This guide shows how to configure Git webhooks so Argo CD receives repository change notifications immediately instead of waiting for the default three-minute poll. With webhooks configured, Argo CD can detect and apply manifest changes as soon as you push them, enabling true GitOps continuous delivery. Key topics covered:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Webhook endpoint for Argo CD
- Example repository manifest
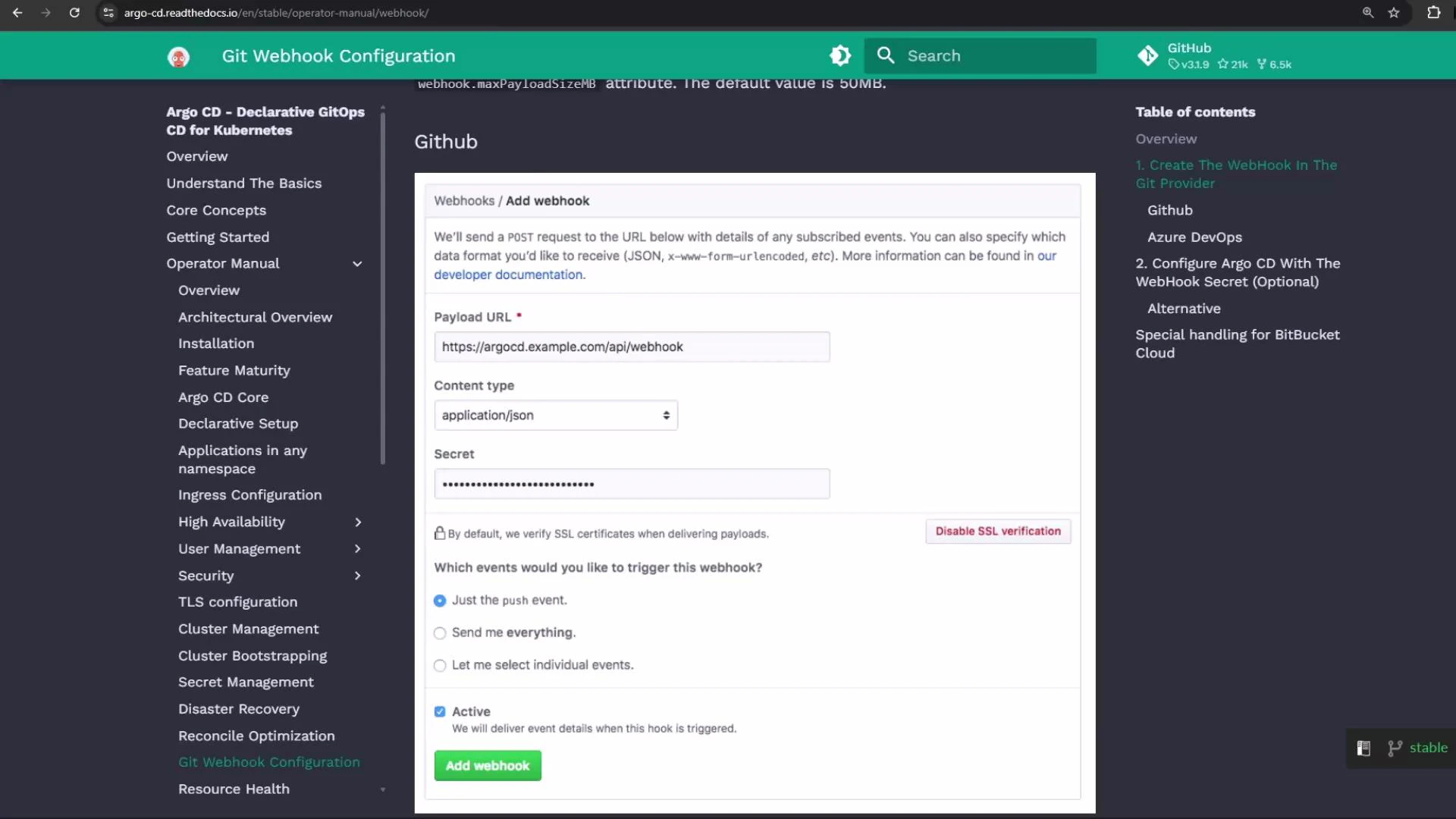
