In this lesson, you’ll learn how to encrypt large files using AWS KMS envelope encryption. By leveraging envelope encryption, AWS KMS generates a data key from a primary KMS key that encrypts files of any size. Although we will use a sample file named “db-creds,” the same steps apply to larger files.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
Generating a Data Key
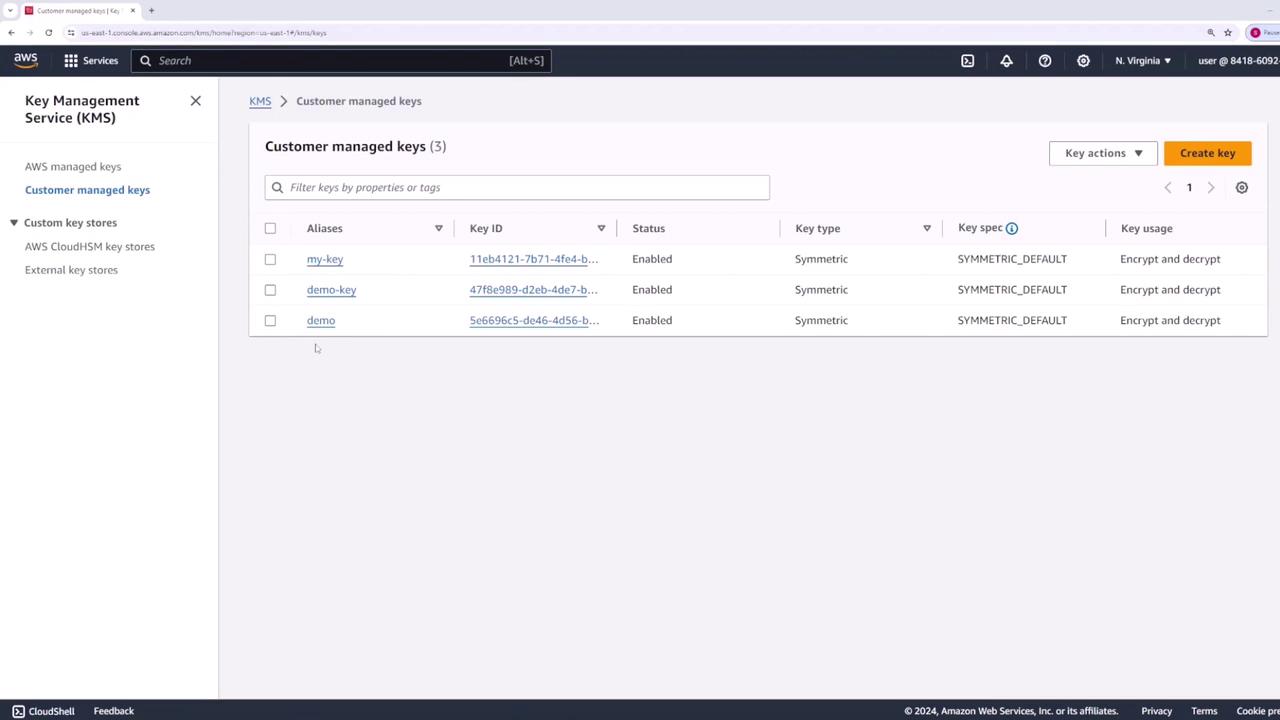
A KMS key (for example, one named “demo”) can directly encrypt or decrypt data up to 4 KB. To handle larger files, we generate a data key through our KMS key. This data key is provided in two forms:- The plaintext key, used by OpenSSL for file encryption.
- The encrypted key, stored securely for later decryption.
Encrypting Data
With your plaintext data key ready, use it to encrypt the “db-creds” file with OpenSSL. Execute the following command:- OpenSSL employs the AES-256 cipher.
- The encryption key is read from the provided plaintext key file.
- The
-pbkdf2flag ensures a secure key derivation and prevents warnings.
Removing the plaintext key from disk prevents it from being compromised, ensuring the security of your encrypted data.
Decrypting Data
To decrypt the encrypted data file later, follow these steps:-
Decrypt the Encrypted Key Using AWS KMS
Run the command below to decrypt the stored encrypted key:
The output will resemble:
-
Store the Decrypted Plaintext Key
Decode the returned plaintext key and save it:
-
Decrypt the Data Using OpenSSL
Now decrypt the file with this command:
The
-dflag indicates decryption. After executing this command, the file “decrypted-data” will match the original “db-creds” file.
Final Notes
Envelope encryption requires you to store both the encrypted data and the corresponding encrypted data key. When decryption is necessary, AWS KMS can be used to extract the plaintext key from the encrypted key. Then, OpenSSL uses this plaintext key to restore your original data. This method ensures the data key is never stored in plaintext for an extended period, enhancing your overall security.By following this workflow, you effectively safeguard your sensitive data while leveraging the robust encryption capabilities offered by AWS KMS and OpenSSL.