Welcome to the final section of our CompTIA Security+ preparation series. In this segment, we dive into the critical components of security program management and oversight, covering essential topics such as security governance, risk management, compliance, audits and assessments, and security awareness practices. These subjects are vital for managing an organization’s security posture, regardless of size, and are especially significant for individuals preparing for the Security+ certification exam.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
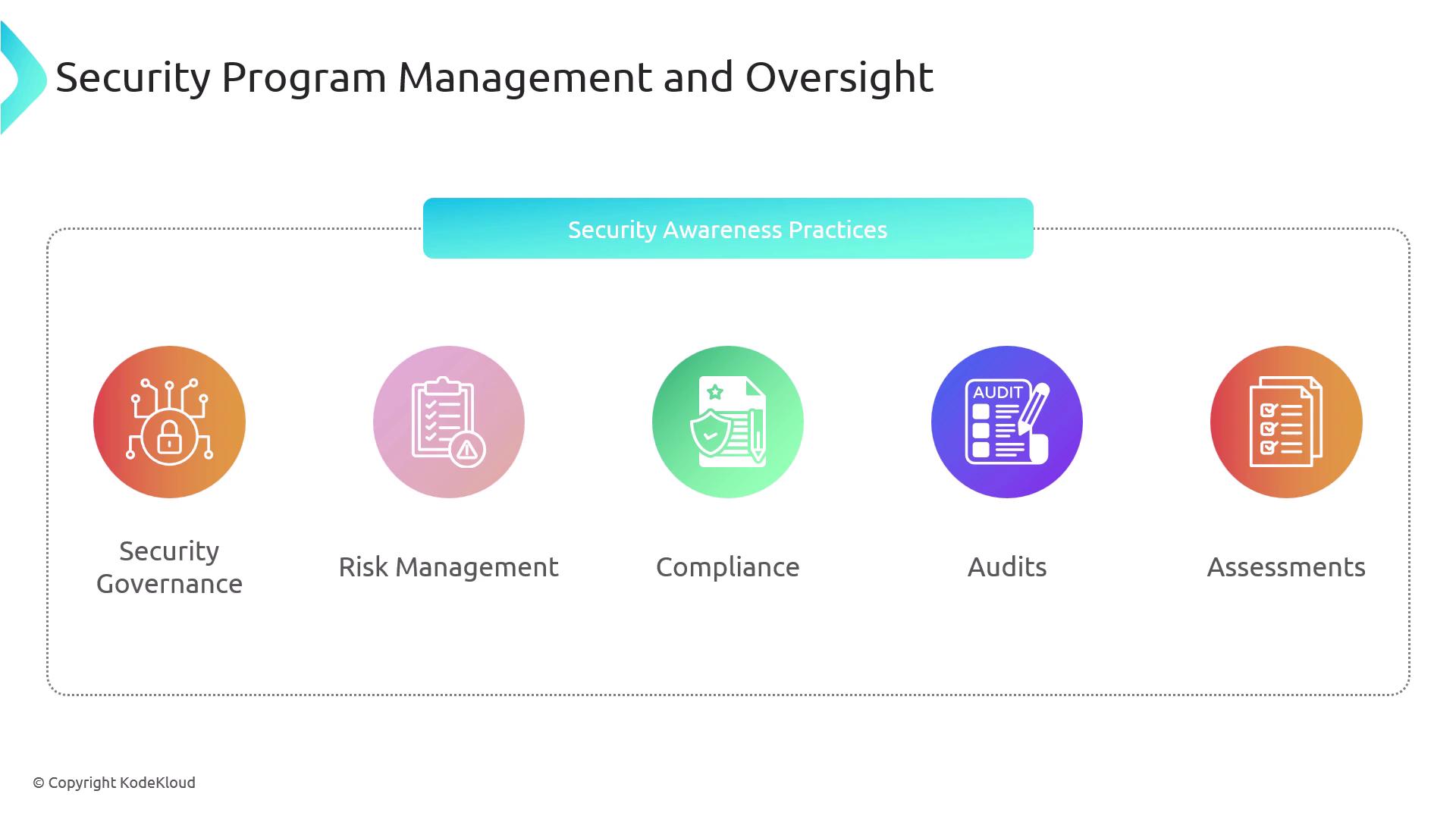
Understanding and integrating robust security program management practices is essential for protecting your organization’s digital assets and ensuring compliance with emerging regulations.
Security Governance
Security governance, as defined by CISA, represents a comprehensive cybersecurity strategy that aligns with an organization’s operational framework to prevent activity interruptions caused by cyber threats or attacks. Effective security governance involves a blend of guidelines, policies, standards, procedures, and external factors like vendor management.
