RBAC (Role-Based Access Control) is a core component of Kubernetes security. Properly configuring RBAC helps protect your service accounts, users, and Kubernetes resources (such as Deployments, Services, Ingresses, ConfigMaps, and Secrets) from unauthorized access. Below, we break down the RBAC concepts and explain how they function to secure a Kubernetes cluster.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
What is RBAC?
RBAC provides a structured way to authorize access to resources. By assigning specific permissions to users, ServiceAccounts, or groups, RBAC ensures that only authorized entities can perform defined actions on resources. For example, you can allow a ServiceAccount to create Pods within a particular namespace (like the Sock Shop namespace) or let specific users fetch and create resources based on their roles. RBAC can be defined at two levels:- Namespace Level: Controls access within a single namespace.
- Cluster Level: Grants permissions across all namespaces.

Namespace vs. Cluster Scope
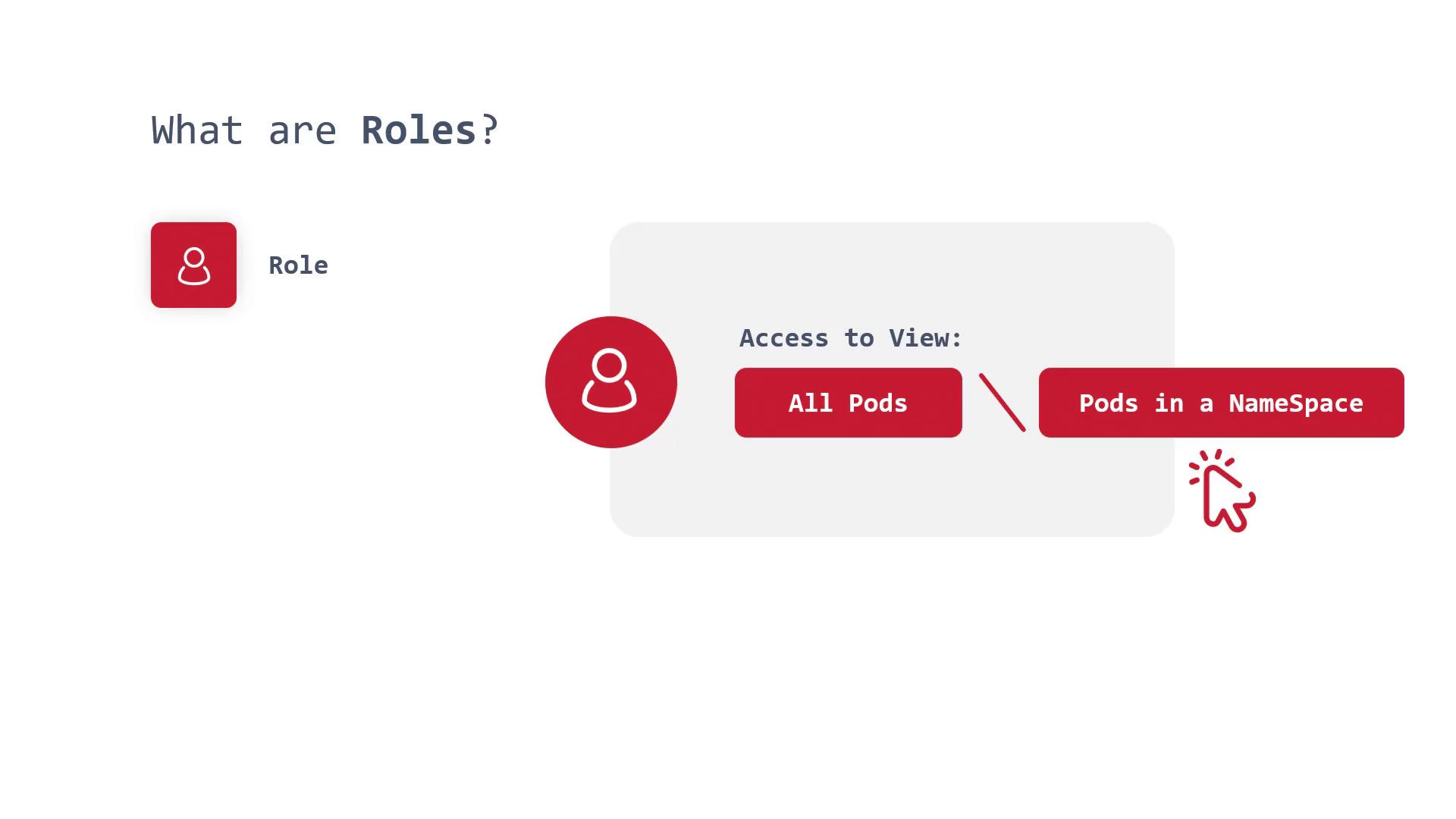
You can define RBAC roles to limit access either to specific namespaces or the entire cluster. A role created within a namespace confines its permissions to that namespace, whereas a cluster role provides access control across all namespaces.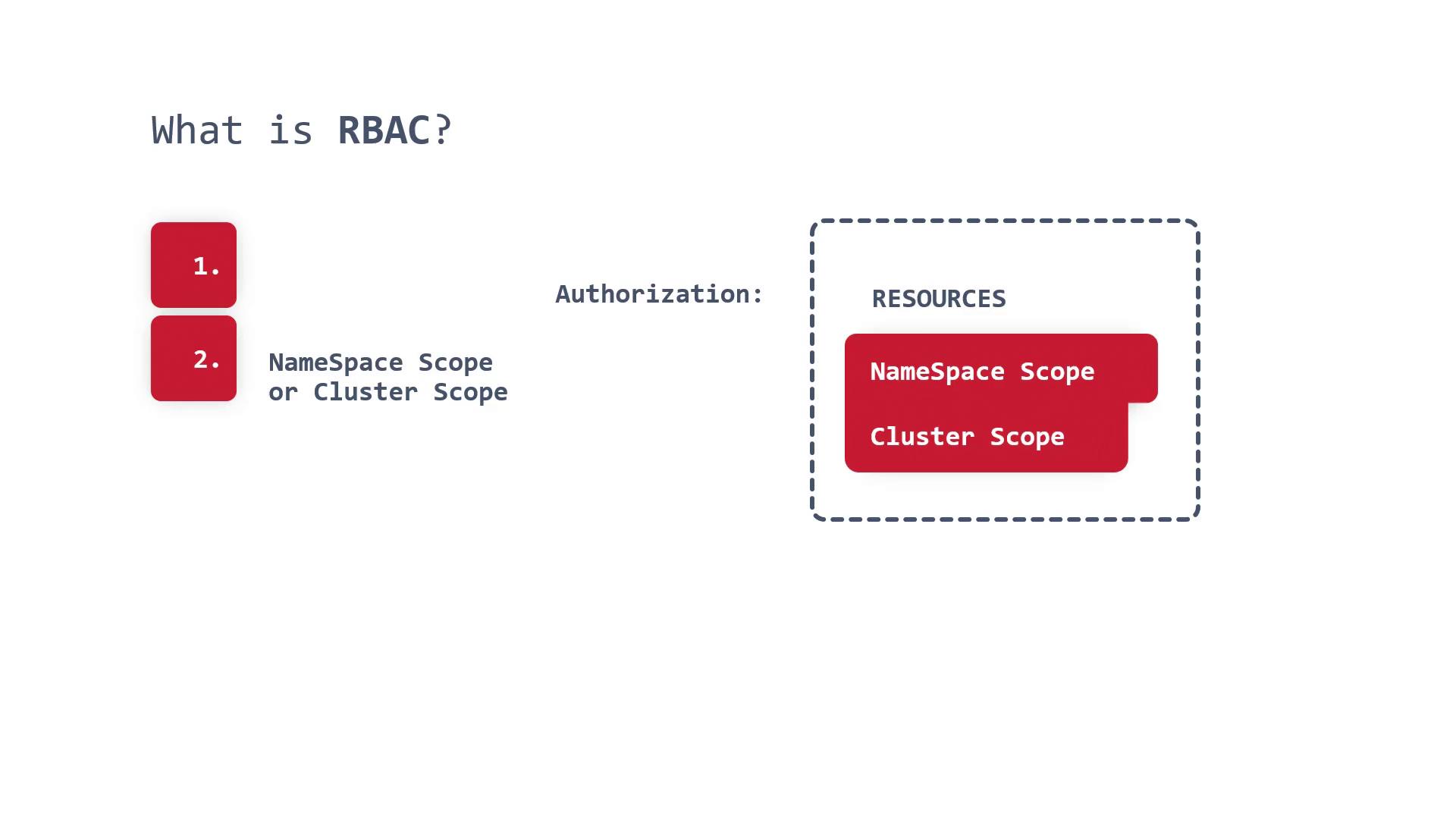
If RBAC is not configured correctly, your Kubernetes cluster and all its resources might be exposed to potential security breaches. Always implement RBAC with careful planning.
