In this lesson, we’ll explore Static Application Security Testing (SAST), also known as static analysis. SAST examines your source code to identify security vulnerabilities before runtime, scanning the application code and reporting potential issues. By contrast, Dynamic Application Security Testing (DAST) runs tests against a deployed application. For our SAST examples, we’ll use SonarQube.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Why SonarQube for SAST?
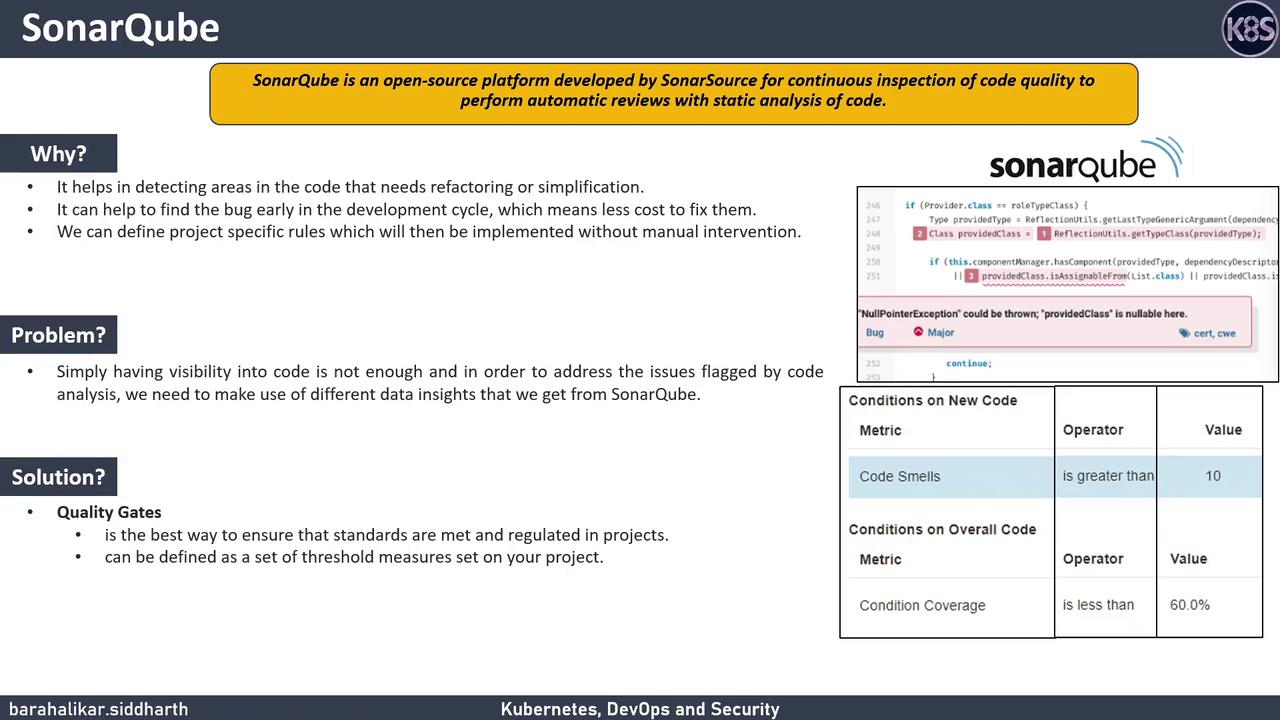
SonarQube is an open-source platform by SonarSource that performs continuous inspection of code quality through automatic static analysis. It gives you visibility into your code by pinpointing specific lines where issues occur and offering remediation guidance. You can also enforce quality gates—thresholds on code metrics—to ensure that every commit meets your organization’s standards.| Feature | Benefit |
|---|---|
| Code Smells Detection | Identify code areas that need refactoring or simplification |
| Early Bug Discovery | Catch bugs during development to reduce fix costs |
| Quality Gates Enforcement | Prevent merges until code meets defined metrics |
Defining Quality Gates
With quality gates, you can set conditions such as:- Number of code smells
- Number of security hotspots
- Code coverage percentage
Installing SonarQube with Docker
A quick way to get SonarQube up and running is via the official Docker image. Run:The environment variable
SONAR_ES_BOOTSTRAP_CHECKS_DISABLE=true disables Elasticsearch bootstrap checks for development environments. Do not use this in production.http://<your-host>:9000. The default credentials are admin/admin.