Sync Hooks let you control the order and lifecycle of Kubernetes resources ArgoCD creates during an application sync. Instead of lettingDocumentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
kubectl apply (or ArgoCD’s default sync) create everything at once—potentially starting your app before its database or ConfigMap exist—you annotate specific resources in your manifests so ArgoCD runs them at well-defined moments in the sync lifecycle.
Use cases for Sync Hooks:
- Run database migrations before deploying the application.
- Create or restore backups prior to changes.
- Run integration tests or notify systems after a successful deployment.
- Clean up temporary resources after syncs.
Sync hooks are defined with annotations in your Kubernetes manifests (for example,
argocd.argoproj.io/hook: PreSync). ArgoCD will create the hook resource (a Job, Pod, etc.) and wait for its completion where applicable, before proceeding to the next phase.Sync phases
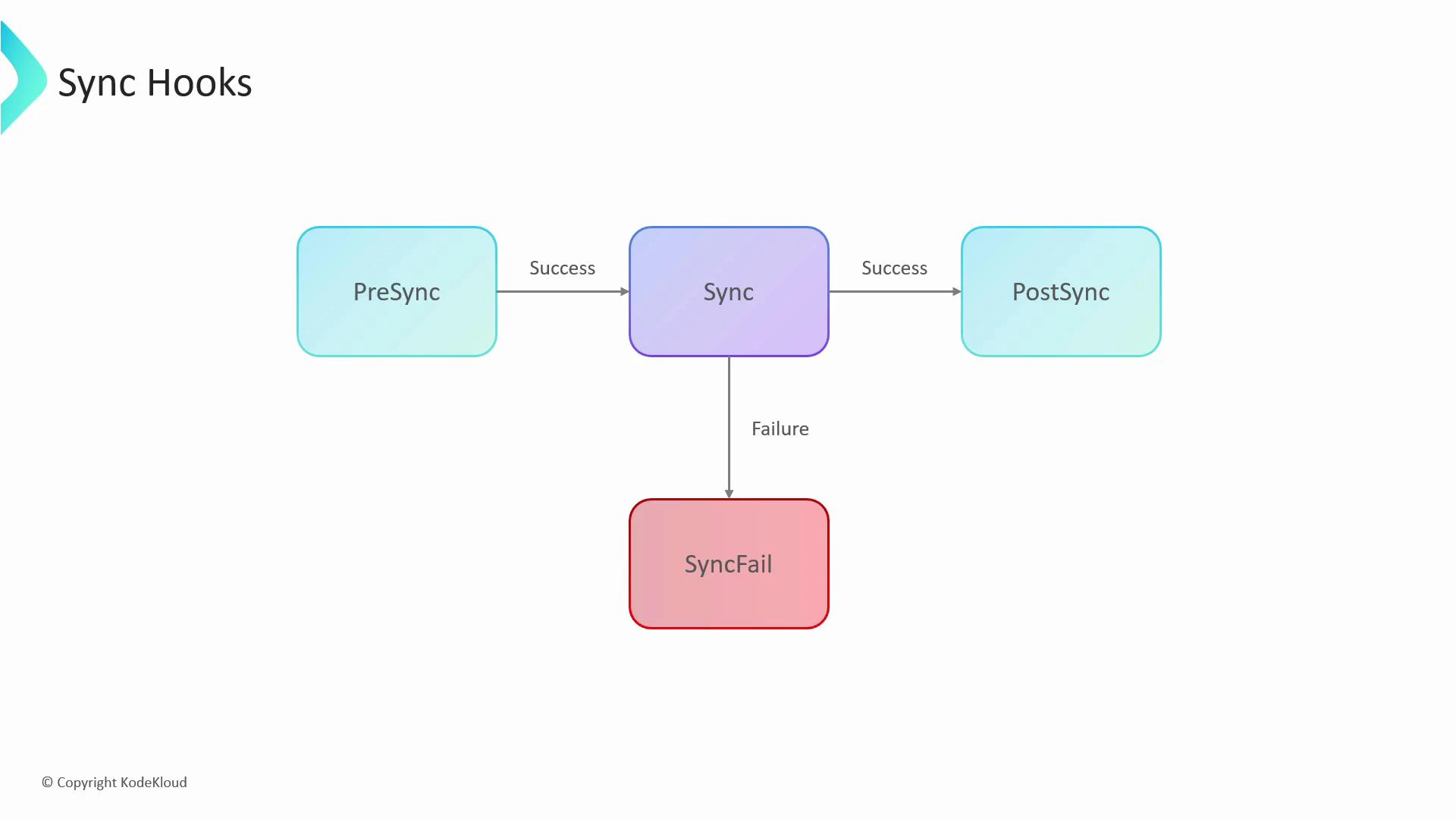
ArgoCD processes hooks in these primary phases:| Phase | When it runs | Typical use cases |
|---|---|---|
| PreSync | Before the main sync is applied | db migrations, secrets creation, backups |
| Sync (default) | Apply main resources (Deployments, Services, ConfigMaps, etc.) | Primary application rollout; ArgoCD waits for health checks |
| PostSync | After main sync succeeds and resources are healthy | Integration tests, notifications, cleanup tasks |
| SyncFail | Triggered when main sync fails | Rollbacks, notifications, remedial tasks |
Example: run DB migration before deployment
Imagine these files in your repo:db-migration to run first (and succeed) before ArgoCD creates the my-app Deployment. Annotate the migration Job with argocd.argoproj.io/hook: PreSync. ArgoCD will:
- Create the Job and wait for it to finish successfully.
