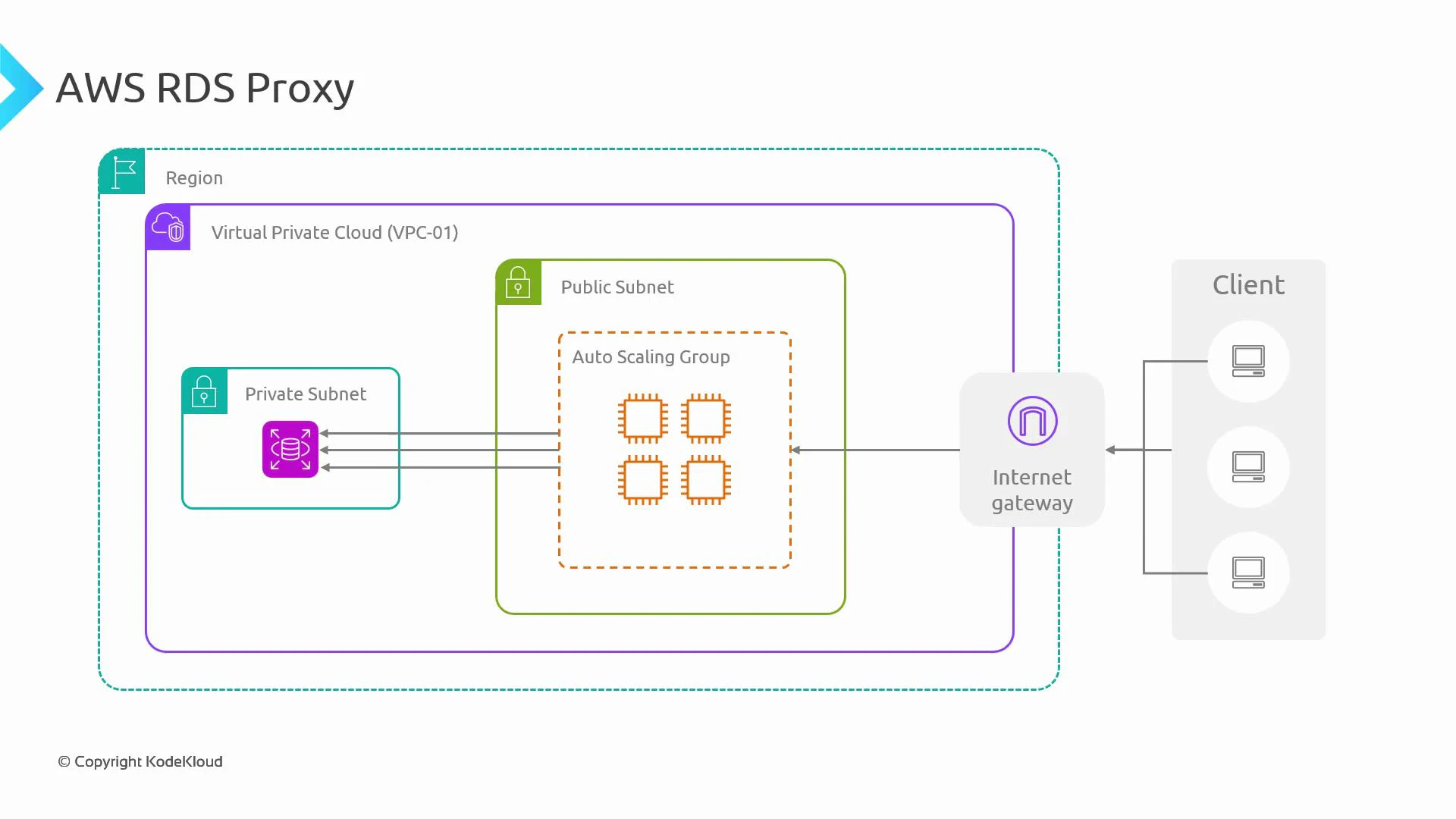
In this lesson we explain how AWS RDS Proxy improves networking, security, and reliability for your Amazon RDS and Aurora databases. You’ll learn where the proxy fits in a typical VPC architecture, how it reduces connection pressure on the database, how it helps during failovers, and how it centralizes authentication using IAM + Secrets Manager. Consider a typical architecture: a client accesses an application through an Internet Gateway. The application runs on EC2 instances in an Auto Scaling Group inside a public subnet. Currently the Auto Scaling Group has one instance that establishes a database connection. When the application scales out, multiple EC2 instances will each try to open connections to the database.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Databases enforce limits on concurrent connections and consume CPU/RAM to manage each connection.
- When many application instances open connections (or fail to close them), the database can hit connection limits and return errors such as “too many connections”.
- While application-level pooling, retries, and backoff help, they add complexity and are not always consistent across services (for example, serverless functions often open many short-lived connections).
- Connection pooling: reuse a smaller set of database connections across many clients.
- Failover resilience: the proxy can re-establish backend connections to a standby or new writer during database failover, preserving the client-facing endpoint.
- Centralized secrets and IAM enforcement: integration with AWS Secrets Manager and IAM DB authentication avoids embedding credentials in application code.
- Predictable throttling/queueing: the proxy can queue or throttle requests when pooled connections are not immediately available, smoothing spikes.
- Store and rotate credentials securely in Secrets Manager.
- Optionally enforce IAM-based authentication so applications use temporary auth tokens rather than long-lived passwords.
- Remove the need to hard-code credentials in application code or configuration files.
| Feature | Benefit | Use case |
|---|---|---|
| Connection pooling | Fewer backend DB connections, lower CPU/memory on DB | High-concurrency apps, serverless functions |
| Failover handling | Maintains stable client endpoint during writer failover | Multi-AZ / Aurora clusters |
| IAM + Secrets Manager integration | Centralized, rotated credentials and optional IAM auth | Security-first deployments, compliance needs |
| Queueing/throttling | Smooths spikes, prevents connection storms | Burst workloads, autoscaling fleets |
- Connect your application to the proxy endpoint the same way you connect to the DB endpoint (hostname, port, username). The proxy forwards queries to the pooled backend connections.
- For IAM authentication, generate an auth token and use it as the password (clients must connect using TLS).
- Use RDS Proxy for serverless or high-concurrency services to avoid connection storms.
- Keep client-side retries and exponential backoff; some in-flight requests may still fail during backend failover.
- Integrate RDS Proxy with Secrets Manager for automatic credential rotation and with IAM DB auth for short-lived credentials.
- Monitor proxy metrics (ConnectionsBorrowed, NewConnections, ConnectionPoolFullCount, etc.) using CloudWatch to tune pool size and behavior.
Use RDS Proxy for high-concurrency applications (including serverless workloads), to centralize secrets and IAM authentication, and to reduce the connection-management burden on your database. RDS Proxy supports Amazon RDS and Aurora engines for MySQL and PostgreSQL.
- Amazon RDS Proxy documentation
- AWS Secrets Manager
- IAM database authentication for MySQL and PostgreSQL on Amazon RDS