In this lesson you’ll provision an Amazon RDS (MariaDB) instance, capture the auto-generated master password shown during creation, and securely store that credential in AWS Secrets Manager so your applications can retrieve it at runtime. This pattern reduces secrets sprawl, enables automatic rotation, and follows least-privilege and auditable access to database credentials. What you will doDocumentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Create an RDS (MariaDB) instance and let RDS auto-generate a strong master password.
- Retrieve the generated password from the RDS creation banner (the password is displayed only once).
- Store the username/password pair in AWS Secrets Manager and link the secret to the RDS instance.
- Use example client code (Python and Java) that reads the secret before creating DB connections.
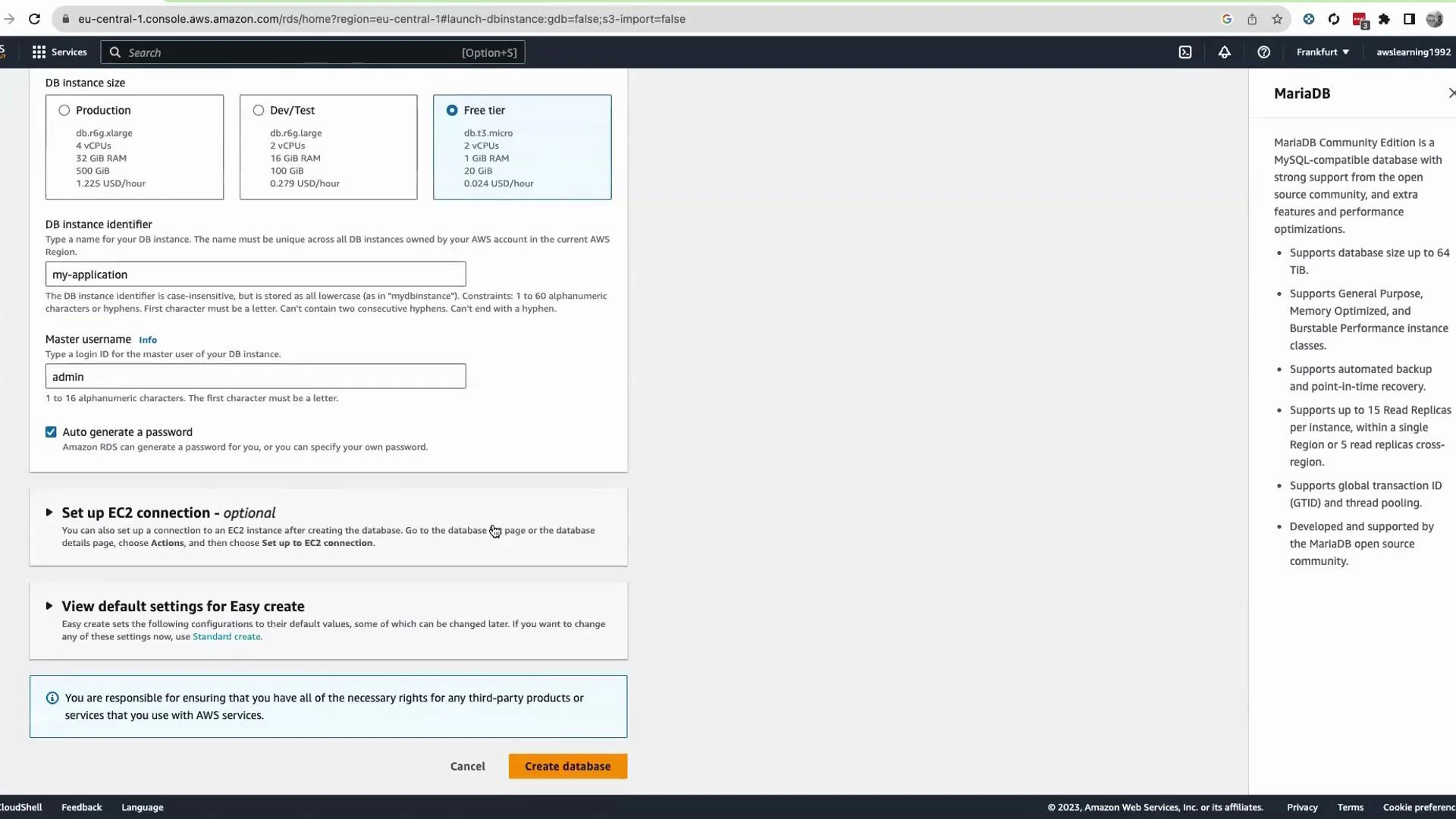
- Open the AWS Management Console and navigate to Amazon RDS.
