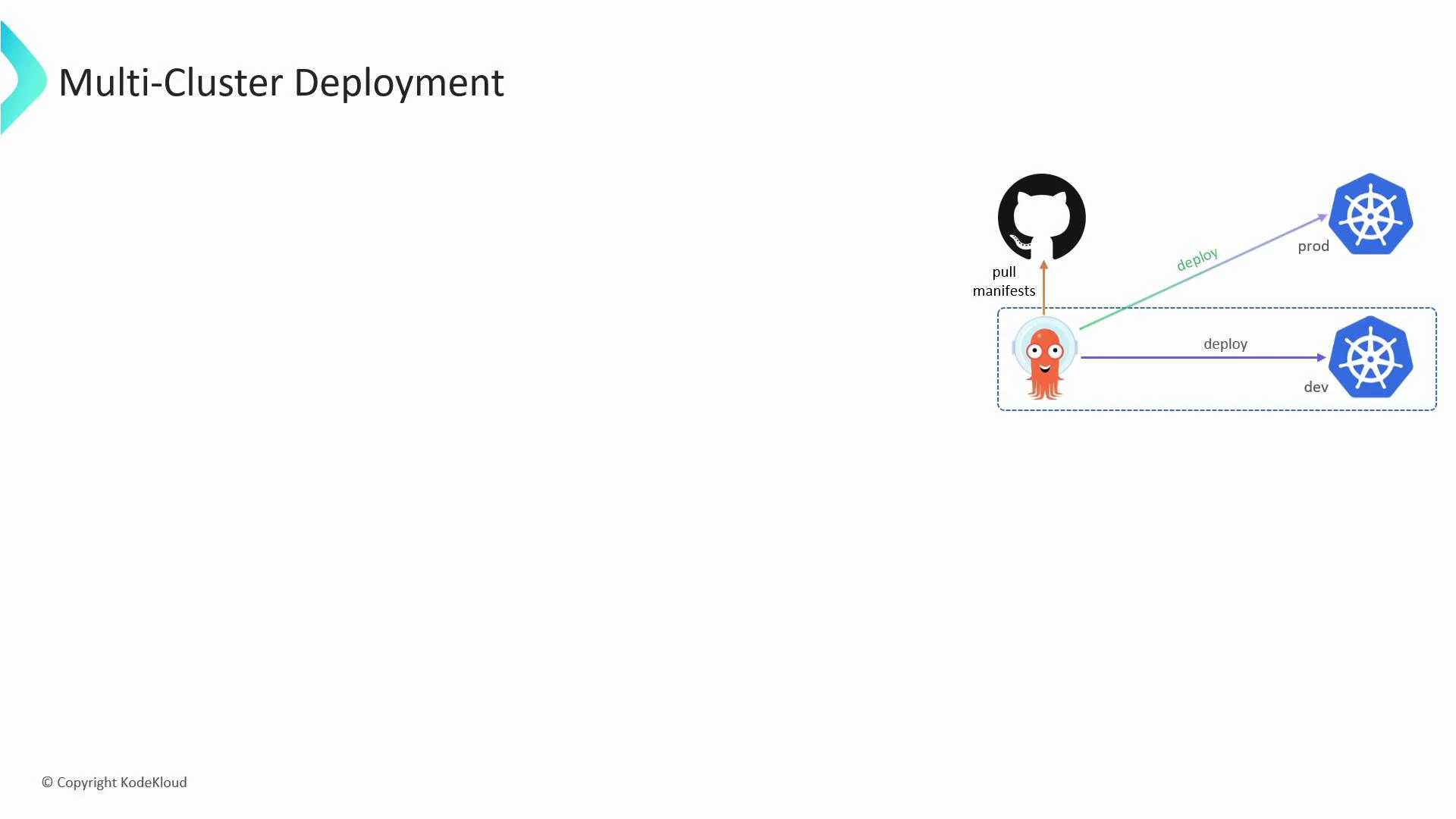
Learn how Argo CD can manage applications across multiple Kubernetes clusters — not just the cluster where Argo CD itself runs. This guide shows the recommended sequence: prepare your kubeconfig, register the external cluster with Argo CD, and verify that the cluster is available as a deployment destination. Argo CD supports multi-cluster deployments by storing external cluster credentials in its own namespace and using a dedicated service account on each external cluster to apply manifests.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview — steps to add an external cluster
- Add the external cluster details (server, certificates, user credentials, context) to your local kubeconfig.
- Use the argocd CLI to register that kubeconfig context with Argo CD (
argocd cluster add). - Confirm Argo CD created the required ServiceAccount, ClusterRole, and ClusterRoleBinding on the target cluster.
- Verify the cluster appears in Argo CD’s cluster list and inspect the stored secret if needed.
Before running the commands below, ensure you have access to the target cluster API endpoint and appropriate client certificates or tokens. You can also use cloud provider IAM auth (e.g., EKS, GKE) depending on your environment.
Example commands
Add the cluster server, user credentials, and context into kubeconfig:Output:
When you run
argocd cluster add, Argo CD will create an argocd-manager ServiceAccount with cluster-admin level permissions by default. Limit access and scope where possible — for production, prefer restricting RBAC to the minimum required privileges.Quick reference — commands and purpose
| Command | Purpose | Notes |
|---|---|---|
kubectl config set-cluster | Add cluster endpoint & CA to kubeconfig | Provide the API server URL and CA cert |
kubectl config set-credentials | Add user credentials (cert/key or token) | Use client certs or bearer token |
kubectl config set-context | Create a kubeconfig context for the cluster | Include namespace if you want a default namespace |
argocd cluster add <context> | Register the kubeconfig context with Argo CD | Creates ServiceAccount, ClusterRole, ClusterRoleBinding on target cluster |
argocd cluster list | List clusters registered in Argo CD | Shows status and server URL |
kubectl describe secret <name> -n argocd | Inspect stored cluster credentials | Secrets store the kubeconfig/config data |
Verification and troubleshooting
- Use
argocd cluster listto confirm the cluster status shows Successful. - If a cluster shows errors, check the target cluster’s kube-apiserver reachability, certificate validity, and whether the created ServiceAccount/RBAC objects exist in the target cluster’s
kube-systemnamespace. - Inspect Argo CD logs for errors:
kubectl -n argocd logs deploy/argocd-serveror check the repo-server and application-controller logs for sync problems.
Links and references
- Argo CD documentation — multi-cluster setup
- Kubernetes kubeconfig documentation
- kubectl config command reference
- Kubernetes ServiceAccount concept
- Kubernetes Secrets