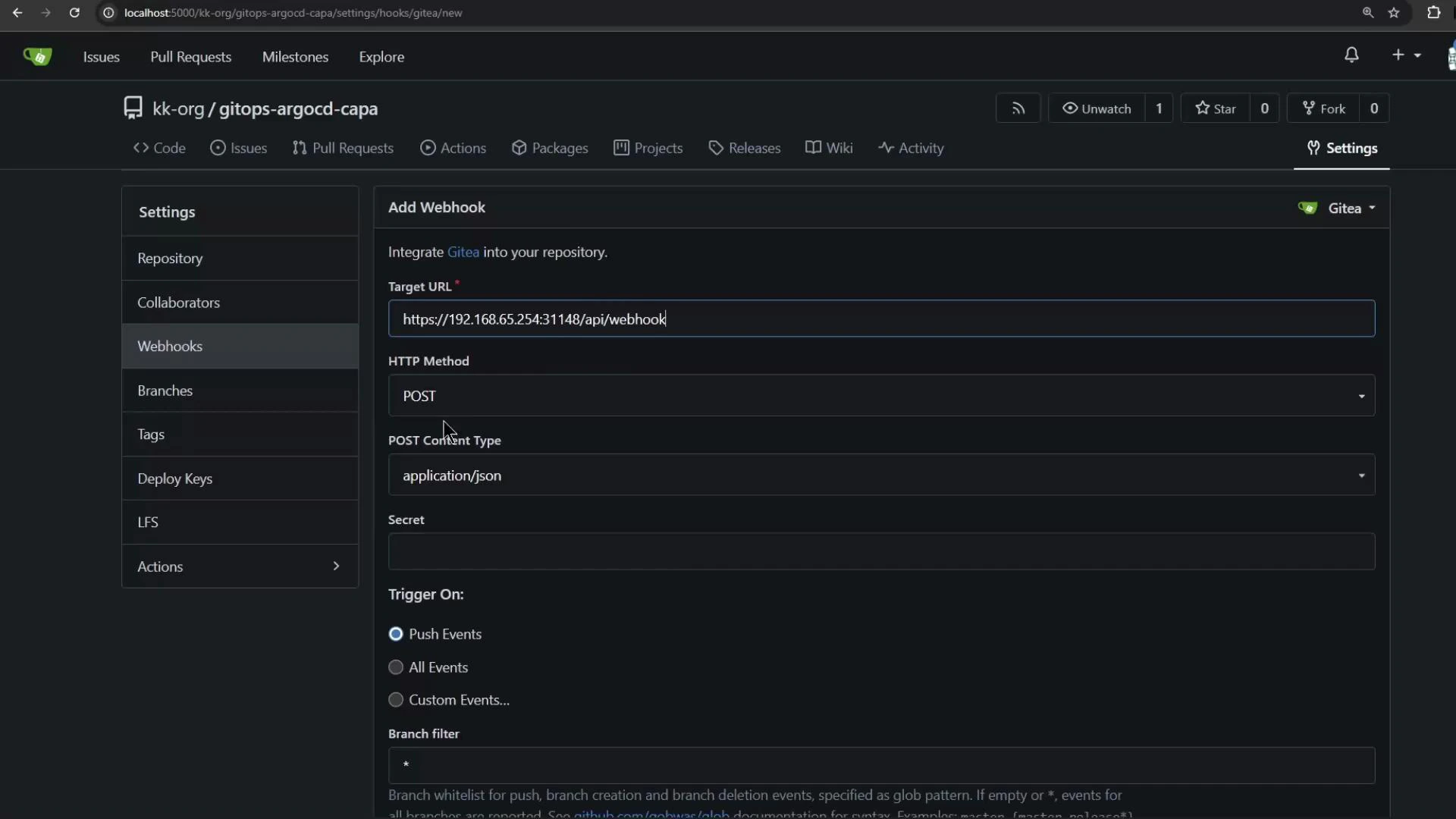
- Adding the webhook in your Git provider
- Troubleshooting TLS / self-signed certificates
- Running Argo CD in insecure mode for testing
- Validating the webhook workflow in the Argo CD UI
This guide assumes you have Argo CD installed and an application configured to track your Git repository. For Argo CD installation and basic app creation, see the official Argo CD docs: Argo CD Documentation.
