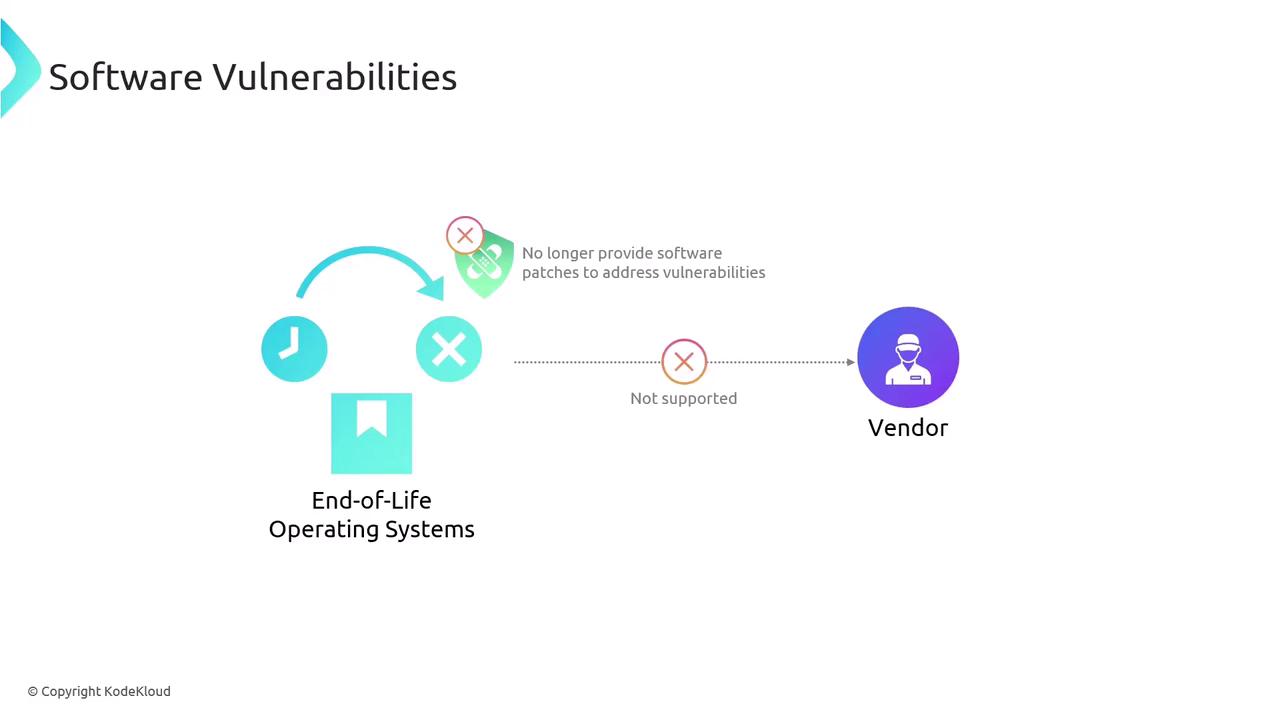
Unsupported products and systems can become critical attack vectors. It is essential to either remove, isolate, or remediate these systems promptly to mitigate the risk.
- Software agents are installed on each client machine. These agents continuously monitor the system and report vulnerabilities back to a centralized management server.
- Agentless scanning relies on a central server to scan each client directly without installing additional software.