User-controlled inputs in GitHub Actions workflows can introduce critical vulnerabilities. This article demonstrates how untrusted issue titles may allow an attacker to run arbitrary shell commands, enumerate workspace files, and exfiltrate secrets.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
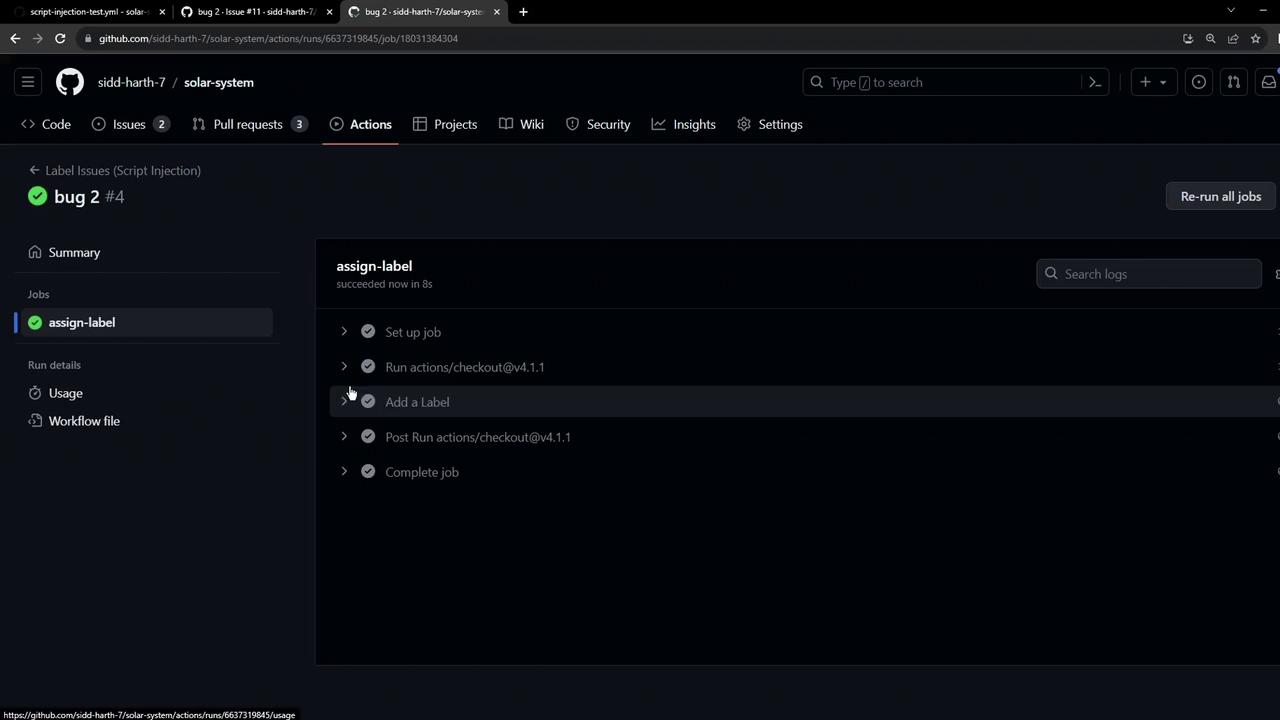
Example Workflow
The following workflow triggers on newly opened issues. It inspects the issue title for the keywordbug, echoes a message, and assigns a label. An AWS secret is loaded from repository secrets as an environment variable.
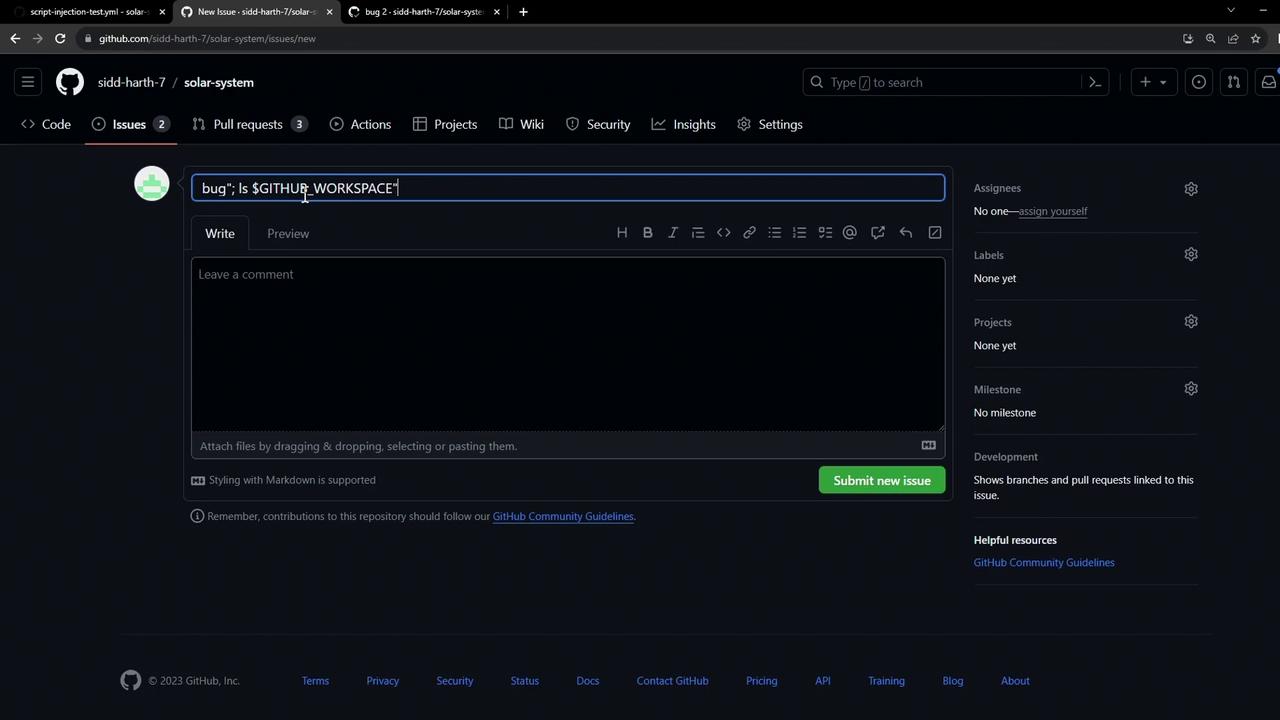
Demonstrating Script Injection
An attacker can craft an issue title that injects shell commands into therun step. For example:
ls command executes on the runner, revealing files:
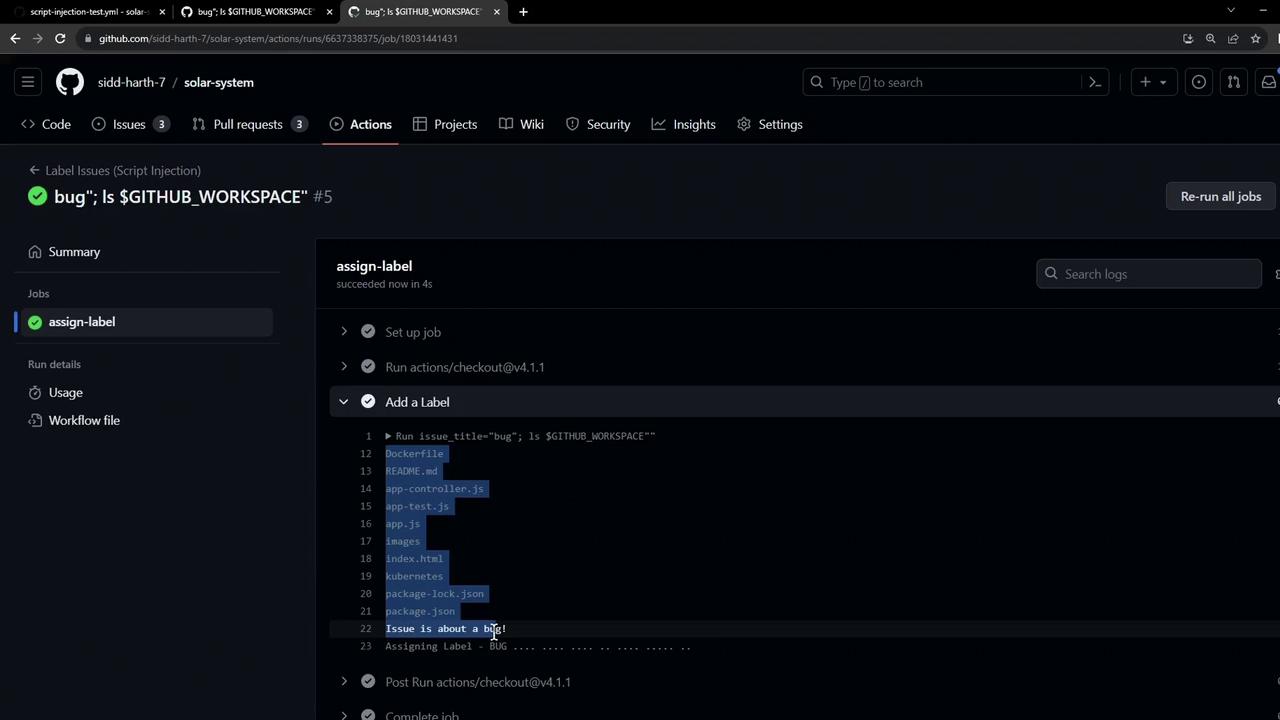
Exfiltrating Secrets
Beyond directory listing, an attacker can chain commands to leak secrets. The followingcurl command posts the AWS secret to a remote dump service:
Exposed
AWS_SECRET_ACCESS_KEY can be exploited to access AWS resources, incurring data breaches or infrastructure compromise.Risk Summary
| Risk Type | Impact | Example |
|---|---|---|
| Command Injection | Arbitrary code execution on runner | ls $GITHUB_WORKSPACE via issue title |
| Secret Exfiltration | Leakage of environment secrets | curl of $AWS_SECRET_ACCESS_KEY |
| Data Disclosure | Exposure of repository files | Listing workspace directory |
Mitigation Strategies
- Sanitize Inputs
Avoid direct interpolation of untrusted data. Use proper quoting: - Use Composite or JavaScript Actions
Isolate processing in actions that handle inputs without a shell. - Scope Secrets Minimally
Restrict secret access with job permissions. - Validate Patterns
Enforce regex or allowlists when matching user-supplied values. - Leverage Third-Party Utilities
Consider actions like nektos/act-sanitizer for automatic escaping.
For more guidance on securing workflows, see the GitHub Actions security hardening guide.