- Choose “DB instances” → “Create DB instance”.
- For this demo select MariaDB and choose the Free tier (if eligible).
- Provide a DB instance identifier (for example, my-application) and a master username (for example, admin).
- Click “Auto-generate a password” to have RDS create a strong master password. Leave other defaults as appropriate for your environment.
- Click “Create database”.
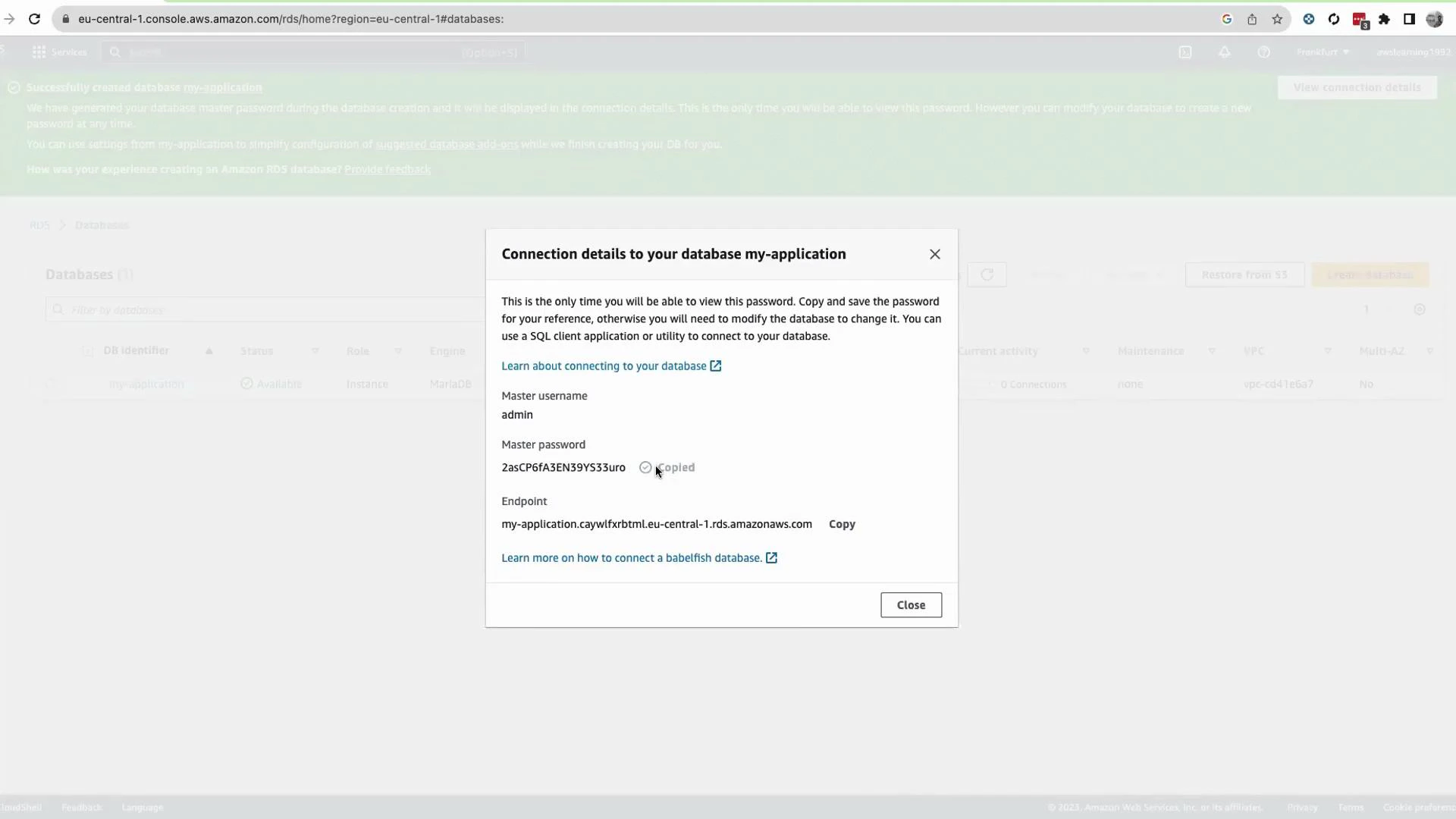
The auto-generated master password is shown only once in the RDS creation banner. If you close the banner without saving it elsewhere, the password cannot be retrieved — you would need to reset the master password.
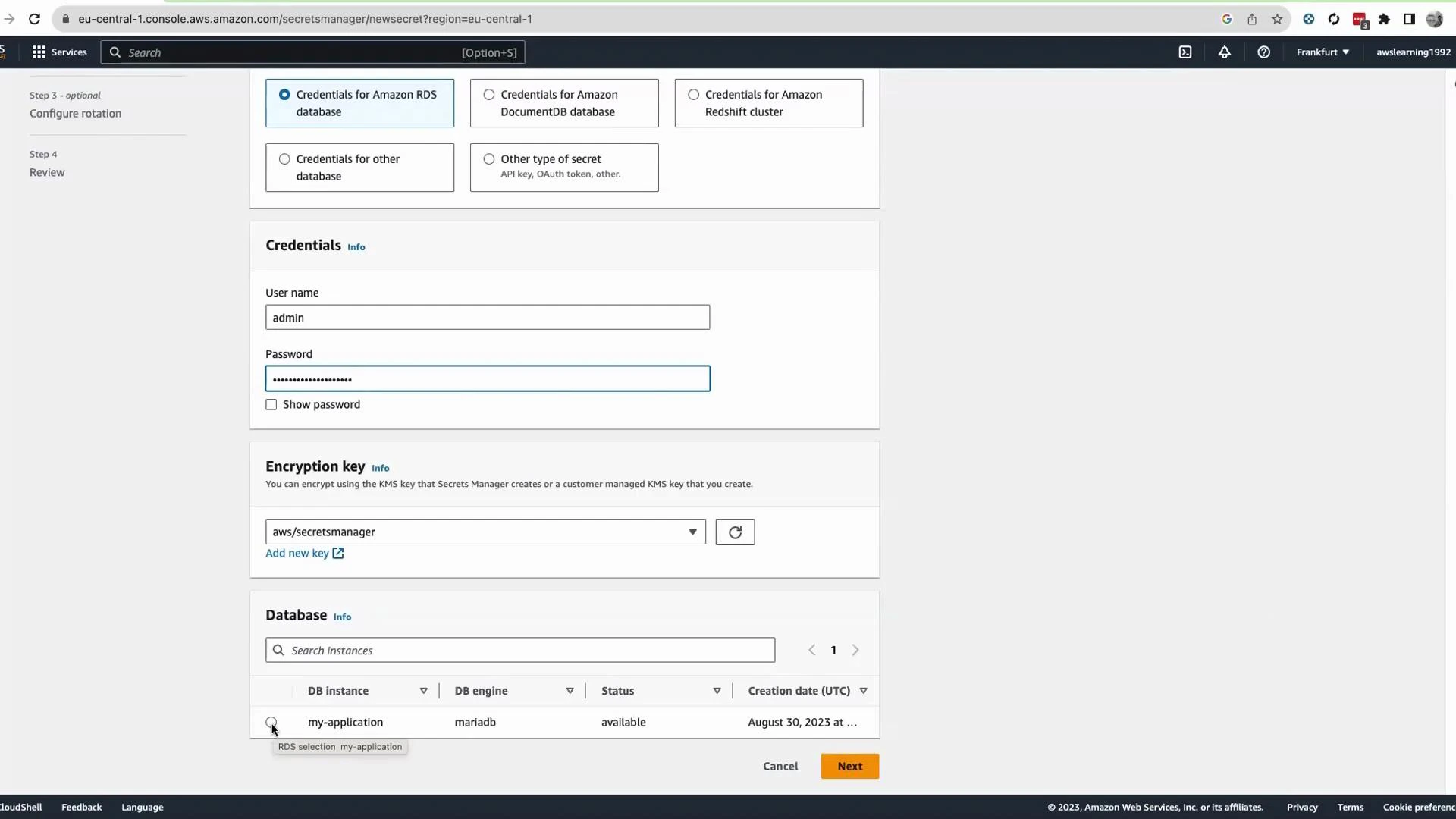
- In the AWS Console search bar open AWS Secrets Manager.
- Click “Store a new secret”.
- Choose the secret type: “Credentials for RDS database”.
- Enter the DB username (admin) and paste the master password you copied from the RDS banner.