- Risk Management: Continuously identify and mitigate potential security risks.
- Organizational Structures: Leverage boards, committees, and regulatory agencies to facilitate oversight.
- Data Management: Understand roles and responsibilities related to the collection, processing, and storage of personal data.
Guidelines, Policies, Procedures, and Standards
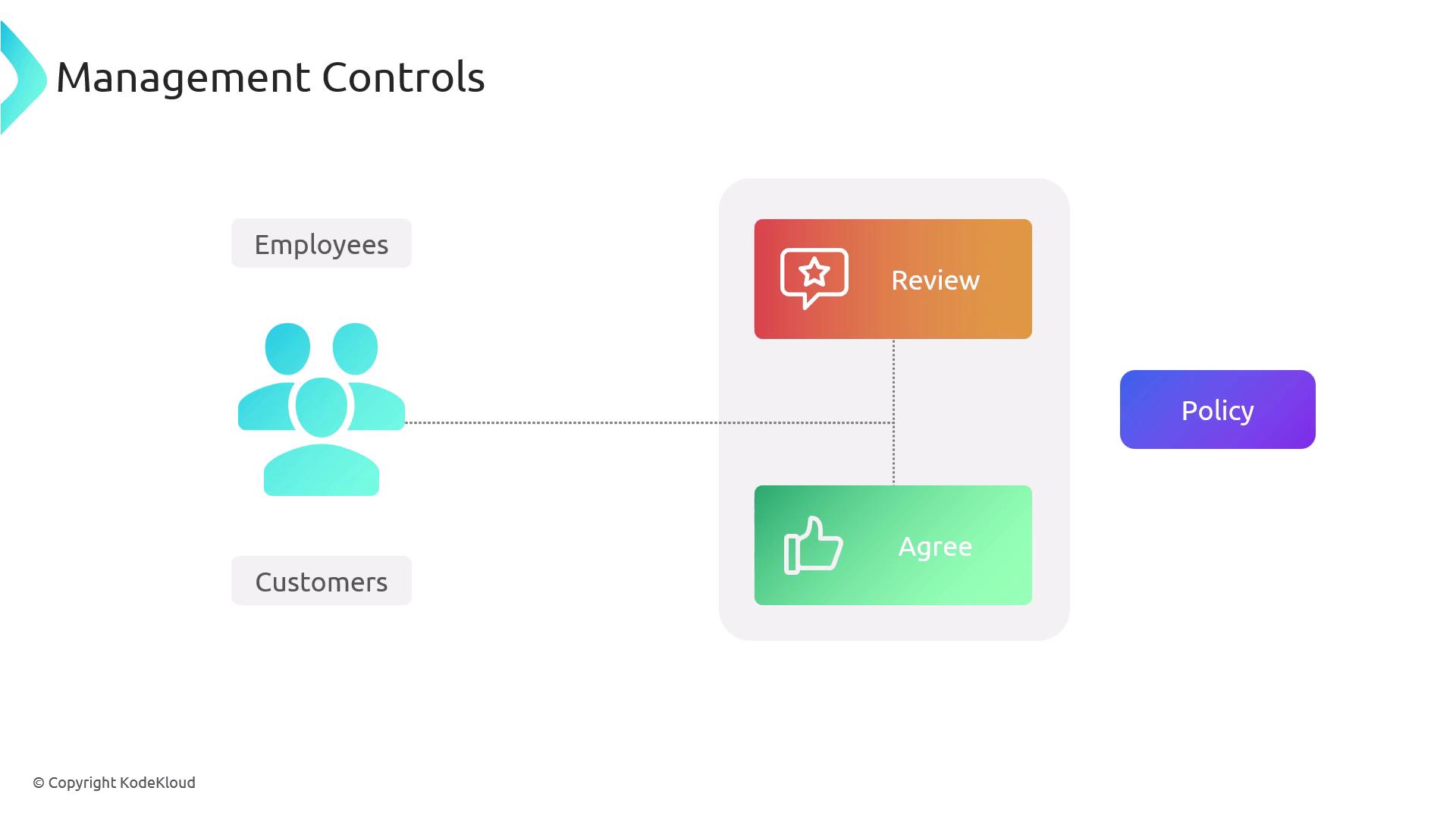
When establishing effective cybersecurity practices, organizations must develop comprehensive guidelines, policies, procedures, and standards. These components fall under various categories of controls, including management controls, which direct employee behavior and mitigate human-related vulnerabilities.