- The webhook endpoint for Argo CD accepts POST events at /api/webhook on the Argo CD server. Example forms of the endpoint:
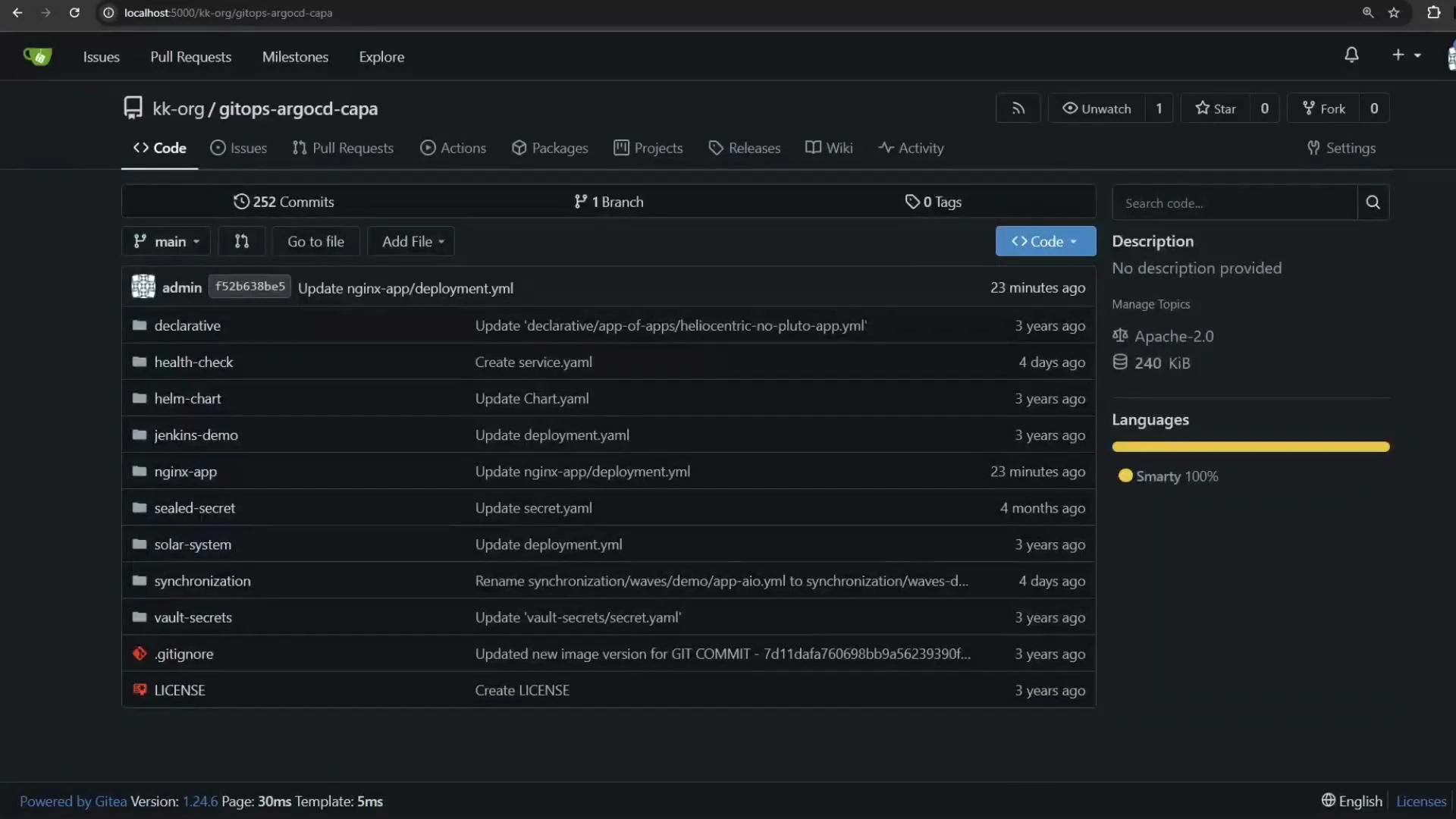
- In this example we have a GitOps repository containing an Nginx Deployment manifest. The goal is for Argo CD to update the cluster whenever this file changes.
