Security in the Kubernetes ecosystem is often overlooked, even though it plays a crucial role in maintaining a reliable and secure environment. In many organizations, a significant disparity exists between the number of developers and dedicated security engineers. In some cases, there may not even be a dedicated security team at all. A recent Red Hat State of Kubernetes and Container Security report revealed that nearly 70% of security issues are caused by misconfigurations, while 27% stem from runtime security incidents. These alarming statistics highlight the critical need to address security challenges effectively.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
What are Security Context Constraints (SCC)?
Security Context Constraints (SCC) provide a robust mechanism for controlling pod permissions. Think of SCC as the access control system for pods—it defines what a pod is allowed to do, which resources it can access, and its overall security credentials. While Role-Based Access Control (RBAC) manages user permissions, SCC focuses on system-level security, including integrations with third-party applications. Moreover, SCC leverages native Linux capabilities, such as SELinux, enabling you to apply familiar policies directly to your pods.
SCC not only enhances security by limiting pod actions but also complements other controls like RBAC and network policies, creating a layered defense strategy.
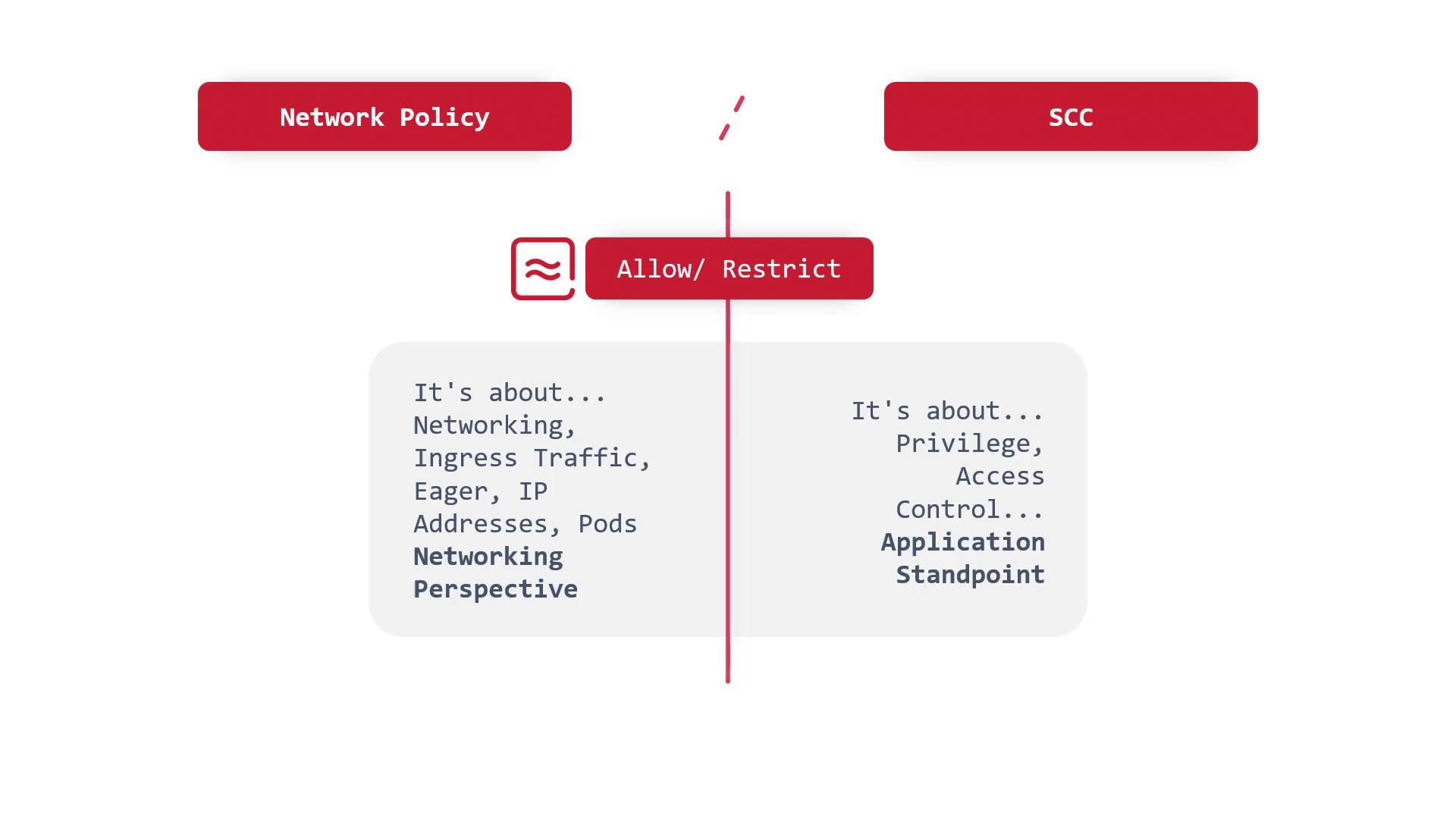
SCC vs. Network Policy
Both SCC and network policies are vital for Kubernetes security, yet they focus on different aspects:- Network Policies: These are designed to manage inbound and outbound traffic at the network level, considering factors like IP addresses, ports, and the OSI model. Their primary focus is regulating communication between pods and external entities.
- Security Context Constraints (SCC): These govern privileges and access control from an application and system perspective. SCC ensures that a pod operates within defined restrictions regarding system-level permissions and resources.
SCC and Open Policy Agent (OPA)
Although SCC is integrated into the Kubernetes system, there are similar tools such as Open Policy Agent (OPA) that extend security capabilities. OPA allows for advanced policy enforcement, but SCC serves as a strong first layer of defense, establishing fundamental access controls and aiding in early identification of security vulnerabilities.
Leveraging Linux Native Security Features
One practical approach to enhancing security is by using Linux native features such as AppArmor—a security module within the Linux kernel. AppArmor helps in restricting container access to resources by controlling file permissions and network access for specific applications. Note that AppArmor is specific to Linux environments, and its implementation may vary on Windows worker nodes.