| Metric | Definition |
|---|---|
| Recovery Time Objective (RTO) | The maximum acceptable time to restore systems after a disruption. |
| Recovery Point Objective (RPO) | The acceptable limit of data loss measured in time. |
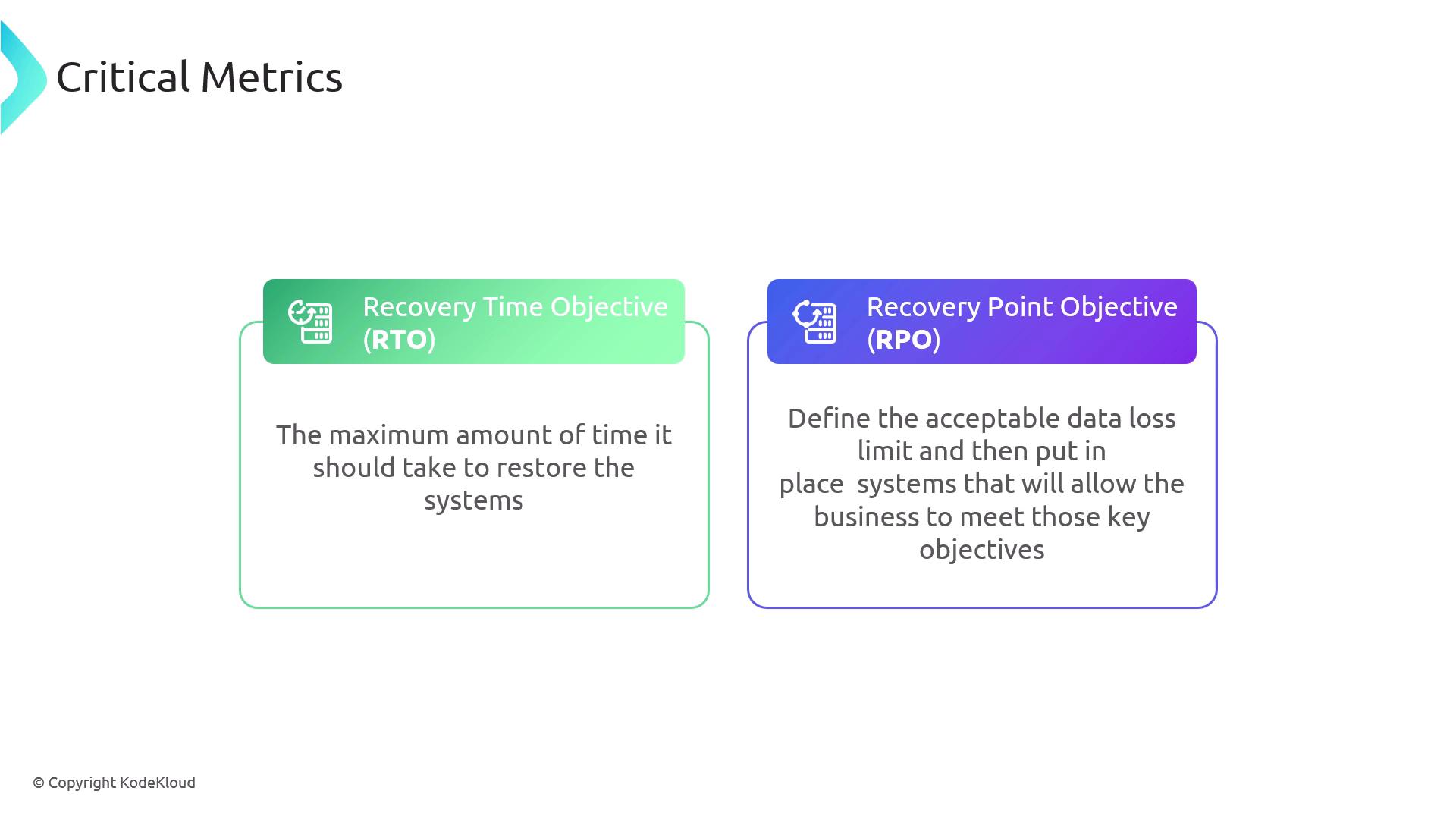
Scheduling regular disaster recovery tests and reviewing outcomes are essential practices to ensure that recovery plans remain effective and up to date.
Integrating the Software Development Lifecycle (SDLC) in Cybersecurity
Although the Software Development Lifecycle (SDLC) may seem unrelated to security at first glance, it is an integral component in mitigating application-related threats like SQL injection, buffer overflows, and vulnerabilities from outdated code. Incorporating security best practices—such as peer reviews and robust input validation—within the SDLC can significantly diminish these risks.