| Setting | Value / Recommendation |
|---|---|
| Payload URL | https://<argocd-host>/api/webhook |
| HTTP method | POST |
| Content type | application/json |
| Events | Push events (or custom events that include push) |
| Secret | Optional — set and configure Argo CD if you use a secret token |
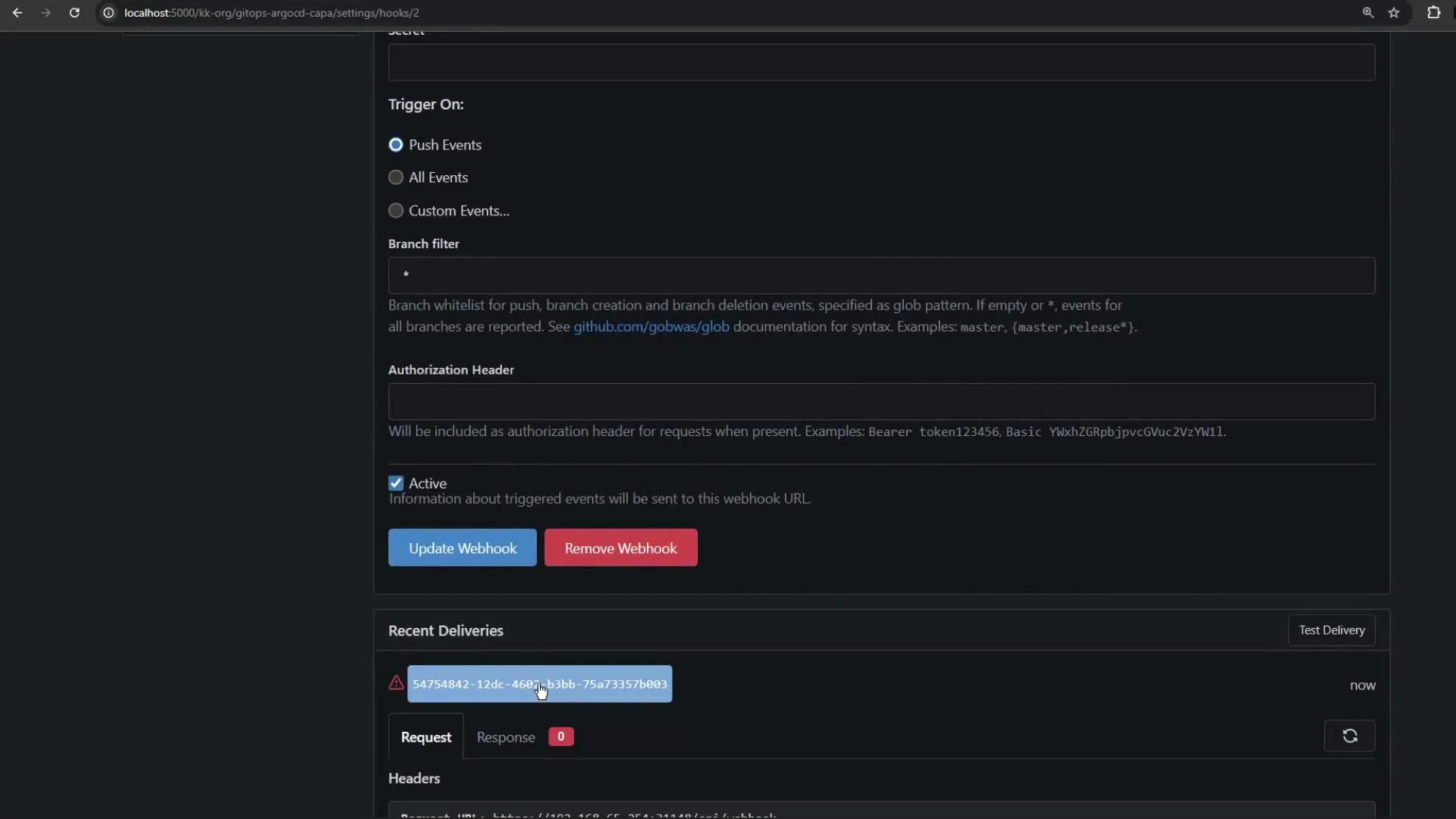
- If Argo CD is served over HTTPS with a self-signed certificate, Git providers may reject webhook delivery because the certificate is not trusted. A common delivery error looks like:
- Provision a valid TLS certificate signed by a trusted CA and use that on the Argo CD server.
- Configure your Git provider to trust your test CA (if supported).
- For demo or local testing only, run Argo CD in insecure (HTTP) mode so webhooks can be delivered without TLS verification. Do not use insecure mode in production.
- Edit the ConfigMap used by Argo CD command parameters (example: argocd-cmd-params-cm in the argocd namespace) and add the
server.insecurekey set to “true”. This configures the Argo CD server to run in insecure HTTP mode for testing.
- Save the ConfigMap and restart the Argo CD server deployment so the change takes effect:
- Verify pods are running:
Enabling server.insecure: “true” disables TLS on the Argo CD server and allows webhook delivery over plain HTTP. This is strictly for demo or test environments. For production, always provision TLS certificates from a trusted CA or configure your Git provider to trust your certificate authority.
- After setting
server.insecure: "true"and restarting the server, update the webhook URL in your Git provider to use http:// instead of https:// so the provider posts to the insecure test endpoint. Re-trigger the webhook delivery and check for a successful response (HTTP 200/201 or other success code).