Components of RBAC
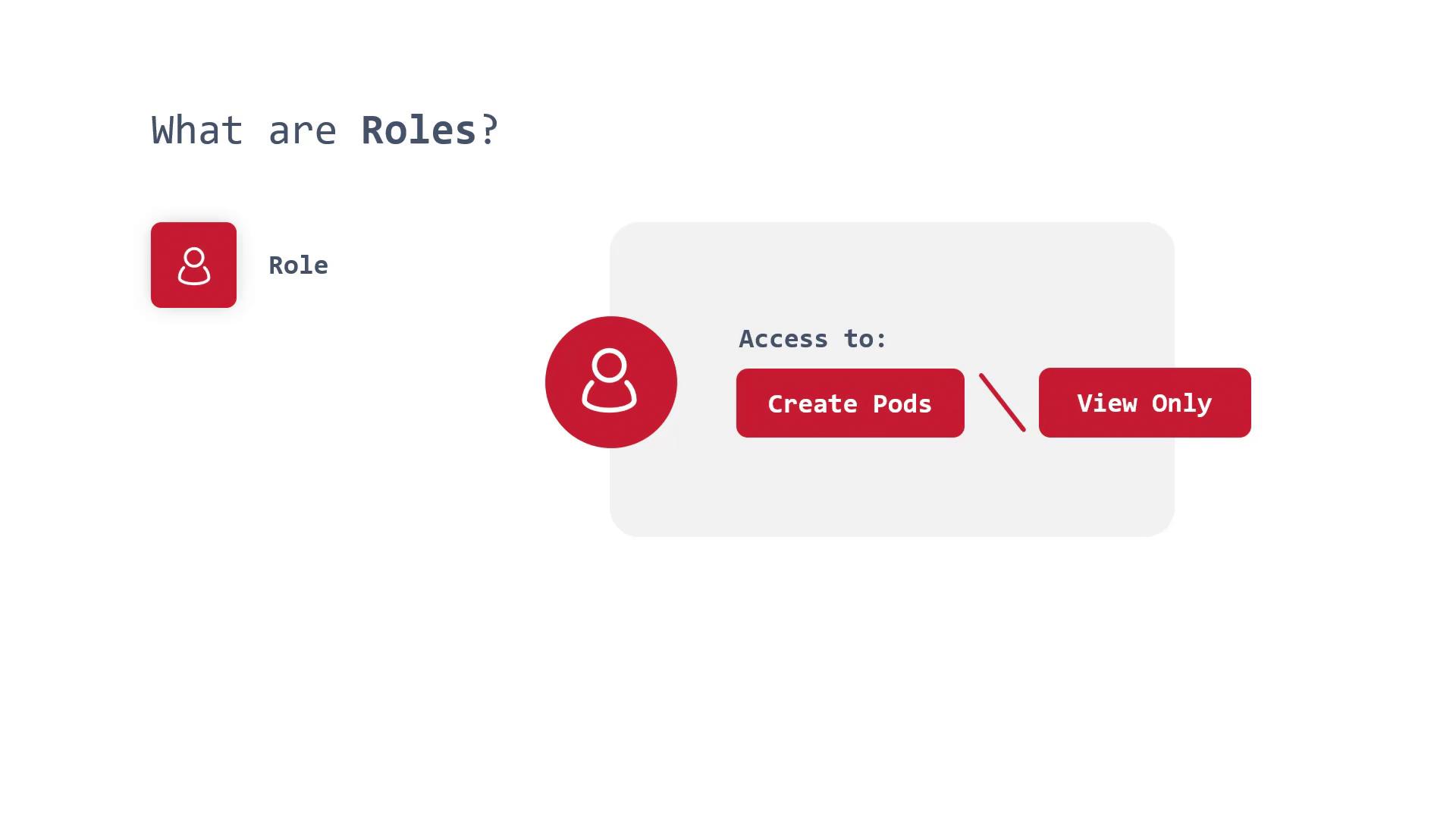
RBAC in Kubernetes is built around four key components:1. Roles
Roles define the permitted actions for users, ServiceAccounts, or groups within a specific namespace. For example, one role may allow a user to create Pods in the Sock Shop namespace, while another role might restrict access to read-only permissions.