- Keep the KMS encryption key as the default (aws/secretsmanager) unless you require a custom KMS key.
- Secrets Manager will list RDS instances available in the account/region — select the RDS instance you created (for example, my-application).
- Click “Next”.
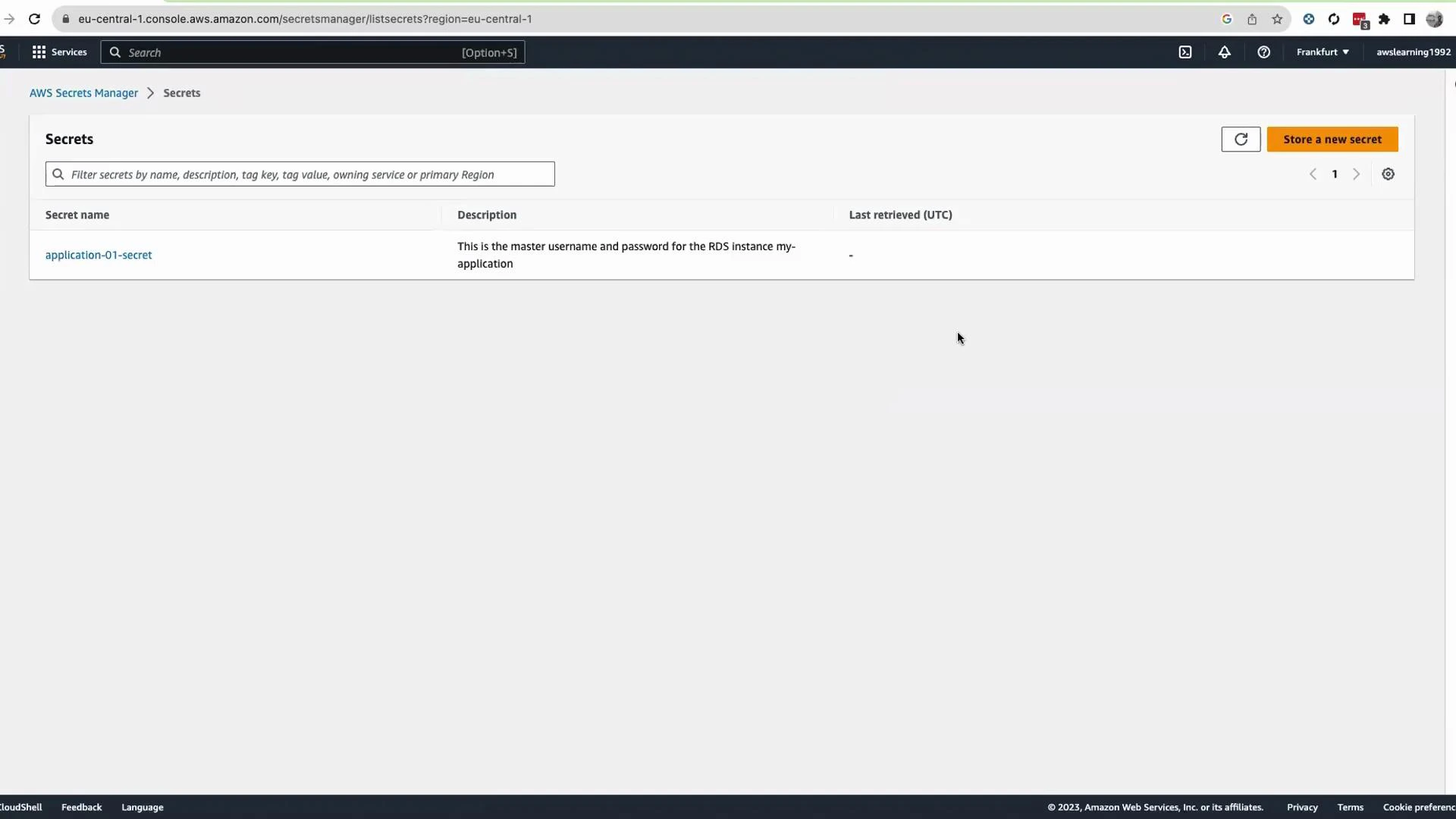
- Provide a secret name (for example, application-01-secret) and an optional description.
- Configure cross-region replication only if you need it; otherwise continue with “Next”.
- Click “Store” to persist the secret into Secrets Manager.
- Install boto3: pip install boto3
- Ensure the application’s IAM role or IAM user has permission to call GetSecretValue: https://docs.aws.amazon.com/secretsmanager/latest/apireference/API_GetSecretValue.html
- Ensure your build includes the AWS SDK v2 Secrets Manager module and that the app’s IAM identity has GetSecretValue permission.
