In this article, we explore the significance of Amazon S3 access logs. These logs provide detailed records of every request made to an S3 bucket, making them an invaluable tool for both security and auditing purposes. For example, when a user named John requests the file “file1.txt”, the system logs who made the request, when it was made, and which object was accessed. This information can help you analyze user interactions and fine-tune your S3 storage setup, including selecting the optimal storage class for your data.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
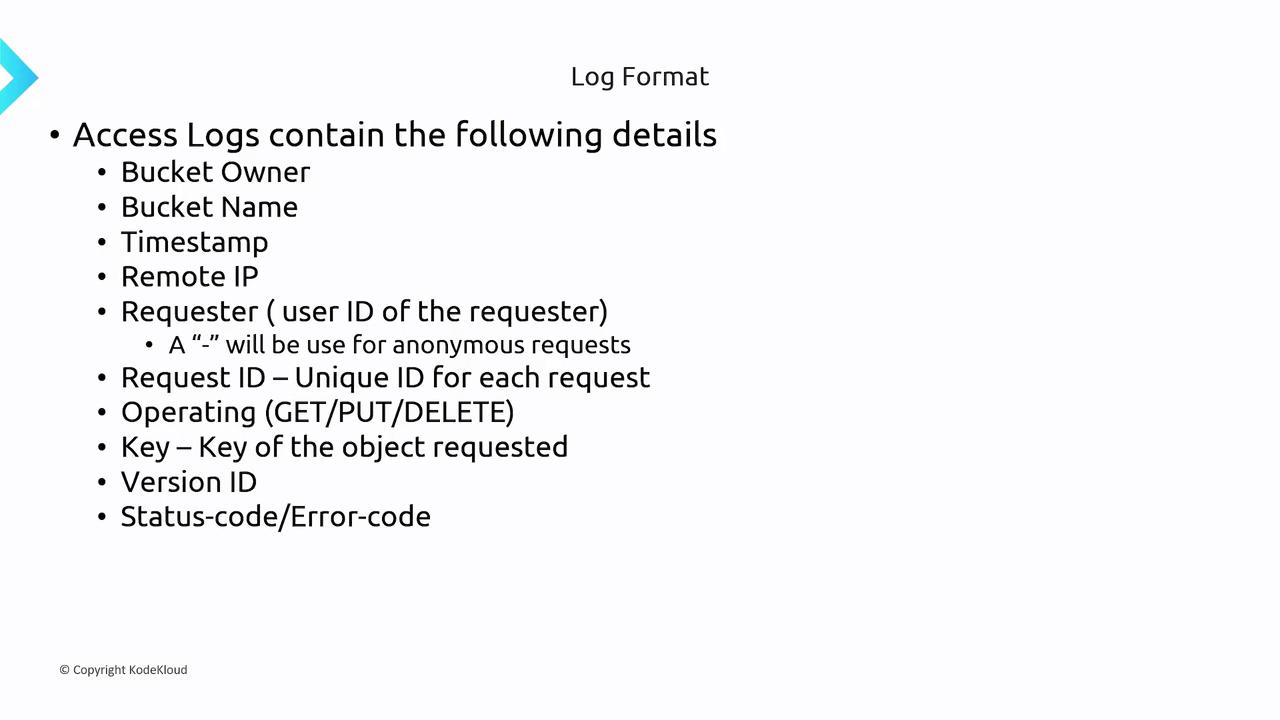
The access logs capture crucial details such as the bucket owner, bucket name, timestamp, IP address of the requester, requester’s identifier, unique request ID, operation performed (GET, PUT, DELETE, etc.), object key, version ID (if applicable), status, and error codes.
Summary
An S3 access log entry provides you with essential details about each access request, including:- Bucket Owner and Name: Identifies the owner and the specific bucket accessed.
- Request Timestamp: Records the time and date when the access occurred.
- Requester Details: Captures the IP address and user identifier of the requester.
- Operation Performed: Specifies the type of operation executed (e.g., GET, PUT, DELETE).
- Accessed Object Details: Includes the object key, version ID (if applicable), and status/error information.