- Open the Argo CD UI and view your application (for example, an application named nginx-app-1). Before changes, the application should show Healthy and Synced when there are no pending updates.
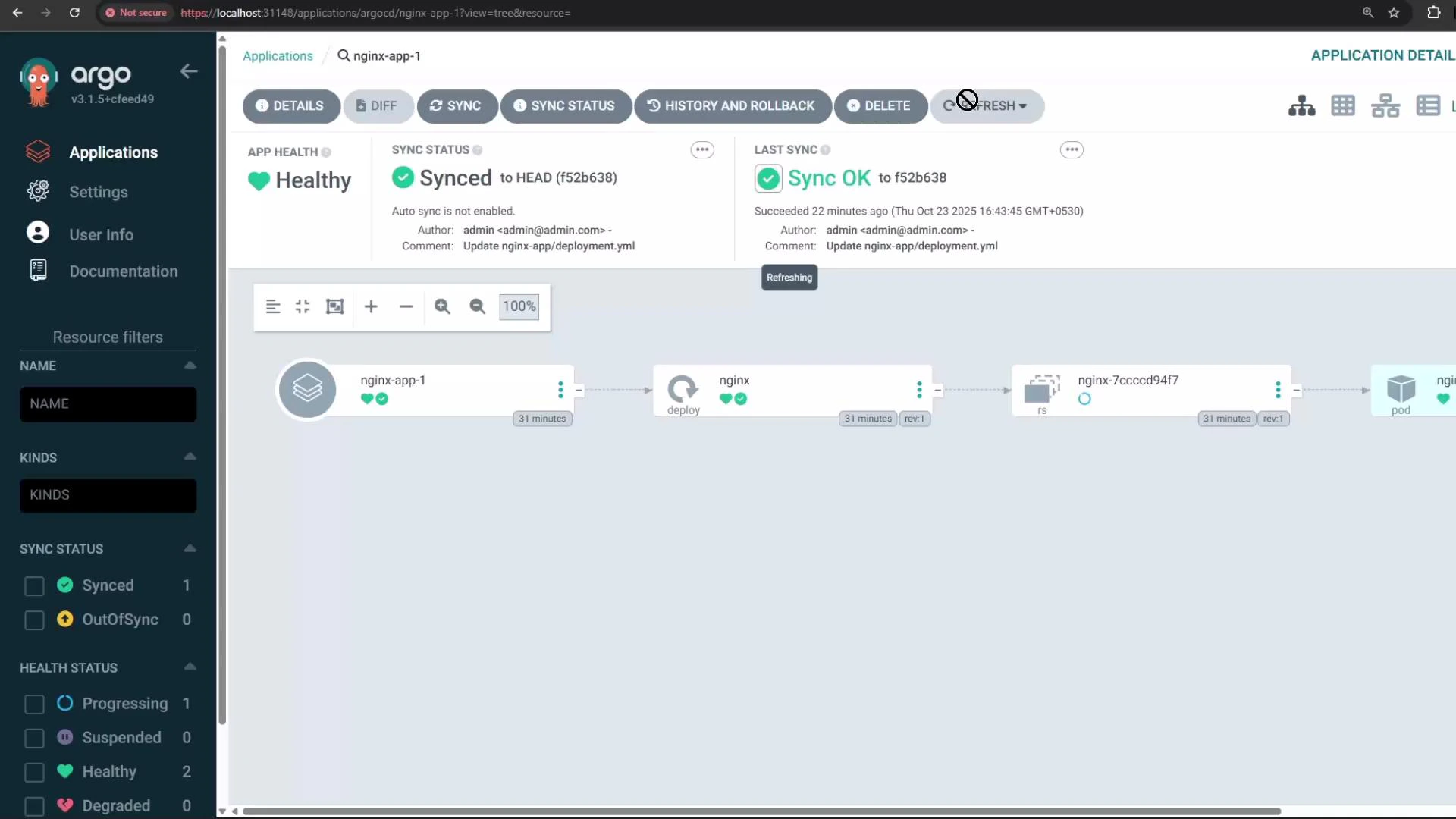
- The webhook payload contains commit metadata and the list of modified files. Argo CD uses this to refresh the repository and detect changed manifests.
- Argo CD immediately detects the change from the webhook and refreshes the repository.
- If auto-sync is enabled for the application, Argo CD will apply the updated manifest automatically. Otherwise, you can sync manually from the UI or CLI.
- Occasionally you may need to refresh the Argo CD UI or re-login to see updated statuses.