Hi, and welcome back! In this lesson, we explore the critical concepts of threat vectors and attack surfaces in cybersecurity. Later, we will identify various types of threat actors along with the attributes and motivations that distinguish them. There’s a lot to cover, so let’s dive in. Imagine your house with its multiple entry points—doors, windows, balconies, and even a garage. These entry points represent the attack surfaces. Similarly, in cybersecurity, attack surfaces include public-facing websites, applications, network ports, and system users.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
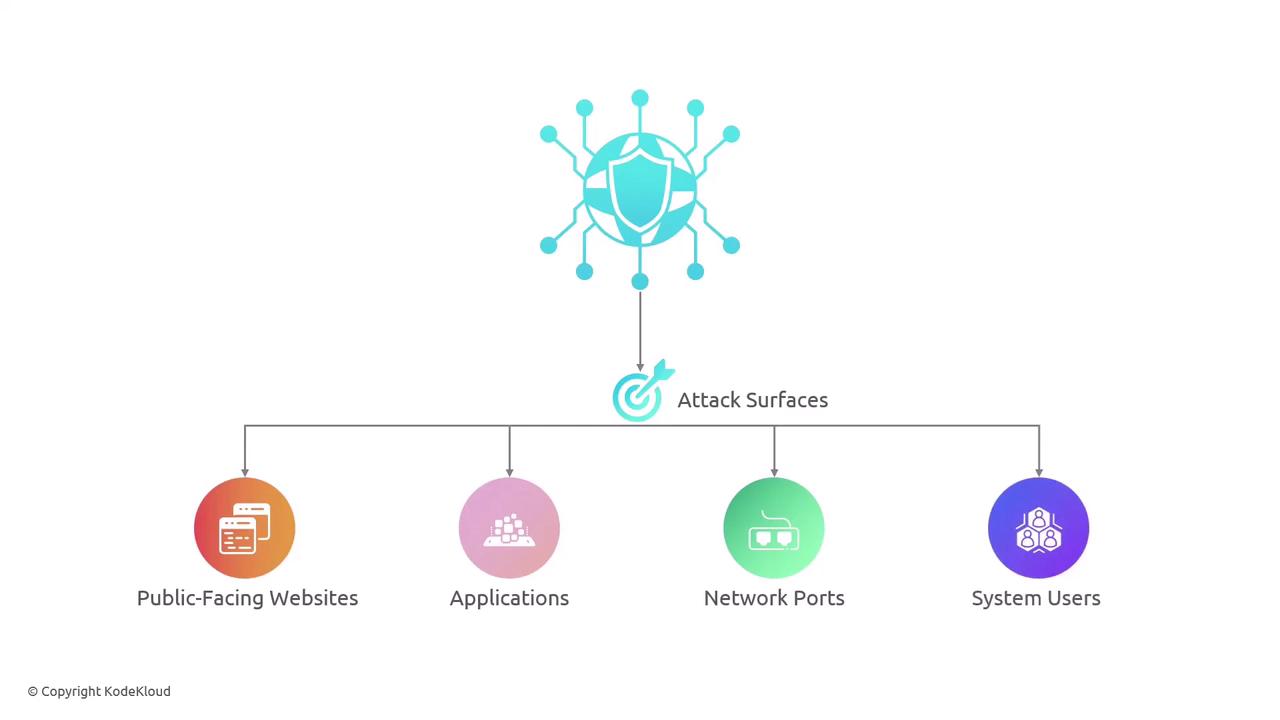

Understanding the relationship between attack surfaces and threat vectors is essential in building a robust cybersecurity defense. Regular assessments and vulnerability testing help protect against potential weaknesses.