- If the Job succeeds, proceed to apply the main resources (Deployment, Service), waiting for them to become healthy.
- After the main sync completes and resources are healthy, run any PostSync hooks.
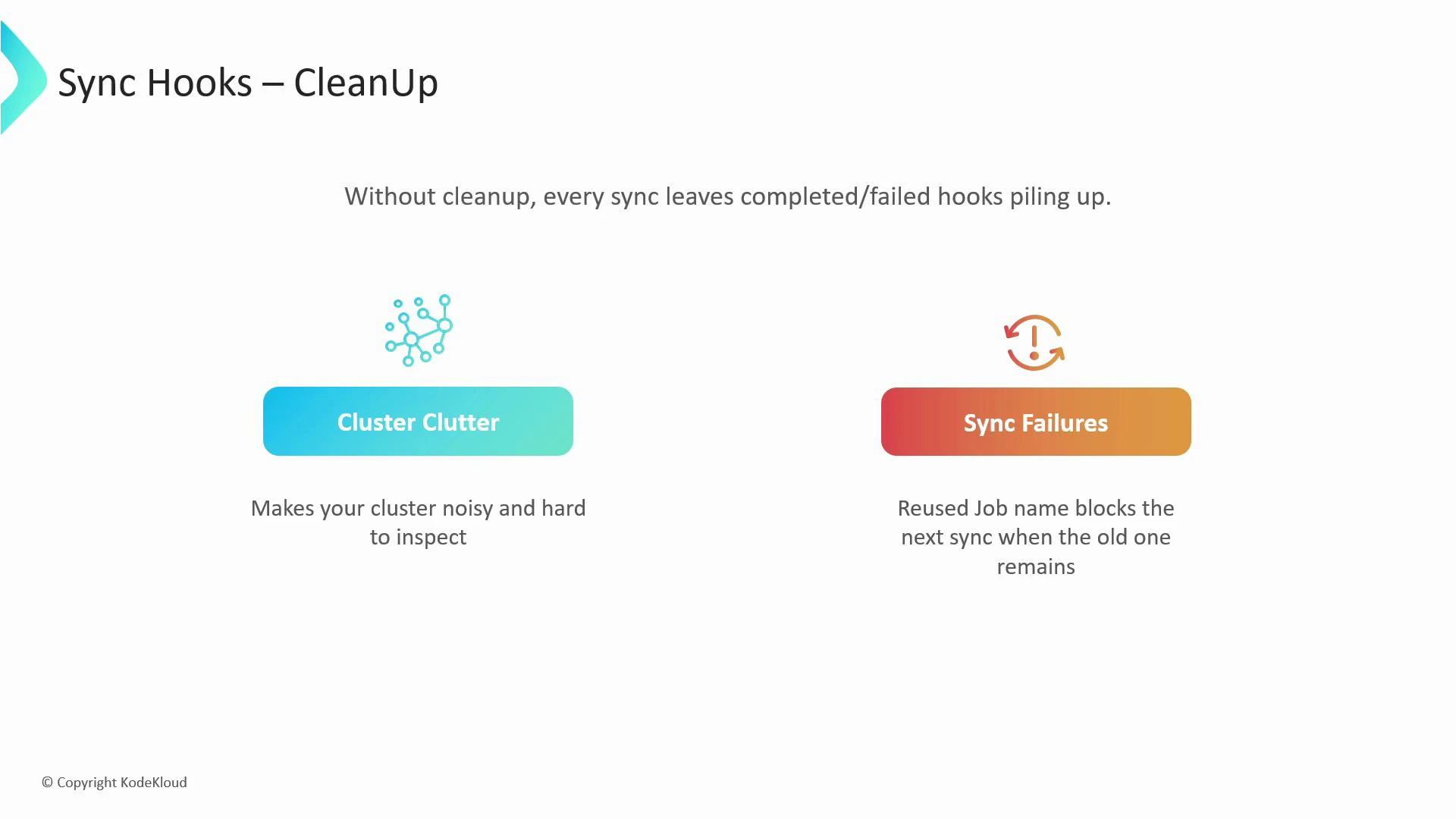
Hooks create real Kubernetes resources (Jobs, Pods, etc.). Without a cleanup strategy, completed or failed hook resources accumulate in the cluster and can cause:
- Cluster clutter — harder to inspect and manage.
- Sync failures — a future sync may fail if it attempts to create a resource with the same name as an existing completed hook.
Cleaning up hook resources: hook-delete-policy
ArgoCD provides theargocd.argoproj.io/hook-delete-policy annotation to automatically remove hook resources according to chosen policies. Two practical policies:
| Policy | Behavior | Typical reason |
|---|---|---|
| HookSucceeded | Delete the hook resource only if it completed successfully | Keep cluster clean while preserving failed runs for debugging |
| HookFailed | Delete the hook resource only if it failed | Keep successful runs as audit evidence; discard failed ones |
- The
db-migrationjob will be deleted after a successful run (keeps the cluster tidy). - The
clean-upjob will be retained if it succeeded, or deleted if it failed (useful if you want success records kept for auditing).
Quick best practices
- Use unique names when necessary, or apply delete policies to avoid collisions.
- Keep prolonged-running hook Jobs to a minimum; they block the sync progress until completion.
- Use PreSync for anything that must exist before the main app; use PostSync for tasks that depend on the full app being healthy.
- Retain failed hook resources (default HookSucceeded behavior) to help with debugging.