Welcome to the wrap-up of our DevSecOps pipeline. We have:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Secured the developer workstation with Talisman Git Hooks
- Run mutation tests, unit tests, and integration tests
- Performed static analysis (SAST) and dynamic analysis (DAST) using OWASP ZAP
- Scanned dependencies with Dependency Check and Trivy
- Validated manifests via OPA Conftest and Kubesec
- Configured automatic rollbacks in Kubernetes deployments
- Sent build notifications to Slack for real-time visibility
Below is a quick overview of the tools and their purposes:
| Security Measure | Tool | Purpose |
|---|---|---|
| Git pre-commit Hook | Talisman | Prevents accidental secrets or high-risk files |
| Static Application Security | SAST | Detects code vulnerabilities early |
| Dynamic Application Security | DAST (OWASP ZAP) | Scans running applications for flaws |
| Dependency Scanning | Dependency Check, Trivy | Identifies vulnerable or outdated libraries |
| Policy as Code | OPA Conftest | Ensures infrastructure policies compliance |
| Manifest Linting | Kubesec | Validates Kubernetes manifest best practices |
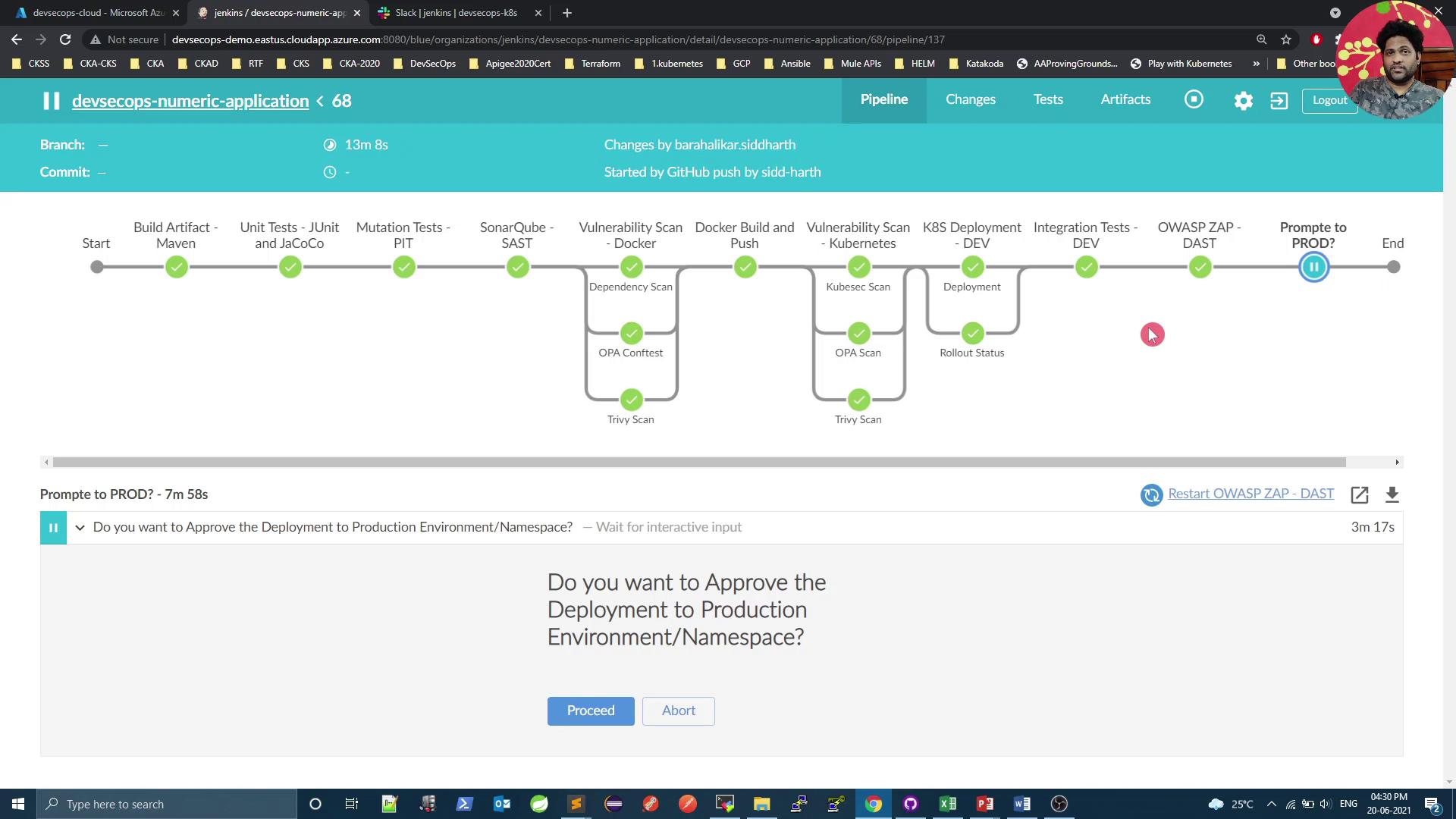
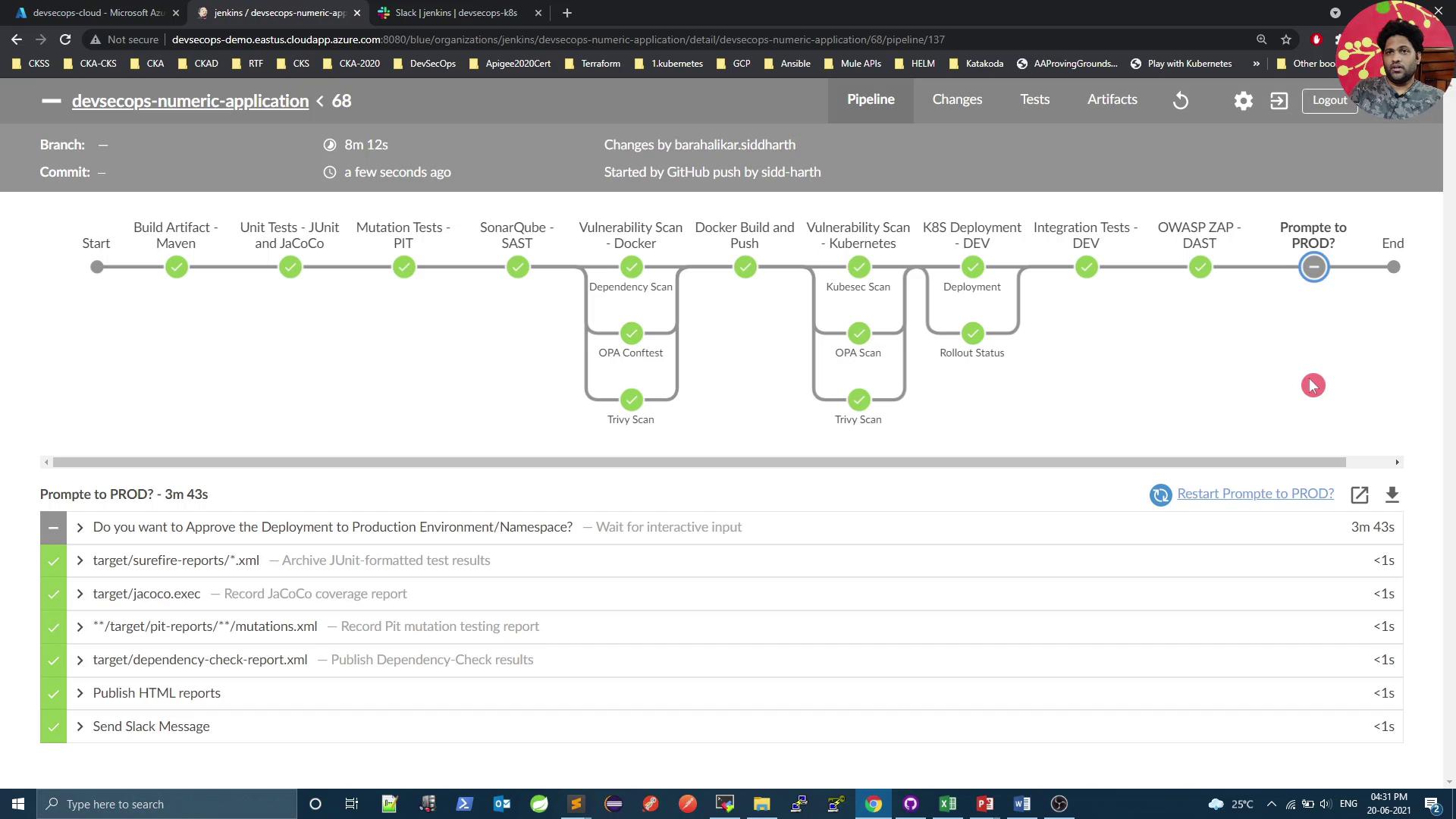
Adding a Manual Approval Stage
To ensure an architect or manager authorizes production deployments, we introduce a Promote to PROD stage with a two-day timeout. The snippet below shows how to integrate this into yourJenkinsfile:
The pipeline will pause at the Promote to PROD stage until an approver selects Proceed or Abort. Aborting will stop the pipeline and notify the team via Slack.