In this lesson you’ll register an Argo Events EventSource that listens for MinIO bucket notifications. Argo Events receives events in a CloudEvents-style JSON envelope; a simplified example looks like:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
argo-events namespace.
Prerequisites & connectivity
Ensure the following before creating the EventSource:| Requirement | Purpose | Example / Notes |
|---|---|---|
| Reachable MinIO API | Argo Events must connect to MinIO (default port 9000) | Service endpoint like minio.argo.svc.cluster.local:9000 |
| Kubernetes Secret with MinIO creds | EventSource reads credentials from a secret in argo-events | minio-creds containing accesskey and secretkey |
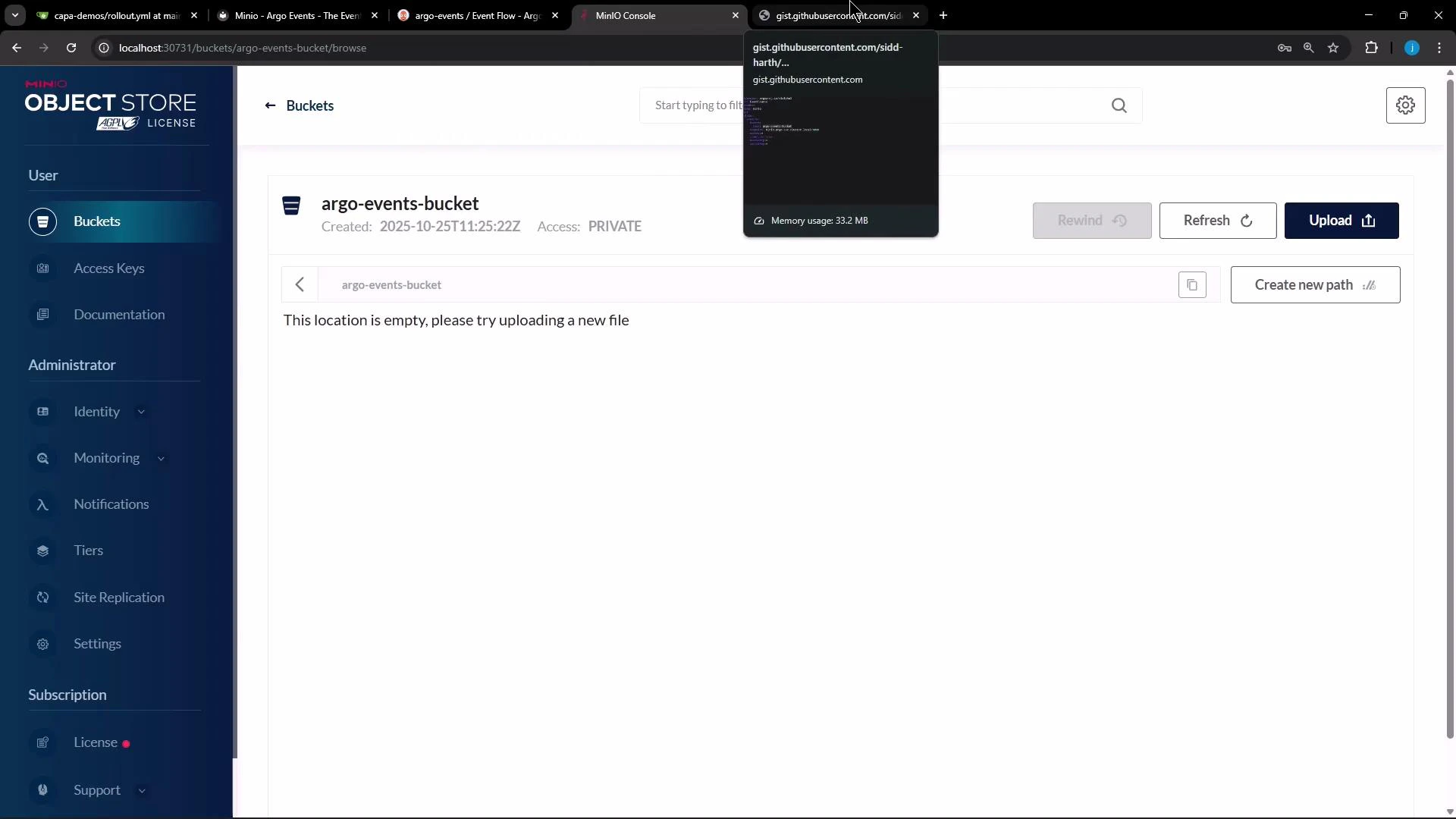
| Bucket to watch | The bucket that will emit notifications | argo-events-bucket |
If your cluster’s DNS or service discovery differs, adjust the endpoint to the correct FQDN or ClusterIP:port. Confirm the MinIO API is accessible from the
argo-events namespace.Port-forward locally and set up the MinIO client (optional)
If you prefer to configure the bucket from your workstation using the MinIO client (mc), port-forward the MinIO service and configure an alias:
Create the Kubernetes Secret for MinIO credentials
Create a secret in theargo-events namespace so the EventSource can authenticate to MinIO. The simplest method is using kubectl:
Do not commit plain-text credentials to repositories. Use sealed secrets, HashiCorp Vault, or another secret management solution for production. Ensure RBAC limits who can read the
minio-creds secret.EventSource manifest: MinIO listener
Below is a working EventSource YAML that registers a MinIO event source namedminio with a configuration called example. It watches the argo-events-bucket bucket for object creation and deletion events, points at an in-cluster MinIO endpoint, and pulls credentials from the minio-creds secret.
eventsource-minio.yaml (or a suitable name) and apply it:
Test behavior and troubleshooting
- Upload or remove an object in
argo-events-bucket. The MinIO server will emit a notification; Argo Events should receive it and generate a CloudEvent payload like the JSON example above. - Check EventSource logs to verify connection and event receipt:
- If you see authentication errors, re-check the secret keys and the MinIO endpoint and port.
Next steps
- Create an Argo Events Sensor that subscribes to the
minioEventSource and triggers an Argo Workflow, HTTP call, or other consumer when notifications arrive. - Validate end-to-end by uploading/deleting objects and observing Sensor-triggered actions.
- Consider configuring retry/backoff and dead-lettering for production workflows.
Ensure the endpoint (service name, namespace, and port) is correct for your cluster (for example: minio.argo.svc.cluster.local:9000). Also make sure the credentials in the
minio-creds secret match the MinIO server credentials.Links and references
- Argo Events documentation: https://argoproj.github.io/argo-events/
- MinIO documentation: https://min.io/docs/
- Kubernetes documentation: https://kubernetes.io/docs/
- MinIO client (mc): https://min.io/docs/minio/linux/reference/minio-mc.html