In the final section of our discussion on Threats, Vulnerabilities, and Mitigations, we explore how cryptography can defend against security risks. Cryptography involves encoding and decoding data to protect its confidentiality and integrity. This article provides an in‐depth look at Public Key Infrastructure (PKI), encryption methods, digital certificates, and related cryptographic solutions.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
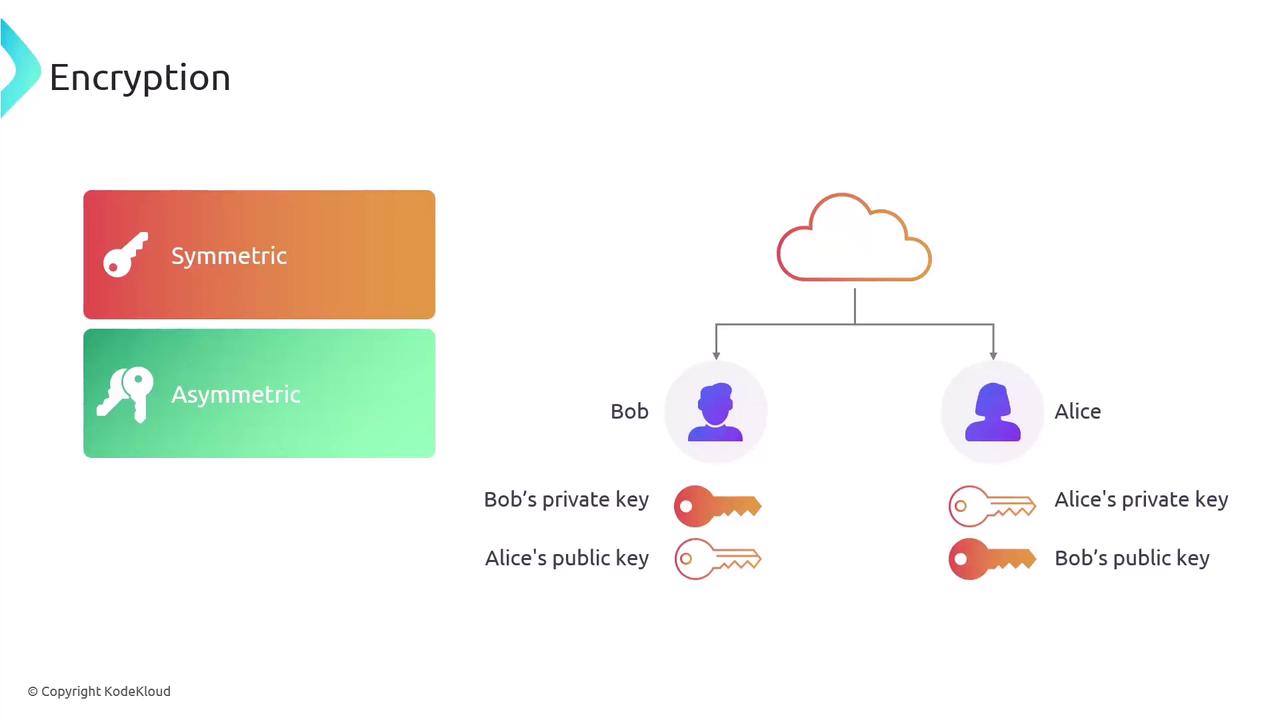
Public Key Infrastructure (PKI)
Public Key Infrastructure (PKI) is a cryptographic framework that establishes trust through encryption and digital signatures. It plays a crucial role in securing communications over public internet channels as well as within private networks. To grasp how PKI operates, it is essential to understand the concept of asymmetric encryption, which secures data confidentiality by utilizing two distinct keys:- Public Key: This key can be shared openly and is even available on the internet.
- Private Key: This key is kept exclusively by the owner and is never shared.
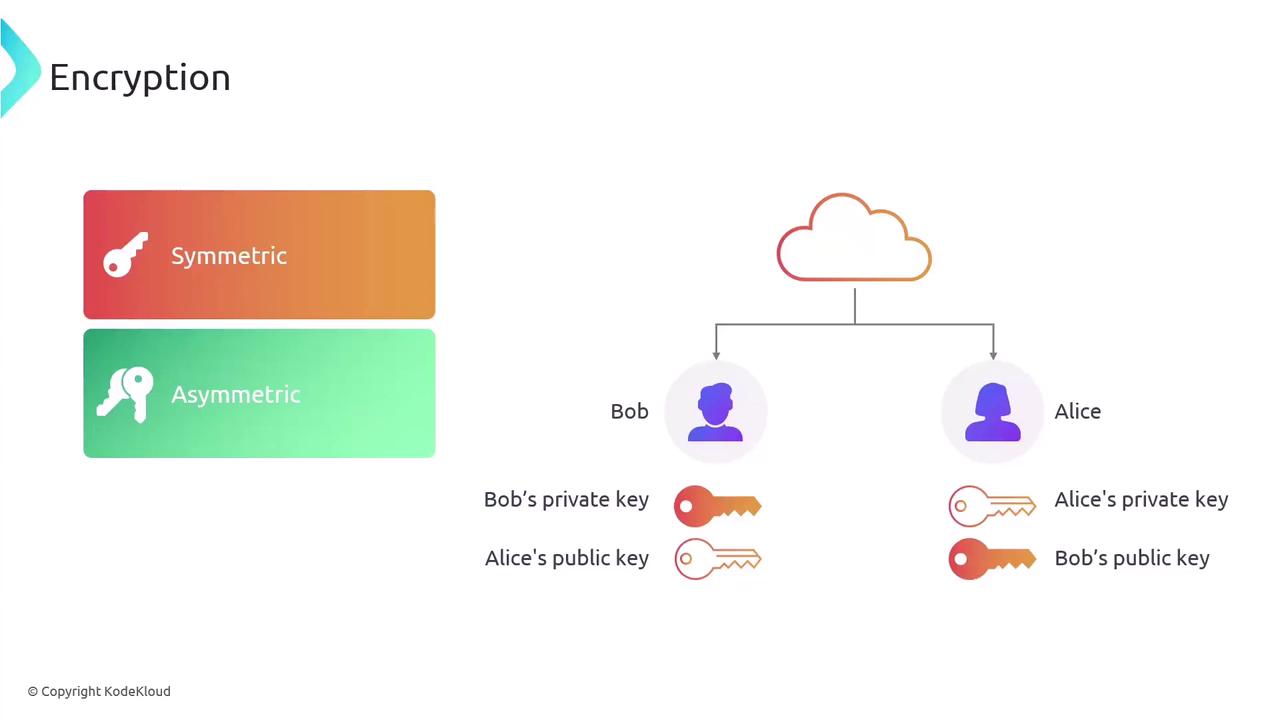
Encryption Methods
Encryption is at the heart of cryptographic systems like PKI. There are two primary types of encryption:- Symmetric Encryption: Uses the same key for both encryption and decryption.
- Asymmetric Encryption: Utilizes a pair of keys—one public and one private—for encryption and decryption.
Digital Certificates
A digital certificate functions as a secure wrapper for a public key. It contains the public key along with information about its issuer, and it is digitally signed by a certificate authority. This signature validates the certificate and attests to the public key’s trustworthiness.Understanding digital certificates is critical for ensuring the authenticity of public keys and maintaining secure communications.