- The method below returns the secret string; if it contains JSON, parse it into an object using your JSON library of choice.
| Topic | Recommendation | Reference |
|---|---|---|
| Retrieval timing | Fetch secrets at startup or immediately before DB connections to avoid long-lived secrets in memory | https://docs.aws.amazon.com/secretsmanager/latest/userguide/intro.html |
| Permissions | Grant minimal IAM permissions (GetSecretValue) to the application role; include kms:Decrypt if using a custom KMS key | https://docs.aws.amazon.com/secretsmanager/latest/apireference/API_GetSecretValue.html and https://docs.aws.amazon.com/kms/latest/developerguide/overview.html |
| Automatic rotation | Enable Secrets Manager rotation for supported engines to rotate and update DB credentials automatically | https://docs.aws.amazon.com/secretsmanager/latest/userguide/rotating-secrets.html |
| Secret format | Store RDS secrets as JSON (username, password, host, port) to simplify parsing in apps | Console samples and SDK examples |
AWS provides sample snippets for many languages in the Secrets Manager console. Use those samples as a starting point and adapt them to your application’s error handling, caching, and refresh strategy.
- Amazon RDS Documentation
- AWS Secrets Manager Documentation
- Secrets Manager API - GetSecretValue
- Secrets rotation with AWS Secrets Manager
- AWS KMS overview
- You provisioned a MariaDB instance in RDS and used the auto-generated master password.
- The auto-generated password is visible only once during creation; copy it immediately or store it in Secrets Manager.
- You stored the credential in AWS Secrets Manager and learned how to retrieve it from Python and Java applications, enabling secure, auditable access to DB credentials.
- Consider enabling automatic rotation and apply least-privilege IAM policies for production deployments.